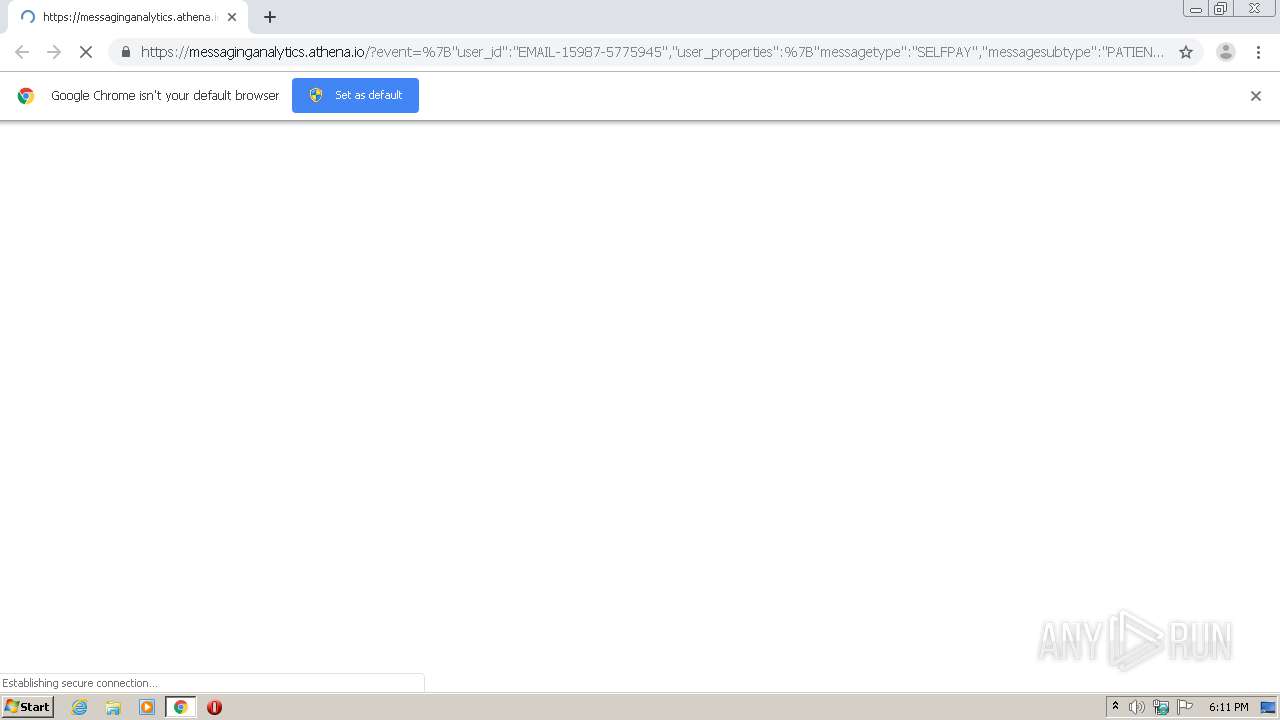
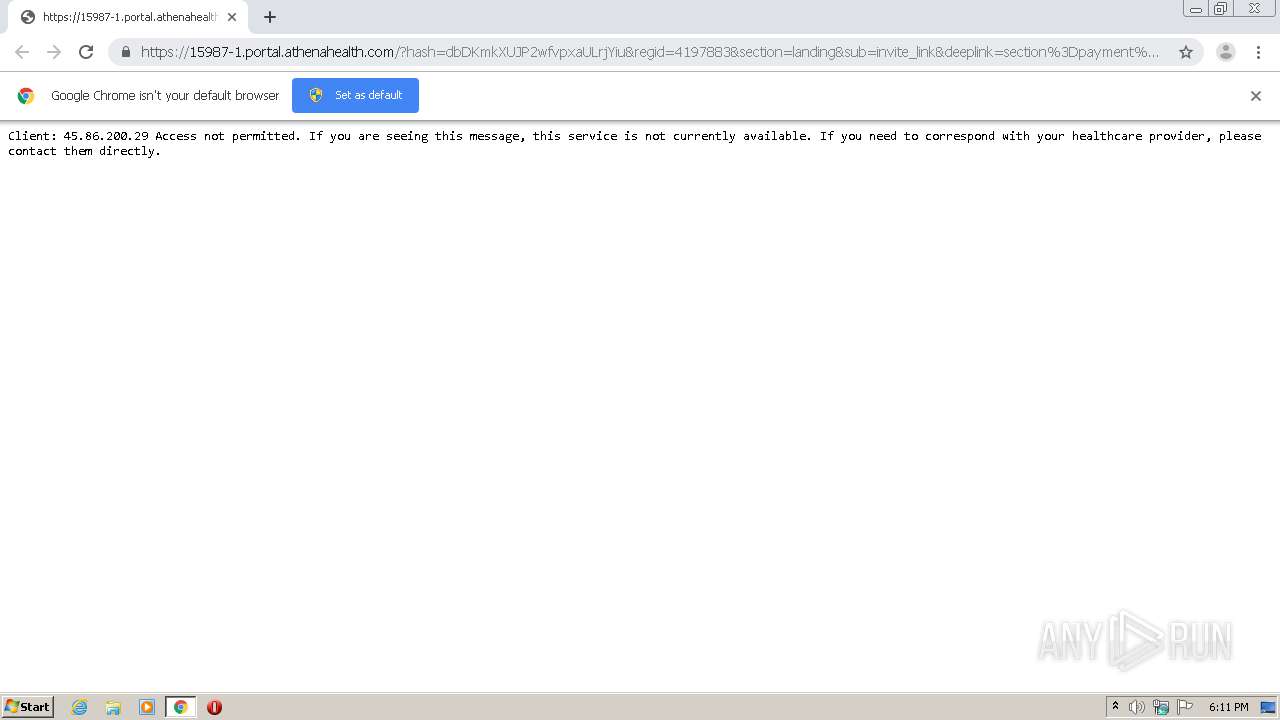
| URL: | https://messaginganalytics.athena.io/?event=%7B%22user_id%22:%22EMAIL-15987-5775945%22,%22user_properties%22:%7B%22messagetype%22:%22SELFPAY%22,%22messagesubtype%22:%22PATIENT%22,%22messageaudience%22:%22Default%22,%22tenant%22:%22Default%22,%22source%22:%22athenanet:generic_source%22,%22contextid%22:%2215987%22%7D,%22event_properties%22:%7B%22Messagetype%22:%22SELFPAY%22,%22Messagesubtype%22:%22PATIENT%22,%22Messageaudience%22:%22Default%22,%22Tenant%22:%22Default%22,%22Source%22:%22athenanet:generic_source%22,%22ContextID%22:%2215987%22,%22TemplateVersionNumber%22:%22e2cd3e10-f850-4416-b333-3ba4ab33d81b%22,%22ExperimentId%22:null,%22URL%22:%22https%3A%2F%2F15987-1.portal.athenahealth.com%2F%3Fhash%3DdbDKmkXUJP2wfvpxaULrjYiu%26amp%3Bregid%3D4197883%26amp%3Bsection%3Dlanding%26amp%3Bsub%3Dinvite%255Flink%26deeplink%3Dsection%253Dpayment%2526athenareferrer%253DSELFPAY%255FPATIENT%255FCTA%22%7D,%22event_type%22:%22EMAIL_LINK_CLICKED%22%7D&redirect=https://15987-1.portal.athenahealth.com/?hash=dbDKmkXUJP2wfvpxaULrjYiu®id=4197883§ion=landing&sub=invite%5Flink&deeplink=section%3Dpayment%26athenareferrer%3DSELFPAY%5FPATIENT%5FCTA |
| Full analysis: | https://app.any.run/tasks/f836c036-13d1-4ff9-accd-4cf57121975d |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2021, 18:10:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B709FC7AD05BF31F313E820DF6162BC9 |
| SHA1: | 3E381E45BC02755713ECA63C120378576C45616D |
| SHA256: | 686AF03F5DFCC95F537C3FDD16EB5C9778CE197EB9413690D4835D345224530E |
| SSDEEP: | 12:2/p4fvowWJrLPnHb9C93ucM+gwMrLPHb9i9d5u8R/sjZbh9ogTej/kzQh0aigPec:2/6fvoZBnHhS33g7HhyXz/OkuKjTUa |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2708)
Reads the hosts file
- chrome.exe (PID: 2184)
- chrome.exe (PID: 2708)
Application launched itself
- chrome.exe (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6179964765750515131 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=920 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7926233524751606298 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12844615391617201741 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://messaginganalytics.athena.io/?event=%7B%22user_id%22:%22EMAIL-15987-5775945%22,%22user_properties%22:%7B%22messagetype%22:%22SELFPAY%22,%22messagesubtype%22:%22PATIENT%22,%22messageaudience%22:%22Default%22,%22tenant%22:%22Default%22,%22source%22:%22athenanet:generic_source%22,%22contextid%22:%2215987%22%7D,%22event_properties%22:%7B%22Messagetype%22:%22SELFPAY%22,%22Messagesubtype%22:%22PATIENT%22,%22Messageaudience%22:%22Default%22,%22Tenant%22:%22Default%22,%22Source%22:%22athenanet:generic_source%22,%22ContextID%22:%2215987%22,%22TemplateVersionNumber%22:%22e2cd3e10-f850-4416-b333-3ba4ab33d81b%22,%22ExperimentId%22:null,%22URL%22:%22https%3A%2F%2F15987-1.portal.athenahealth.com%2F%3Fhash%3DdbDKmkXUJP2wfvpxaULrjYiu%26amp%3Bregid%3D4197883%26amp%3Bsection%3Dlanding%26amp%3Bsub%3Dinvite%255Flink%26deeplink%3Dsection%253Dpayment%2526athenareferrer%253DSELFPAY%255FPATIENT%255FCTA%22%7D,%22event_type%22:%22EMAIL_LINK_CLICKED%22%7D&redirect=https://15987-1.portal.athenahealth.com/?hash=dbDKmkXUJP2wfvpxaULrjYiu®id=4197883§ion=landing&sub=invite%5Flink&deeplink=section%3Dpayment%26athenareferrer%3DSELFPAY%5FPATIENT%5FCTA" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15129650214854327988 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1817761451658853995 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4378258323966742311 --mojo-platform-channel-handle=3532 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12949466368788854255,7157889469079647308,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13045718718540901397 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c3ea9d0,0x6c3ea9e0,0x6c3ea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
281
Read events
232
Write events
46
Delete events
3
Modification events
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2184-13261169467876875 |
Value: 259 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
9
Text files
48
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-605CD23C-888.pma | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ff142b97-9f5c-4f56-b1e8-4070a6f0bbf9.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF12c2db.TMP | text | |
MD5:74D4DB05A4D3E7263E8AE314DEDD8DF1 | SHA256:67BF9950E818713E054268D40BED61A22D324385CE98E89DDF406A405B870802 | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12c50d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2708 | chrome.exe | 65.9.58.120:443 | messaginganalytics.athena.io | AT&T Services, Inc. | US | whitelisted |
2708 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
2708 | chrome.exe | 142.250.185.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2708 | chrome.exe | 34.218.118.19:443 | api.amplitude.com | Amazon.com, Inc. | US | unknown |
2708 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2708 | chrome.exe | 208.78.141.21:443 | 15987-1.portal.athenahealth.com | Athenahealth | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
messaginganalytics.athena.io |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
api.amplitude.com |
| whitelisted |
15987-1.portal.athenahealth.com |
| unknown |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |