| File name: | adv.exe |
| Full analysis: | https://app.any.run/tasks/cbb1b5fa-3941-4e0e-8be7-aeadb3ab96dd |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2021, 07:56:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1A233B201B86B96E5BA2466F93FD0ACD |
| SHA1: | 2A0046A26D3548616794ACA94FA3328E7B7D82E3 |
| SHA256: | 68A74311FA5340DD437F63B2CCB51F17A76595C636C4DE2DA26388F94C95DDD6 |
| SSDEEP: | 196608:X+gqLKB2p+cda8hQOdBupPMPua7io60/4q:X+jOB2pNdwOd8p27iP+7 |
MALICIOUS
Loads dropped or rewritten executable
- adv.exe (PID: 3460)
- MsiExec.exe (PID: 1956)
- MsiExec.exe (PID: 852)
- plagsync.exe (PID: 2168)
Drops executable file immediately after starts
- adv.exe (PID: 3460)
Loads the Task Scheduler COM API
- adv.exe (PID: 3460)
Application was dropped or rewritten from another process
- plagsync.exe (PID: 2168)
SUSPICIOUS
Reads the computer name
- adv.exe (PID: 3460)
- plagsync.exe (PID: 2168)
Checks supported languages
- adv.exe (PID: 3460)
- plagsync.exe (PID: 2168)
Executed as Windows Service
- msiexec.exe (PID: 2276)
Reads Windows owner or organization settings
- adv.exe (PID: 3460)
- msiexec.exe (PID: 584)
- msiexec.exe (PID: 2276)
Application launched itself
- msiexec.exe (PID: 2276)
Drops a file that was compiled in debug mode
- adv.exe (PID: 3460)
- msiexec.exe (PID: 2276)
Executable content was dropped or overwritten
- adv.exe (PID: 3460)
- msiexec.exe (PID: 2276)
Reads Environment values
- adv.exe (PID: 3460)
Reads the Windows organization settings
- adv.exe (PID: 3460)
- msiexec.exe (PID: 584)
- msiexec.exe (PID: 2276)
Starts Microsoft Installer
- adv.exe (PID: 3460)
Drops a file with a compile date too recent
- adv.exe (PID: 3460)
- msiexec.exe (PID: 2276)
Creates files in the user directory
- msiexec.exe (PID: 2276)
- adv.exe (PID: 3460)
INFO
Checks supported languages
- msiexec.exe (PID: 2276)
- MsiExec.exe (PID: 1956)
- msiexec.exe (PID: 584)
- MsiExec.exe (PID: 852)
Checks Windows Trust Settings
- adv.exe (PID: 3460)
- msiexec.exe (PID: 584)
- msiexec.exe (PID: 2276)
Reads the computer name
- msiexec.exe (PID: 2276)
- MsiExec.exe (PID: 1956)
- msiexec.exe (PID: 584)
- MsiExec.exe (PID: 852)
Reads settings of System Certificates
- adv.exe (PID: 3460)
- msiexec.exe (PID: 2276)
- msiexec.exe (PID: 584)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:27 15:39:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 1597952 |
| InitializedDataSize: | 609792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12ea61 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.8.32.3 |
| ProductVersionNumber: | 2.8.32.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
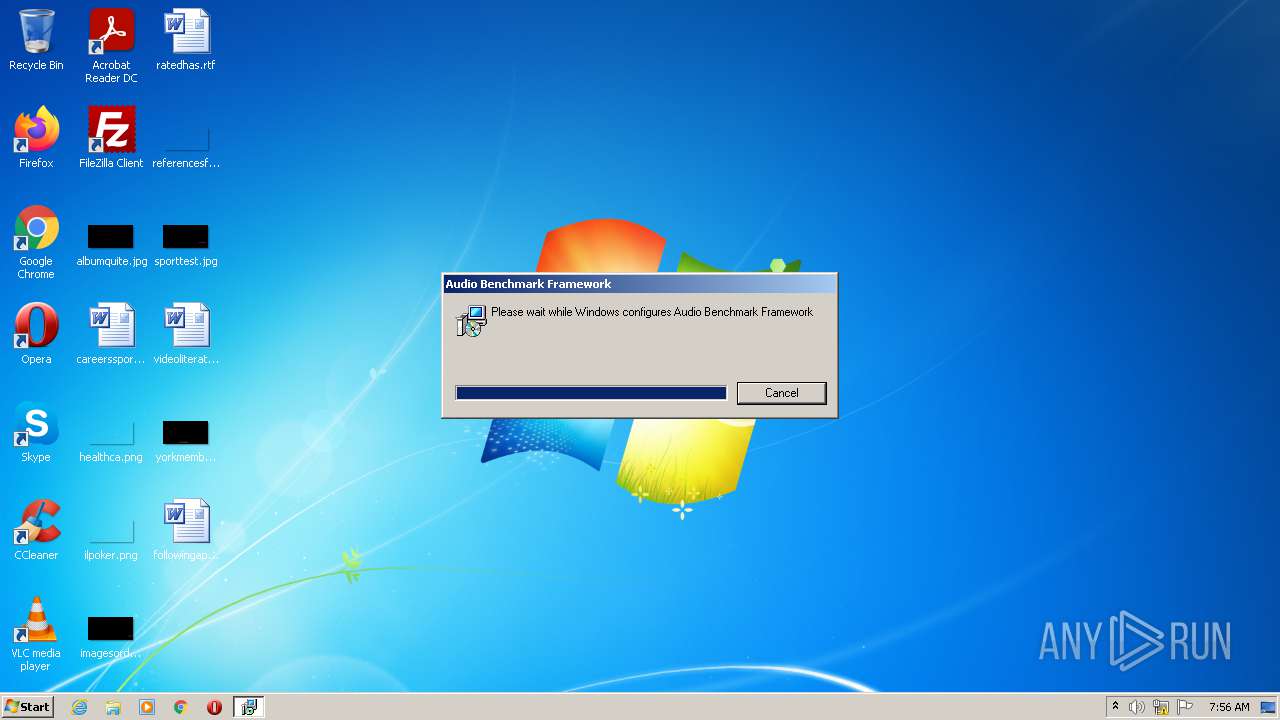
| CompanyName: | Emjysoft |
| FileDescription: | Audio Benchmark Framework Installer |
| FileVersion: | 2.8.32.3 |
| InternalName: | adv |
| LegalCopyright: | Copyright (C) 2021 Emjysoft |
| OriginalFileName: | adv.exe |
| ProductName: | Audio Benchmark Framework |
| ProductVersion: | 2.8.32.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jul-2021 13:39:02 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Emjysoft |
| FileDescription: | Audio Benchmark Framework Installer |
| FileVersion: | 2.8.32.3 |
| InternalName: | adv |
| LegalCopyright: | Copyright (C) 2021 Emjysoft |
| OriginalFileName: | adv.exe |
| ProductName: | Audio Benchmark Framework |
| ProductVersion: | 2.8.32.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Jul-2021 13:39:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0018611F | 0x00186200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4256 |
.rdata | 0x00188000 | 0x0005FD94 | 0x0005FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.585 |
.data | 0x001E8000 | 0x00006E88 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.03685 |
.rsrc | 0x001EF000 | 0x000156B4 | 0x00015800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.3634 |
.reloc | 0x00205000 | 0x0001A068 | 0x0001A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56895 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.34881 | 836 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.38539 | 938 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
38
Monitored processes
6
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Emjysoft\Audio Benchmark Framework 2.8.32.3\install\4E5F961\adv.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\adv.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1637480323 " AI_EUIMSI="" | C:\Windows\system32\msiexec.exe | — | adv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\MsiExec.exe -Embedding DD1542437134FC9F050351B1BF5C0346 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1956 | C:\Windows\system32\MsiExec.exe -Embedding DF74A70E546EA43CA8C100B65DD9318C C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Roaming\Emjysoft\Audio Benchmark Framework\plagsync.exe" | C:\Users\admin\AppData\Roaming\Emjysoft\Audio Benchmark Framework\plagsync.exe | — | msiexec.exe | |||||||||||
User: admin Company: PlagiusCommon Integrity Level: MEDIUM Description: PlagiusCommon Exit code: 0 Modules
| |||||||||||||||
| 2276 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\AppData\Local\Temp\adv.exe" | C:\Users\admin\AppData\Local\Temp\adv.exe | Explorer.EXE | ||||||||||||
User: admin Company: Emjysoft Integrity Level: MEDIUM Description: Audio Benchmark Framework Installer Exit code: 0 Version: 2.8.32.3 Modules
| |||||||||||||||
Total events
12 545
Read events
12 410
Write events
123
Delete events
12
Modification events
| (PID) Process: | (3460) adv.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (584) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E40800000029634AADDED701 | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 13C32D54CD3CA575E12A8951D27D2D932F4167A94618A464AA438C5EF559C145 | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\104579.ipi | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\10457a.rbs |
Value: 30924461 | |||
| (PID) Process: | (2276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\10457a.rbsLow |
Value: | |||
Executable files
50
Suspicious files
9
Text files
218
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | adv.exe | C:\Users\admin\AppData\Roaming\Emjysoft\Audio Benchmark Framework 2.8.32.3\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 3460 | adv.exe | C:\Users\admin\AppData\Roaming\Emjysoft\Audio Benchmark Framework 2.8.32.3\install\4E5F961\adv.msi | executable | |
MD5:— | SHA256:— | |||
| 3460 | adv.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2276 | msiexec.exe | C:\Windows\Installer\104577.msi | executable | |
MD5:— | SHA256:— | |||
| 3460 | adv.exe | C:\Users\admin\AppData\Roaming\Emjysoft\Audio Benchmark Framework 2.8.32.3\install\decoder.dll | executable | |
MD5:831E0B597DB11A6EB6F3F797105F7BE8 | SHA256:E3404D4AF16702A67DCAA4DA4C5A8776EF350343B179AE6E7F2D347E7E1D1FB7 | |||
| 3460 | adv.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3460 | adv.exe | C:\Users\admin\AppData\Local\Temp\Tar4067.tmp | cat | |
MD5:D99661D0893A52A0700B8AE68457351A | SHA256:BDD5111162A6FA25682E18FA74E37E676D49CAFCB5B7207E98E5256D1EF0D003 | |||
| 3460 | adv.exe | C:\Users\admin\AppData\Local\Temp\MSI4346.tmp | executable | |
MD5:A32DECEE57C661563B038D4F324E2B42 | SHA256:FCF24B9B574ED026D3F68B7B70AA6533806BA7FC566C476CCB62E6493AC28F04 | |||
| 3460 | adv.exe | C:\Users\admin\AppData\Local\Temp\Cab4066.tmp | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3460 | adv.exe | C:\Users\admin\AppData\Local\Temp\MSI4396.tmp | executable | |
MD5:4E2E67FC241AB6E440AD2789F705FC69 | SHA256:98F4EBAA6EA1083E98EA0DD5C74C2CB22B1375C55B6A12CFDC5D877F716DE392 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3460 | adv.exe | GET | 200 | 67.27.157.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?11ac0699cec01ae8 | US | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3460 | adv.exe | 67.27.157.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |