| File name: | FiIes .exe |
| Full analysis: | https://app.any.run/tasks/ac9c39c2-1a03-4090-8ce9-3ba15b980704 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2020, 14:00:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A6C776F57B289B97DDF353C32776A4AE |
| SHA1: | 6DA71EE426632B691E785B22CE9762DB728F68AD |
| SHA256: | 686467F75A5C0A056ABA4614AA42E404FE9535D3DE98806AD8C059C582F55716 |
| SSDEEP: | 12288:eIGmqFaVrXRP5Qo1CaeFWO+N+P52WZUHcyEaK54W7i4ZP/XjI:eStVFPutfo5X |
MALICIOUS
Changes the autorun value in the registry
- a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe (PID: 1352)
Application was dropped or rewritten from another process
- cmd.exe (PID: 3080)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 1024)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3984)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 2956)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 3956)
- svcnosts.exe (PID: 2940)
- svcnost.exe (PID: 3008)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 1500)
- cmd.exe (PID: 2656)
SUSPICIOUS
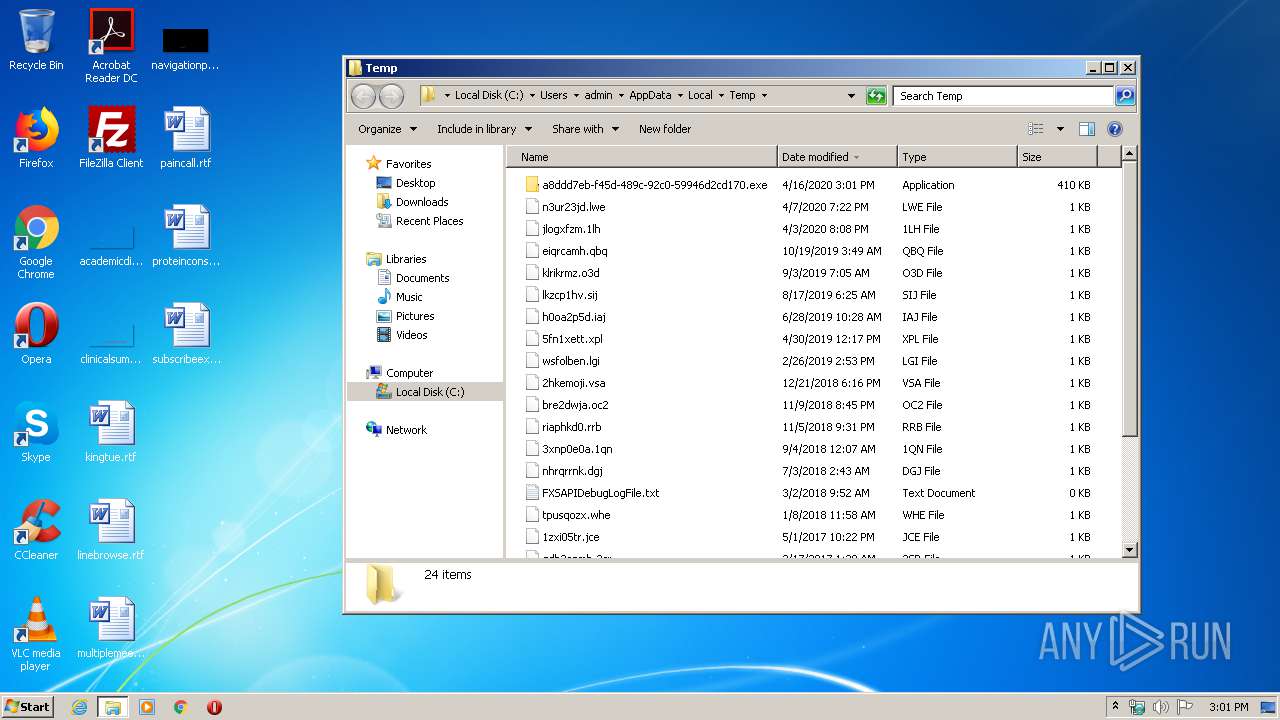
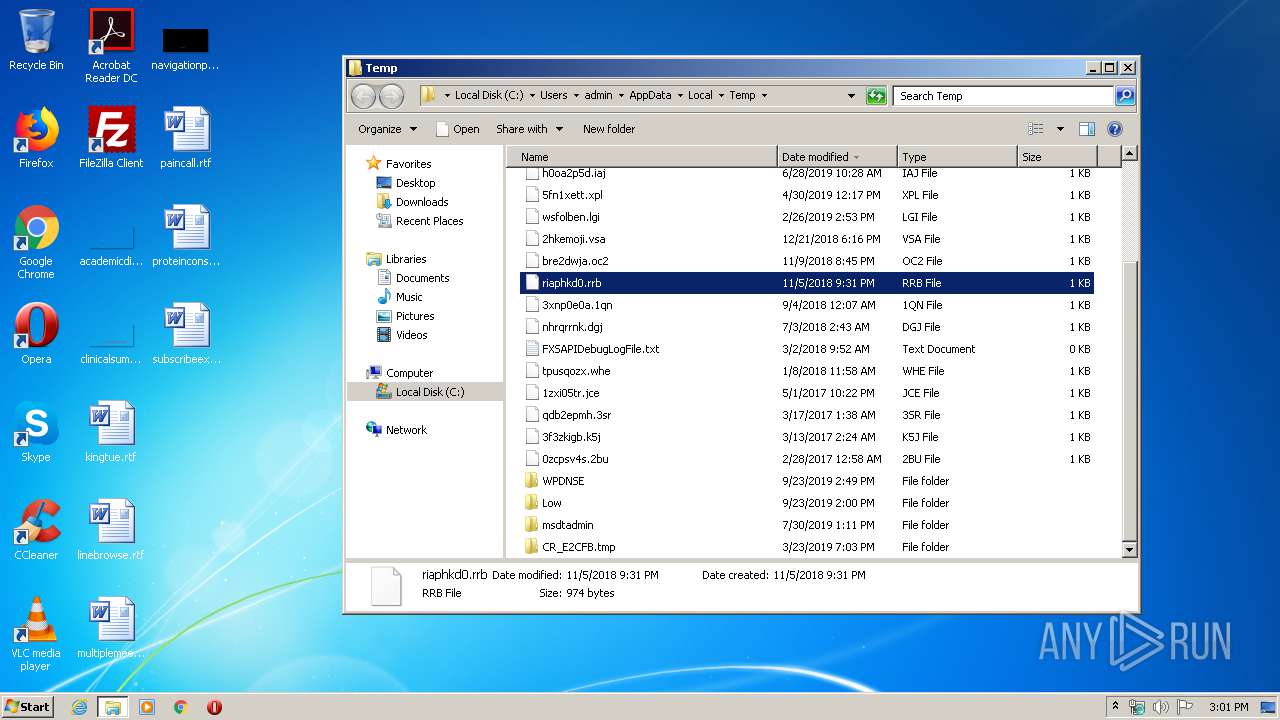
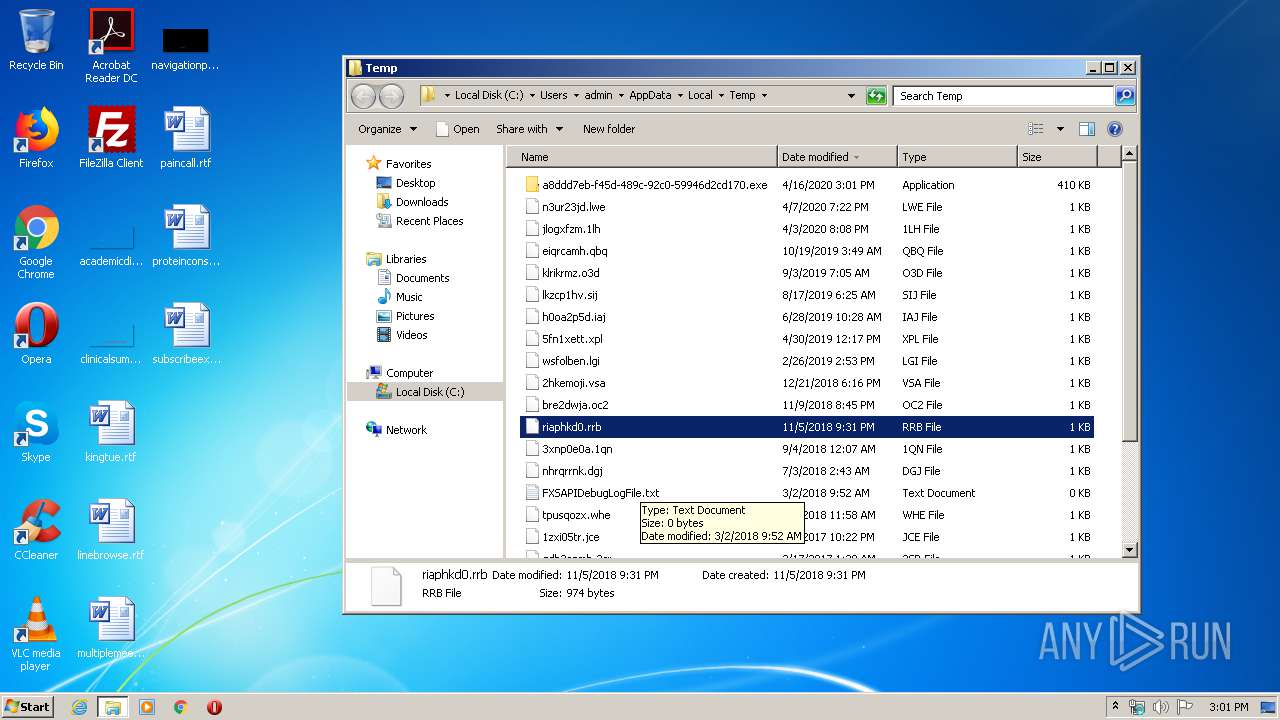
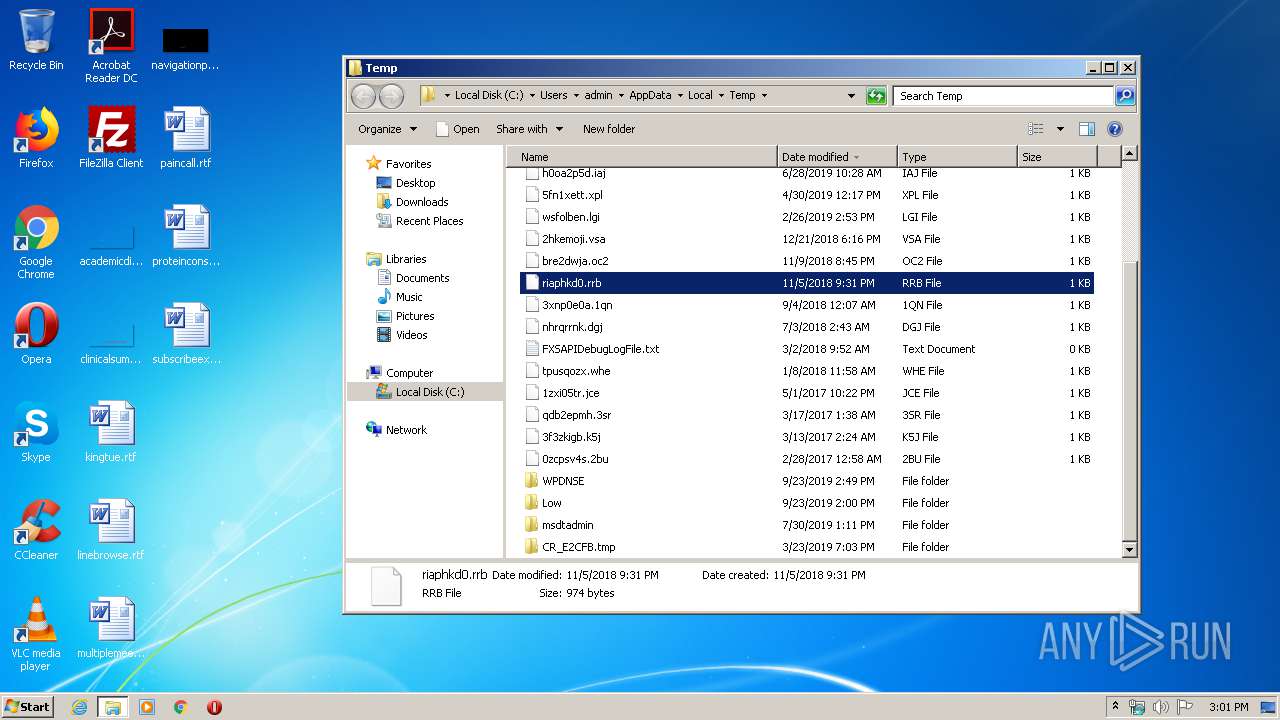
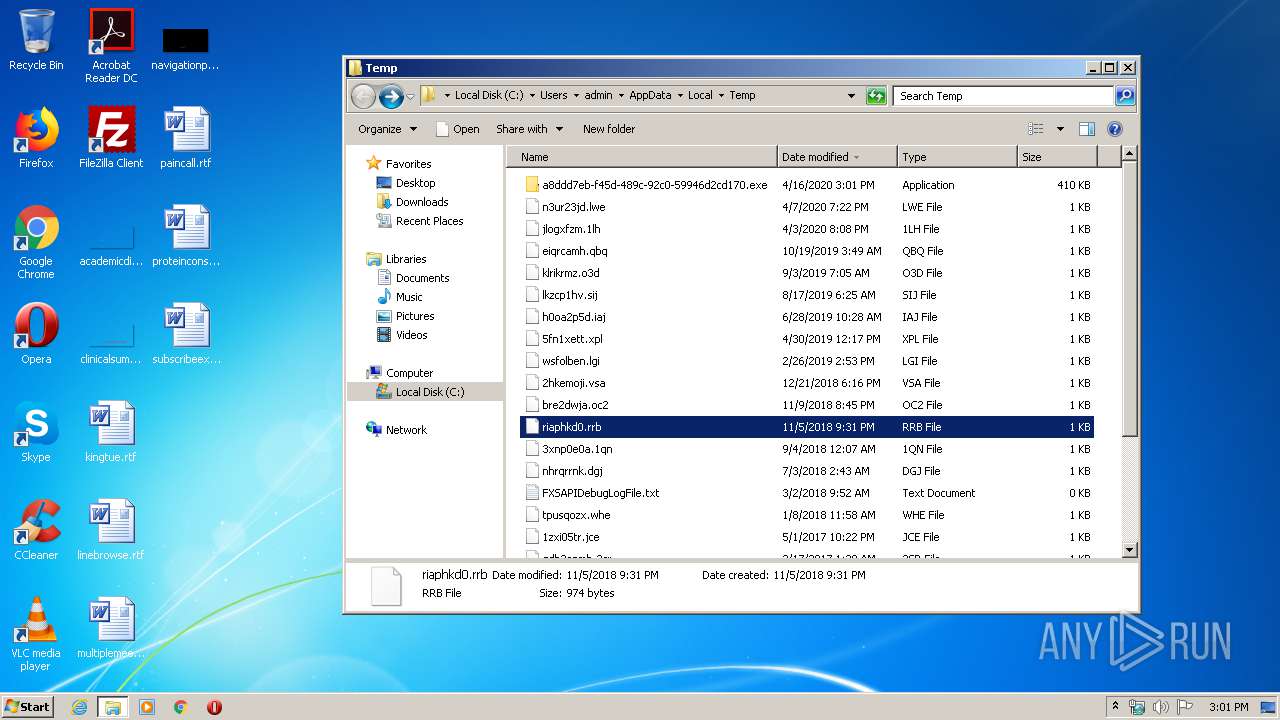
Executable content was dropped or overwritten
- a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe (PID: 1352)
Executed via COM
- explorer.exe (PID: 2848)
Modifies the open verb of a shell class
- a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe (PID: 1352)
Starts CMD.EXE for commands execution
- a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe (PID: 1352)
Creates executable files which already exist in Windows
- a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe (PID: 1352)
Writes to a desktop.ini file (may be used to cloak folders)
- a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe (PID: 1352)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3768)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 2956)
- cmd.exe (PID: 3984)
Starts itself from another location
- svcnosts.exe (PID: 2940)
Reads Environment values
- svcnost.exe (PID: 3008)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:20 17:29:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 80896 |
| InitializedDataSize: | 337920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6c00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Windows File Explorer |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Explorer |
| FileVersion: | 1.0.0.0 |
| InternalName: | Windows Explorers.exe |
| LegalCopyright: | 4F89C700331F900C |
| LegalTrademarks: | - |
| OriginalFileName: | Windows Explorers.exe |
| ProductName: | File Manager |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Oct-2019 15:29:47 |
| Comments: | Windows File Explorer |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Explorer |
| FileVersion: | 1.0.0.0 |
| InternalName: | Windows Explorers.exe |
| LegalCopyright: | 4F89C700331F900C |
| LegalTrademarks: | - |
| OriginalFilename: | Windows Explorers.exe |
| ProductName: | File Manager |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Oct-2019 15:29:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
@\x16O\x1a:\I*\xfc\x19\x05 | 0x00002000 | 0x000519FC | 0x00051A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99948 |
.text | 0x00054000 | 0x00013828 | 0x00013A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.50988 |
.rsrc | 0x00068000 | 0x00000A40 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.31479 |
.reloc | 0x0006A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x0006C000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
101
Monitored processes
43
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | attrib C:\sefera\Jnt\fecoyigo\desktop.ini +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Windows\system32\cmd.exe" /c cacls n:\System_VoIume_lnformation\Jnt\null\..\.. /r administrators /e /t | C:\Windows\system32\cmd.exe | — | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1028 | cacls n:\System_VoIume_lnformation\Jnt\null\..\.. /g everyone:f /e /t | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe" | C:\Users\admin\AppData\Local\Temp\a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1500 | "C:\Windows\system32\cmd.exe" /c cacls C:\System_VoIume_lnformation\Jnt\bowyru\..\.. /d administrators /e | C:\Windows\system32\cmd.exe | — | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1748 | attrib C:\sefera\Jnt\fecoyigo\..\.. +r +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | attrib C:\sefera\Jnt\fecoyigo +r +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | cacls n:\sefera\Jnt\null\..\.. /r admin /e /t | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | cacls C:\sefera\Jnt\fecoyigo\..\.. /d administrators /e | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | cacls n:\sefera\Jnt\null\..\.. /r administrators /e /t | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 243
Read events
1 080
Write events
163
Delete events
0
Modification events
| (PID) Process: | (1352) a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1352) a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000A0000000700000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\39\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1352) a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft |
| Operation: | write | Name: | STR |
Value: C|fecoyigo|bowyru|svcnost|svcnosts | |||
Executable files
4
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
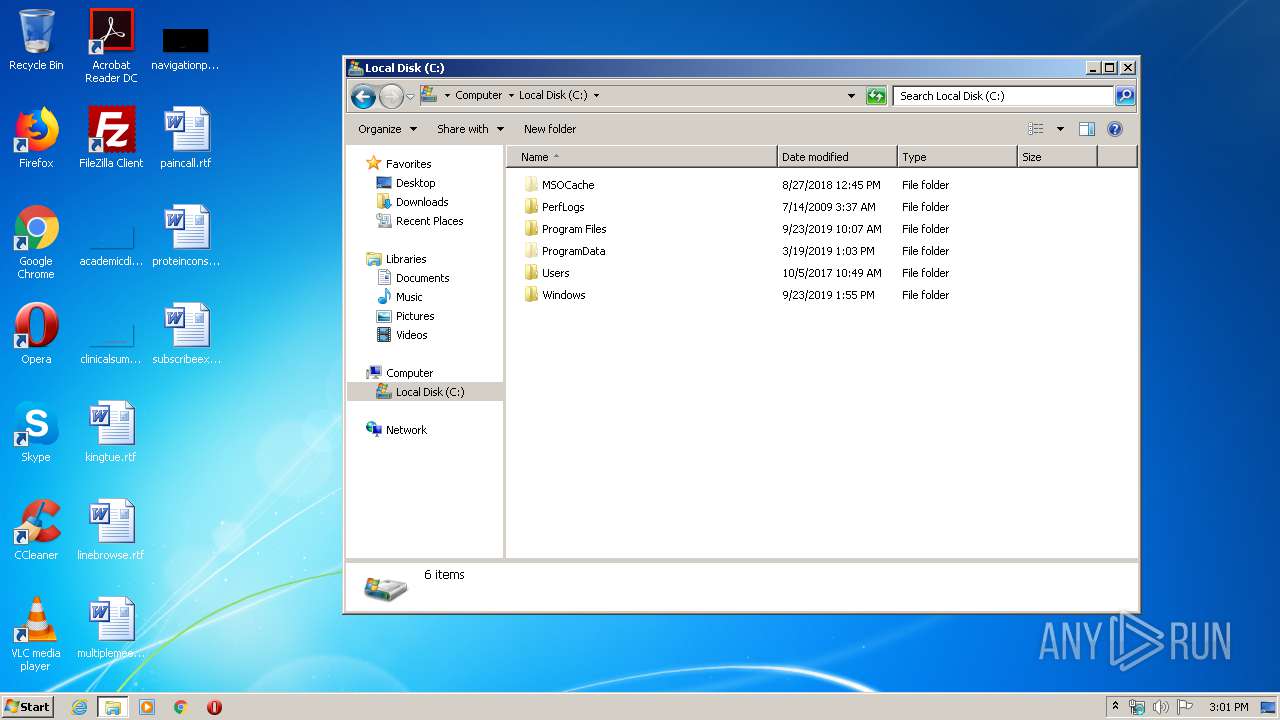
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\System_VoIume_lnformation\Jnt\bowyru\gotera.bmp | binary | |
MD5:F1A2D63899B87CEF381F57BB4D195F7C | SHA256:C0F305F40A1CCCCE836A9DC9F44368ABC4173D4A697709D3EC8C71AFDC30FCEA | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\System_VoIume_lnformation\Jnt\bowyru\explorers.exe | executable | |
MD5:E1C8E6FA5477FC3C6459B70EC2C362E0 | SHA256:33AEDB26DBCAC8C27AD724A2583C93CDD5E2F1C8535444AB0DBAF0ECCAABD360 | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\sefera\Jnt\fecoyigo\svcnost.exe | executable | |
MD5:E1C8E6FA5477FC3C6459B70EC2C362E0 | SHA256:33AEDB26DBCAC8C27AD724A2583C93CDD5E2F1C8535444AB0DBAF0ECCAABD360 | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\sefera\Jnt\fecoyigo\gotera.bmp | binary | |
MD5:F1A2D63899B87CEF381F57BB4D195F7C | SHA256:C0F305F40A1CCCCE836A9DC9F44368ABC4173D4A697709D3EC8C71AFDC30FCEA | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\System_VoIume_lnformation\Jnt\bowyru\bmz\explorer.exe | executable | |
MD5:AD7B9C14083B52BC532FBA5948342B98 | SHA256:17F746D82695FA9B35493B41859D39D786D32B23A9D2E00F4011DEC7A02402AE | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\sefera\desktop.ini | ini | |
MD5:ADC4B5D4444D26293DC782B6238CA6F0 | SHA256:ABE8A5933FF450A89B8E9A736F08874B43B7355D17FFE6540C4A6EAD0F0995D3 | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\sefera\Jnt\fecoyigo\svcnosts.exe | executable | |
MD5:E1C8E6FA5477FC3C6459B70EC2C362E0 | SHA256:33AEDB26DBCAC8C27AD724A2583C93CDD5E2F1C8535444AB0DBAF0ECCAABD360 | |||
| 1352 | a8ddd7eb-f45d-489c-92c0-59946d2cd170.exe | C:\sefera\Jnt\fecoyigo\desktop.ini | ini | |
MD5:ADC4B5D4444D26293DC782B6238CA6F0 | SHA256:ABE8A5933FF450A89B8E9A736F08874B43B7355D17FFE6540C4A6EAD0F0995D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3008 | svcnost.exe | 151.101.1.195:443 | clear-march.firebaseapp.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clear-march.firebaseapp.com |
| malicious |