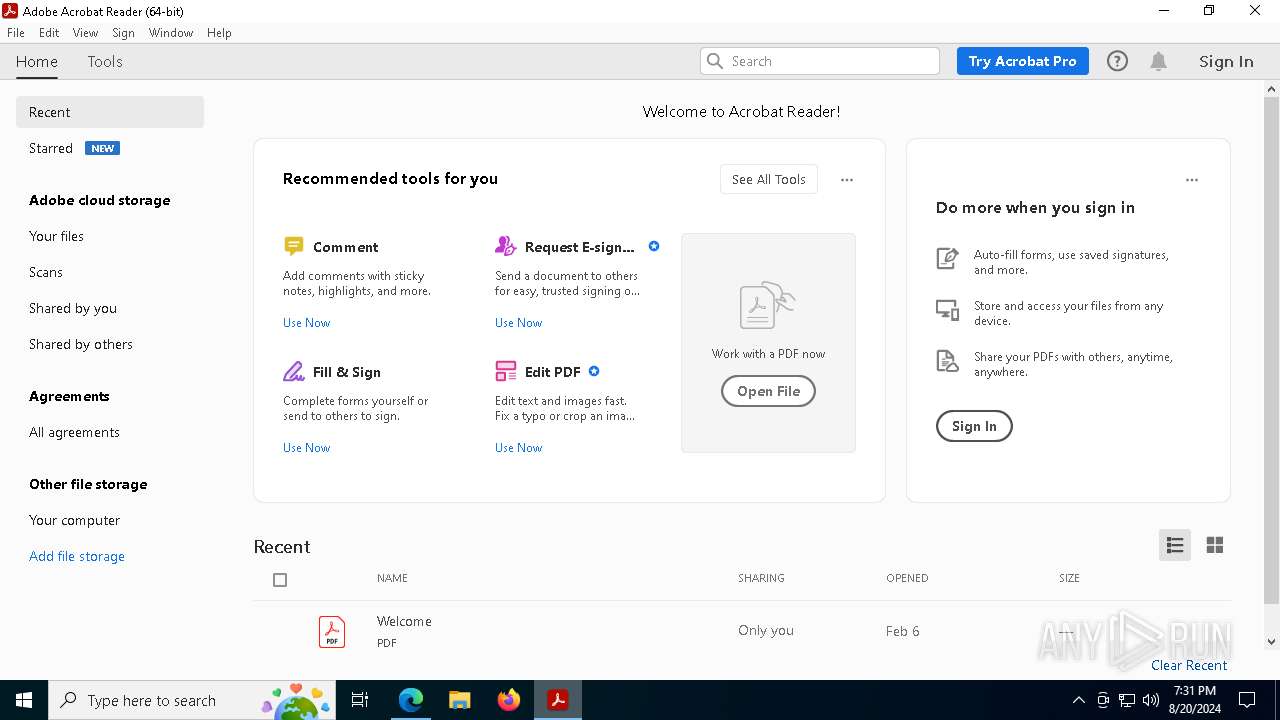
| File name: | Reader_en_install.exe |
| Full analysis: | https://app.any.run/tasks/36ed461c-b312-44ec-b62e-55736ac9c47a |
| Verdict: | Malicious activity |
| Analysis date: | August 20, 2024, 19:30:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 1FA2DDD09795C4922BFA0DB99988BF7F |
| SHA1: | 4FD7ABAE61C25E7BD65CA9FF6A3B3F2F51756264 |
| SHA256: | 689E094091AB3EA17171B9529B308C4CB40412309AC75062F74F9DC43E8F613A |
| SSDEEP: | 49152:JB51ZQjPFFa2CEMErggmZbvY9FbMsdSKm3eHuTE3iLL9jRVSoFvIOJe9bg4dLsFu:OjP6EVgnvqQ+4eOflFgYWjsdLTSnV8Ab |
MALICIOUS
Scans artifacts that could help determine the target
- Reader_en_install.exe (PID: 6752)
Create files in the Startup directory
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
SUSPICIOUS
Reads the date of Windows installation
- Reader_en_install.exe (PID: 6752)
Drops the executable file immediately after the start
- Reader_en_install.exe (PID: 6752)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Reads Microsoft Outlook installation path
- Reader_en_install.exe (PID: 6752)
Reads security settings of Internet Explorer
- Reader_en_install.exe (PID: 6752)
- Reader_en_install.exe (PID: 6828)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Application launched itself
- Reader_en_install.exe (PID: 6752)
Checks Windows Trust Settings
- Reader_en_install.exe (PID: 6828)
- Reader_en_install.exe (PID: 6752)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Reads Internet Explorer settings
- Reader_en_install.exe (PID: 6752)
Executable content was dropped or overwritten
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
- Reader_en_install.exe (PID: 6752)
The process creates files with name similar to system file names
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
The process verifies whether the antivirus software is installed
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
- McCHSvc.exe (PID: 6872)
- McCHSvc.exe (PID: 7028)
- SSScheduler.exe (PID: 6640)
Starts application with an unusual extension
- Reader_en_install.exe (PID: 6828)
Malware-specific behavior (creating "System.dll" in Temp)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Process drops legitimate windows executable
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Adds/modifies Windows certificates
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Searches for installed software
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Executes as Windows Service
- McCHSvc.exe (PID: 7028)
Creates a software uninstall entry
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
INFO
Checks supported languages
- Reader_en_install.exe (PID: 6752)
- Reader_en_install.exe (PID: 6828)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
- McCHSvc.exe (PID: 6872)
- SSScheduler.exe (PID: 6640)
- McCHSvc.exe (PID: 7028)
- acrobat_sl.exe (PID: 7320)
Create files in a temporary directory
- Reader_en_install.exe (PID: 6752)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Creates files or folders in the user directory
- Reader_en_install.exe (PID: 6752)
- Reader_en_install.exe (PID: 6828)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Reads the machine GUID from the registry
- Reader_en_install.exe (PID: 6828)
- Reader_en_install.exe (PID: 6752)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Reads the computer name
- Reader_en_install.exe (PID: 6752)
- Reader_en_install.exe (PID: 6828)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
- McCHSvc.exe (PID: 6872)
- McCHSvc.exe (PID: 7028)
Process checks computer location settings
- Reader_en_install.exe (PID: 6752)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Process checks Internet Explorer phishing filters
- Reader_en_install.exe (PID: 6752)
Reads the software policy settings
- Reader_en_install.exe (PID: 6828)
- Reader_en_install.exe (PID: 6752)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
Checks proxy server information
- Reader_en_install.exe (PID: 6752)
- Reader_en_install.exe (PID: 6828)
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
UPX packer has been detected
- Reader_en_install.exe (PID: 6752)
Creates files in the program directory
- BEB3B08B-FD79-458C-9905-C9E6EB11B47A (PID: 6572)
- SSScheduler.exe (PID: 6640)
- McCHSvc.exe (PID: 7028)
Application launched itself
- Acrobat.exe (PID: 1432)
- AcroCEF.exe (PID: 7640)
- msedge.exe (PID: 5300)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5300)
- Reader_en_install.exe (PID: 6752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:08 11:44:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.35 |
| CodeSize: | 1417216 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 3035136 |
| EntryPoint: | 0x43f400 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.761 |
| ProductVersionNumber: | 2.0.0.761 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Inc |
| FileDescription: | Adobe Download Manager |
| FileVersion: | 2.0.0.761s |
| InternalName: | Adobe Download Manager |
| LegalCopyright: | Copyright 2019 Adobe Inc. All rights reserved. |
| OriginalFileName: | Adobe Download Manager |
| ProductName: | Adobe Download Manager |
| ProductVersion: | 2.0.0.761s |
Total processes
178
Monitored processes
41
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2364 --field-trial-handle=2372,i,17851224025576143532,4291371466125055245,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | Reader_en_install.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2736 --field-trial-handle=2372,i,17851224025576143532,4291371466125055245,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://get.adobe.com/reader/completion/adm/?exitcode=-1&type=install&appId=300&preinstalled=1&workflow=64 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | Reader_en_install.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6028 | "C:\WINDOWS\system32\explorer.exe" | C:\Windows\SysWOW64\explorer.exe | — | Reader_en_install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6252 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 6496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x31c,0x320,0x324,0x30c,0x32c,0x7fffd36b5fd8,0x7fffd36b5fe4,0x7fffd36b5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6572 | "C:\Users\admin\AppData\Local\Adobe\4C7442D7-B6D4-4C23-AC45-9DE8A31E5AF2\62CC6878-3ACB-4127-A564-0C24D535472E\BEB3B08B-FD79-458C-9905-C9E6EB11B47A" /S /noeula /Affid=1641 /rid=10 /source="AdobeReader" | C:\Users\admin\AppData\Local\Adobe\4C7442D7-B6D4-4C23-AC45-9DE8A31E5AF2\62CC6878-3ACB-4127-A564-0C24D535472E\BEB3B08B-FD79-458C-9905-C9E6EB11B47A | Reader_en_install.exe | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee Security Scan Plus Installer Exit code: 0 Version: 4.1.482 Modules
| |||||||||||||||
| 6640 | "C:\Program Files (x86)\McAfee Security Scan\4.1.482\SSScheduler.exe" | C:\Program Files (x86)\McAfee Security Scan\4.1.482\SSScheduler.exe | — | BEB3B08B-FD79-458C-9905-C9E6EB11B47A | |||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee Security Scanner Scheduler Version: 4,1,482,0 Modules
| |||||||||||||||
| 6752 | "C:\Users\admin\AppData\Local\Temp\Reader_en_install.exe" | C:\Users\admin\AppData\Local\Temp\Reader_en_install.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Inc Integrity Level: MEDIUM Description: Adobe Download Manager Exit code: 0 Version: 2.0.0.761s Modules
| |||||||||||||||
Total events
47 805
Read events
47 590
Write events
200
Delete events
15
Modification events
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6752) Reader_en_install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6572) BEB3B08B-FD79-458C-9905-C9E6EB11B47A | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6572) BEB3B08B-FD79-458C-9905-C9E6EB11B47A | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6572) BEB3B08B-FD79-458C-9905-C9E6EB11B47A | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
15
Suspicious files
214
Text files
94
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\Local\Adobe\4C7442D7-B6D4-4C23-AC45-9DE8A31E5AF2\62CC6878-3ACB-4127-A564-0C24D535472E\BEB3B08B-FD79-458C-9905-C9E6EB11B47A.aamdownload | — | |
MD5:— | SHA256:— | |||
| 6828 | Reader_en_install.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_F47D0D738DC3C3984730C80B8D674D25 | der | |
MD5:2BE722C9B7D0954179C46FBE1548D351 | SHA256:E1018009798F92E21E15FDF20AD61AFEEF4BF48B1A84320F2099B9C2F6BE5307 | |||
| 6828 | Reader_en_install.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_F47D0D738DC3C3984730C80B8D674D25 | binary | |
MD5:452F253E18E489F35D8346814845C5FB | SHA256:937102BAD63902F0ABE3502147865E453FC2E44F421E52760743DBC1EB1BE131 | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\bxf0ivf[2].js | text | |
MD5:CFE609917C9E7D4EED2C80563DED171B | SHA256:AD84B43FFD121E46AC4D2FA817B5863E4802C523BC3FB5E864DB28B3DB0E2514 | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\d[1] | woff | |
MD5:DF0CD5EDE266E9EA694C3D28209FCE9F | SHA256:5ECD3C64E4C0D1A51D13E2762BECB9E7DA2ACD30D670058A6B16761BE3E017DB | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\p[1].gif | image | |
MD5:81144D75B3E69E9AA2FA3E9D83A64D03 | SHA256:9B9265C69A5CC295D1AB0D04E0273B3677DB1A6216CE2CCF4EFC8C277ED84B39 | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\d[2] | woff | |
MD5:590A9EEBC0AC0BA776529CBA1D5B718A | SHA256:28195F698F74D701F5B253495756F7ECD70C50047C1F795952587E6F3E742B19 | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | der | |
MD5:EF251242C68DA9415B1B879B97034419 | SHA256:7623A12C25C58C08312B302C0A268CBA235F17E16B37BA56991AE5C5F2D47009 | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:E38596E778EFF92E3DF91DD2EA1C68F6 | SHA256:5B4F8DD7203053C5B555613E15AAA5881AD89FEF5F05EAB393C252DEF7735120 | |||
| 6752 | Reader_en_install.exe | C:\Users\admin\AppData\Local\Temp\Adobe_ADMLogs\Adobe_ADM.log | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
106
DNS requests
119
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6828 | Reader_en_install.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6752 | Reader_en_install.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
6828 | Reader_en_install.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA5uMvyw4DoMCyvAS1byA4s%3D | unknown | — | — | whitelisted |
2228 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6828 | Reader_en_install.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6752 | Reader_en_install.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDH2emIjQ%2BXpUMoJ6Xg%3D%3D | unknown | — | — | whitelisted |
6752 | Reader_en_install.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
6752 | Reader_en_install.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDEfg2FeKsgAIORn6EQ%3D%3D | unknown | — | — | whitelisted |
6572 | BEB3B08B-FD79-458C-9905-C9E6EB11B47A | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS1ltXHf0Gu7UbTwUFXQxqswh7XKQQUrrrnB8N4tGHsArqIlJV3X9NjtKoCEHyfTd%2Fqg0L%2Ff%2BJPDnmJnMc%3D | unknown | — | — | whitelisted |
1432 | Acrobat.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3304 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5500 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6828 | Reader_en_install.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6752 | Reader_en_install.exe | 184.24.77.156:443 | use.typekit.net | Akamai International B.V. | DE | unknown |
6752 | Reader_en_install.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6752 | Reader_en_install.exe | 23.213.164.167:443 | geo-dc.adobe.com | AKAMAI-AS | DE | unknown |
6752 | Reader_en_install.exe | 54.74.179.44:443 | rdc.adobe.io | AMAZON-02 | IE | unknown |
6752 | Reader_en_install.exe | 184.24.77.146:443 | p.typekit.net | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
use.typekit.net |
| whitelisted |
geo-dc.adobe.com |
| whitelisted |
rdc.adobe.io |
| whitelisted |
p.typekit.net |
| shared |
dlmping2.adobe.com |
| whitelisted |
platformdl.adobe.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |