| File name: | tmphvke7hx3 |
| Full analysis: | https://app.any.run/tasks/e3018d53-d5d7-4dd3-9241-f4486efe6bc5 |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2021, 06:53:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0C5D539BF22F164193BBE323FEC6EDD3 |
| SHA1: | 48E3FAD1A61727C3590933C48D22D7F04821125F |
| SHA256: | 689F3DB67462AE67027184D73266B998EEE25FA53AC25018064AC6EA45300740 |
| SSDEEP: | 384:8GEIWIDVuO4rQw2NUH6ovEpxnJjPnoGFIYIPUbPScRQhUf7LAR:8V8cOu2NOSnJLnRFWgqcKS78 |
MALICIOUS
Application was dropped or rewritten from another process
- cabinstaller.exe (PID: 2448)
- InstallerControl_setup.exe (PID: 1232)
- cabinstaller.exe (PID: 3612)
- F5InstH.exe (PID: 3336)
- F5InstH.exe (PID: 3116)
- f5instd.exe (PID: 3956)
- f5unistall.exe (PID: 3052)
- F5PolicyServer.exe (PID: 1208)
- ietrust.exe (PID: 788)
- ietrust.exe (PID: 3960)
- F5PolicyServer.exe (PID: 1516)
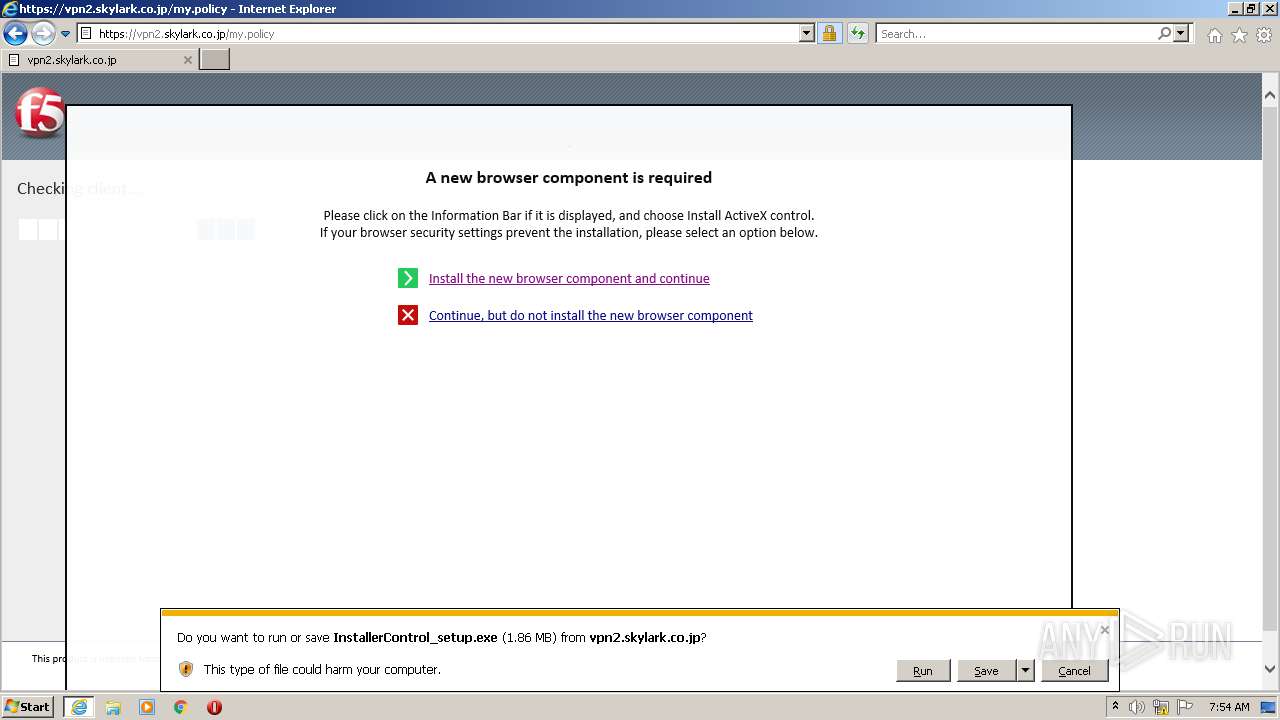
Drops executable file immediately after starts
- InstallerControl_setup.exe (PID: 1232)
- cabinstaller.exe (PID: 2448)
- f5unistall.exe (PID: 3052)
Changes settings of System certificates
- cabinstaller.exe (PID: 2448)
Loads dropped or rewritten executable
- F5InstH.exe (PID: 3336)
- iexplore.exe (PID: 4076)
- cabinstaller.exe (PID: 2448)
- iexplore.exe (PID: 2456)
- f5instd.exe (PID: 3956)
- iexplore.exe (PID: 2660)
SUSPICIOUS
Checks supported languages
- tmphvke7hx3.exe (PID: 3452)
- cmd.exe (PID: 3884)
- InstallerControl_setup.exe (PID: 1232)
- cabinstaller.exe (PID: 2448)
- cabinstaller.exe (PID: 3612)
- f5unistall.exe (PID: 3052)
- F5InstH.exe (PID: 3116)
- f5instd.exe (PID: 3956)
- F5InstH.exe (PID: 3336)
- F5PolicyServer.exe (PID: 1208)
- ietrust.exe (PID: 3960)
- F5PolicyServer.exe (PID: 1516)
Reads the computer name
- tmphvke7hx3.exe (PID: 3452)
- cabinstaller.exe (PID: 3612)
- cabinstaller.exe (PID: 2448)
- F5InstH.exe (PID: 3336)
- f5instd.exe (PID: 3956)
- ietrust.exe (PID: 3960)
- F5PolicyServer.exe (PID: 1516)
Starts CMD.EXE for commands execution
- tmphvke7hx3.exe (PID: 3452)
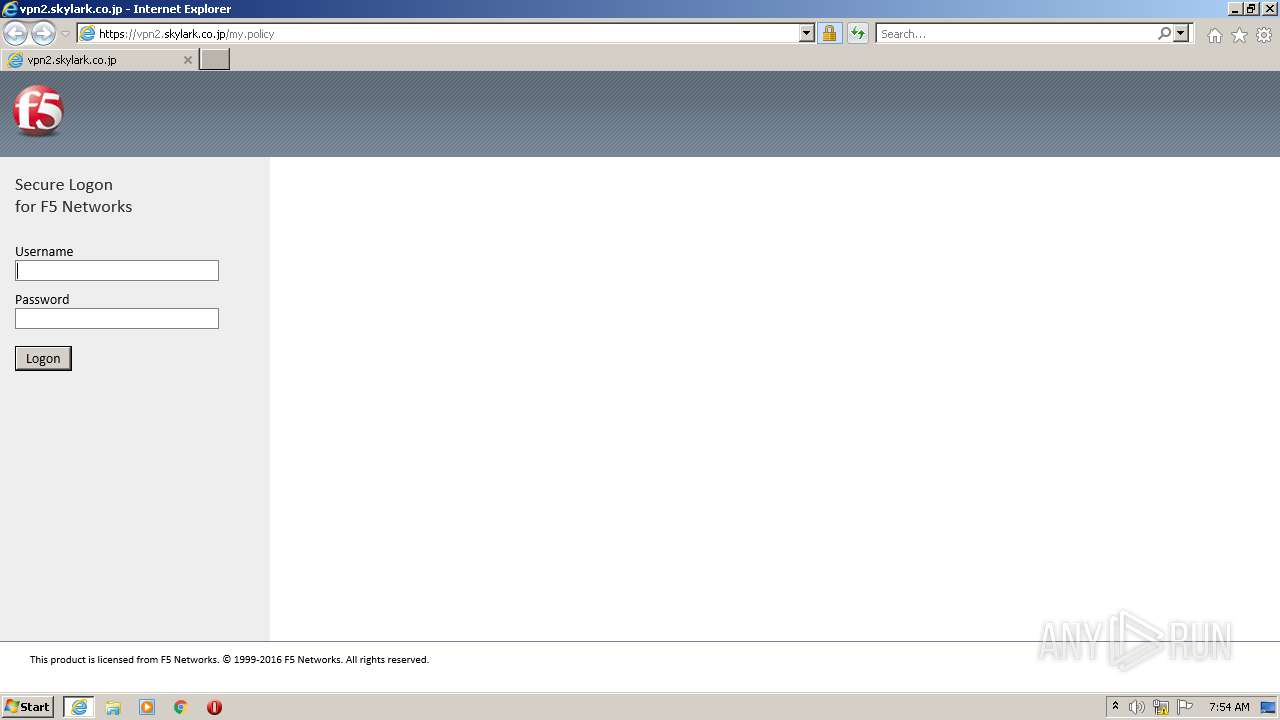
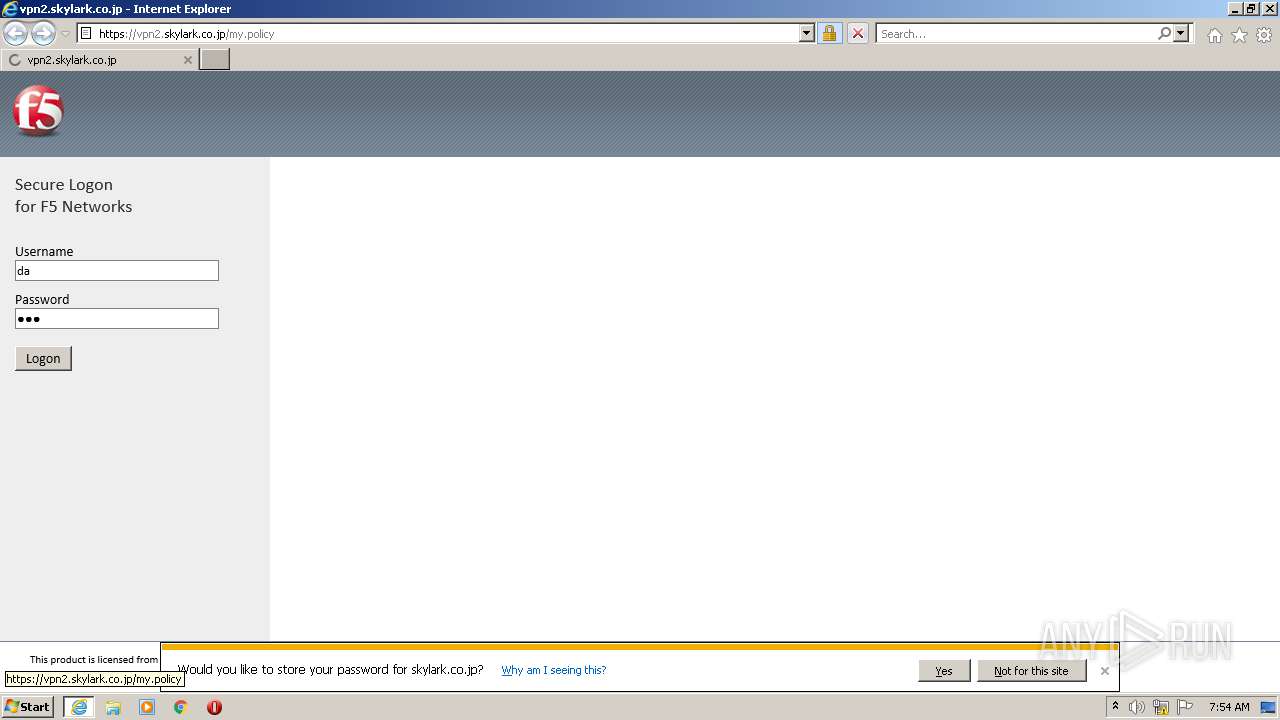
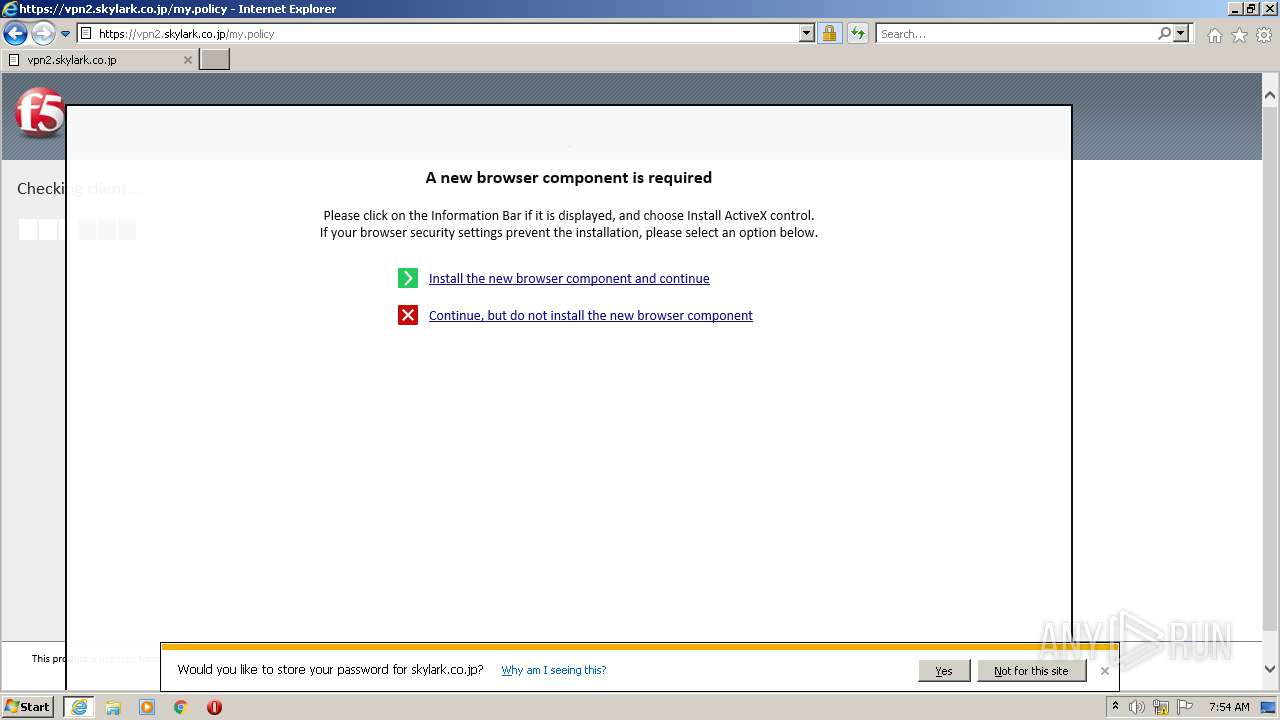
Starts Internet Explorer
- cmd.exe (PID: 3884)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3884)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2660)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 4076)
- InstallerControl_setup.exe (PID: 1232)
- cabinstaller.exe (PID: 2448)
- f5unistall.exe (PID: 3052)
- f5instd.exe (PID: 3956)
Drops a file that was compiled in debug mode
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 4076)
- InstallerControl_setup.exe (PID: 1232)
- cabinstaller.exe (PID: 2448)
- f5unistall.exe (PID: 3052)
- f5instd.exe (PID: 3956)
Application launched itself
- cabinstaller.exe (PID: 3612)
Reads Environment values
- cabinstaller.exe (PID: 3612)
- cabinstaller.exe (PID: 2448)
- iexplore.exe (PID: 2456)
- f5instd.exe (PID: 3956)
- iexplore.exe (PID: 2660)
Adds / modifies Windows certificates
- cabinstaller.exe (PID: 2448)
Creates files in the Windows directory
- cabinstaller.exe (PID: 2448)
- f5unistall.exe (PID: 3052)
- f5instd.exe (PID: 3956)
Creates/Modifies COM task schedule object
- cabinstaller.exe (PID: 2448)
- F5InstH.exe (PID: 3116)
- f5instd.exe (PID: 3956)
Creates a software uninstall entry
- f5unistall.exe (PID: 3052)
Executed via COM
- F5InstH.exe (PID: 3336)
- F5PolicyServer.exe (PID: 1516)
Creates files in the program directory
- f5unistall.exe (PID: 3052)
INFO
Reads the computer name
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 2660)
Checks supported languages
- iexplore.exe (PID: 2456)
- reg.exe (PID: 2060)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2660)
Reads settings of System Certificates
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 4076)
- f5instd.exe (PID: 3956)
- iexplore.exe (PID: 2660)
- cabinstaller.exe (PID: 2448)
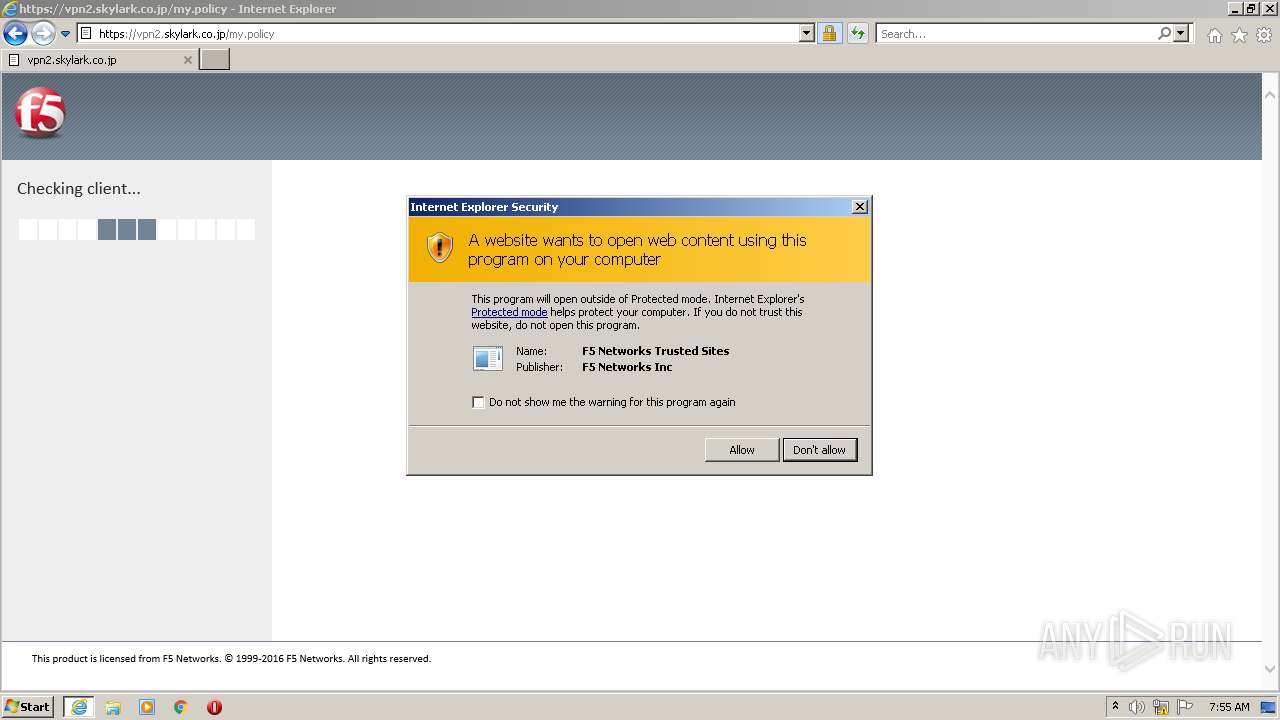
Checks Windows Trust Settings
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2456)
- cabinstaller.exe (PID: 2448)
- f5instd.exe (PID: 3956)
- iexplore.exe (PID: 2660)
Reads internet explorer settings
- iexplore.exe (PID: 2456)
- iexplore.exe (PID: 2660)
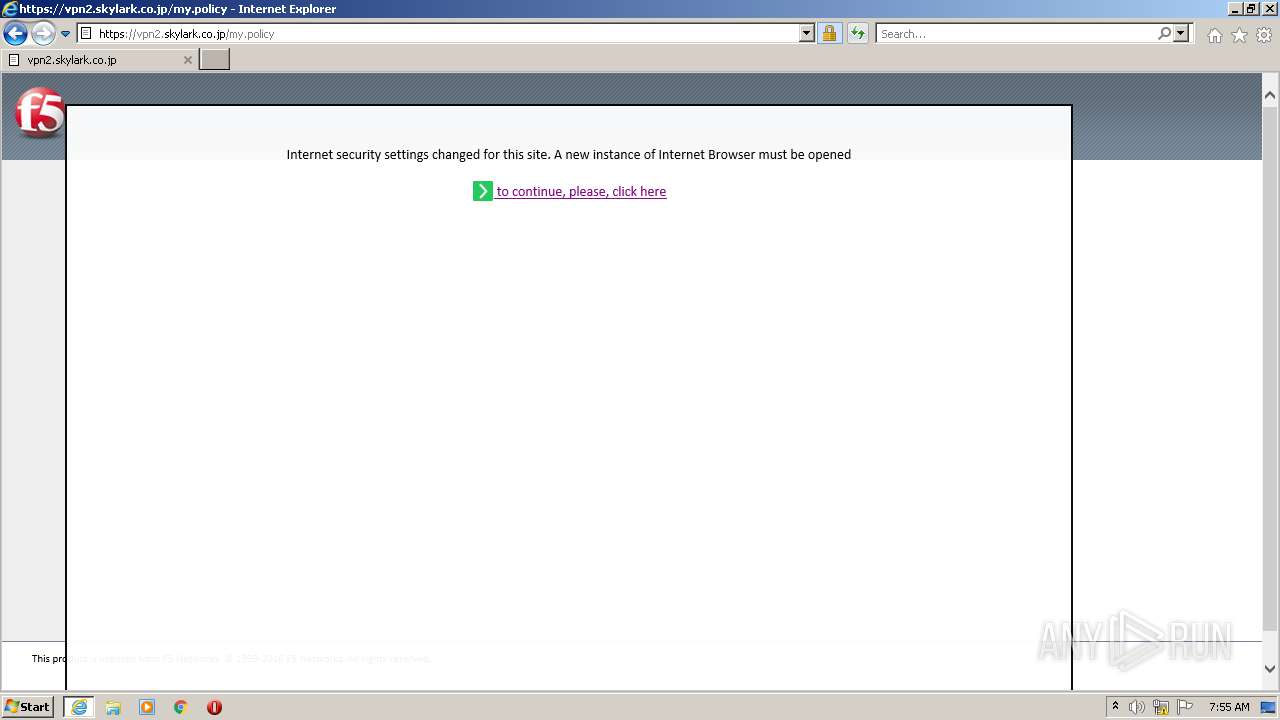
Changes internet zones settings
- iexplore.exe (PID: 4076)
Application launched itself
- iexplore.exe (PID: 4076)
Changes settings of System certificates
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2660)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2660)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4076)
Creates files in the user directory
- iexplore.exe (PID: 4076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 1.2 |
| OSVersion: | 5.1 |
| EntryPoint: | 0x4527 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 12800 |
| CodeSize: | 16896 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2016:06:11 12:54:48+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Jun-2016 10:54:48 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 11-Jun-2016 10:54:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004044 | 0x00004200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.42311 |
.data | 0x00006000 | 0x000006AC | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.87951 |
.rsrc | 0x00007000 | 0x0000265C | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97768 |
.reloc | 0x0000A000 | 0x00000526 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.93573 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87607 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 1.91924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
Total processes
59
Monitored processes
17
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
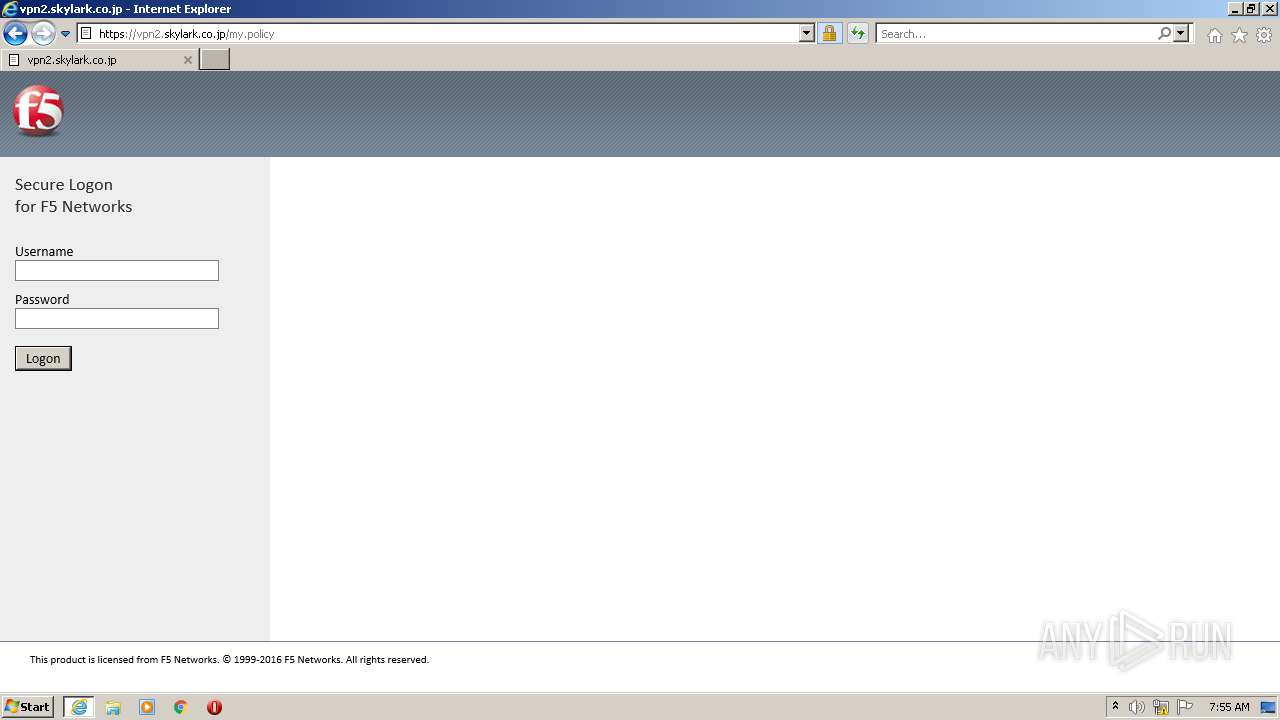
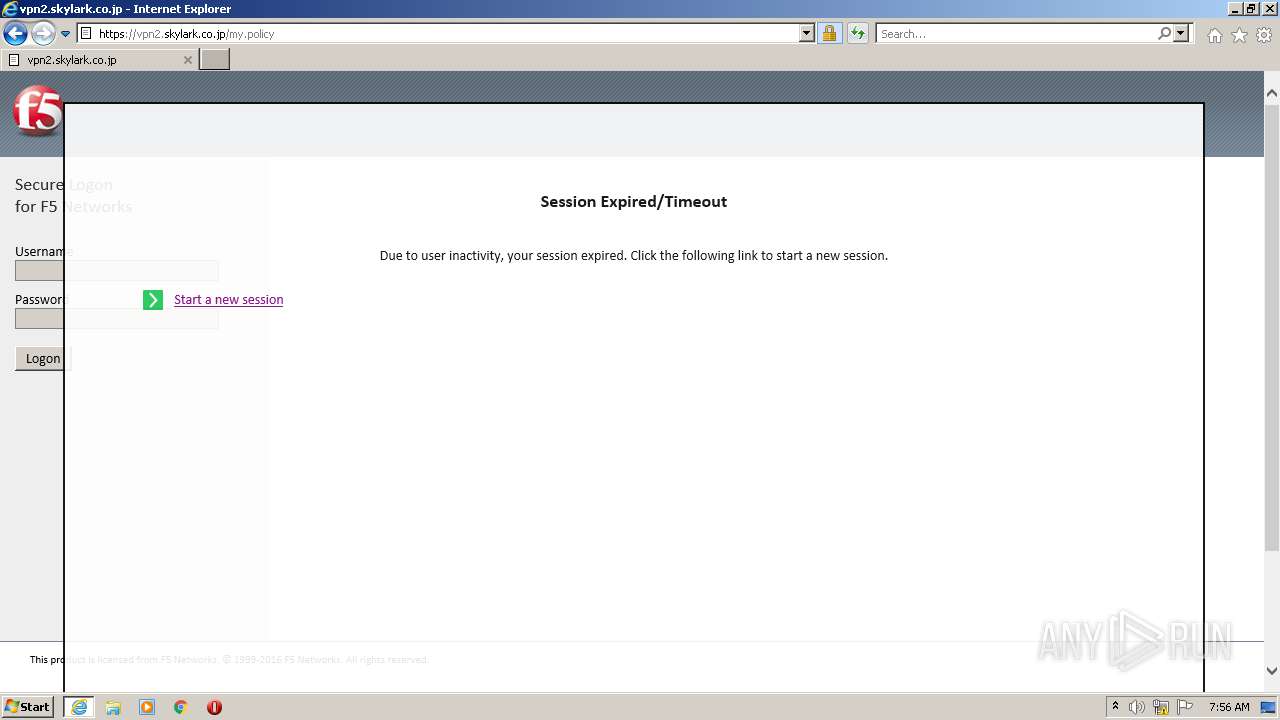
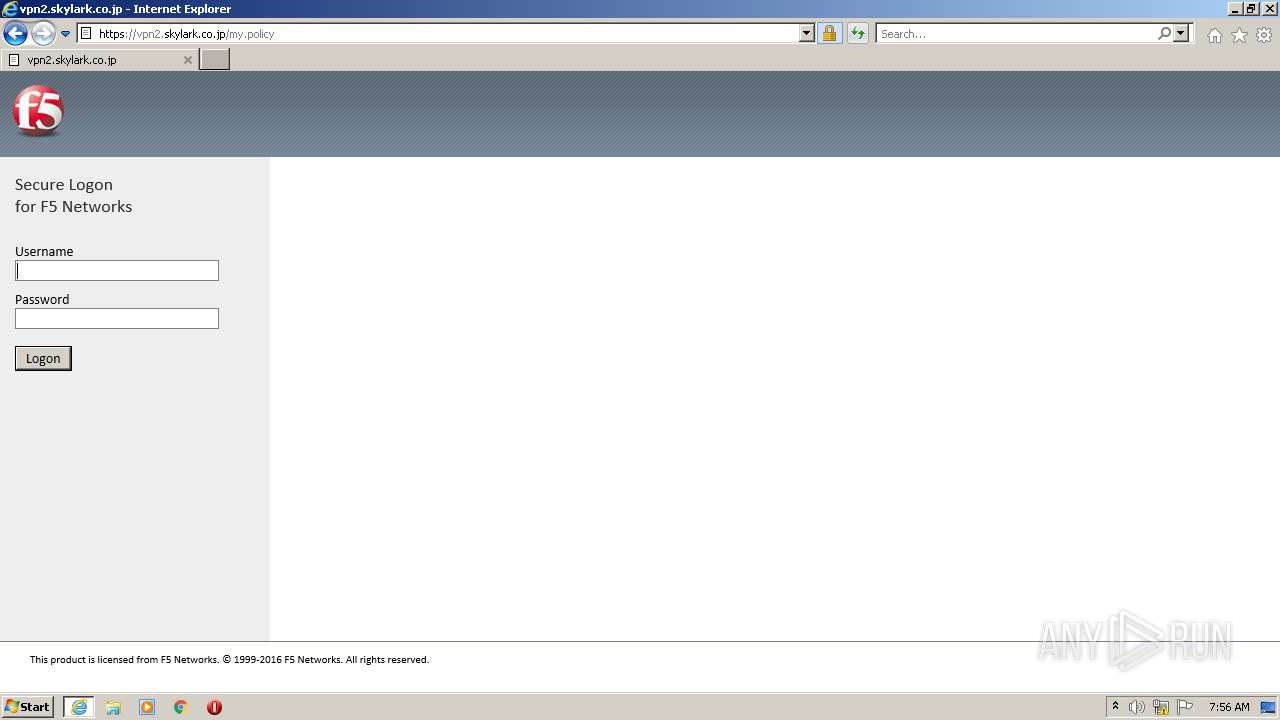
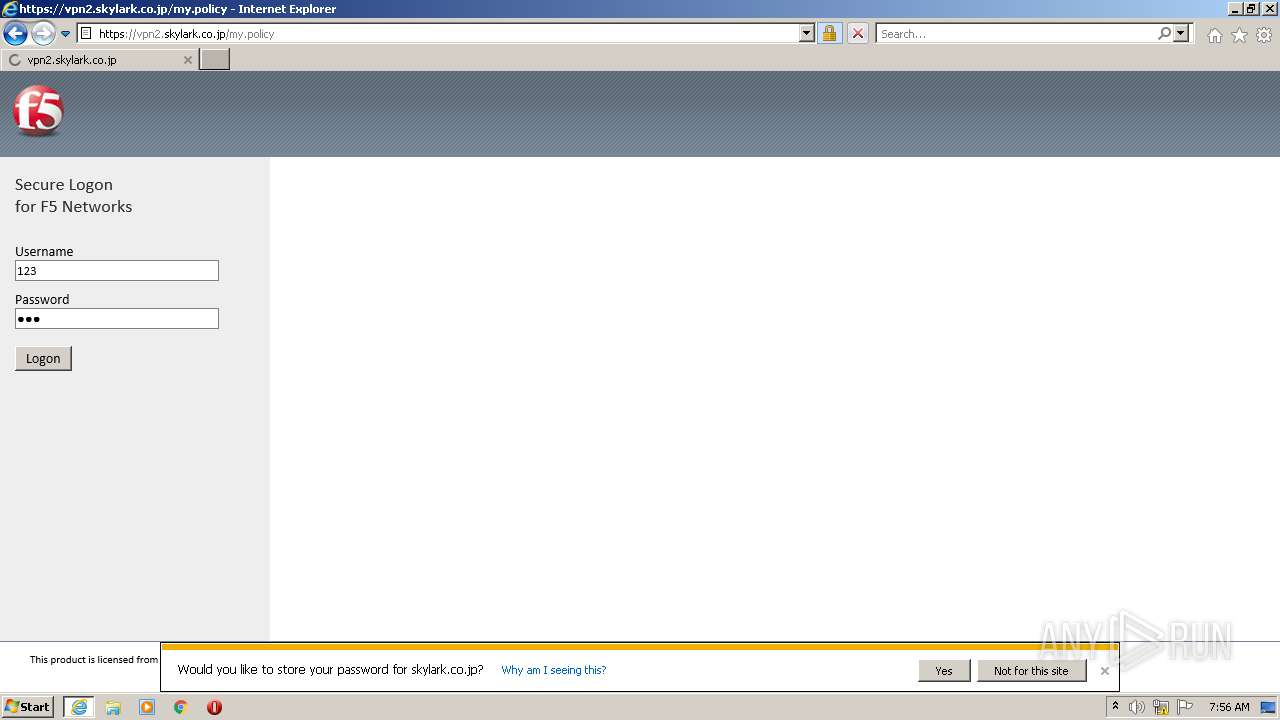
| 788 | "C:\Windows\Downloaded Program Files\ietrust.exe" "https://vpn2.skylark.co.jp" | C:\Windows\Downloaded Program Files\ietrust.exe | — | iexplore.exe | |||||||||||
User: admin Company: F5 Networks, Inc. Integrity Level: LOW Description: F5 Networks Trusted Sites Exit code: 0 Version: 7132, 2017, 0404, 2206 Modules
| |||||||||||||||
| 1208 | "C:\Windows\Downloaded Program Files\F5PolicyServer.exe" /RegServer | C:\Windows\Downloaded Program Files\F5PolicyServer.exe | — | f5instd.exe | |||||||||||
User: admin Company: F5 Networks, Inc. Integrity Level: HIGH Description: F5 Networks Client Policy Server Exit code: 0 Version: 7132, 2017, 0404, 2206 Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\InstallerControl_setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\InstallerControl_setup.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1516 | "C:\Windows\Downloaded Program Files\F5PolicyServer.exe" -Embedding | C:\Windows\Downloaded Program Files\F5PolicyServer.exe | — | svchost.exe | |||||||||||
User: admin Company: F5 Networks, Inc. Integrity Level: MEDIUM Description: F5 Networks Client Policy Server Exit code: 0 Version: 7132, 2017, 0404, 2206 Modules
| |||||||||||||||
| 2060 | reg delete "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings" /f /v ProxyEnable | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\cabinstaller.exe" | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\cabinstaller.exe | cabinstaller.exe | ||||||||||||
User: admin Company: F5 Networks, Inc. Integrity Level: HIGH Description: F5 Networks Package installer Exit code: 0 Version: 7132, 2017, 0404, 2206 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4076 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4076 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3052 | "C:\Windows\Downloaded Program Files\f5unistall.exe" /createshortcut | C:\Windows\Downloaded Program Files\f5unistall.exe | cabinstaller.exe | ||||||||||||
User: admin Company: F5 Networks, Inc. Integrity Level: HIGH Description: F5 Networks Components Troubleshooting Exit code: 0 Version: 7132, 2017, 0404, 2206 Modules
| |||||||||||||||
| 3116 | "C:\Windows\Downloaded Program Files\F5InstH.exe" /RegServer | C:\Windows\Downloaded Program Files\F5InstH.exe | — | cabinstaller.exe | |||||||||||
User: admin Company: F5 Networks, Inc. Integrity Level: HIGH Description: F5 Networks InstallerHelper Module Exit code: 0 Version: 7132, 2017, 0404, 2206 Modules
| |||||||||||||||
Total events
35 978
Read events
35 410
Write events
550
Delete events
18
Modification events
| (PID) Process: | (3452) tmphvke7hx3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3452) tmphvke7hx3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3452) tmphvke7hx3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3452) tmphvke7hx3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2060) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902726 | |||
| (PID) Process: | (4076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902726 | |||
Executable files
24
Suspicious files
19
Text files
58
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72C3314B18E47DC7C3A0A7EBA606192F_133C2E1400917F7AF379F941FDBF6D50 | binary | |
MD5:— | SHA256:— | |||
| 3452 | tmphvke7hx3.exe | C:\Users\admin\AppData\Local\Temp\nDeC245\???????????????VPN2?????.bat | text | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\my[1].htm | html | |
MD5:— | SHA256:— | |||
| 4076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\355F88C5CC4B0043BFE178CFE81252D4 | binary | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\355F88C5CC4B0043BFE178CFE81252D4 | der | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\72C3314B18E47DC7C3A0A7EBA606192F_133C2E1400917F7AF379F941FDBF6D50 | der | |
MD5:— | SHA256:— | |||
| 4076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\13886C091EC5C0D7486A78E314A2ED81_6D9BDEB650C3BC61067841C5BB132D2A | der | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\13886C091EC5C0D7486A78E314A2ED81_6D9BDEB650C3BC61067841C5BB132D2A | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
58
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2456 | iexplore.exe | GET | 200 | 23.32.238.226:80 | http://scrootca2.ocsp.secomtrust.net/MEowSDBGMEQwQjAJBgUrDgMCGgUABBTyDvPjcY8Z0TDZzHotwwMWHLKc0AQUCoWpd2UFmHxAgfgPlyw48QrsPM8CCSK5sWMM7LQ8Lg%3D%3D | US | der | 1.50 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 61.114.177.151:80 | http://repository.secomtrust.net/SC-Root2/SCRoot2CRL.crl | JP | der | 2.50 Kb | whitelisted |
2456 | iexplore.exe | GET | 200 | 23.32.238.195:80 | http://scrootca1.ocsp.secomtrust.net/MEowSDBGMEQwQjAJBgUrDgMCGgUABBToZI35nvnlbqQAOxgex2VgV2SjmAQUoHNJmWjchVtl45soL1efvTO8B0gCCRK5sPpy4NhIxg%3D%3D | US | der | 1.48 Kb | whitelisted |
2456 | iexplore.exe | GET | 200 | 124.24.58.212:80 | http://ssocsp.cybertrust.ne.jp/OcspServer/MFUwUzBRME8wTTAJBgUrDgMCGgUABBSdAxQrs2W5NWr2QA%2Fa%2BIVB2osTTQQUYqfS2t6FtpLxhbz26JWddaD6Th8CFA2u%2BFfXjw%2BltGTq0wVVjIb63IoA | JP | der | 1.44 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2456 | iexplore.exe | GET | 200 | 2.16.186.9:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?51f3ae1ce1654a99 | unknown | compressed | 4.70 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2456 | iexplore.exe | GET | 200 | 2.16.186.9:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?352c6b61897e02d1 | unknown | compressed | 4.70 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | iexplore.exe | 2.16.186.9:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
— | — | 51.124.78.146:443 | — | Microsoft Corporation | GB | whitelisted |
4076 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2456 | iexplore.exe | 23.32.238.195:80 | scrootca1.ocsp.secomtrust.net | XO Communications | US | suspicious |
2456 | iexplore.exe | 61.114.177.151:80 | repository.secomtrust.net | SECOM Trust Systems Co.,Ltd. | JP | unknown |
4076 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
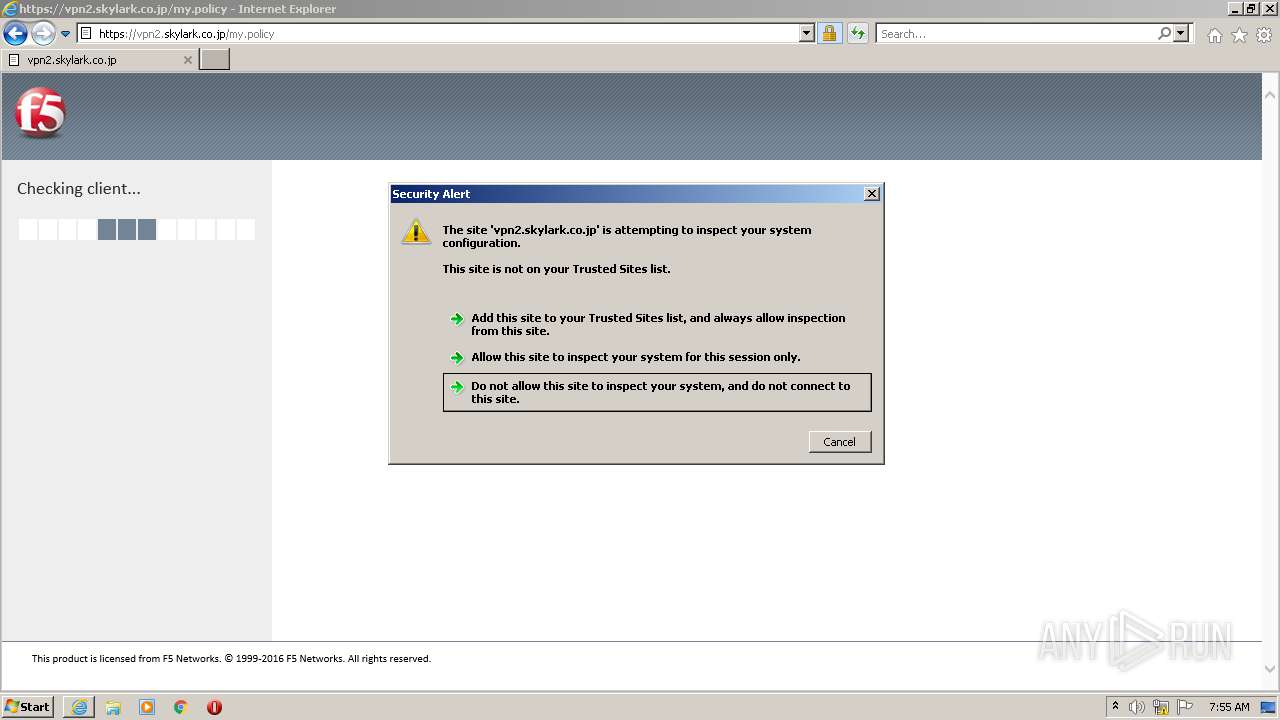
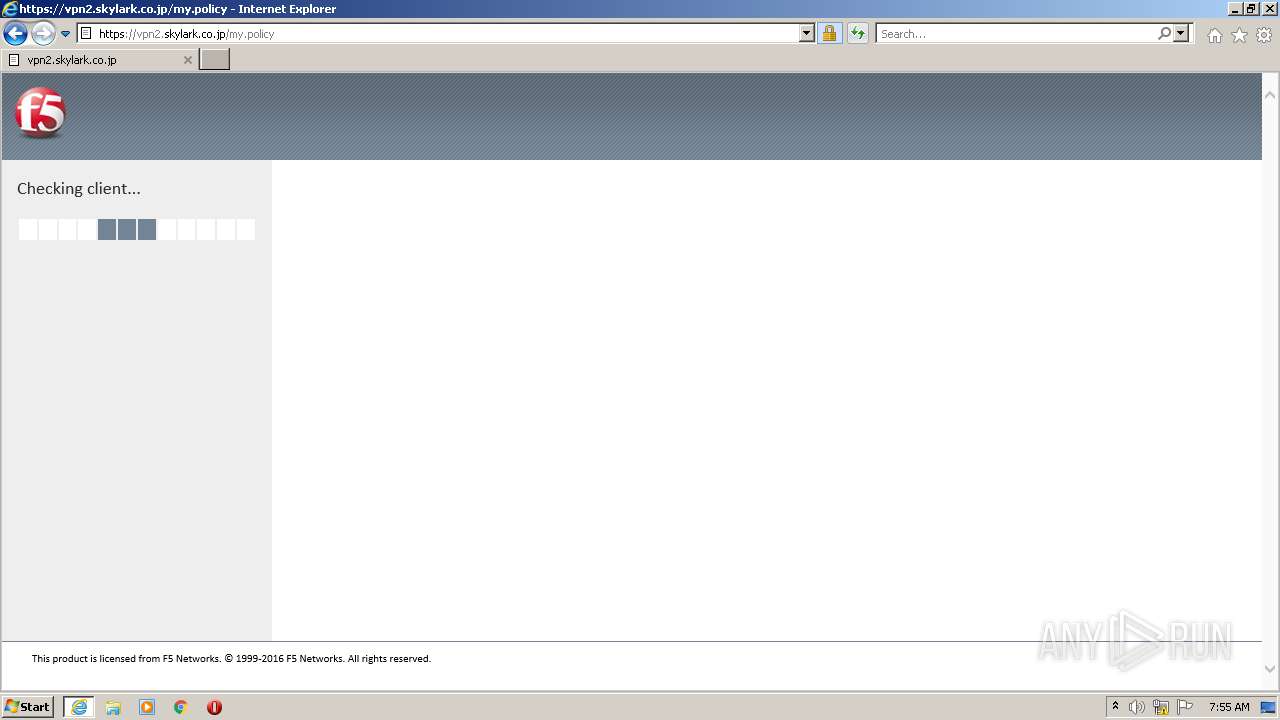
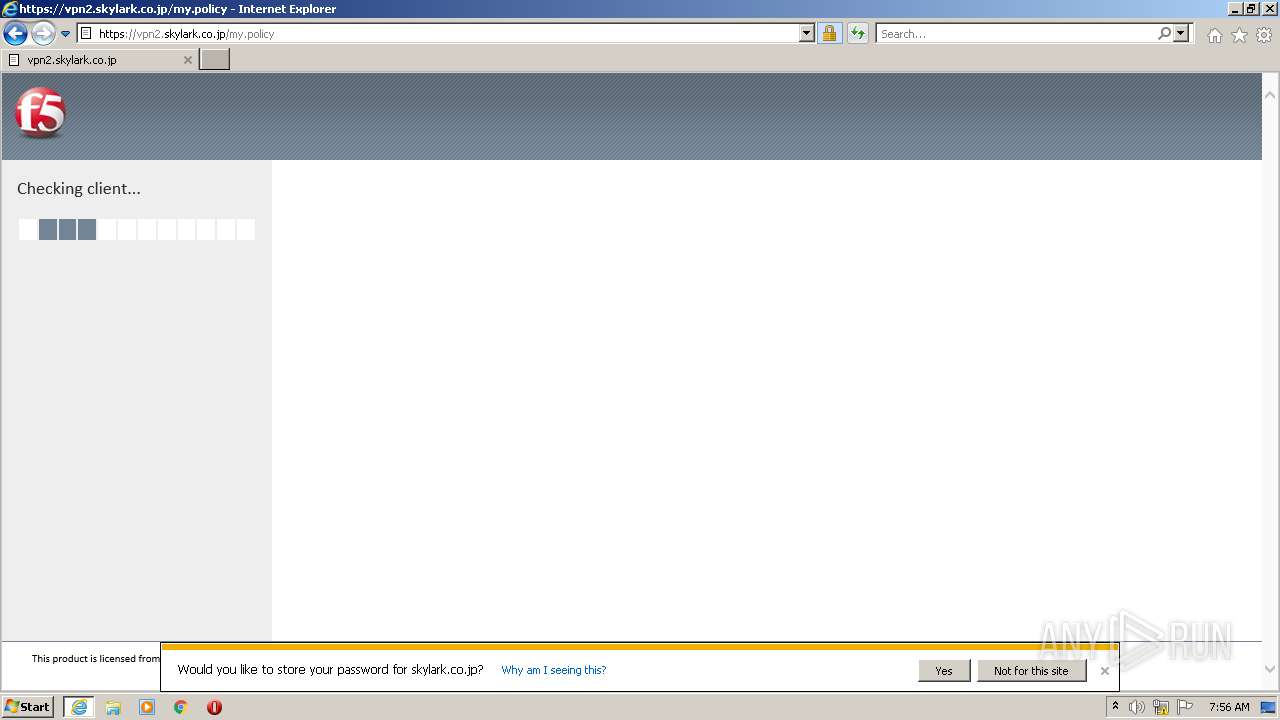
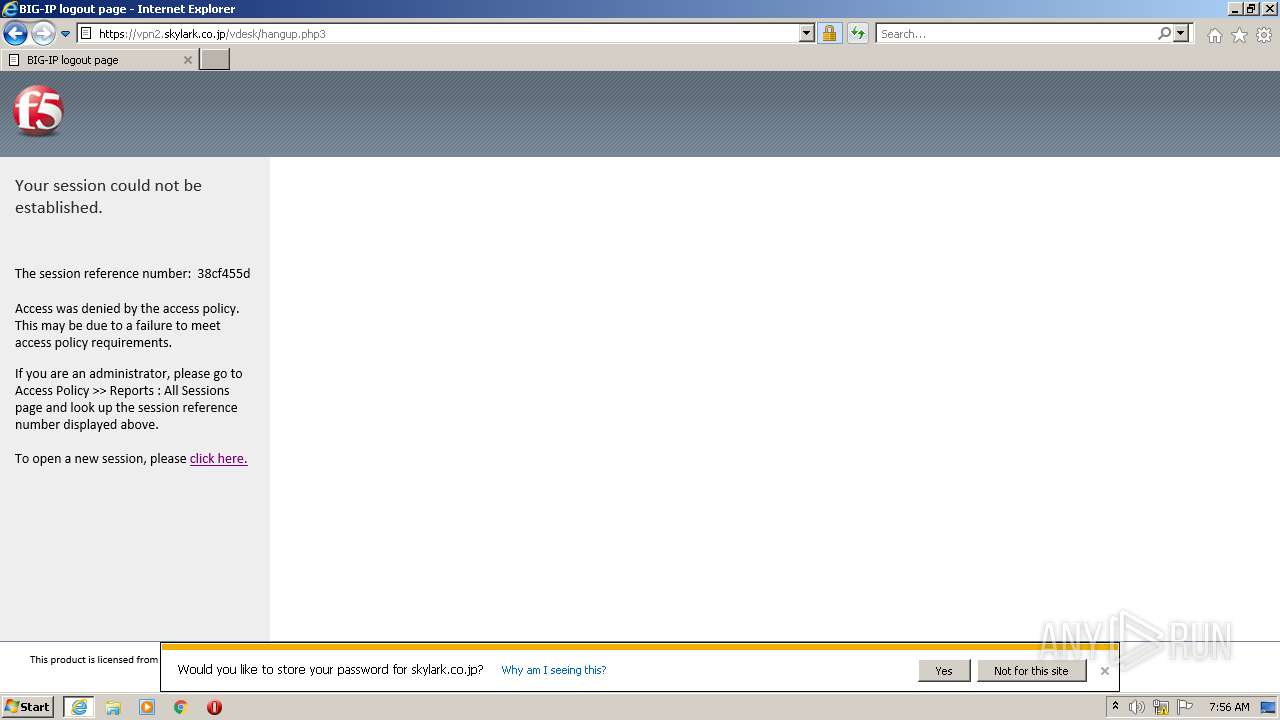
4076 | iexplore.exe | 210.162.145.211:443 | vpn2.skylark.co.jp | NTT Communications Corporation | JP | unknown |
2456 | iexplore.exe | 124.24.58.212:80 | ssocsp.cybertrust.ne.jp | FUJITSU LIMITED | JP | unknown |
1360 | svchost.exe | 51.124.78.146:443 | — | Microsoft Corporation | GB | whitelisted |
4076 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vpn2.skylark.co.jp |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
scrootca1.ocsp.secomtrust.net |
| whitelisted |
scrootca2.ocsp.secomtrust.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
repository.secomtrust.net |
| unknown |
ssocsp.cybertrust.ne.jp |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |