| URL: | https://cdn.discordapp.com/attachments/357538837469069325/716045021933207592/Im_a_dolphin_trust_me_cip_cip.exe |
| Full analysis: | https://app.any.run/tasks/9a9696f0-1196-4a72-bcb0-ccb799775706 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 13:21:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5C763563F4BC735373FD0E11BC6C7976 |
| SHA1: | 77EB2B9DEDC4D5775C184988235CEE33612D02B5 |
| SHA256: | 686E07D2459157B7336190B2CEDCBFA4998D2F447558B099C8D2F1A2DDF96D67 |
| SSDEEP: | 3:N8cCWdy6//Xjal2nAaKUcWASJasHT4KWe5VkA:2cry6XXmkH3J8K75VJ |
MALICIOUS
Application was dropped or rewritten from another process
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 2116)
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 2788)
Loads dropped or rewritten executable
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
Actions looks like stealing of personal data
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
SUSPICIOUS
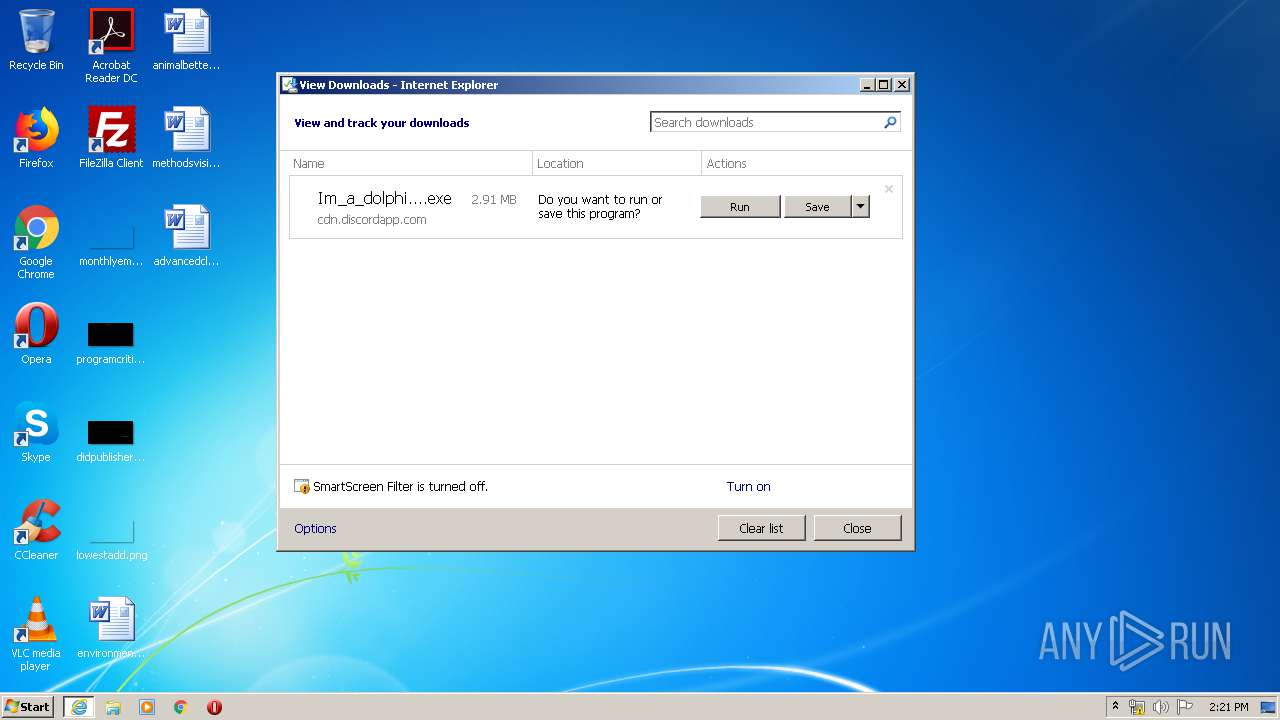
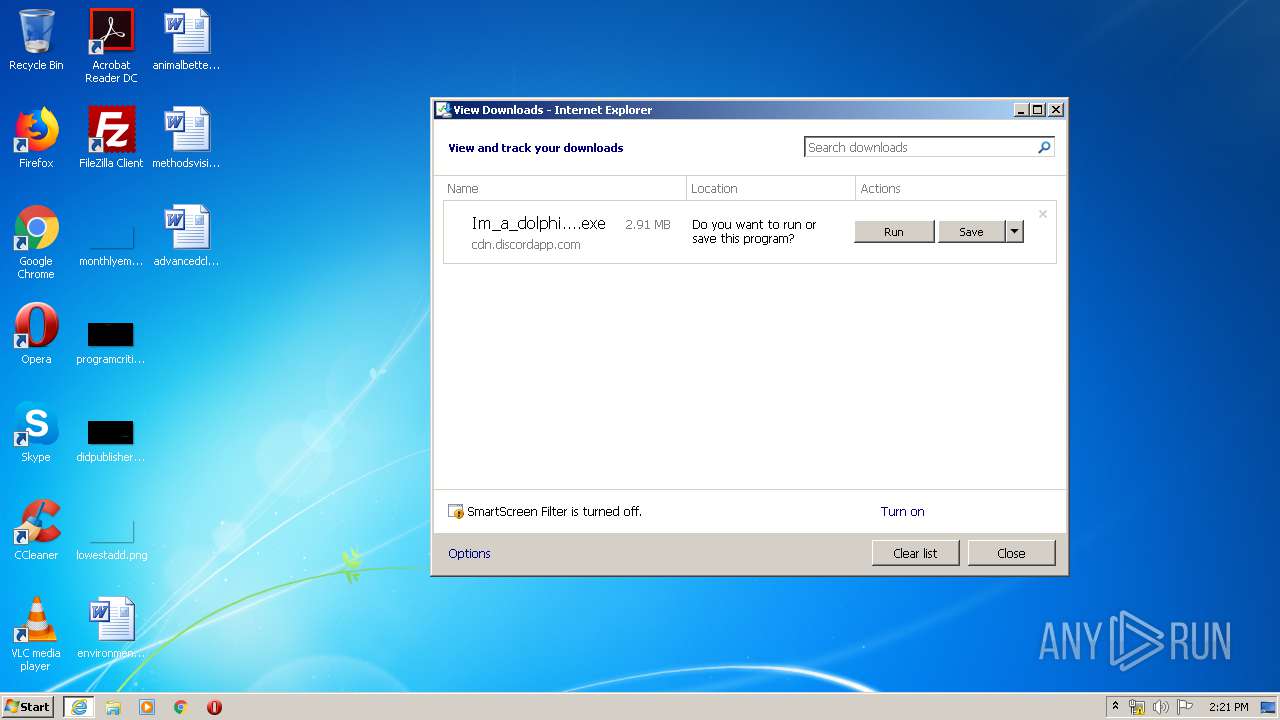
Executable content was dropped or overwritten
- iexplore.exe (PID: 960)
- iexplore.exe (PID: 2400)
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
Application launched itself
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 2116)
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
Cleans NTFS data-stream (Zone Identifier)
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 2116)
Reads Internet Cache Settings
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
Reads Environment values
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
Reads internet explorer settings
- Im_a_dolphin_trust_me_cip_cip.exe (PID: 1020)
INFO
Application launched itself
- iexplore.exe (PID: 960)
Reads Internet Cache Settings
- iexplore.exe (PID: 960)
- iexplore.exe (PID: 2400)
Changes internet zones settings
- iexplore.exe (PID: 960)
Creates files in the user directory
- iexplore.exe (PID: 2400)
Modifies the phishing filter of IE
- iexplore.exe (PID: 960)
Reads settings of System Certificates
- iexplore.exe (PID: 2400)
Adds / modifies Windows certificates
- iexplore.exe (PID: 960)
Changes settings of System certificates
- iexplore.exe (PID: 960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\Internet Explorer\iexplore.exe" https://cdn.discordapp.com/attachments/357538837469069325/716045021933207592/Im_a_dolphin_trust_me_cip_cip.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe" RSF /ppn:YWV4dQ0KChAjb3J1FQUI /ads:1 /mnl | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe | Im_a_dolphin_trust_me_cip_cip.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Lefehonubo Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2116 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe | — | iexplore.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Lefehonubo Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:960 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe" RSF /ppn:YWV4dQ0KChAjb3J1FQUI /ads:1 /_ShowProgress /mnl | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe | — | Im_a_dolphin_trust_me_cip_cip.exe | |||||||||||
User: admin Company: Integrity Level: HIGH Description: Lefehonubo Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
4 719
Read events
1 106
Write events
2 428
Delete events
1 185
Modification events
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1208488908 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30815877 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
14
Text files
71
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_979AB563CEB98F2581C14ED89B8957D4 | — | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9F74.tmp | — | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9F75.tmp | — | |
MD5:— | SHA256:— | |||
| 960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF16DF7317AAD0848C.TMP | — | |
MD5:— | SHA256:— | |||
| 960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Im_a_dolphin_trust_me_cip_cip.exe.ymbcers.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 1020 | Im_a_dolphin_trust_me_cip_cip.exe | C:\Users\admin\AppData\Local\Temp\0013136C.log | — | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_979AB563CEB98F2581C14ED89B8957D4 | der | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | binary | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\H5KIN0IE.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 312 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 312 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDJAnJQUGG0bwuno3m2vDJ8%3D | US | der | 279 b | whitelisted |
1020 | Im_a_dolphin_trust_me_cip_cip.exe | POST | 200 | 13.35.254.76:80 | http://www1.bekottff-sos.com/ | US | — | — | whitelisted |
1020 | Im_a_dolphin_trust_me_cip_cip.exe | POST | 200 | 13.35.254.45:80 | http://www1.bekottff-sos.com/ | US | — | — | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDJAnJQUGG0bwuno3m2vDJ8%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1020 | Im_a_dolphin_trust_me_cip_cip.exe | 13.35.254.45:80 | www1.bekottff-sos.com | — | US | malicious |
1020 | Im_a_dolphin_trust_me_cip_cip.exe | 13.35.254.76:80 | www1.bekottff-sos.com | — | US | malicious |
— | — | 13.35.254.76:80 | www1.bekottff-sos.com | — | US | malicious |
— | — | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2400 | iexplore.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
www1.bekottff-sos.com |
| whitelisted |