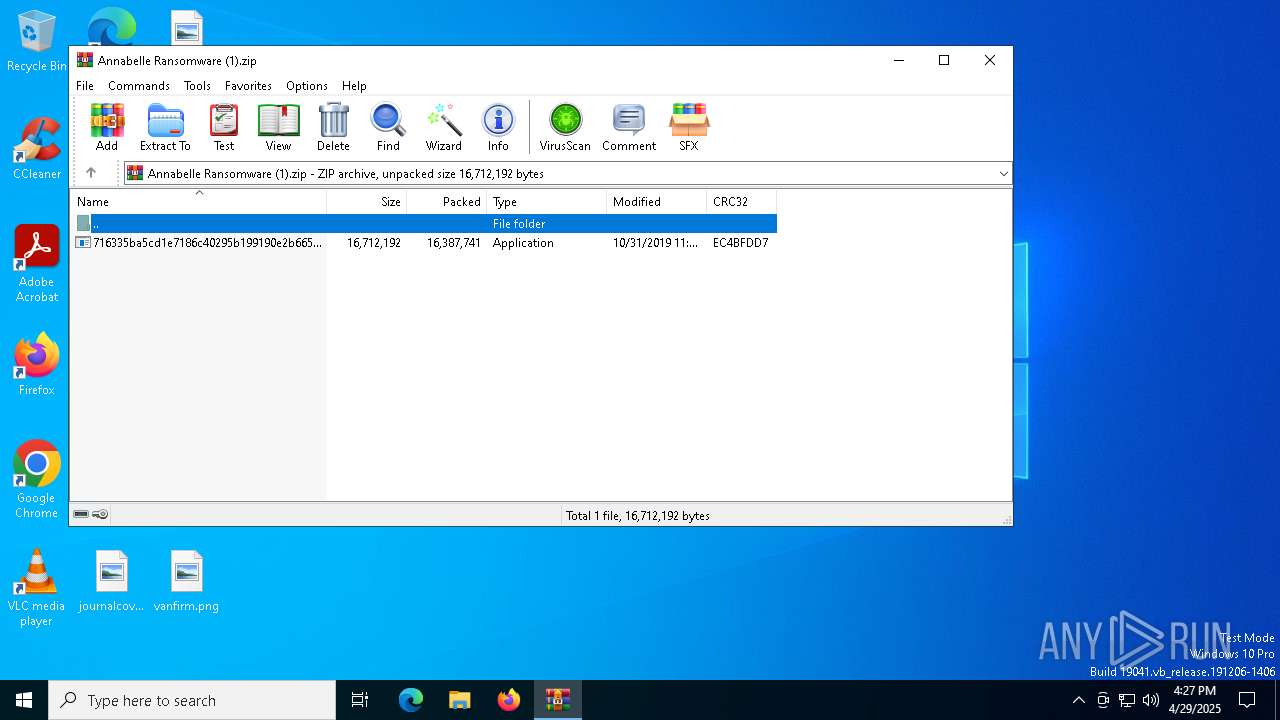
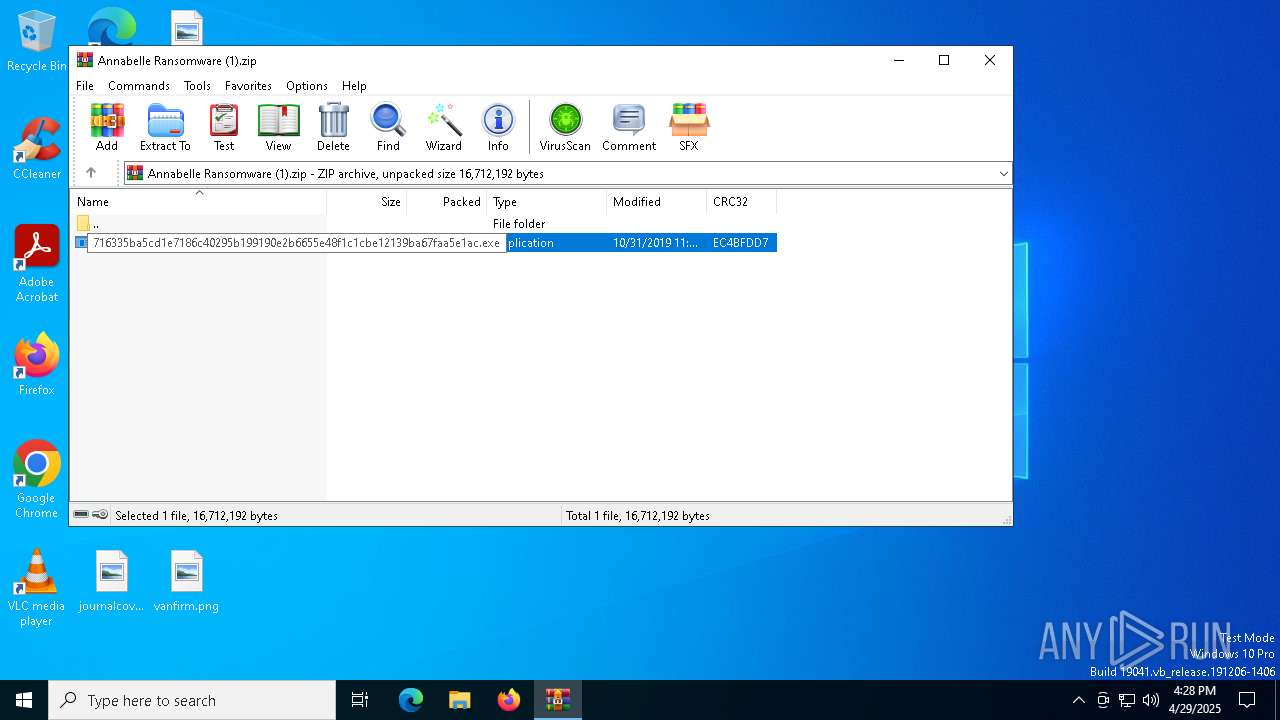
| File name: | Annabelle Ransomware (1).zip |
| Full analysis: | https://app.any.run/tasks/b6b3ae09-f67a-4fe5-8423-f23b00be3e39 |
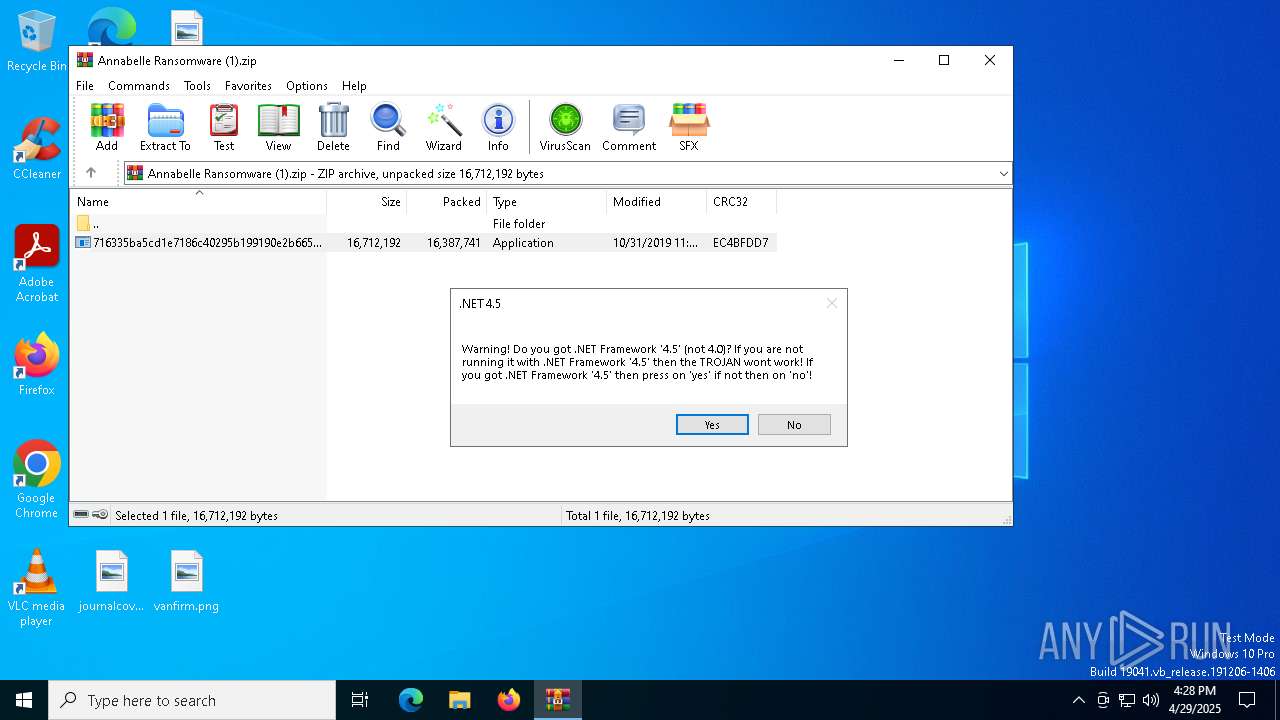
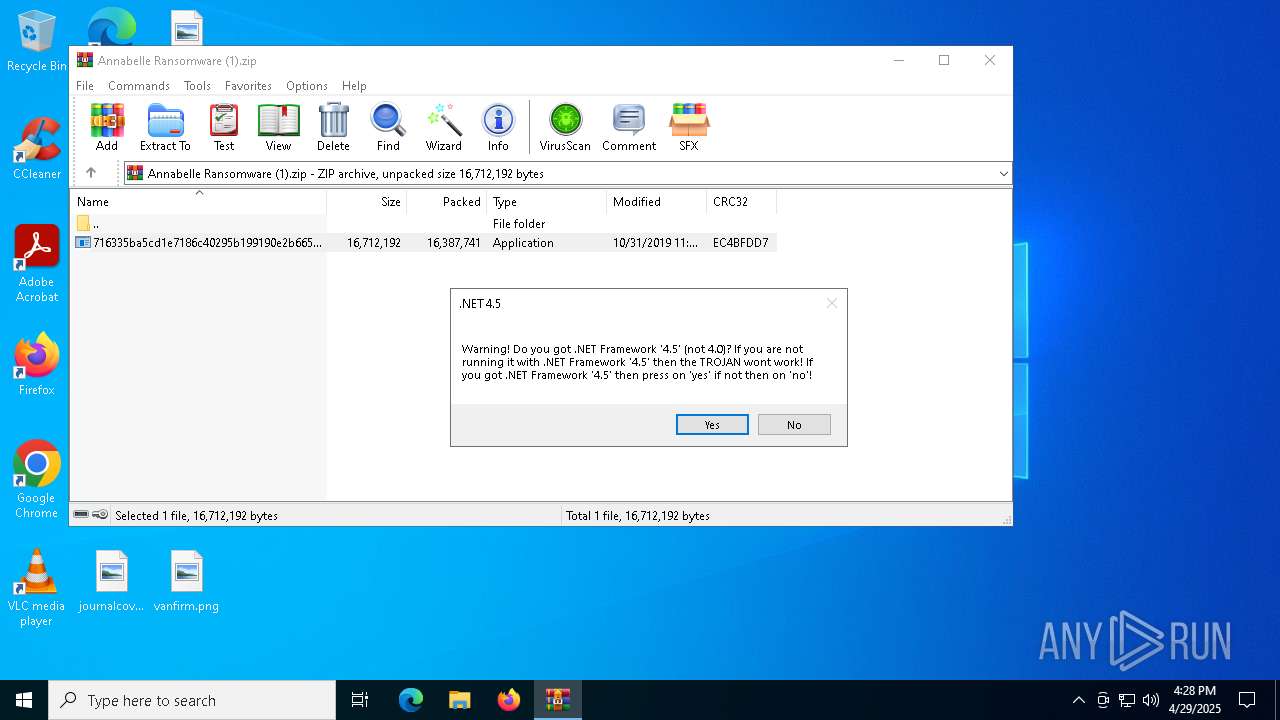
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 16:27:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 12B368C03D5126E918127B27C7D16086 |
| SHA1: | 93CCCEEC02435A7AC6A6A2D242278B80E2C67F7F |
| SHA256: | 6854B5F66A016C933C2978086D85CD4F207E5C35EE554422A3CDD9A88A5FFECD |
| SSDEEP: | 98304:6WAEeVzTs+K5nU+H3ZQkBEu6UcrffvWyB2FqqvLK/XiF2XiDHZvQSLwDIZMa8RiZ:vK9O811Cmq0gmli+kzTlkL0ktzZz9y |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5344)
Changes the autorun value in the registry
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Deletes shadow copies
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Disables task manager
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
UAC/LUA settings modification
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Changes the login/logoff helper path in the registry
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Disables the Run the Start menu
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Disables Windows Defender
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Changes image file execution options
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5344)
- ShellExperienceHost.exe (PID: 6972)
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Uses NETSH.EXE to change the status of the firewall
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Executes as Windows Service
- VSSVC.exe (PID: 728)
Creates file in the systems drive root
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Reads the date of Windows installation
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
The system shut down or reboot
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
INFO
Reads the computer name
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
- ShellExperienceHost.exe (PID: 6972)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5344)
Reads the machine GUID from the registry
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Confuser has been detected (YARA)
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Checks supported languages
- ShellExperienceHost.exe (PID: 6972)
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Process checks computer location settings
- 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:31 17:10:22 |
| ZipCRC: | 0xec4bfdd7 |
| ZipCompressedSize: | 16387741 |
| ZipUncompressedSize: | 16712192 |
| ZipFileName: | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe |
Total processes
135
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Annabelle Exit code: 3221226540 Version: 2.1.0.0 Modules
| |||||||||||||||
| 3268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Annabelle Version: 2.1.0.0 Modules
| |||||||||||||||
| 4108 | NetSh Advfirewall set allprofiles state off | C:\Windows\System32\netsh.exe | — | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | "C:\Windows\System32\shutdown.exe" -r -t 00 -f | C:\Windows\System32\shutdown.exe | — | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5344 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Annabelle Ransomware (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 513
Read events
4 416
Write events
97
Delete events
0
Modification events
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Annabelle Ransomware (1).zip | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4040) 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateBackup |
Value: C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | |||
| (PID) Process: | (4040) 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateBackup |
Value: C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | |||
Executable files
1
Suspicious files
24
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Documents\changesroyal.rtf.ANNABELLE | binary | |
MD5:C1A4AD0CAACC3388787B1A483C8F6050 | SHA256:52FAC9F021708569513D6B761724B8677413BBAF74F66C827032AFD9847FD620 | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Documents\Database1.accdb.ANNABELLE | binary | |
MD5:6923415A237011EFB8D48C0981D40E42 | SHA256:66C65F8208725E985A2DE2E56200173FC3F91FBDB64EFDE9DF799945BF0E9E1C | |||
| 5344 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5344.39004\716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | executable | |
MD5:0F743287C9911B4B1C726C7C7EDCAF7D | SHA256:716335BA5CD1E7186C40295B199190E2B6655E48F1C1CBE12139BA67FAA5E1AC | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Documents\fordcomplex.rtf.ANNABELLE | binary | |
MD5:76A677D425B46BFE9CC3E6AF2D7C40D1 | SHA256:AFE660F9CA6C3869EA86433ECDBC1044329E2A00D7E07EF9A160F494DAD455CE | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Documents\resultoptions.rtf.ANNABELLE | binary | |
MD5:BD6AAC90E2A83A5089BE89CC681701A6 | SHA256:2DF732691D04B6F99EE365C14FC0579D8E1AF70CB1EEE5FA9296A9F53F2DCDF9 | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Downloads\usezip.png.ANNABELLE | binary | |
MD5:6E9A46391B5490050FE883B9398E8585 | SHA256:808B1E72C0FDF94157A4F2CB109BB058AF46962701A3ED26BF755A0E73029782 | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Downloads\saysre.jpg.ANNABELLE | binary | |
MD5:7FC644D5D06013029AA757038FD92F81 | SHA256:397756172E1798CFE97805E2D8DEF0430DB6A88B808D637188E58D6C59BE2A6E | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Desktop\angelesapplications.jpg.ANNABELLE | binary | |
MD5:F8CFF0EB70073F0DE13D9E58A82E679D | SHA256:57EF361ACC1807116E6944A6B69D07A43C3245C210B86EB144F8DCA19B2960C3 | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Desktop\chancepersonal.rtf.ANNABELLE | binary | |
MD5:EE7ADBB1DCA791231C7157911CAED269 | SHA256:D522686F972089F238EA91E6D40C370465394D4673AFEDEF4555B380A3260E5D | |||
| 4040 | 716335ba5cd1e7186c40295b199190e2b6655e48f1c1cbe12139ba67faa5e1ac.exe | C:\Users\admin\Desktop\letof.jpg.ANNABELLE | binary | |
MD5:C10101B83A0D19AA96F3FD11E9EEEB88 | SHA256:FAA6CAC3F81065BE525D04A813789B16C473385CDD975A0EAD2BD3F013EFD3F2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 429 | 146.112.255.205:80 | http://myip.dnsomatic.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2292 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3812 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 20.189.173.8:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Device Retrieving External IP Address Detected | ET INFO Internal Host Retrieving External IP via myip.dnsomatic.com |