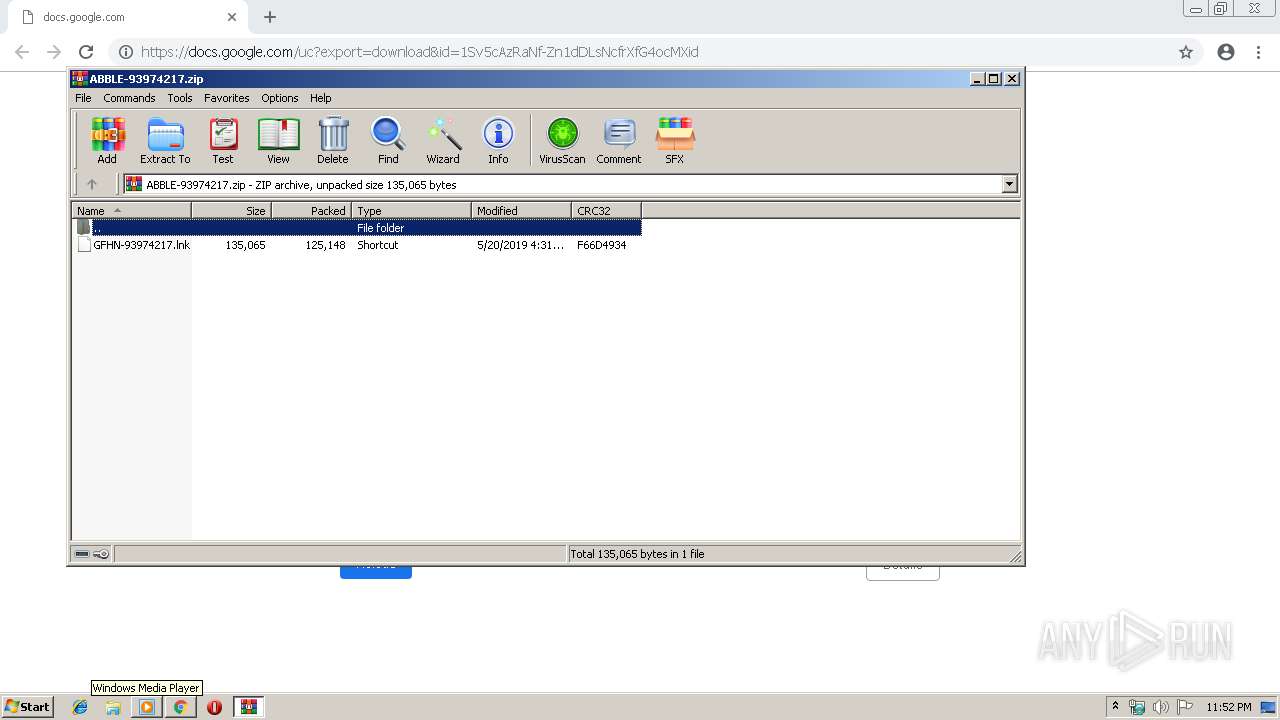
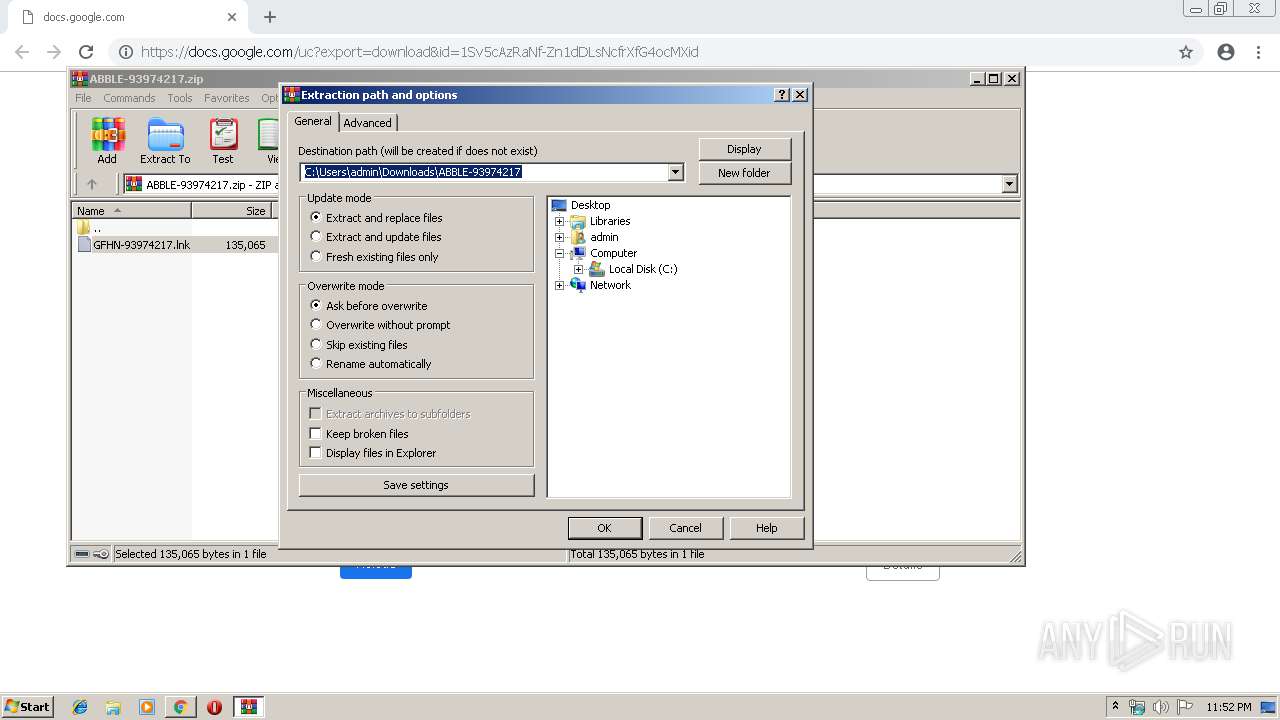
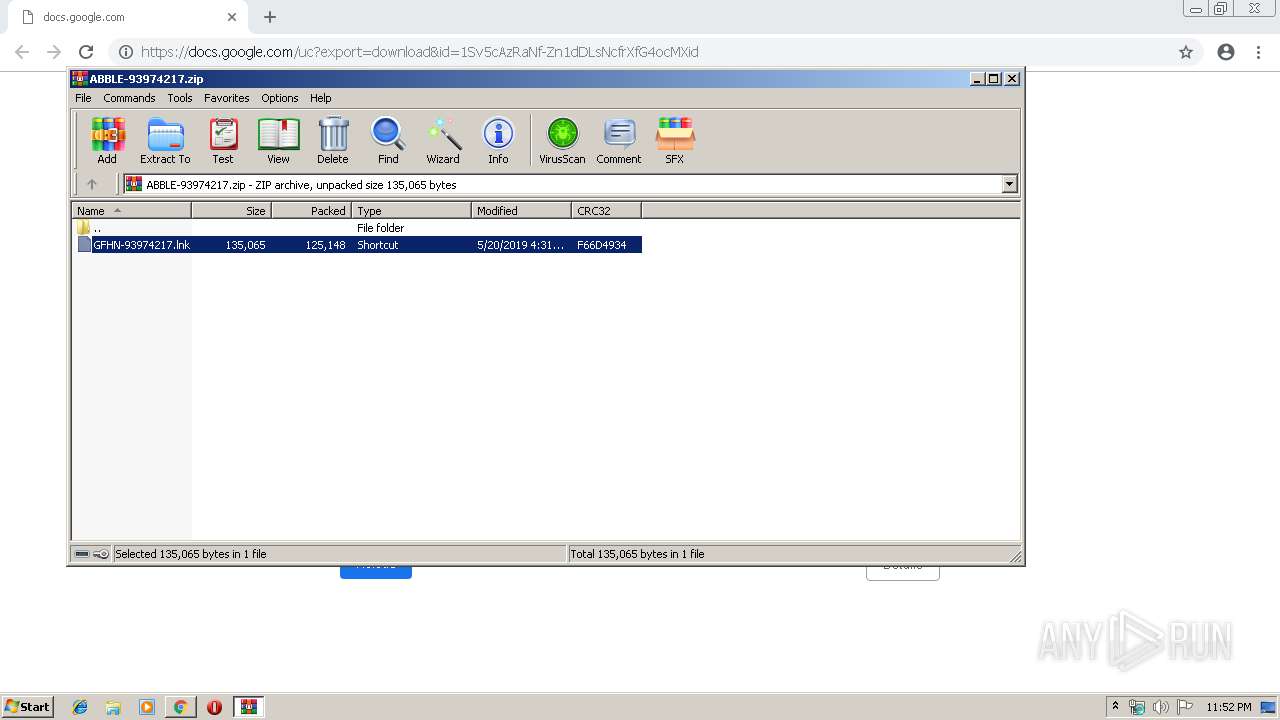
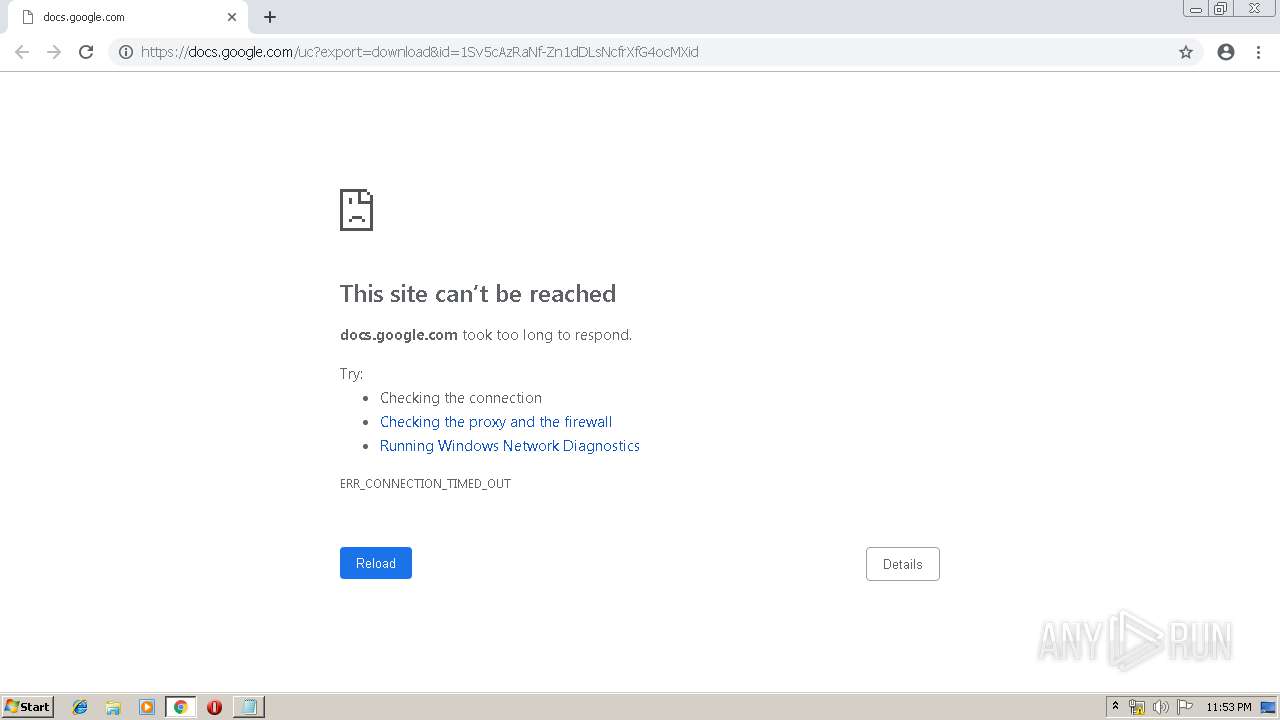
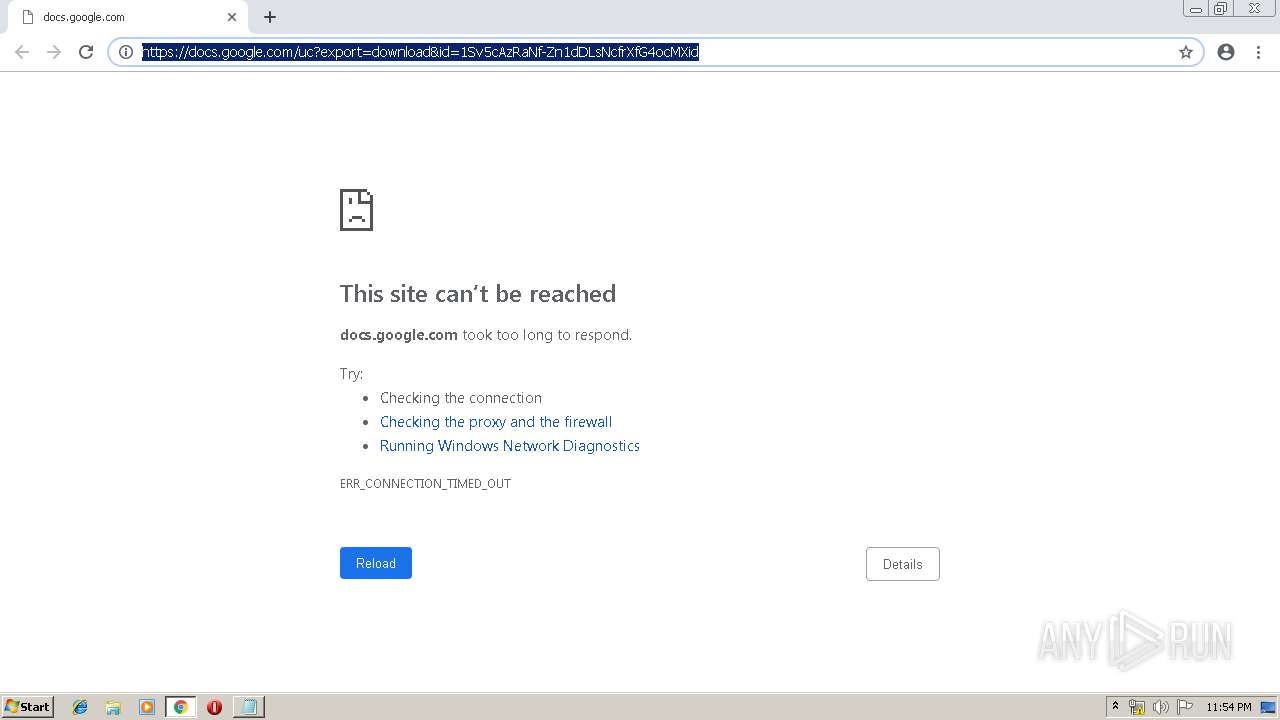
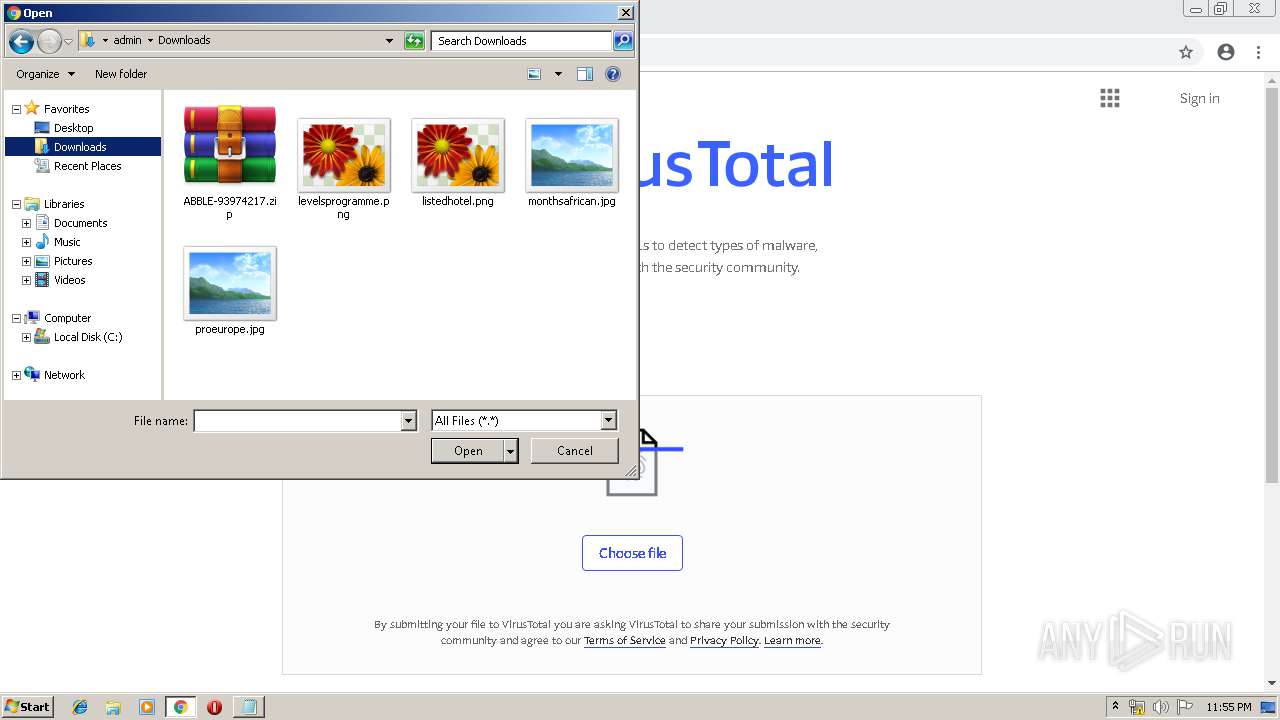
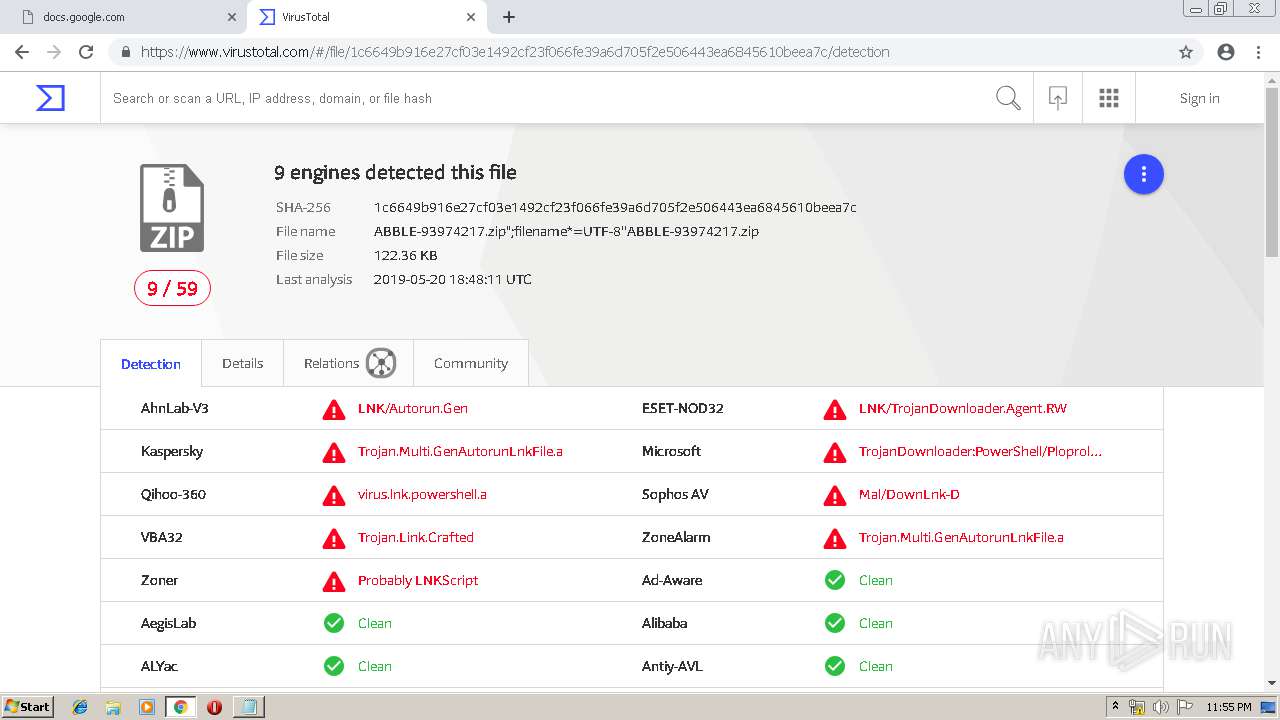
| URL: | https://docs.google.com/uc?export=download&id=1Sv5cAzRaNf-Zn1dDLsNcfrXfG4ocMXid |
| Full analysis: | https://app.any.run/tasks/f41d7cbe-45e1-4656-9259-f2e66d085cf9 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 22:51:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
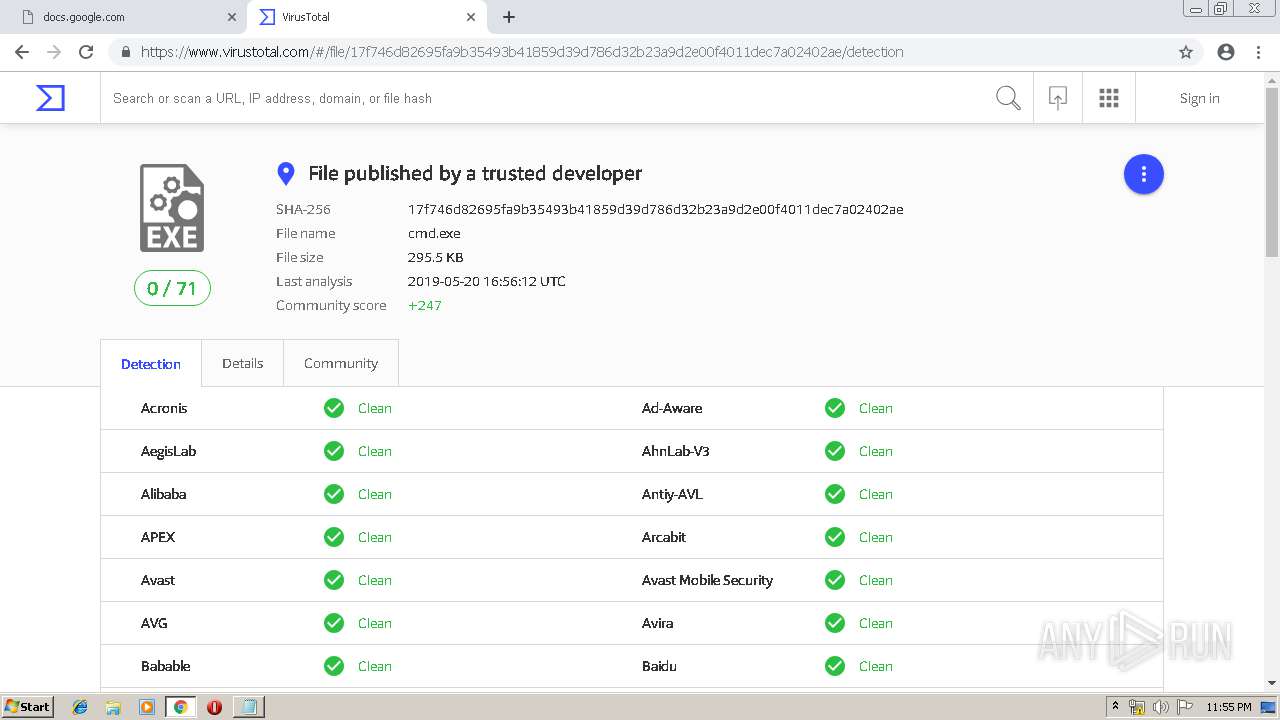
| MD5: | 02E1F9498A6ABF677B929ADC025FD206 |
| SHA1: | 4343FC48F7410176283E7E3B7FDD5389E17EB924 |
| SHA256: | 686403024BC71B5F03E41F7CDDE076CCE0D62A42572E38FE2B2284AE3AC6B184 |
| SSDEEP: | 3:N8SP3u2NAaBrC22GdLM4cyK1A:2Sm2BB+2BdLM4dK1A |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3028)
- cmd.exe (PID: 3056)
- cmd.exe (PID: 3004)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 344)
- cmd.exe (PID: 3296)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3376)
- cmd.exe (PID: 2956)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 3816)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 3124)
Application was dropped or rewritten from another process
- D.exe (PID: 2720)
- D.exe (PID: 1672)
- D.exe (PID: 2284)
- D.exe (PID: 2308)
Known privilege escalation attack
- DllHost.exe (PID: 2460)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 1672)
- D.exe (PID: 2308)
Loads the Task Scheduler COM API
- D.exe (PID: 2284)
- D.exe (PID: 1672)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2984)
Creates files in the user directory
- powershell.exe (PID: 2556)
- powershell.exe (PID: 2228)
- powershell.exe (PID: 1128)
- powershell.exe (PID: 3940)
- powershell.exe (PID: 3572)
- powershell.exe (PID: 2688)
- powershell.exe (PID: 3792)
- D.exe (PID: 1672)
Starts CMD.EXE for commands execution
- D.exe (PID: 2720)
- D.exe (PID: 1672)
- D.exe (PID: 2284)
- D.exe (PID: 2308)
Executable content was dropped or overwritten
- powershell.exe (PID: 2556)
- D.exe (PID: 1672)
- D.exe (PID: 2284)
Executes PowerShell scripts
- cmd.exe (PID: 2992)
- cmd.exe (PID: 2752)
Executed via COM
- DllHost.exe (PID: 2460)
Executed via Task Scheduler
- D.exe (PID: 2308)
Creates files in the program directory
- D.exe (PID: 2308)
INFO
Application launched itself
- chrome.exe (PID: 2984)
Reads Internet Cache Settings
- chrome.exe (PID: 2984)
Manual execution by user
- cmd.exe (PID: 3028)
- cmd.exe (PID: 3004)
Reads settings of System Certificates
- powershell.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
76
Malicious processes
15
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,5251663985741816586,2983713508810238180,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15540790743271879852 --mojo-platform-channel-handle=4344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1116 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1128 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1400 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,5251663985741816586,2983713508810238180,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8578803379606395893 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,5251663985741816586,2983713508810238180,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6836439144300995640 --mojo-platform-channel-handle=3892 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1672 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\D.exe" | C:\Users\admin\AppData\Local\Temp\D.exe | DllHost.exe | ||||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: HIGH Description: NVIDIA PTX JIT Compiler, Version 430.39 Exit code: 0 Version: 26.21.14.3039 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,5251663985741816586,2983713508810238180,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5180046477718545001 --mojo-platform-channel-handle=3568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 985
Read events
3 245
Write events
730
Delete events
10
Modification events
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13202866320798000 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
97
Text files
220
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8bde6bc9-de9f-4bfb-889d-3bc444b6f89d.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
39
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | chrome.exe | GET | 302 | 216.239.34.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2984 | chrome.exe | GET | 200 | 173.194.183.134:80 | http://r1---sn-aigl6ner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-aigl6ner&ms=nvh&mt=1558392737&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2984 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
2984 | chrome.exe | GET | 204 | 172.217.18.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.21.238:443 | docs.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.99:80 | www.gstatic.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.208.33:443 | doc-00-5o-docs.googleusercontent.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.23.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.16.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.18.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
docs.google.com |
| shared |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
doc-00-5o-docs.googleusercontent.com |
| shared |
clients2.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |