| File name: | WinlockerVB6Blacksod.exe |
| Full analysis: | https://app.any.run/tasks/cbe323be-8207-4d91-9af6-c5511d2d4f96 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2020, 07:29:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DBFBF254CFB84D991AC3860105D66FC6 |
| SHA1: | 893110D8C8451565CAA591DDFCCF92869F96C242 |
| SHA256: | 68B0E1932F3B4439865BE848C2D592D5174DBDBAAB8F66104A0E5B28C928EE0C |
| SSDEEP: | 49152:6kAG2QGTC5xvMdgpdb1KRHGepUu2cGbqPs9+q2HRPTnFVSLE:6kAjQGTCnvMmpYQqPNRPTnF4Y |
MALICIOUS
Loads dropped or rewritten executable
- WinlockerVB6Blacksod.exe (PID: 2736)
Loads the Task Scheduler DLL interface
- WinlockerVB6Blacksod.exe (PID: 2736)
SUSPICIOUS
Reads Environment values
- WinlockerVB6Blacksod.exe (PID: 2736)
- MsiExec.exe (PID: 3640)
Executable content was dropped or overwritten
- WinlockerVB6Blacksod.exe (PID: 2736)
Creates files in the user directory
- MsiExec.exe (PID: 3640)
- WinlockerVB6Blacksod.exe (PID: 2736)
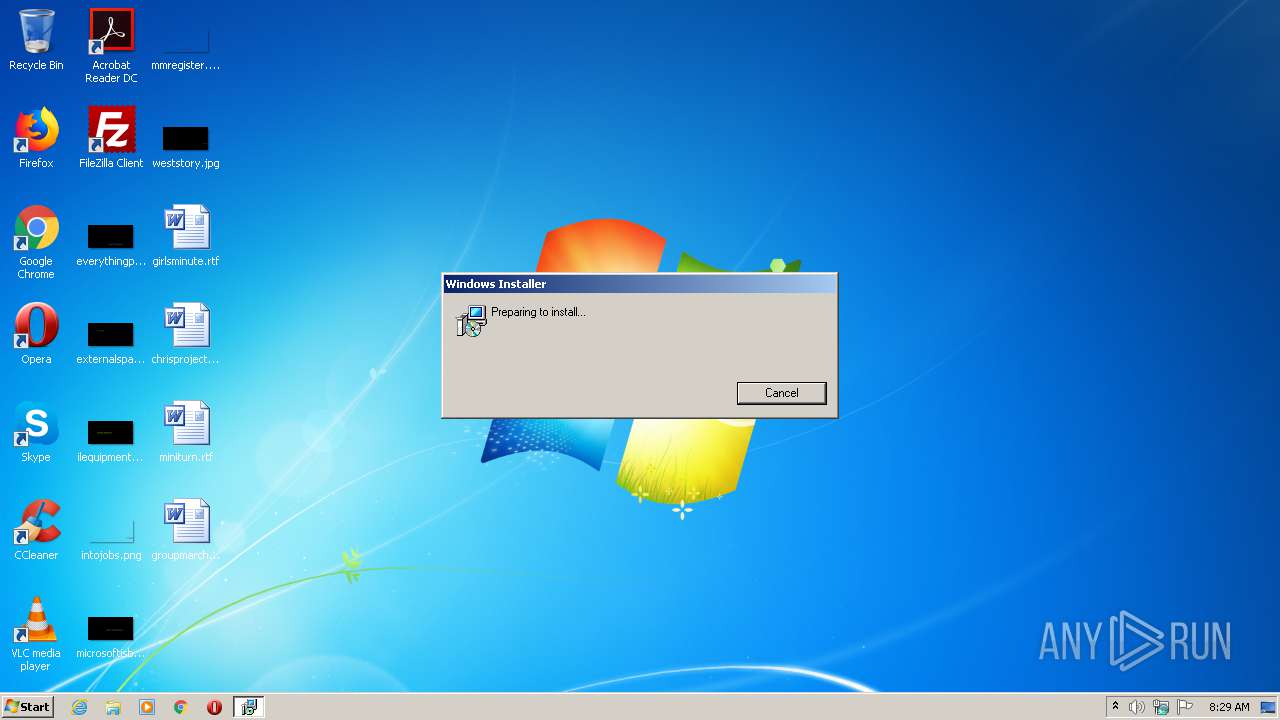
Starts Microsoft Installer
- WinlockerVB6Blacksod.exe (PID: 2736)
Reads Internet Cache Settings
- MsiExec.exe (PID: 3640)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (78.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (11.3) |
| .exe | | | Generic Win/DOS Executable (5) |
| .exe | | | DOS Executable Generic (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:09:23 15:36:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1034240 |
| InitializedDataSize: | 428544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc684c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Windows |
| FileDescription: | This installer database contains the logic and data required to install Error file remover. |
| FileVersion: | 1.0.0.0 |
| InternalName: | Error file remover |
| LegalCopyright: | Copyright (C) 2016 Windows |
| OriginalFileName: | Error file remover.exe |
| ProductName: | Error file remover |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Sep-2015 13:36:22 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Windows |
| FileDescription: | This installer database contains the logic and data required to install Error file remover. |
| FileVersion: | 1.0.0.0 |
| InternalName: | Error file remover |
| LegalCopyright: | Copyright (C) 2016 Windows |
| OriginalFileName: | Error file remover.exe |
| ProductName: | Error file remover |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Sep-2015 13:36:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000FC61C | 0x000FC800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62583 |
.rdata | 0x000FE000 | 0x0003BA7A | 0x0003BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42392 |
.data | 0x0013A000 | 0x00009D08 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.36397 |
.rsrc | 0x00144000 | 0x00011AC8 | 0x00011C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.48512 |
.reloc | 0x00156000 | 0x00018032 | 0x00018200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.23129 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.34086 | 996 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
MSIMG32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2736 | "C:\Users\admin\AppData\Local\Temp\WinlockerVB6Blacksod.exe" | C:\Users\admin\AppData\Local\Temp\WinlockerVB6Blacksod.exe | explorer.exe | ||||||||||||
User: admin Company: Windows Integrity Level: MEDIUM Description: This installer database contains the logic and data required to install Error file remover. Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2944 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Windows\Error file remover 1.0.0.0\install\0A01606\Error file remover.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\WinlockerVB6Blacksod.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /exelang 0 /noprereqs " | C:\Windows\system32\msiexec.exe | — | WinlockerVB6Blacksod.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3640 | C:\Windows\system32\MsiExec.exe -Embedding 158103521527C1B1ADCFD41CA331CD2E | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
271
Read events
262
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3640) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
3
Suspicious files
0
Text files
25
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\LM5C0R34.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\0AGW21C4.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\NTCRWZY6.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\K6WFDTKG.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\IR29X8ZG.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\FC4N8JSI.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\C3WX35U8.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Q57P6GRC.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\IBS7JEYM.txt | — | |
MD5:— | SHA256:— | |||
| 3640 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\C7SCWYY6.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
3640 | MsiExec.exe | POST | 402 | 52.6.210.194:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3640 | MsiExec.exe | 52.6.210.194:80 | collect.installeranalytics.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
collect.installeranalytics.com |
| malicious |