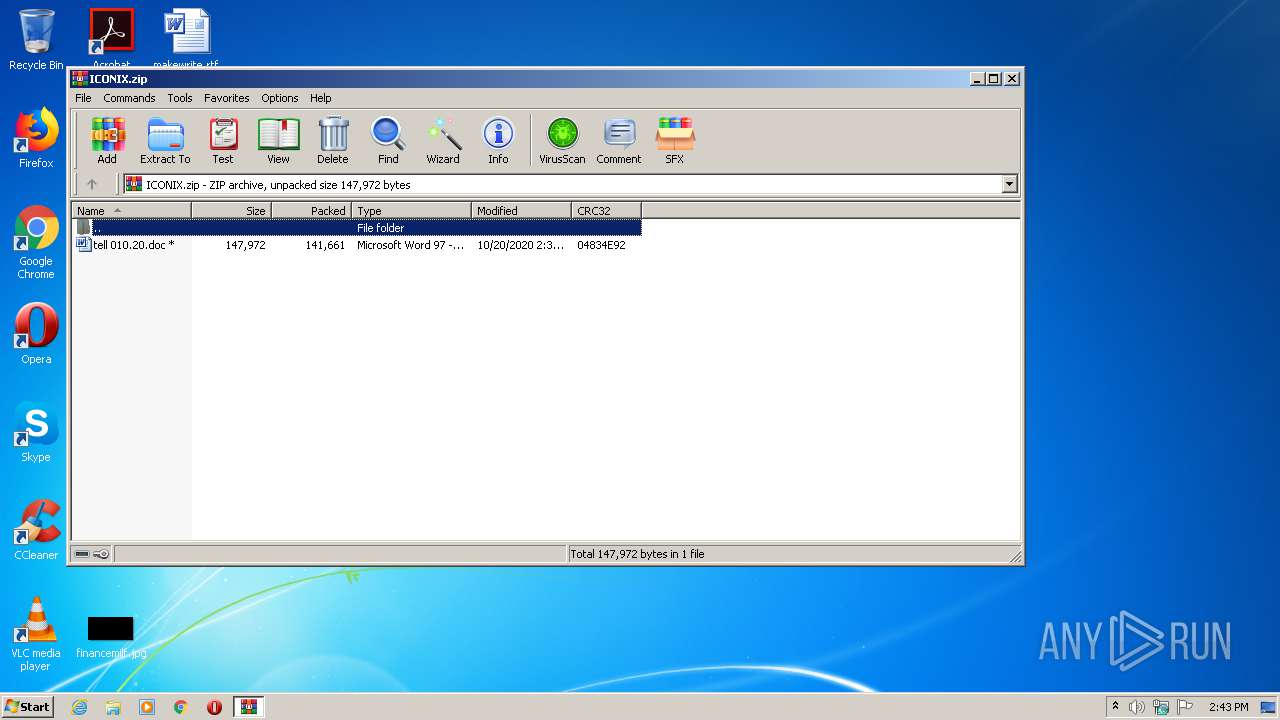
| File name: | ICONIX.zip |
| Full analysis: | https://app.any.run/tasks/2021fd1e-9e54-4b8c-96d8-5730aade3b7d |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 13:43:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D57439707C77FA49A7FE4CA32BF478E8 |
| SHA1: | EE53A48F4C376FFF0935FA582E071D9972112A3C |
| SHA256: | 6869BF7AF0214A488EDD62A0D1D92D0890639F9E714B7F681BD6162824E4A03C |
| SSDEEP: | 3072:GhbQa3ALIB4qIHYRGjxJ4zsxnDPOCu11tz55GmXA27IMn1PB:GIEBIYIxd4t15GmA27IMnpB |
MALICIOUS
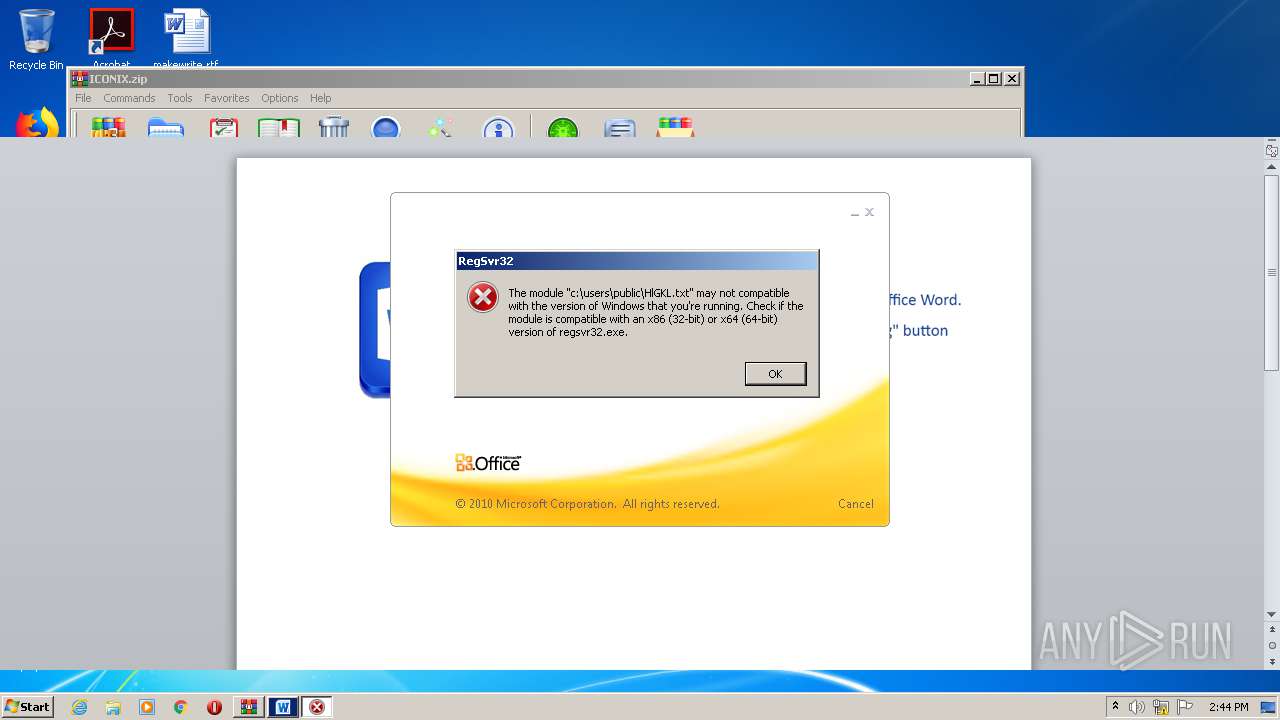
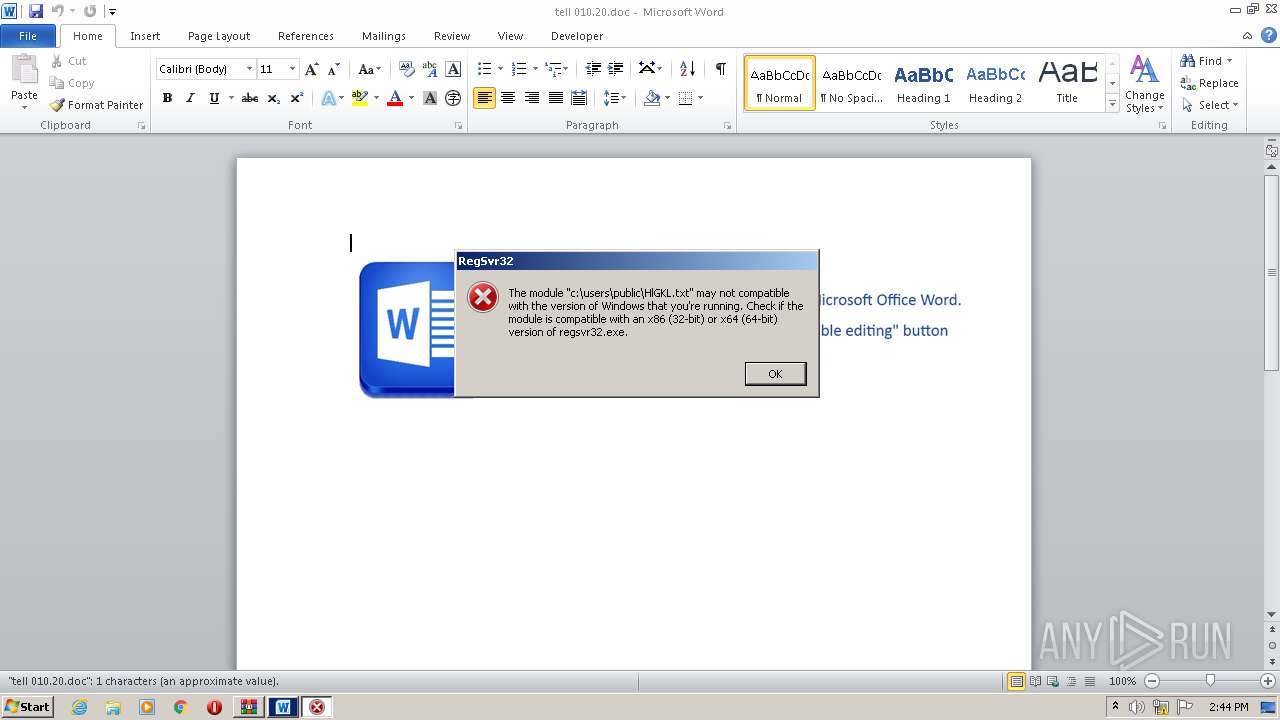
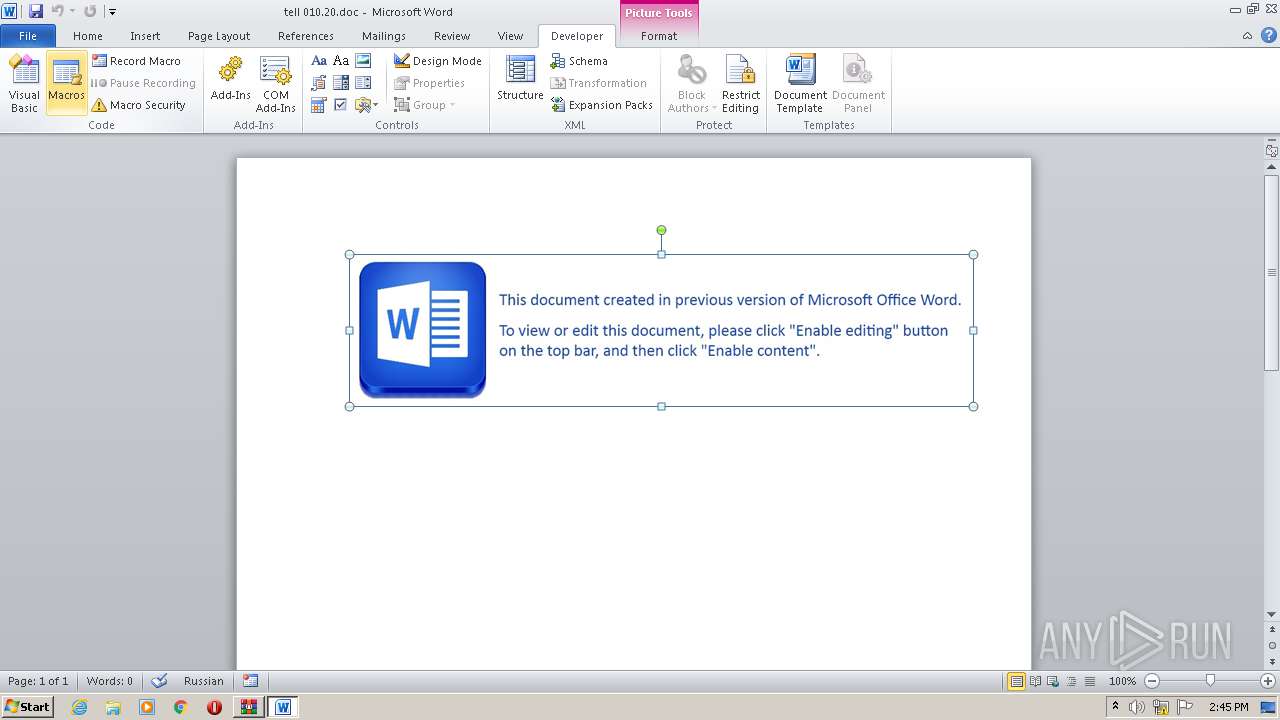
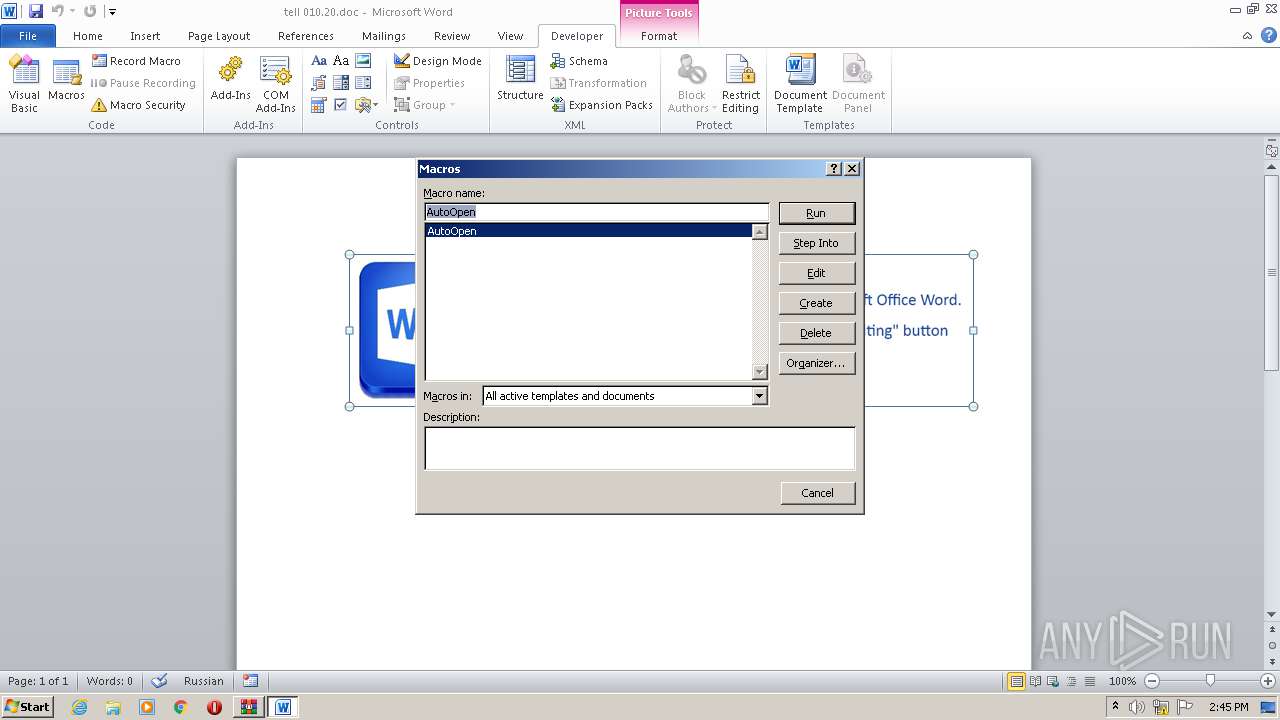
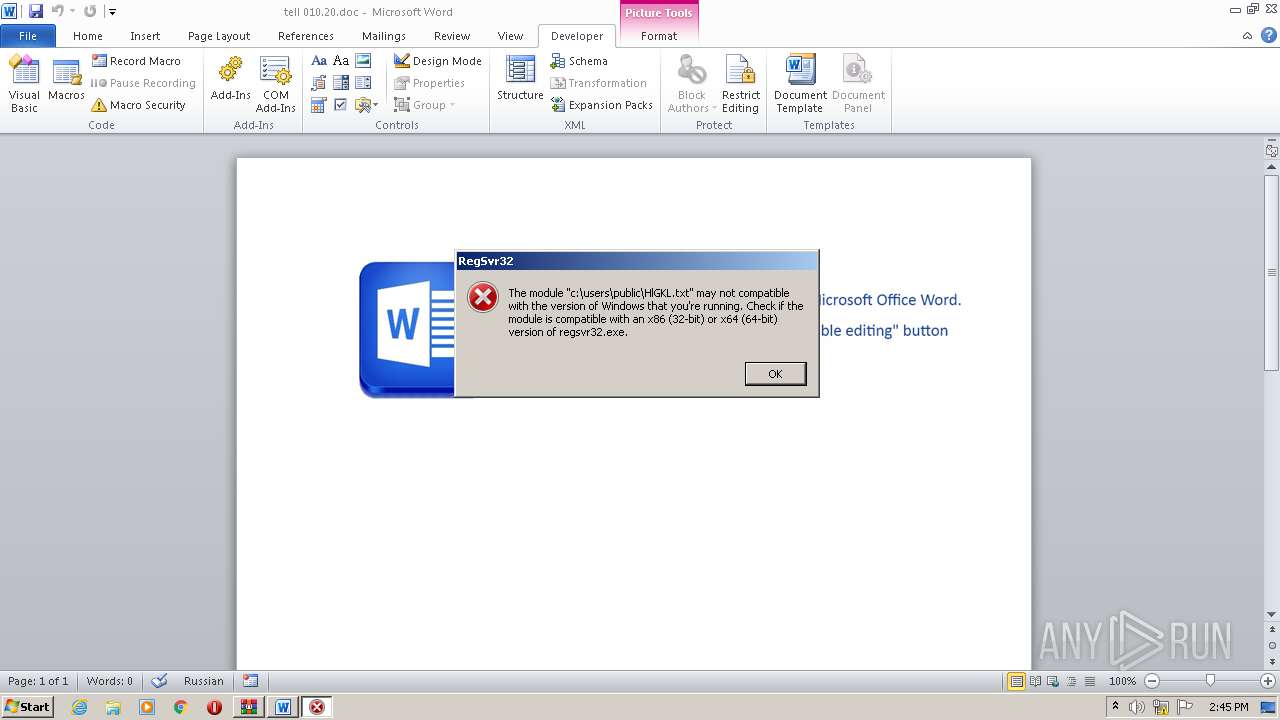
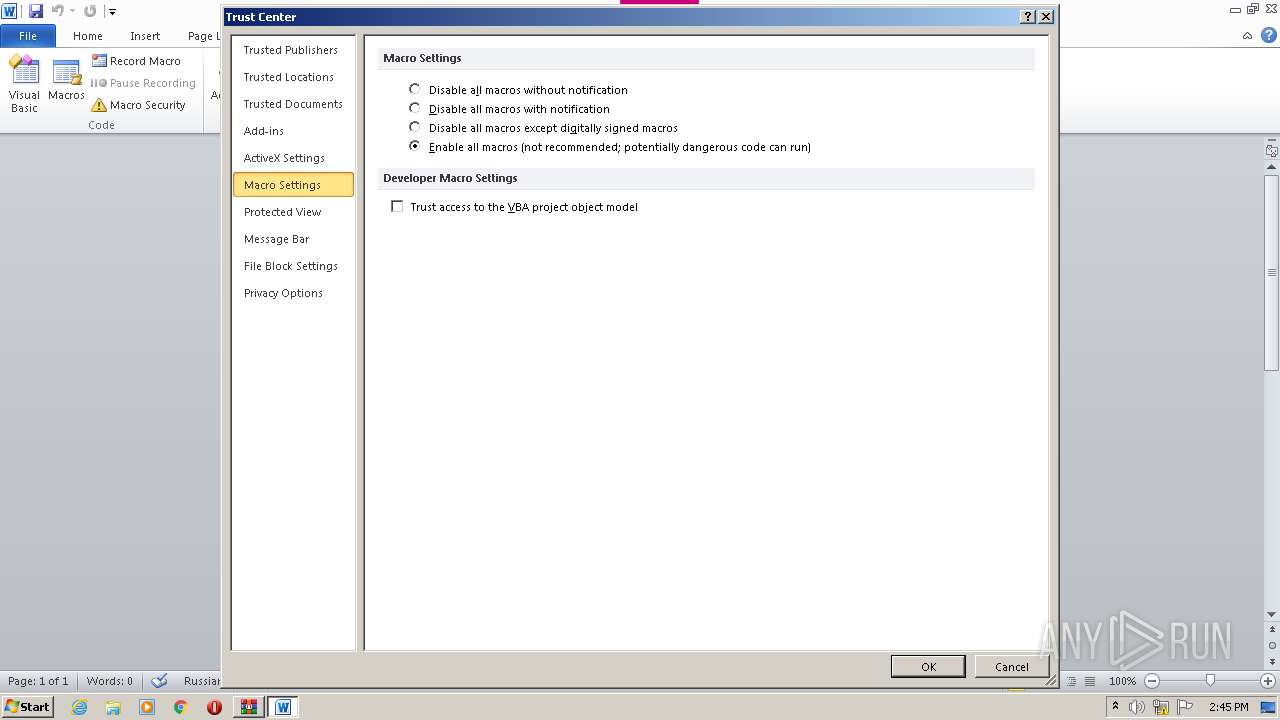
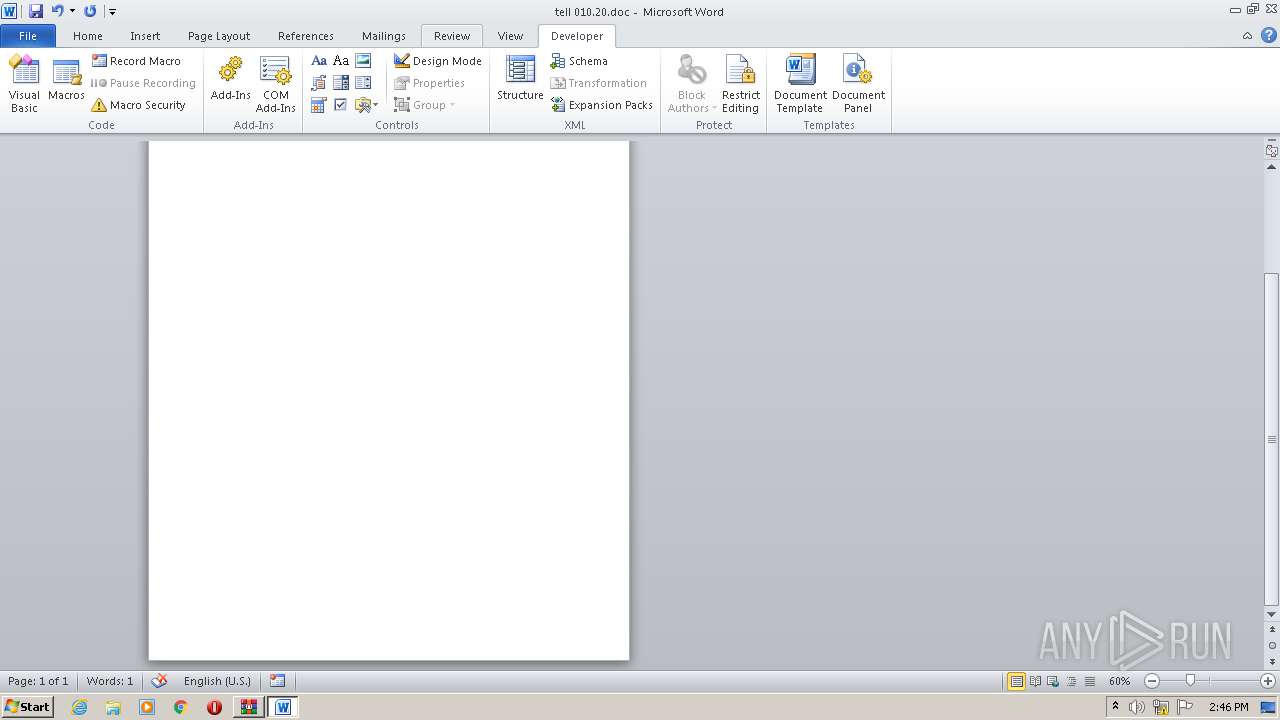
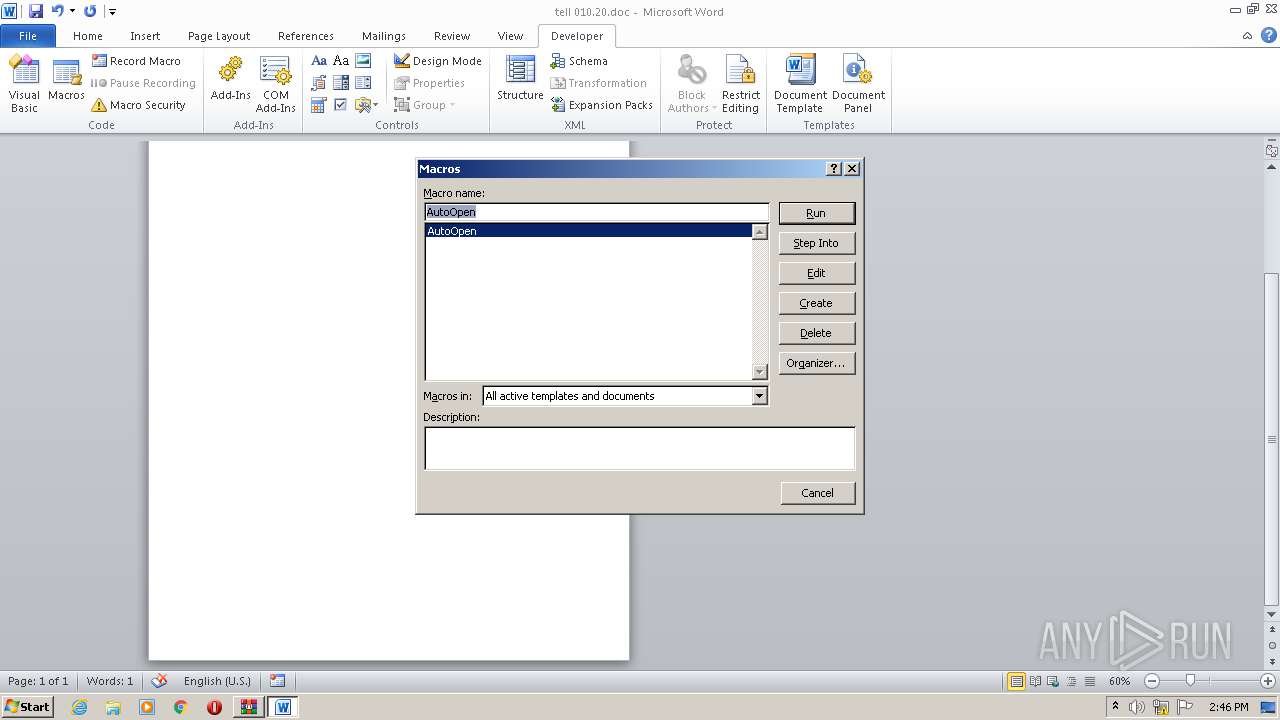
Registers / Runs the DLL via REGSVR32.EXE
- WINWORD.EXE (PID: 3536)
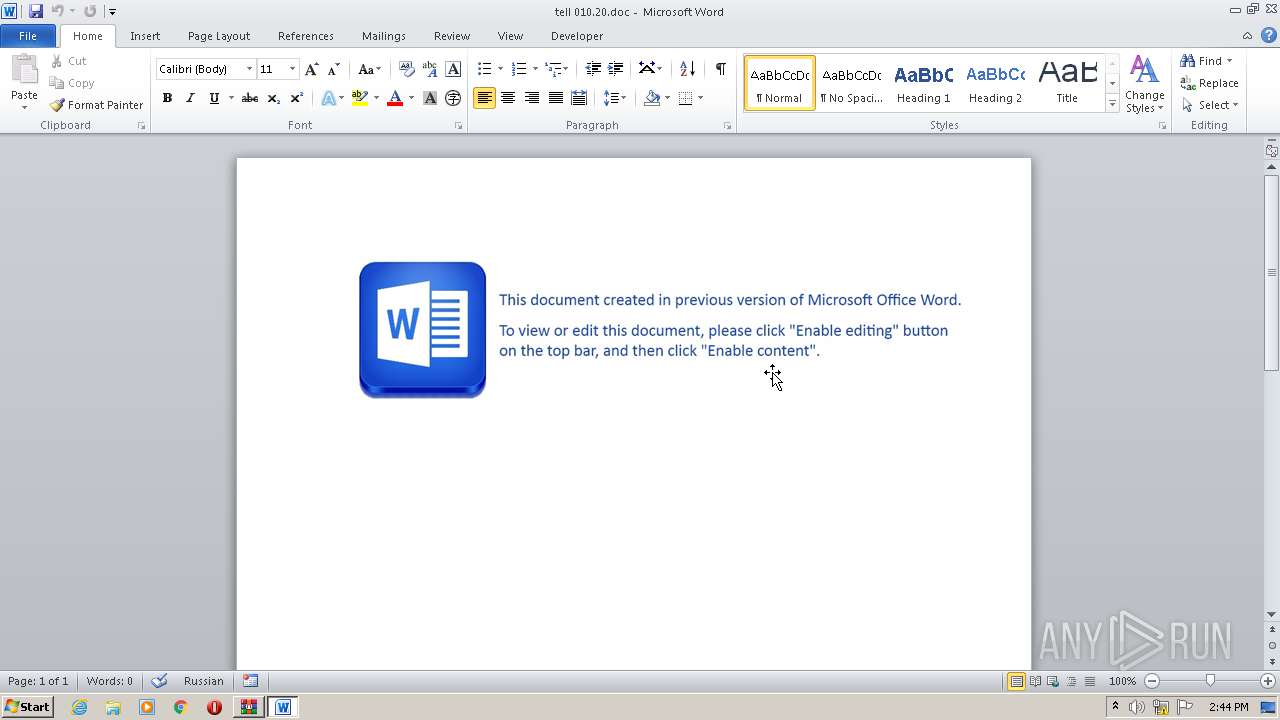
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3536)
SUSPICIOUS
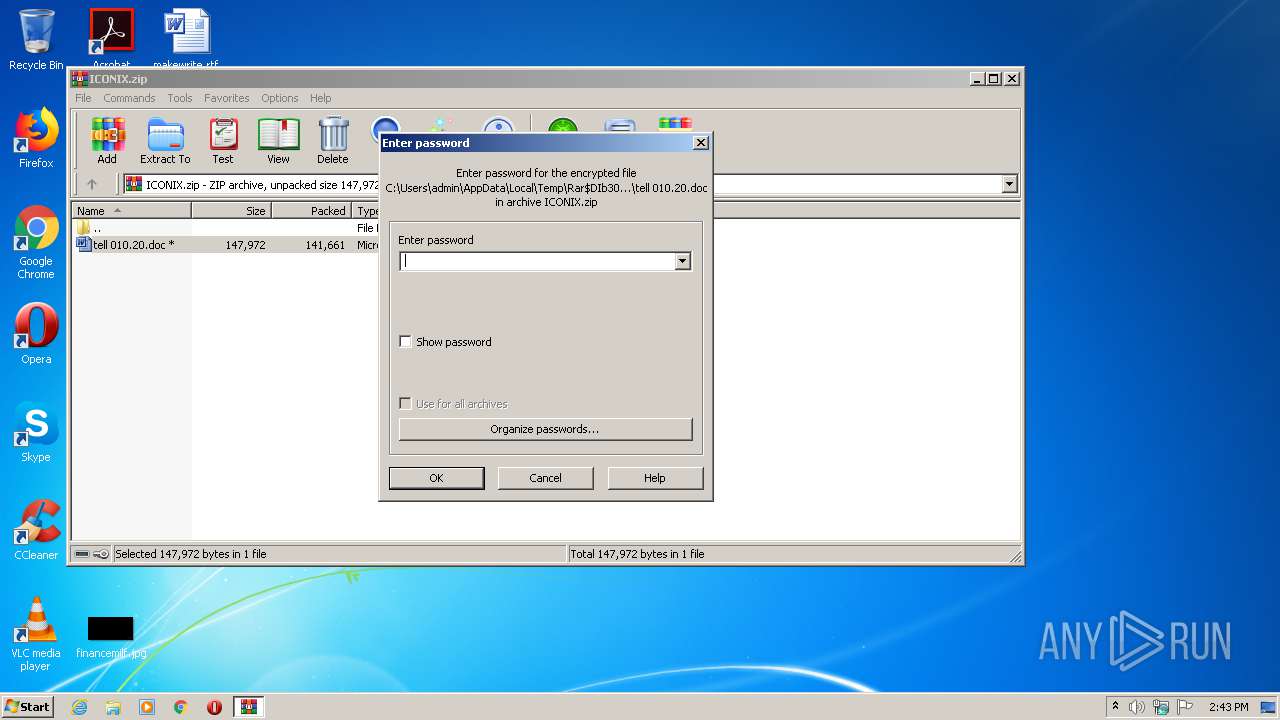
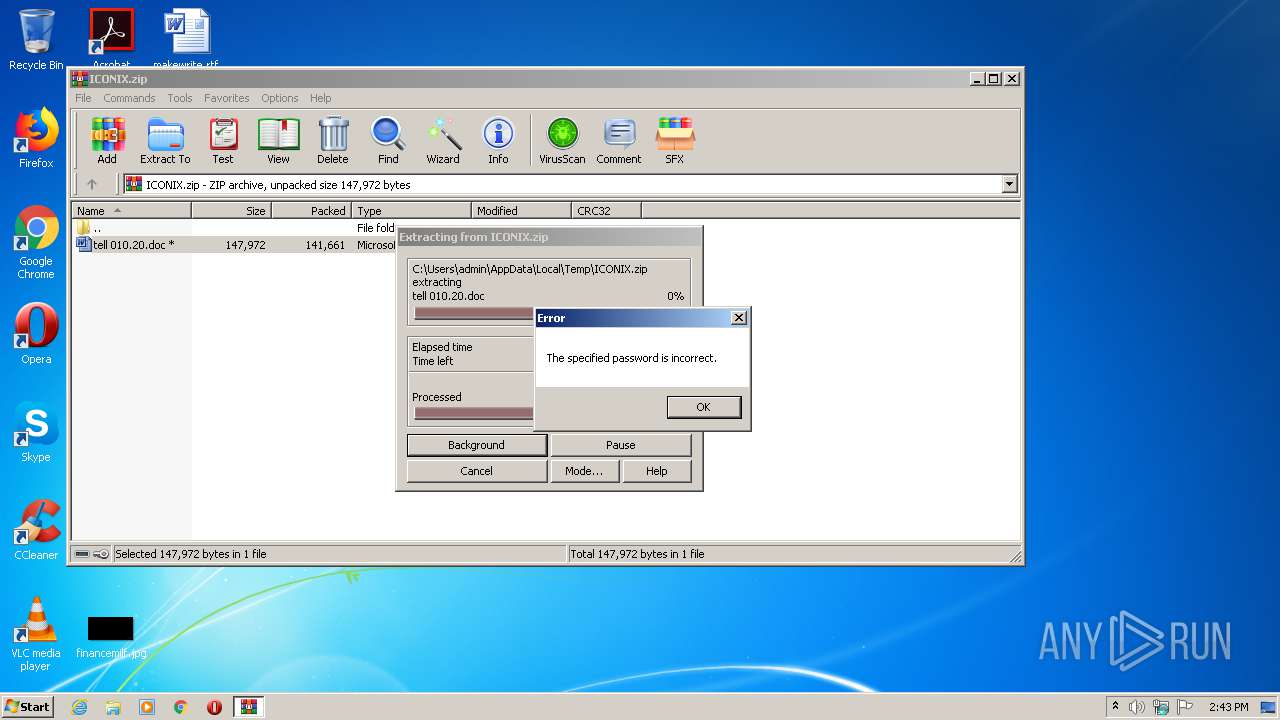
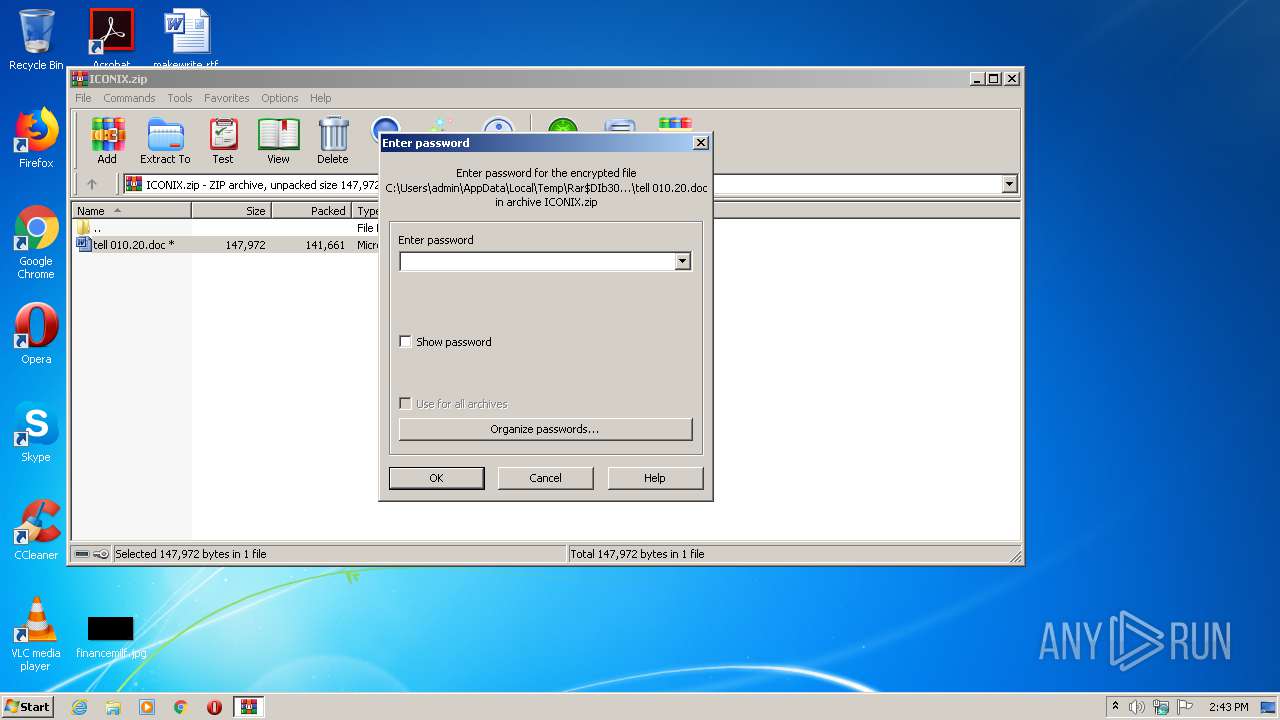
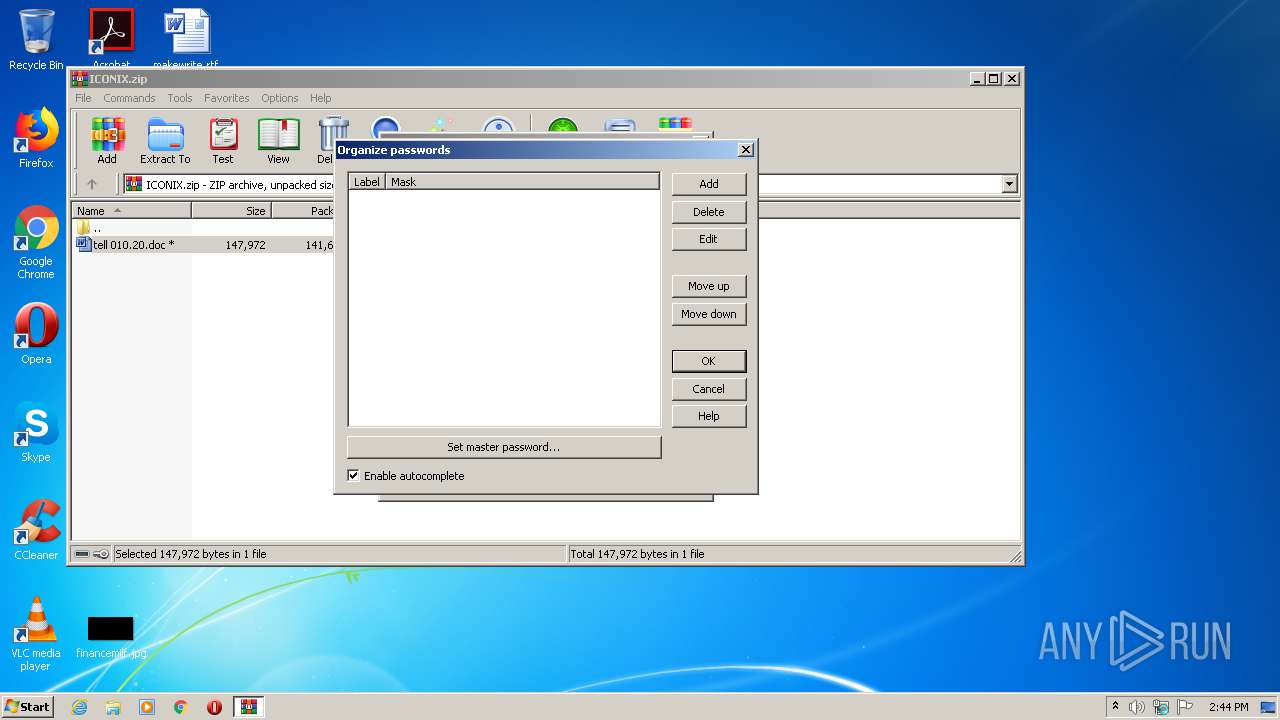
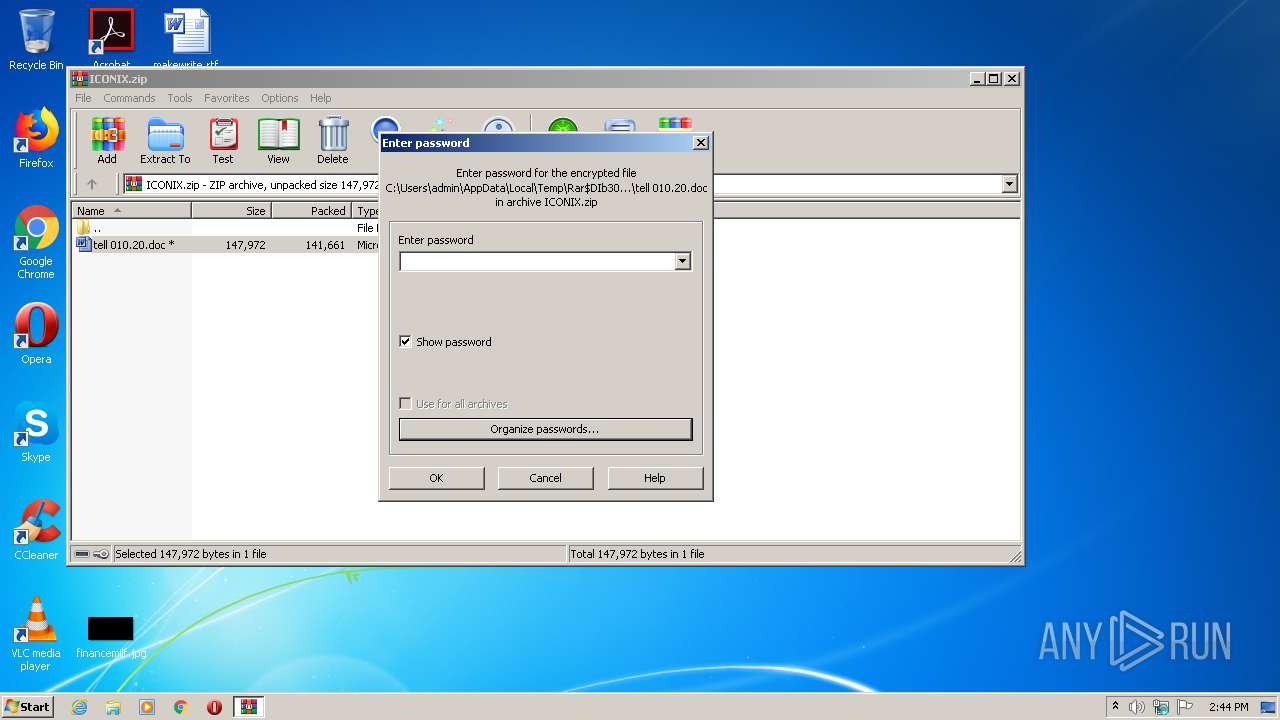
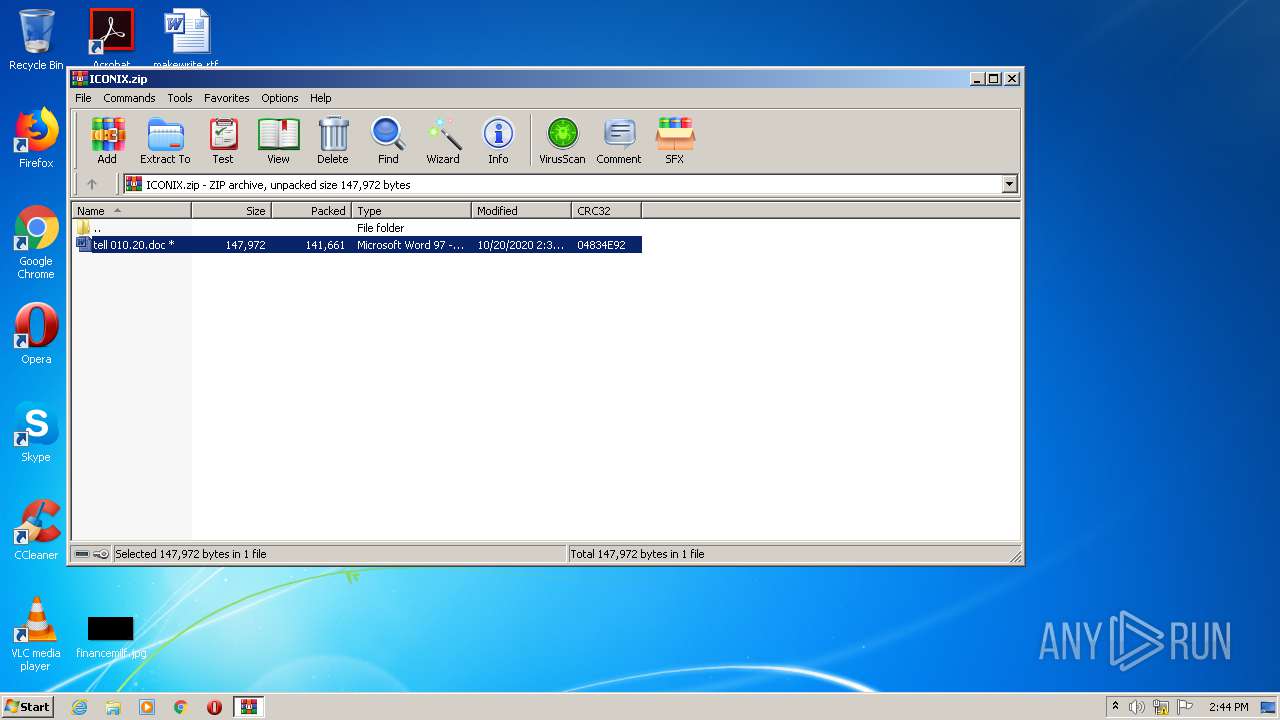
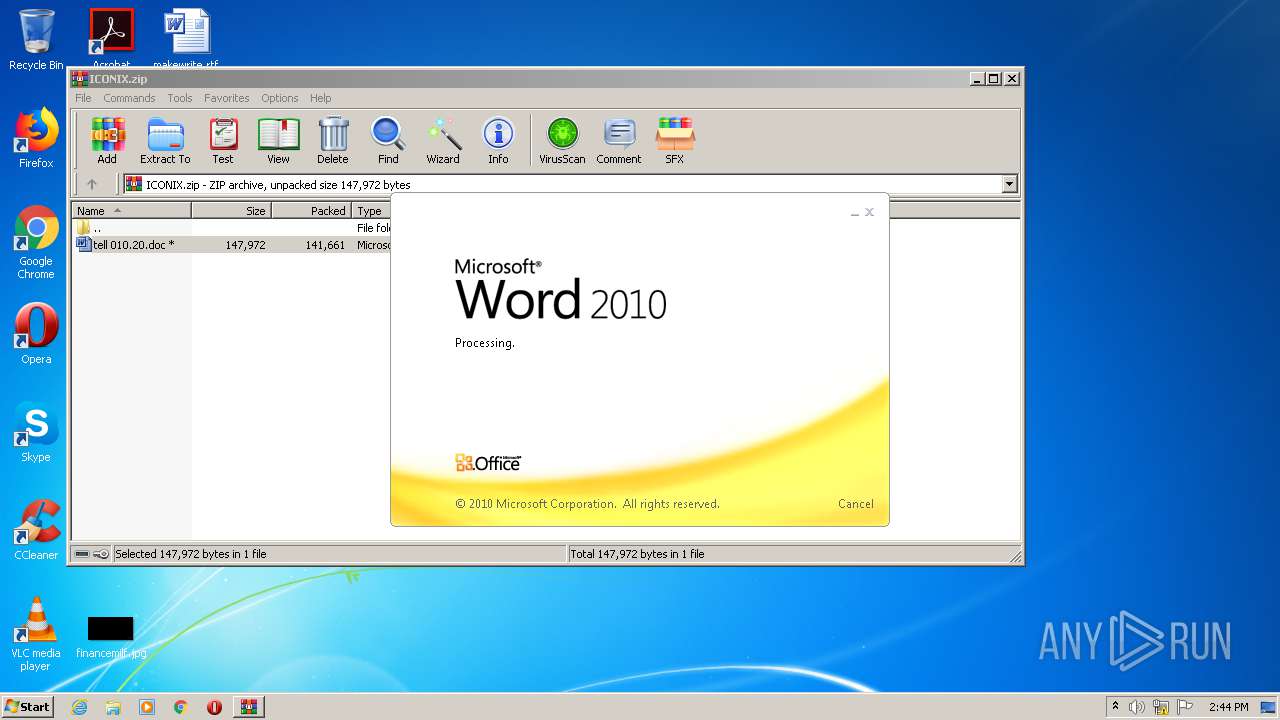
Starts Microsoft Office Application
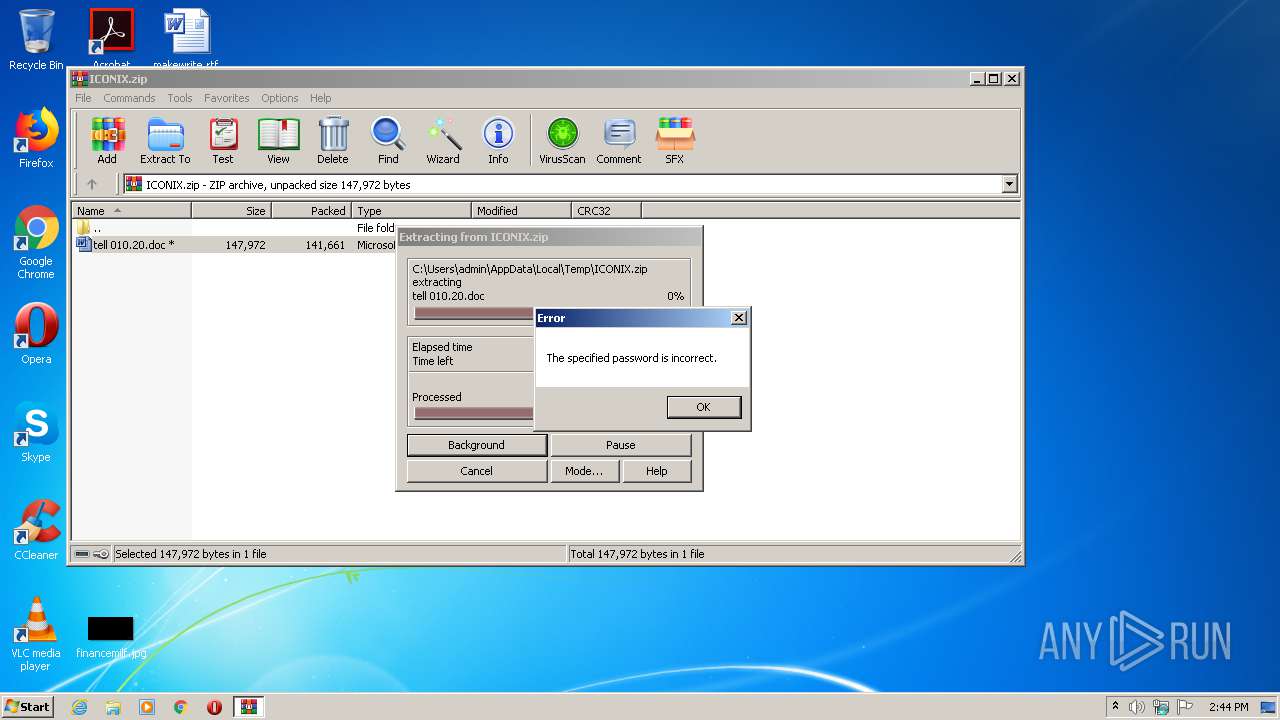
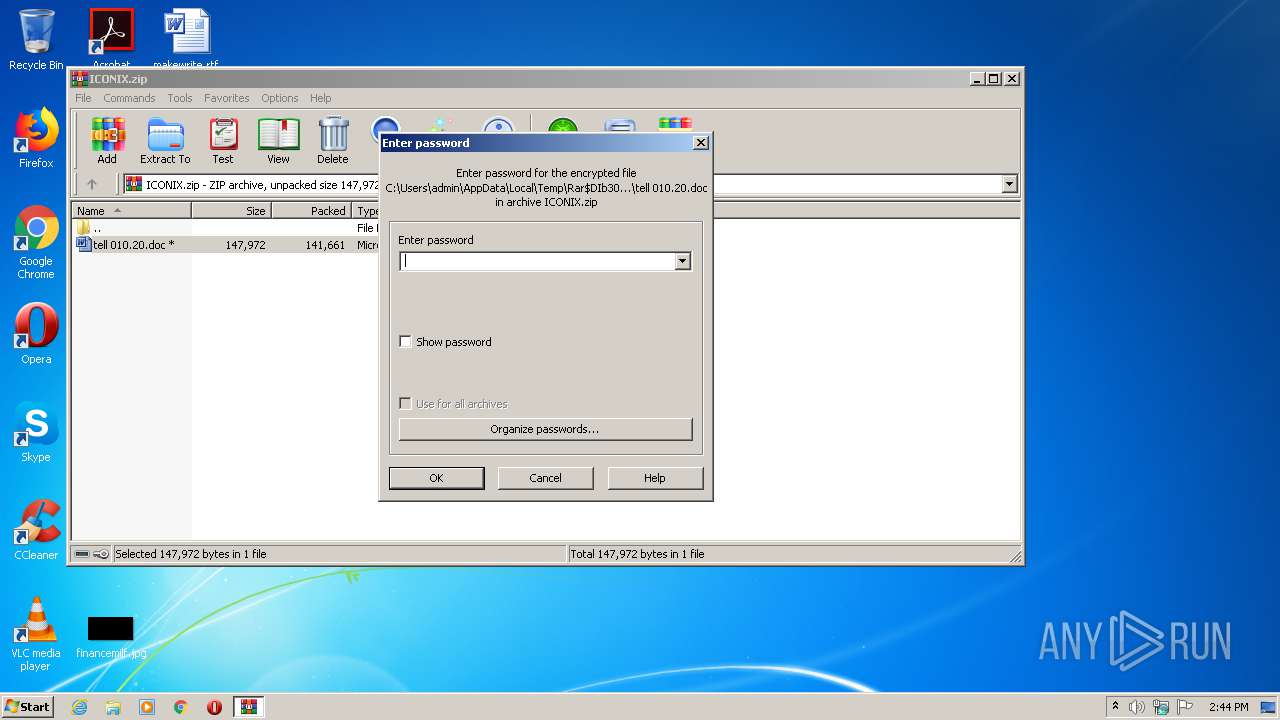
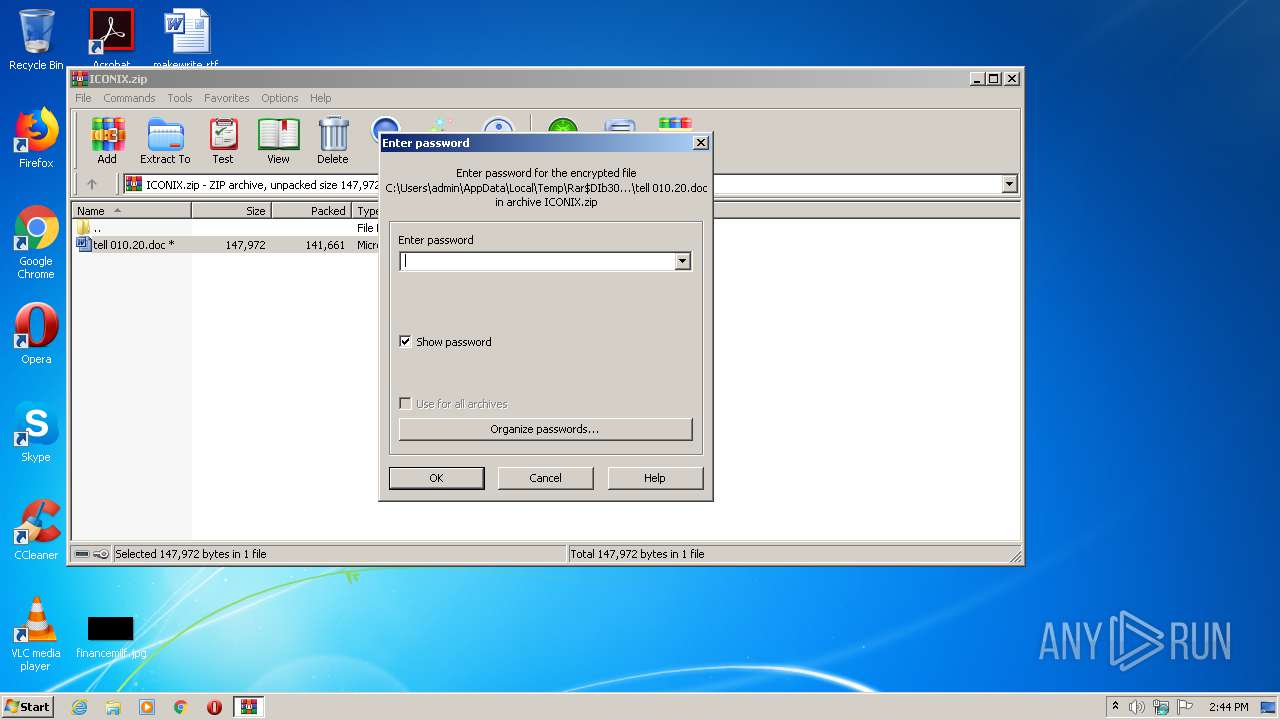
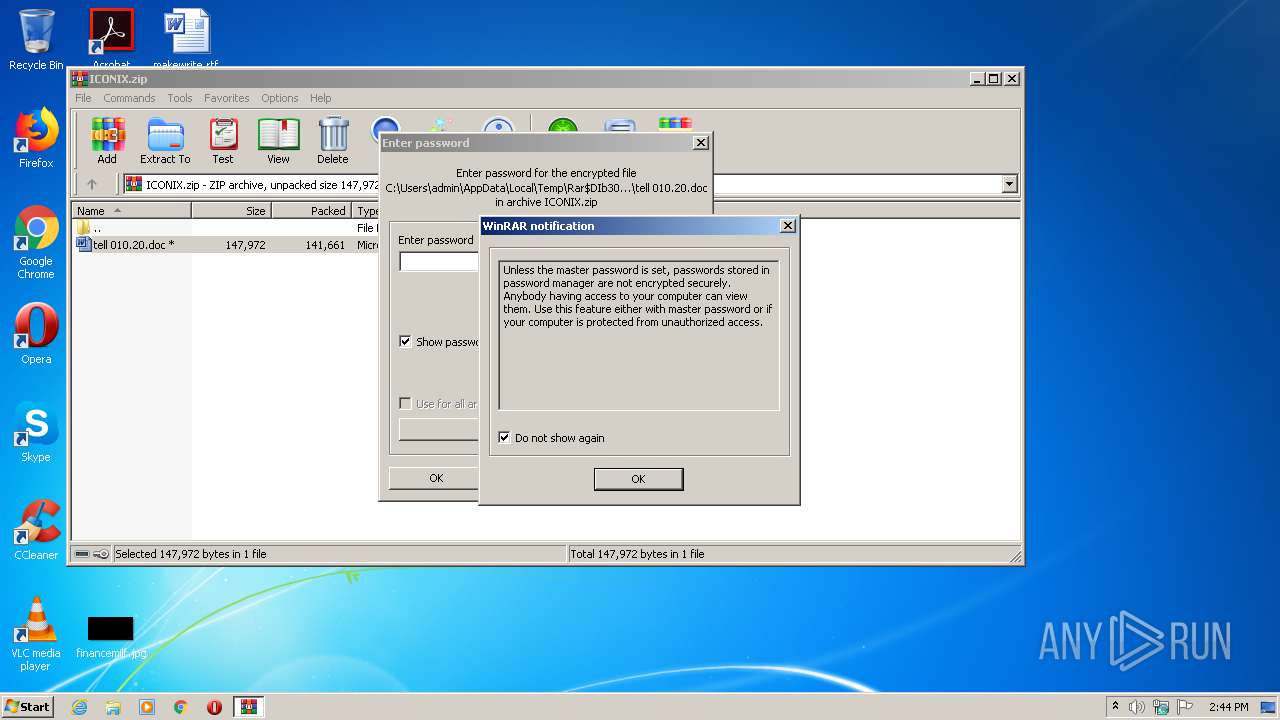
- WinRAR.exe (PID: 3072)
INFO
Reads settings of System Certificates
- WINWORD.EXE (PID: 3536)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 3536)
Creates files in the user directory
- WINWORD.EXE (PID: 3536)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:20 02:39:27 |
| ZipCRC: | 0x04834e92 |
| ZipCompressedSize: | 141661 |
| ZipUncompressedSize: | 147972 |
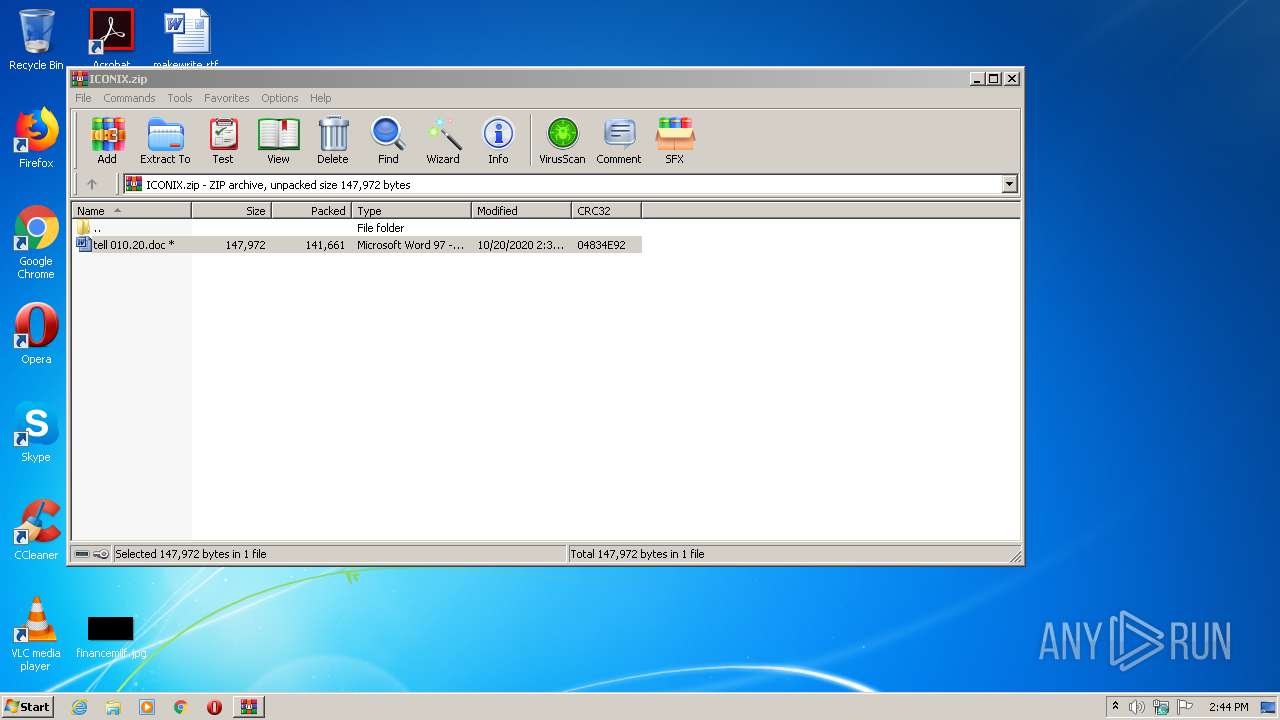
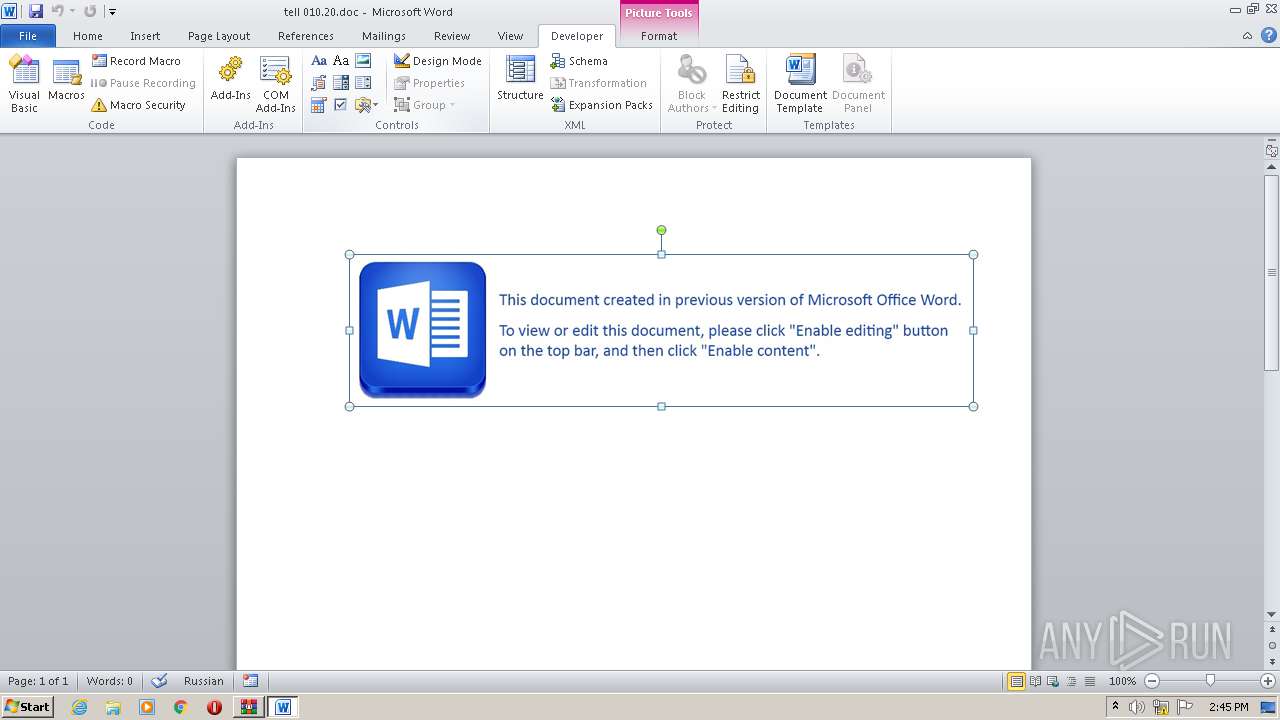
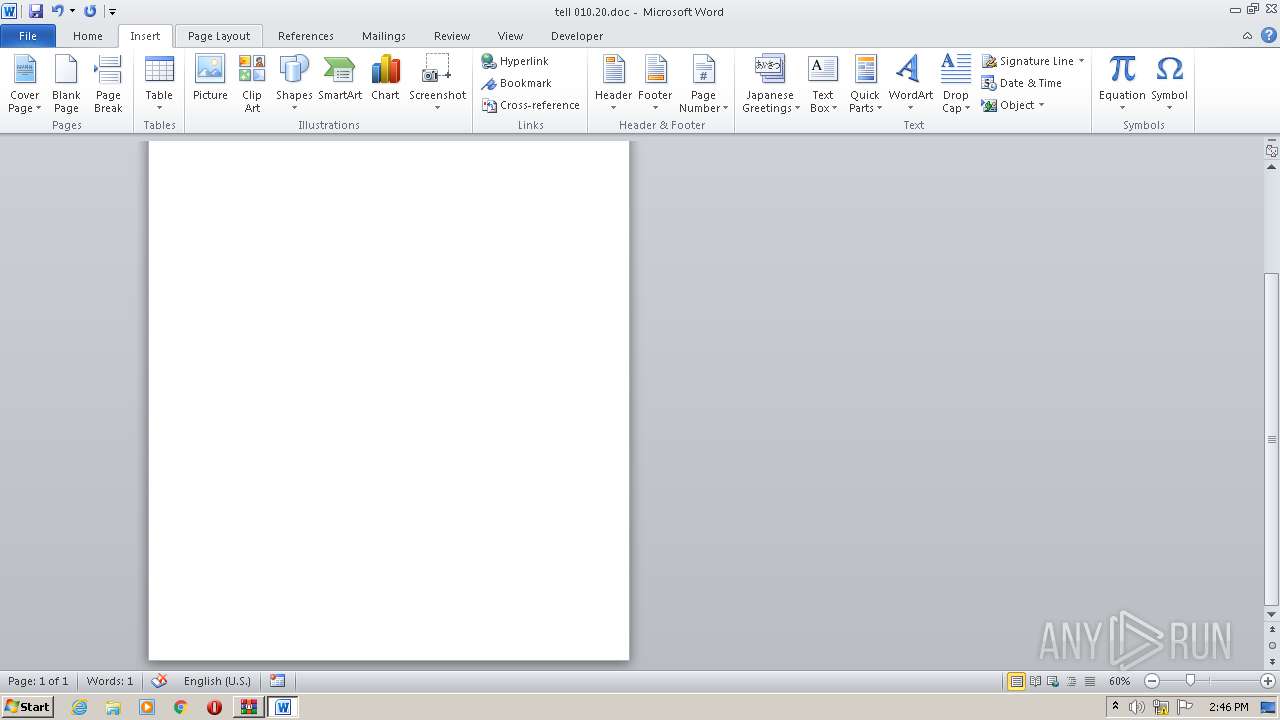
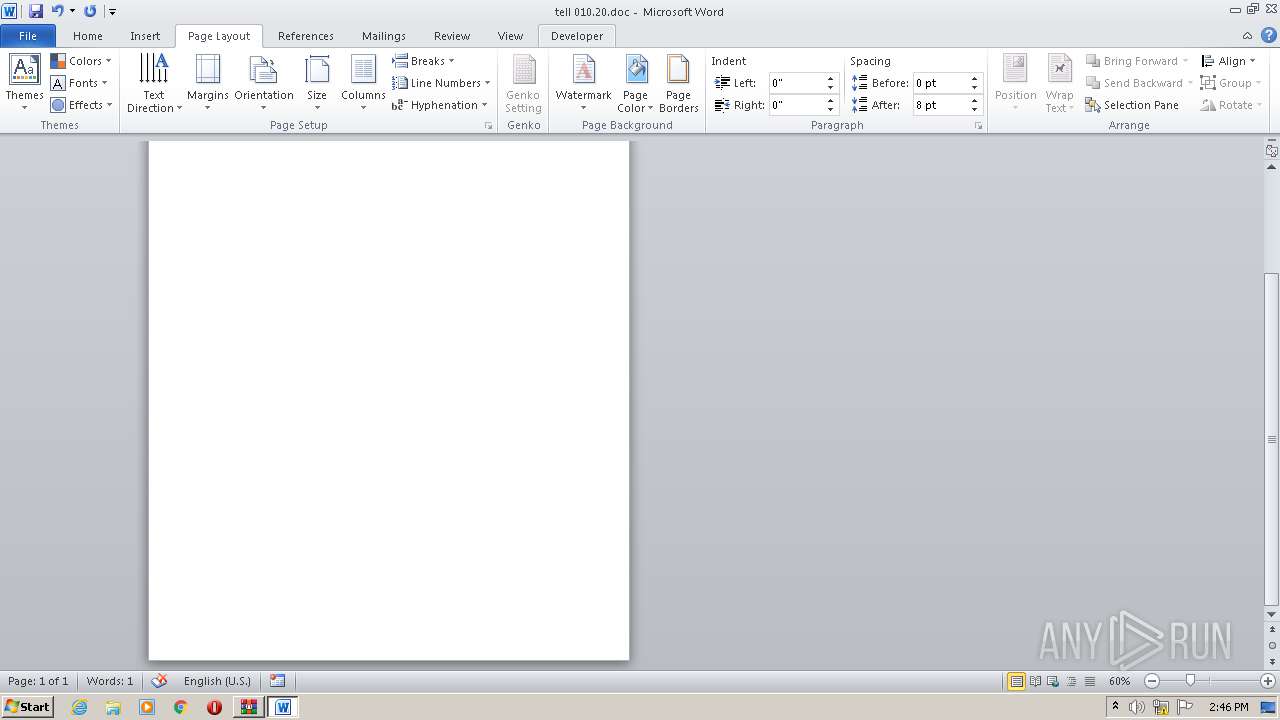
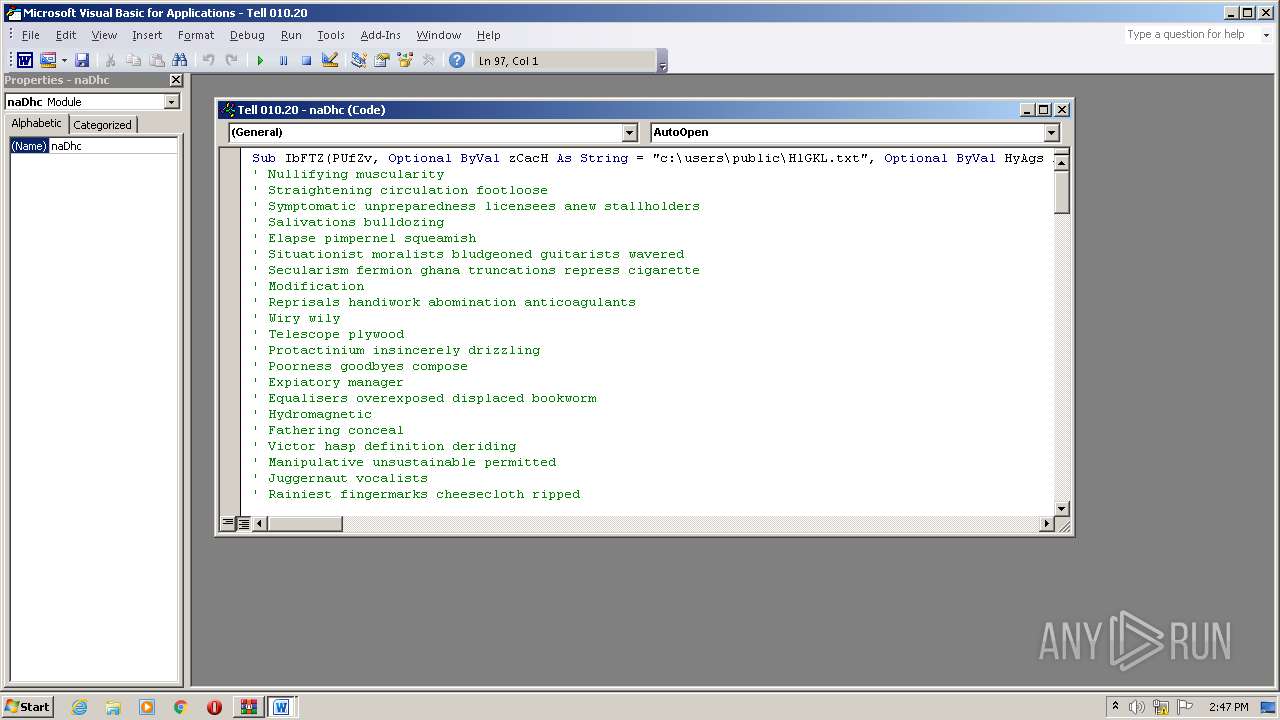
| ZipFileName: | tell 010.20.doc |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2348 | regsvr32 c:\users\public\HlGKL.txt | C:\Windows\system32\regsvr32.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
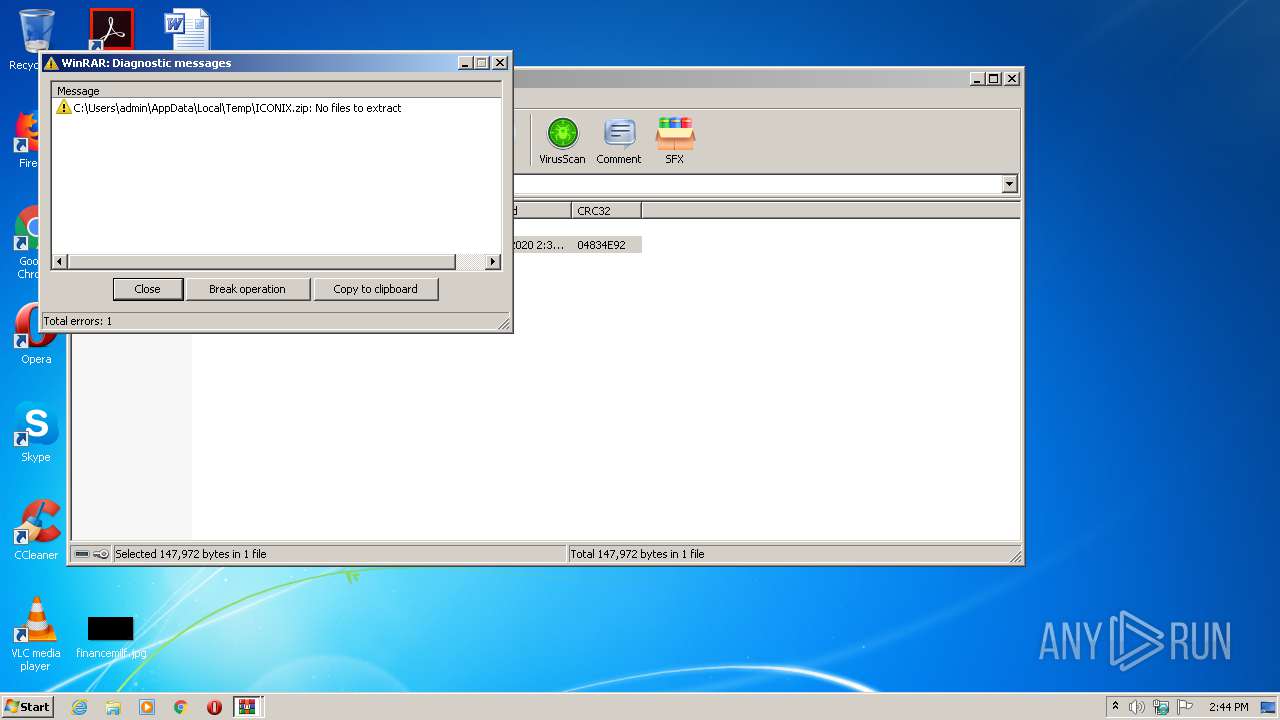
| 3072 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ICONIX.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
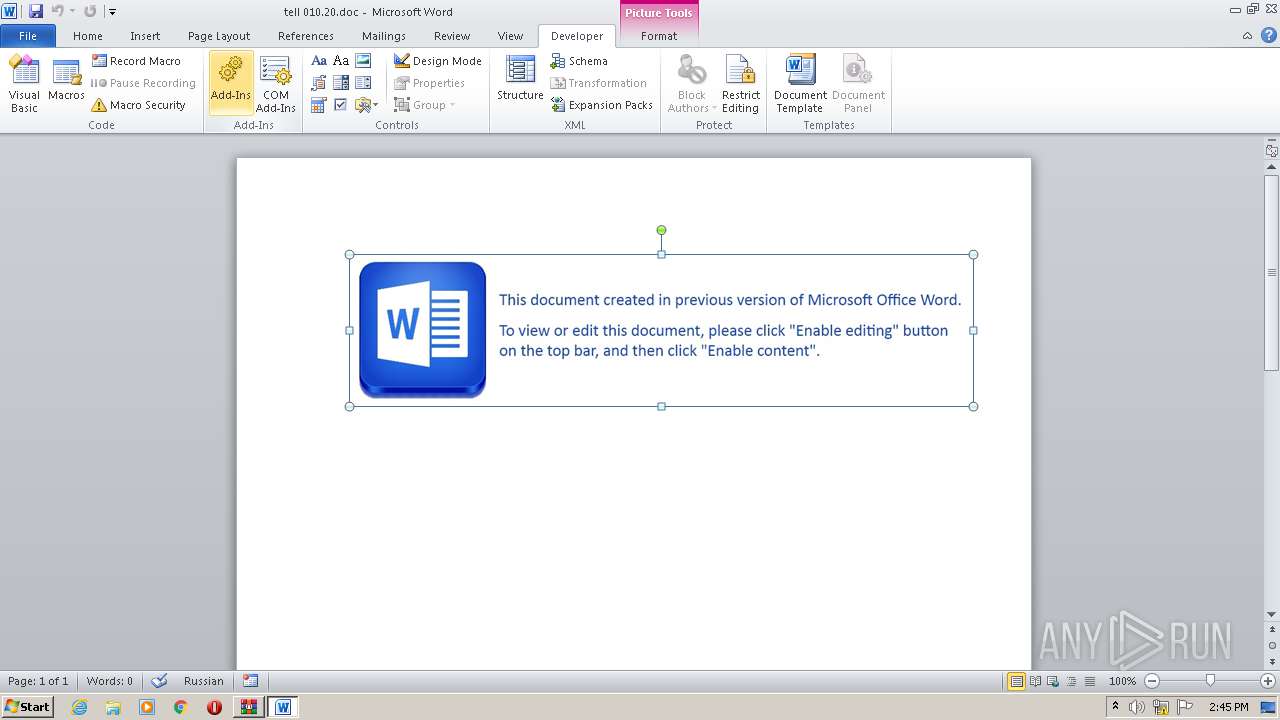
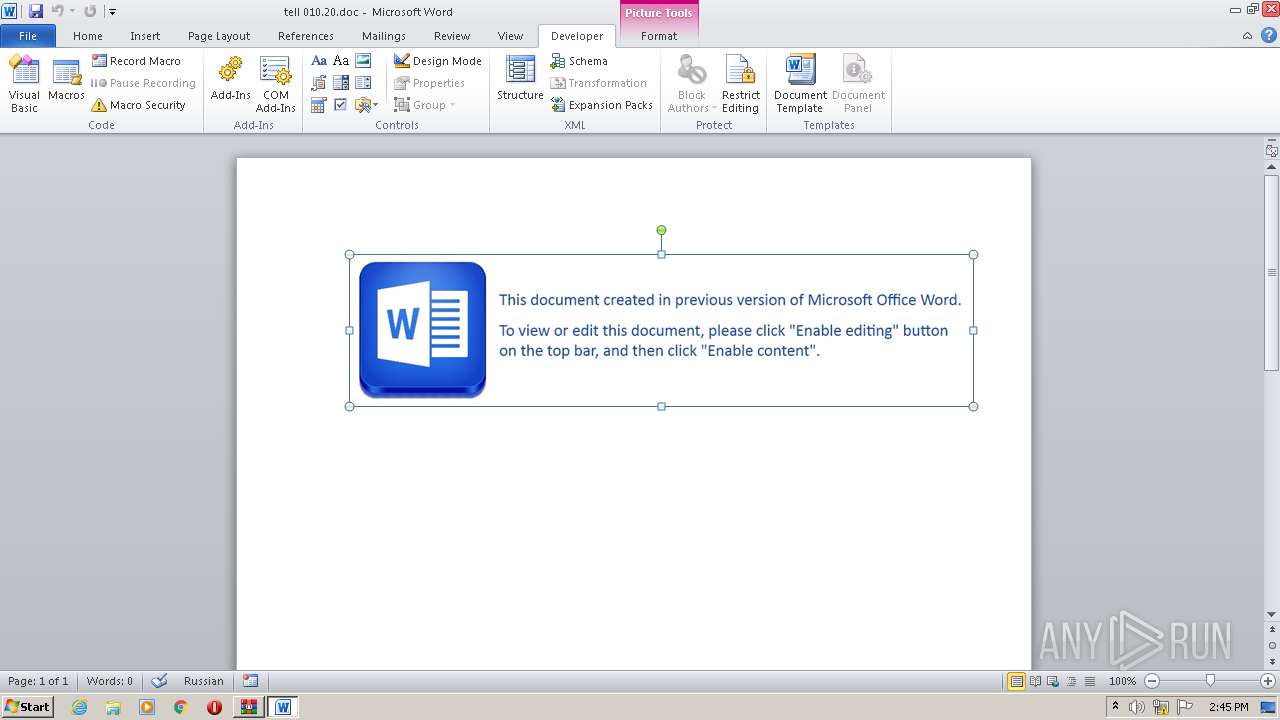
| 3536 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3072.29745\tell 010.20.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4028 | regsvr32 c:\users\public\HlGKL.txt | C:\Windows\system32\regsvr32.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
19 158
Read events
8 347
Write events
10 558
Delete events
253
Modification events
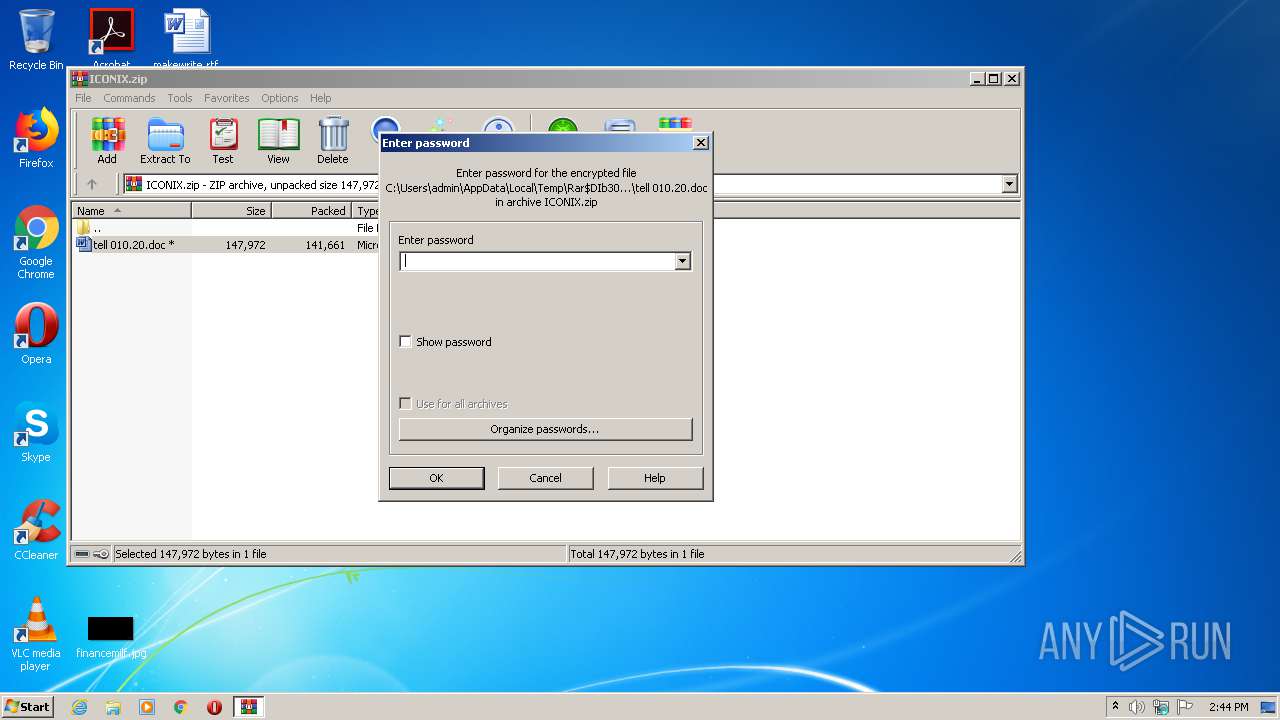
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ICONIX.zip | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Notifications |
| Operation: | write | Name: | NotifyPswMan |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR58AF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\config14[1].xml | — | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Cab807D.tmp | — | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Tar807E.tmp | — | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3072.29745\~$ll 010.20.doc | pgc | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\users\public\HlGKL.txt | html | |
MD5:— | SHA256:— | |||
| 3072 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3072.29745\tell 010.20.doc | document | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\ONetConfig\b6419f5bc3093b5f22142ce454e02407.xml | xml | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\ONetConfig\b6419f5bc3093b5f22142ce454e02407.sig | binary | |
MD5:— | SHA256:— | |||
| 3536 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_C9FB72B5AE80778A08024D8B0FDECC6F | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3536 | WINWORD.EXE | GET | 200 | 178.250.157.193:80 | http://gm9rlei16lamz5.com/_bxlzcpjlmpxlkzblf_zhlsplspz/wtlmwrqnnxfwgzzlkvzdbvnp_mphdqpggxfljvffj_.php?l=chfon13.ppt&lhe=_qzqsogkctxarvtnqdpt | RU | html | 208 b | unknown |
3536 | WINWORD.EXE | GET | 200 | 178.250.157.193:80 | http://gm9rlei16lamz5.com/_bxlzcpjlmpxlkzblf_zhlsplspz/wtlmwrqnnxfwgzzlkvzdbvnp_mphdqpggxfljvffj_.php?l=chfon13.ppt&lhe=_qzqsogkctxarvtnqdpt | RU | html | 208 b | unknown |
3536 | WINWORD.EXE | GET | 200 | 52.109.76.6:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | IE | xml | 1.99 Kb | whitelisted |
3536 | WINWORD.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 178.250.157.193:80 | gm9rlei16lamz5.com | — | RU | unknown |
3536 | WINWORD.EXE | 178.250.157.193:80 | gm9rlei16lamz5.com | — | RU | unknown |
3536 | WINWORD.EXE | 52.109.76.6:80 | office14client.microsoft.com | Microsoft Corporation | IE | whitelisted |
3536 | WINWORD.EXE | 52.109.120.29:443 | rr.office.microsoft.com | Microsoft Corporation | HK | whitelisted |
3536 | WINWORD.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gm9rlei16lamz5.com |
| unknown |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |