| URL: | https://w3g3a5v6.ssl.hwcdn.net/upload2/game/2151479/8245548?GoogleAccessId=uploader@moonscript2.iam.gserviceaccount.com&Expires=1688981192&Signature=LYm%2FY8ha5O9JR%2B%2F%2FMJ%2B4tzo6aH3K5s7Y%2BWcHO7b2dPTkpVUIFnc6gAKyEZFMW5dDuSaxNtvCSxq4w1ZCoyxxJVrYV9Hc6u%2Fd8jxhMFVt5FUfPakBiXCSpQaURBXKNJhqGxe1Ual9mA02bKzdT7Ovs2hvTJwGhG3p%2BcZgZp6ay1L6VsQVEmadq%2BaLN4SMsg2V%2FIYMxs9YWpnOVKVBt64F5zkZm0CUg7725QUREblHvn4x50FM73bcEKuN3GvFt8LpnU3%2FWNr1Envqc5MRNbrMlF%2B0wIaIqNT5%2BNIWomq%2F%2FlLGktUebaa9WtdbZQf49MkcuOpvfJ1l5OX7dS8YpDPSvw==&hwexp=1688981452&hwsig=2763ca294aa1898f356939ee9f0ce9d9 |
| Full analysis: | https://app.any.run/tasks/da825112-8a53-4fd9-846e-e59a023298aa |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2023, 09:33:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 376E4F73A3308483A9C95841DB2149AA |
| SHA1: | 2854C4AB6655DA6169C4898E891CAEF1FA1FE9CF |
| SHA256: | 6857ACAC418D2EF0D1F70E1A84400C88516451DD356409BFED59935544D0F767 |
| SSDEEP: | 12:2G9toIKtyktqQImsbj3i+TSGSVn8ogn/mT86OeDn4zbdRLVOEhhp/QX:28ohlqTmqj3i+TSG68owmTD7kd+gY |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
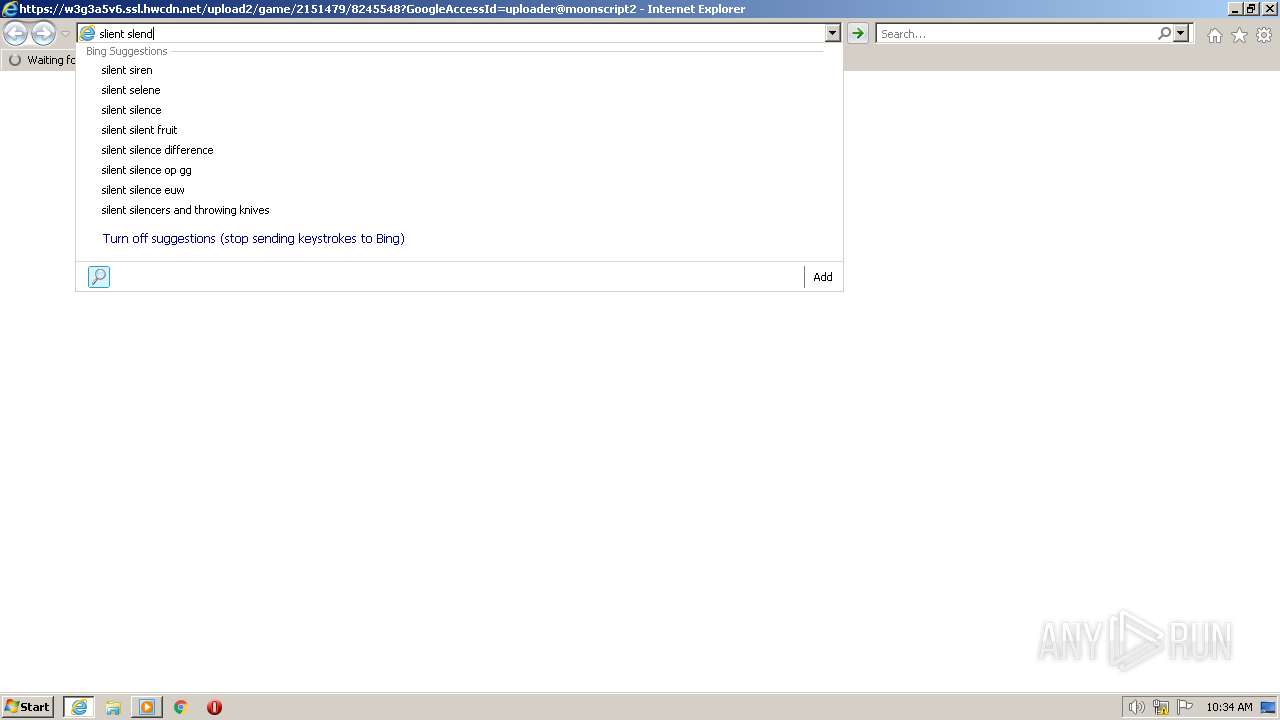
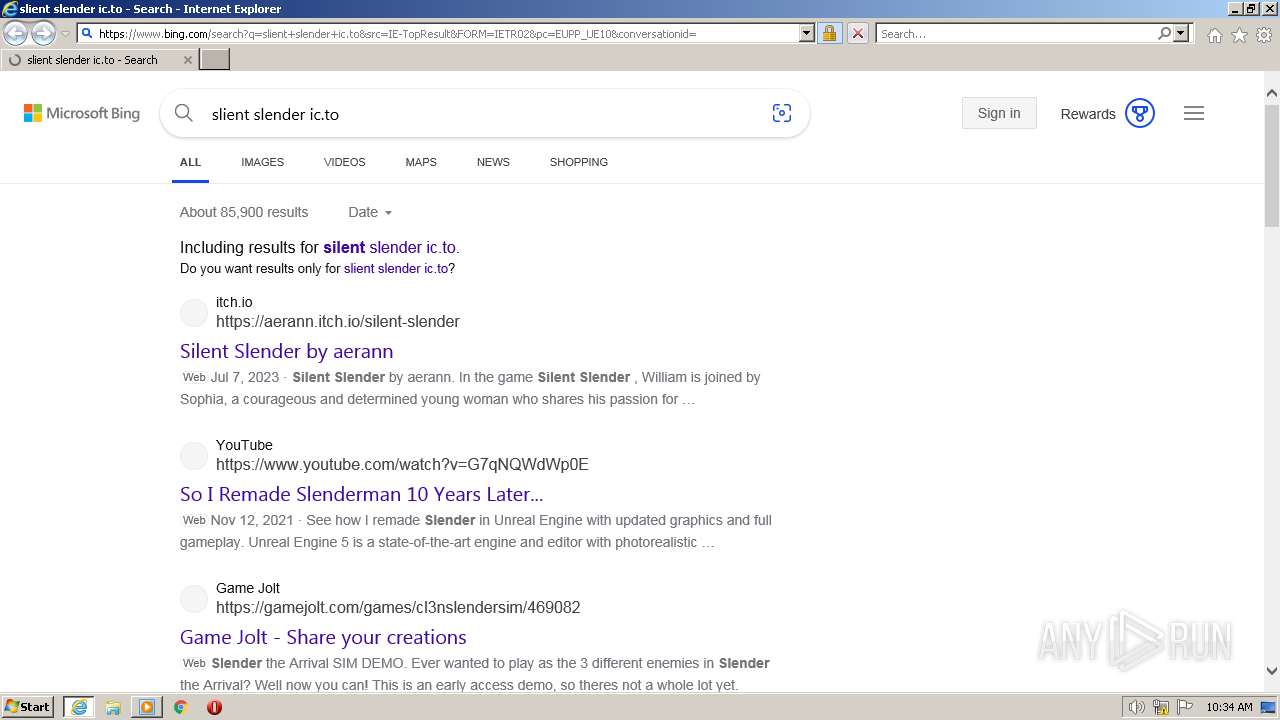
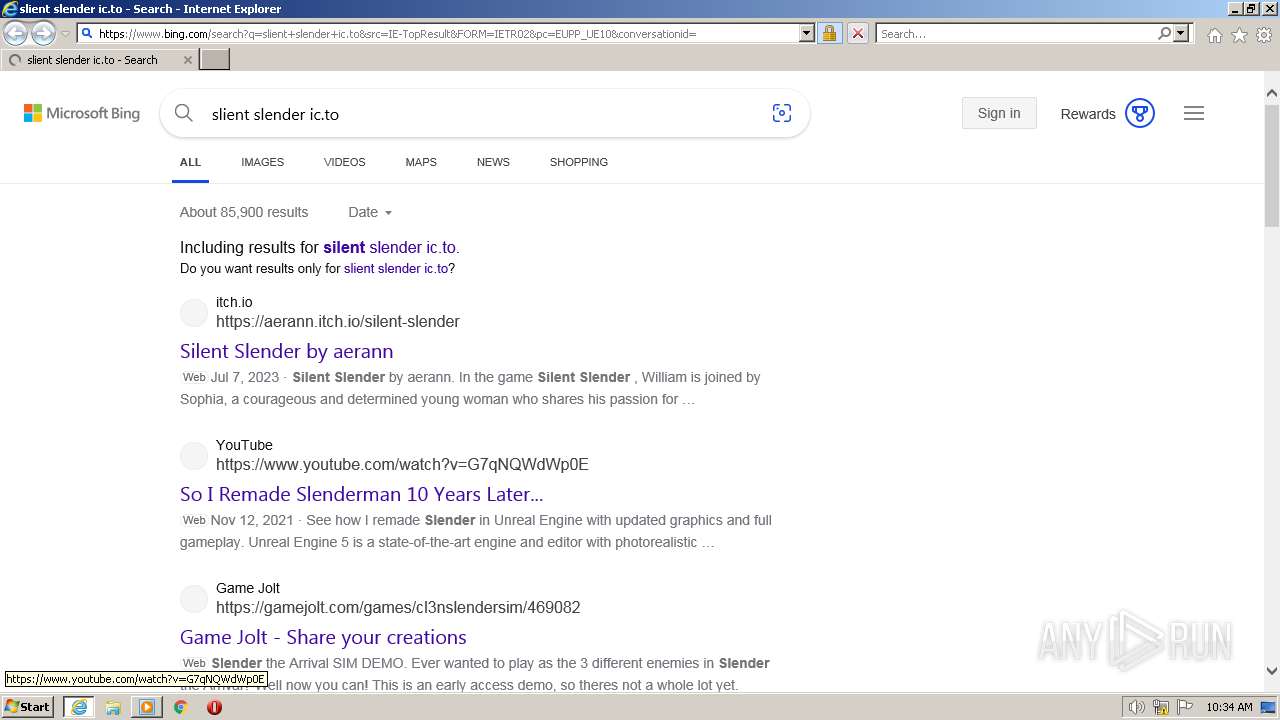
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://w3g3a5v6.ssl.hwcdn.net/upload2/game/2151479/8245548?GoogleAccessId=uploader@moonscript2.iam.gserviceaccount.com&Expires=1688981192&Signature=LYm%2FY8ha5O9JR%2B%2F%2FMJ%2B4tzo6aH3K5s7Y%2BWcHO7b2dPTkpVUIFnc6gAKyEZFMW5dDuSaxNtvCSxq4w1ZCoyxxJVrYV9Hc6u%2Fd8jxhMFVt5FUfPakBiXCSpQaURBXKNJhqGxe1Ual9mA02bKzdT7Ovs2hvTJwGhG3p%2BcZgZp6ay1L6VsQVEmadq%2BaLN4SMsg2V%2FIYMxs9YWpnOVKVBt64F5zkZm0CUg7725QUREblHvn4x50FM73bcEKuN3GvFt8LpnU3%2FWNr1Envqc5MRNbrMlF%2B0wIaIqNT5%2BNIWomq%2F%2FlLGktUebaa9WtdbZQf49MkcuOpvfJ1l5OX7dS8YpDPSvw==&hwexp=1688981452&hwsig=2763ca294aa1898f356939ee9f0ce9d9" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2976 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 627
Read events
18 484
Write events
143
Delete events
0
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
33
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\LF0DLPJ2.txt | text | |
MD5:BF723D741F2190D8AE0C89F7AB00C1D7 | SHA256:B7DEC3A5B6173F554F0660F655B3A6CE48FA30CD1E3311B90CCAB59BB1BE633C | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].htm | xml | |
MD5:9FEBCEB15D14BD3B05F616A1EBBF4B16 | SHA256:A2BCB0F63AD6E57A093D5FE3848741AEE97C893B51FA50473A4BAD19D1FFDBBE | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[2].xml | xml | |
MD5:B9FBCAE984D985E367AFB95CB864487E | SHA256:9A1E787E74C5B7170901614EA5581D342561556B0A43CD859DF37DFECC57011E | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].xml | xml | |
MD5:9FEBCEB15D14BD3B05F616A1EBBF4B16 | SHA256:A2BCB0F63AD6E57A093D5FE3848741AEE97C893B51FA50473A4BAD19D1FFDBBE | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TIBAPTOY.txt | text | |
MD5:6DF0A6347DBD5F3095B1663DFF9B9EA6 | SHA256:00D0140DAF936311DC71D5E4BFB673E6F77C330CC8AB5DCDB2C442A7F50328BA | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EVEO18V5.txt | text | |
MD5:B12D0B44B68AADA0F96890C756D691E5 | SHA256:820625470FEFD530F611CA6323233214DDF760D919EA06861C2DA6BE18570D29 | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\E2CSGH5G.txt | text | |
MD5:786A81ACBCD3E9A9F12C426E8E2ADFF0 | SHA256:E2DBA2C2DAB49553DB5EDBB27DF0962AD63CDF994992564D575BD3DC51B21A39 | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\CDATAQ19.txt | text | |
MD5:BD43C2DAD28EA6AA8DDD4A39F6E42E06 | SHA256:EC5D65580796584765EE8326793EF9313A7E33821C5389095F4CD44C1CCD7806 | |||
| 3552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].xml | xml | |
MD5:B9FBCAE984D985E367AFB95CB864487E | SHA256:9A1E787E74C5B7170901614EA5581D342561556B0A43CD859DF37DFECC57011E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
66
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3552 | iexplore.exe | GET | 200 | 23.201.254.55:80 | http://x1.c.lencr.org/ | CH | binary | 717 b | whitelisted |
3552 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?205b3b8a7552b872 | US | compressed | 4.70 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | binary | 1.47 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 104.18.14.101:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 104.18.14.101:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECmNnjYFmfljCReA%2FraF%2BOY%3D | US | binary | 471 b | whitelisted |
3552 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | whitelisted |
3552 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2744 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
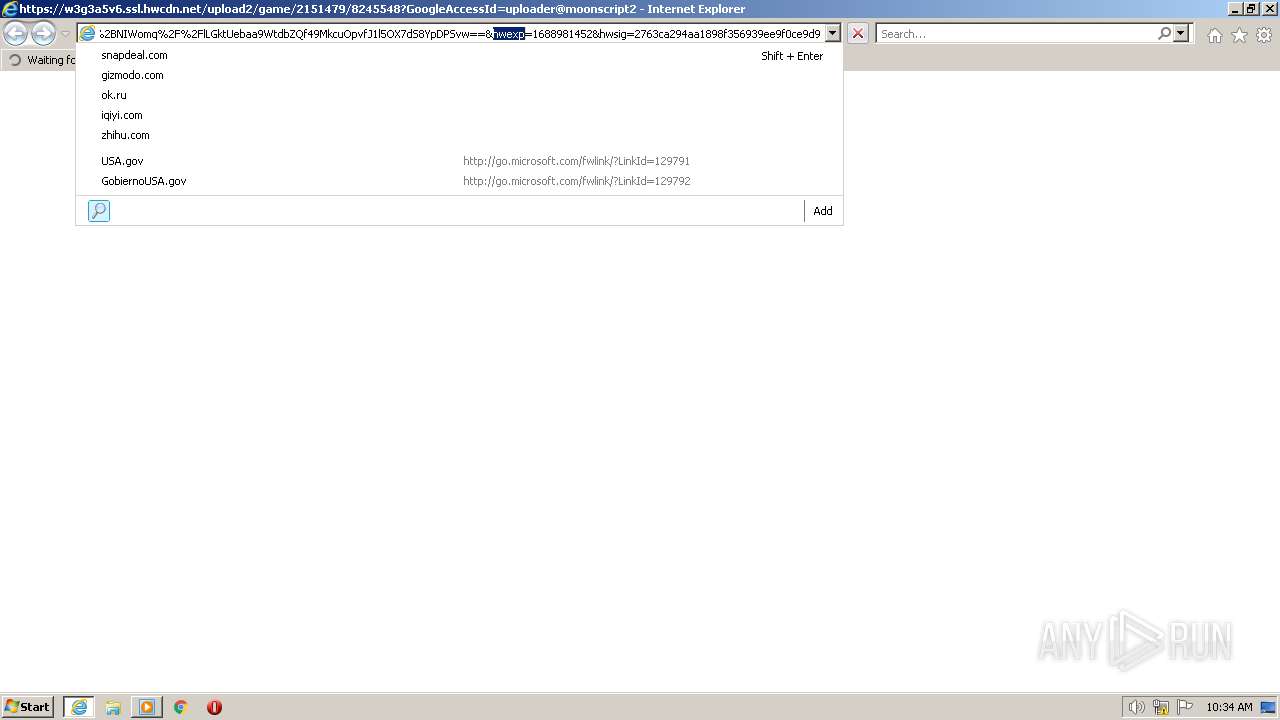
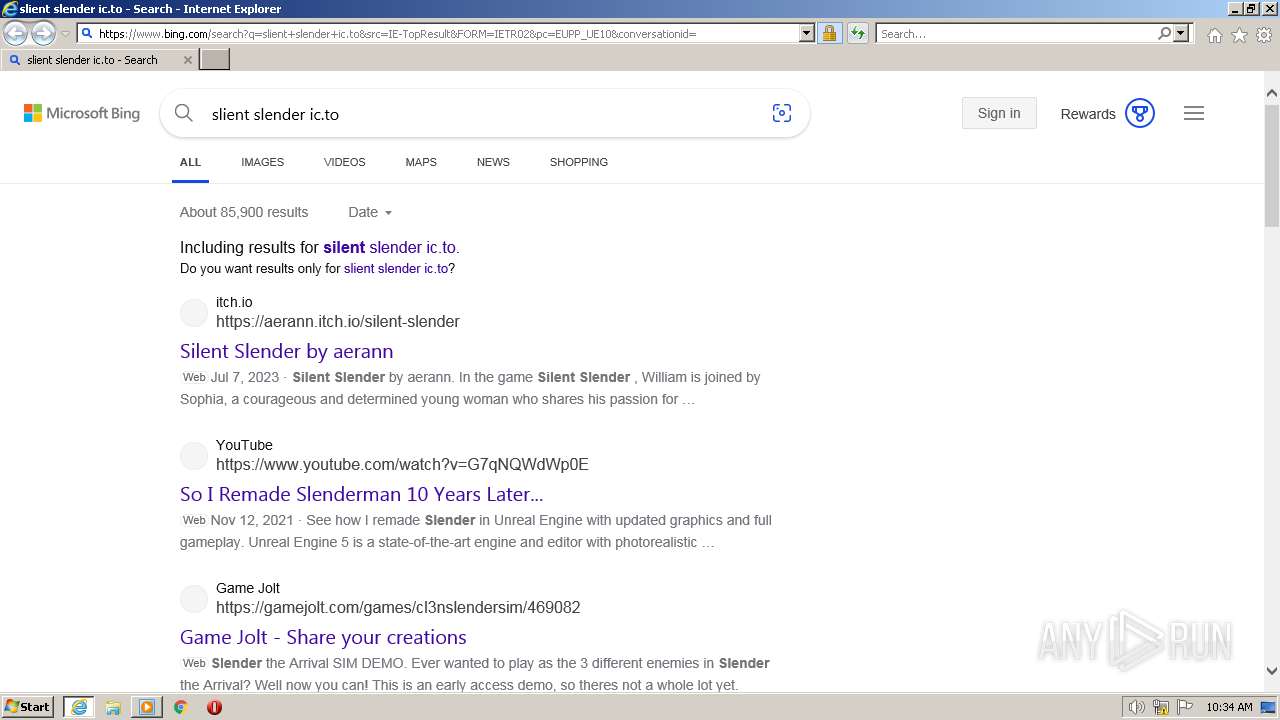
2976 | iexplore.exe | 184.86.251.23:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
2976 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2976 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2976 | iexplore.exe | 184.86.251.20:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
2976 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
3552 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2976 | iexplore.exe | 184.86.251.18:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
w3g3a5v6.ssl.hwcdn.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |