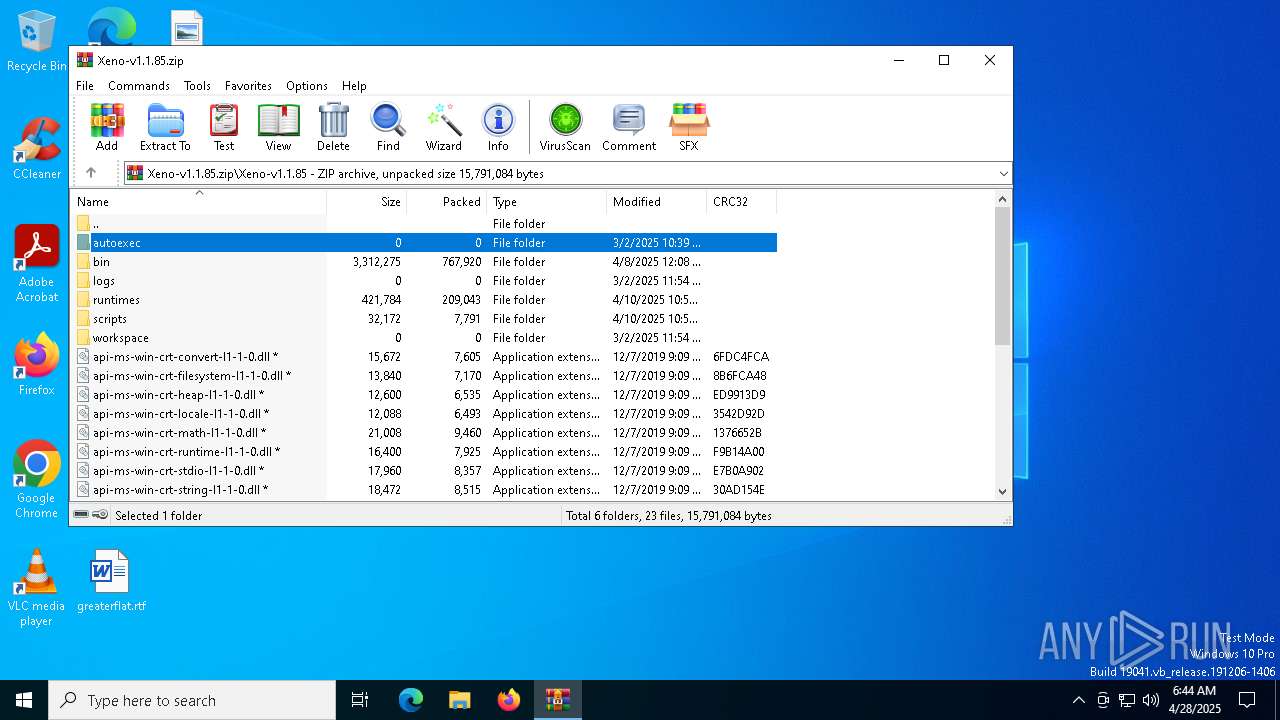
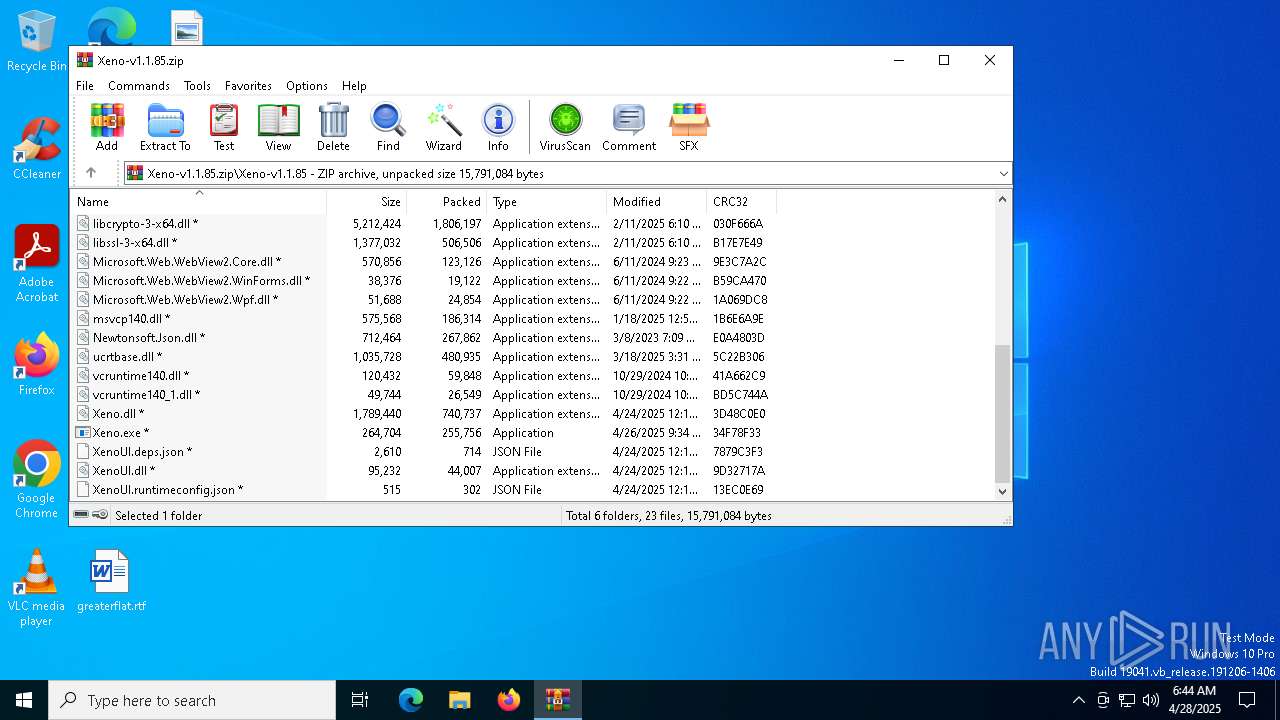
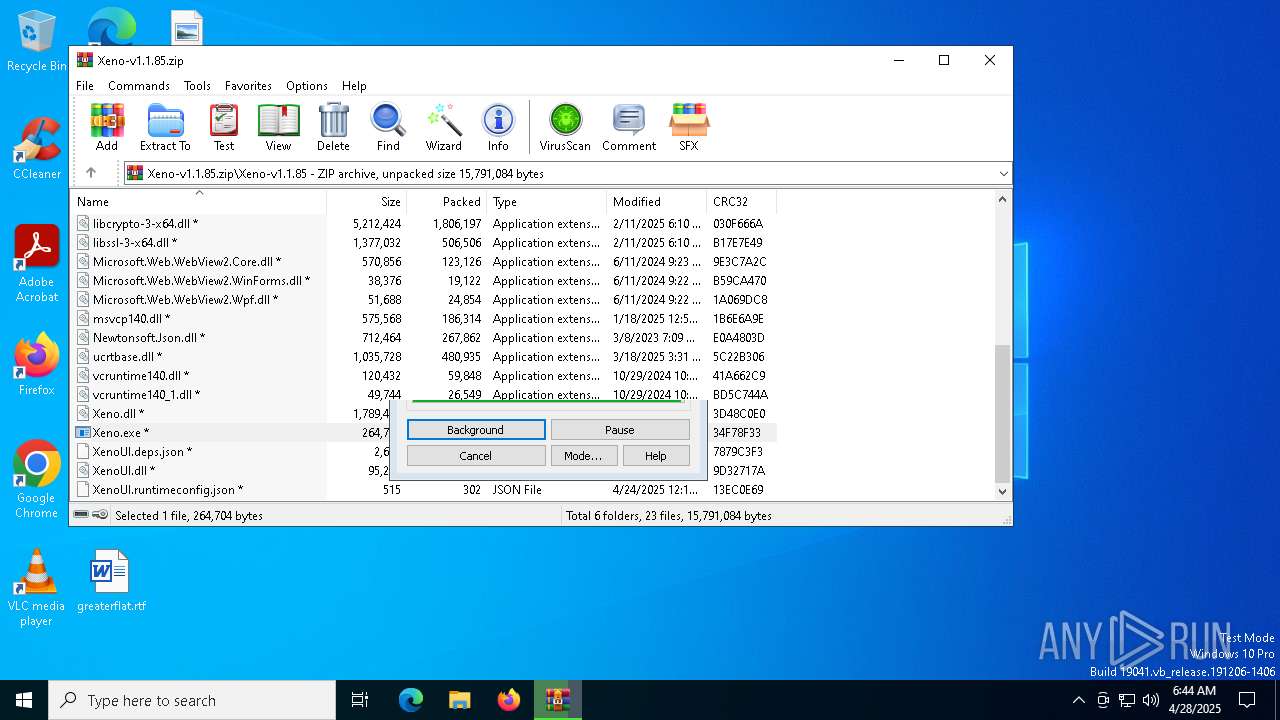
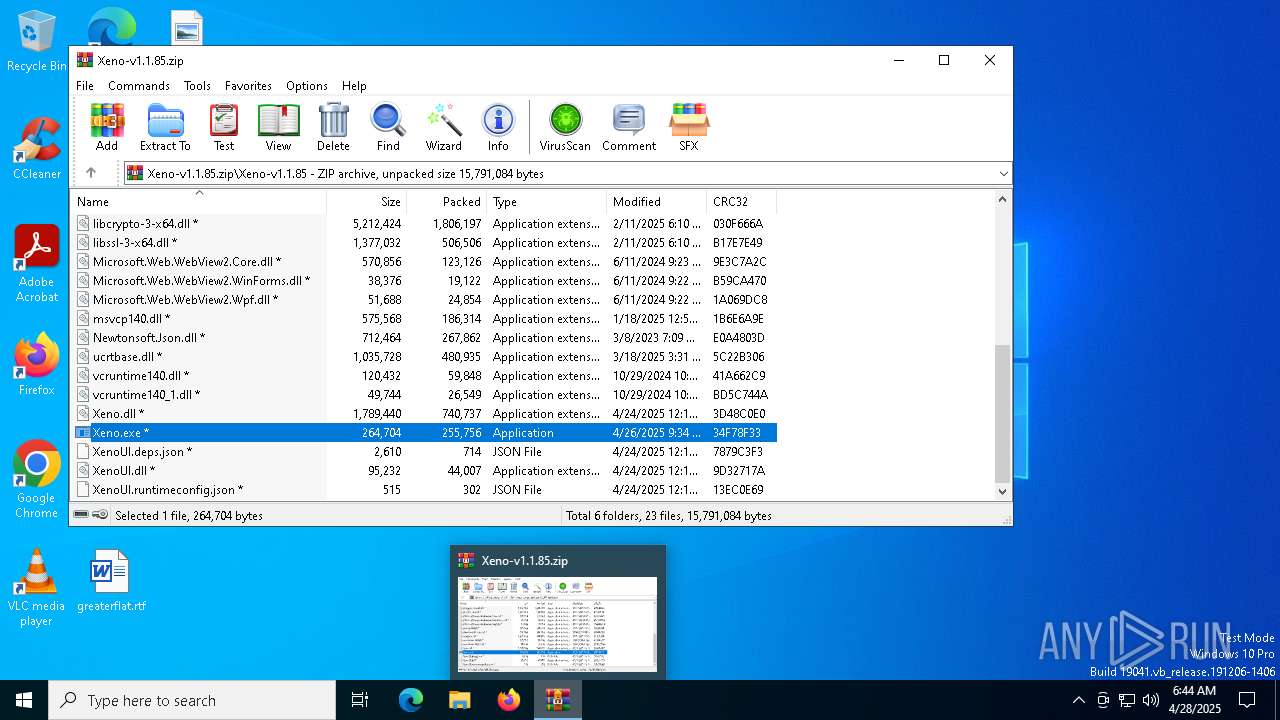
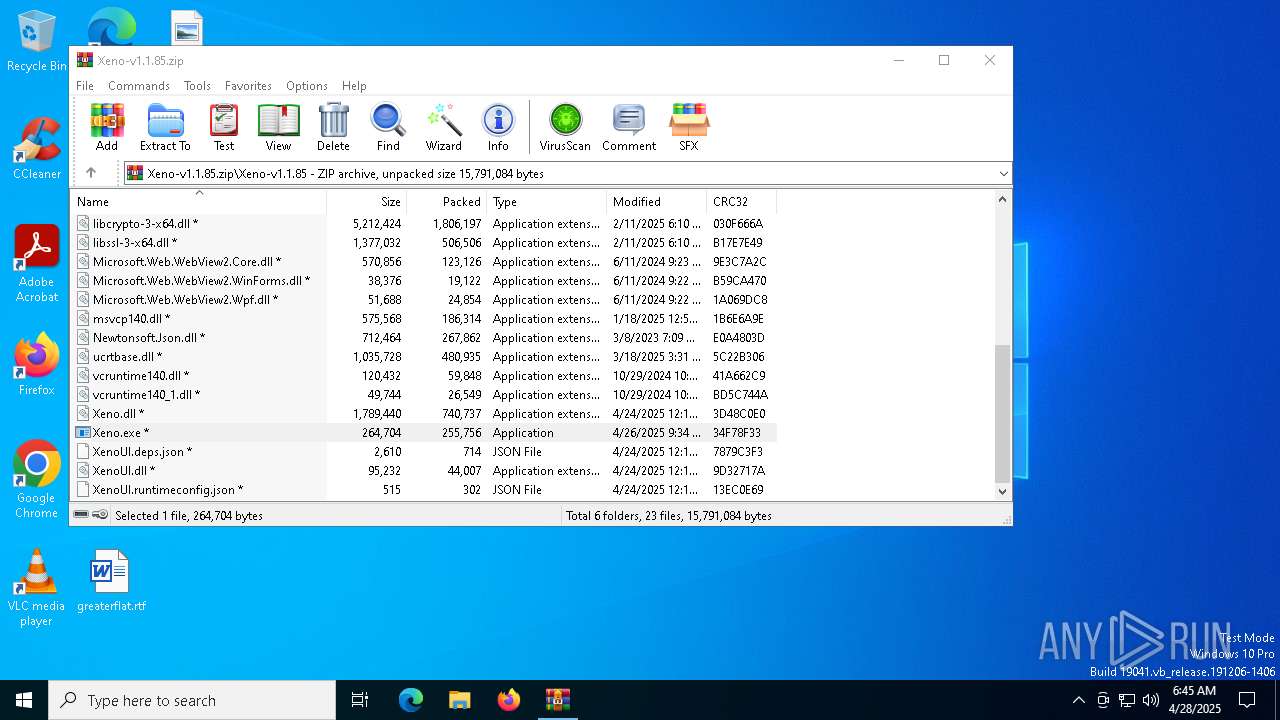
| File name: | Xeno-v1.1.85.zip |
| Full analysis: | https://app.any.run/tasks/7accb7c8-f6e8-4711-9899-384cf73434cf |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 06:44:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 8DC48580B78A0A28852BC36A86FA0CBE |
| SHA1: | E623288FF807D0A62A770B06BF5B84E1FE3B6A7D |
| SHA256: | 68517F68220A1C0397E29692E6AC5D067844EC8ECF844DBFDF5119F727E0A992 |
| SSDEEP: | 98304:/6PD8Q3qq6fphkP6uoeflIZ0aJnPejqlwlA/Kli5zc/Rh8YN73Ng61IYBhQNkn9F:J6Bqr7amFvnC |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4868)
- cmd.exe (PID: 1852)
Changes the AppInit_DLLs value (autorun option)
- XenoUI.exe (PID: 6044)
Changes the login/logoff helper path in the registry
- XenoUI.exe (PID: 6044)
Bypass execution policy to execute commands
- powershell.exe (PID: 7648)
SUSPICIOUS
Reads the date of Windows installation
- Xeno.exe (PID: 8160)
- Xeno.exe (PID: 5376)
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
Reads security settings of Internet Explorer
- Xeno.exe (PID: 5376)
- WinRAR.exe (PID: 7440)
- Xeno.exe (PID: 8160)
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
- tmpC149.tmp.exe (PID: 7620)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7440)
Application launched itself
- Xeno.exe (PID: 8160)
Executable content was dropped or overwritten
- Xeno.exe (PID: 5376)
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
Starts itself from another location
- XenoUI.exe (PID: 6044)
Contacting a server suspected of hosting an CnC
- crss.exe (PID: 920)
Starts CMD.EXE for commands execution
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
Starts process via Powershell
- powershell.exe (PID: 7648)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7560)
Connects to unusual port
- crss.exe (PID: 920)
SQL CE related mutex has been found
- tmpC149.tmp.exe (PID: 7620)
The process executes via Task Scheduler
- crss.exe (PID: 1616)
- crss.exe (PID: 3956)
The system shut down or reboot
- cmd.exe (PID: 7324)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7440)
Reads the computer name
- Xeno.exe (PID: 8160)
- Xeno.exe (PID: 7280)
- Xeno.exe (PID: 5376)
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
- tmpC149.tmp.exe (PID: 7620)
- crss.exe (PID: 3956)
- crss.exe (PID: 1616)
Reads the machine GUID from the registry
- Xeno.exe (PID: 5376)
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
- tmpC149.tmp.exe (PID: 7620)
- crss.exe (PID: 1616)
- crss.exe (PID: 3956)
Process checks computer location settings
- Xeno.exe (PID: 8160)
- Xeno.exe (PID: 5376)
- XenoUI.exe (PID: 6044)
- crss.exe (PID: 920)
Checks supported languages
- Xeno.exe (PID: 7280)
- Xeno.exe (PID: 5376)
- Xeno.exe (PID: 8160)
- crss.exe (PID: 920)
- XenoUI.exe (PID: 6044)
- tmpC149.tmp.exe (PID: 7620)
- crss.exe (PID: 1616)
- crss.exe (PID: 3956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7440)
Create files in a temporary directory
- Xeno.exe (PID: 5376)
- tmpC149.tmp.exe (PID: 7620)
- crss.exe (PID: 920)
Creates files in the program directory
- XenoUI.exe (PID: 6044)
- tmpC149.tmp.exe (PID: 7620)
Reads Environment values
- crss.exe (PID: 920)
The executable file from the user directory is run by the Powershell process
- tmpC149.tmp.exe (PID: 7620)
Creates files or folders in the user directory
- tmpC149.tmp.exe (PID: 7620)
Reads the software policy settings
- crss.exe (PID: 920)
- slui.exe (PID: 5048)
Checks proxy server information
- slui.exe (PID: 5048)
- tmpC149.tmp.exe (PID: 7620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:27 12:26:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Xeno-v1.1.85/ |
Total processes
156
Monitored processes
25
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\WINDOWS\crss.exe" | C:\Windows\crss.exe | XenoUI.exe | ||||||||||||
User: admin Company: XenoUI Integrity Level: HIGH Description: XenoUI Exit code: 1073807364 Version: 1.1.8.0 Modules
| |||||||||||||||
| 1616 | "C:\WINDOWS\crss.exe" | C:\Windows\crss.exe | — | svchost.exe | |||||||||||
User: admin Company: XenoUI Integrity Level: HIGH Description: XenoUI Exit code: 0 Version: 1.1.8.0 Modules
| |||||||||||||||
| 1852 | "cmd" /c schtasks /create /f /sc minute /mo 1 /tn "Microsoft\Windows\WAppCrashNvTew" /tr "C:\WINDOWS\crss.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | XenoUI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | schtasks /create /f /sc minute /mo 30 /tn "Microsoft\MachineCore" /tr "C:\Program Files\CrashReports\RobloxCrashHandler.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | Shutdown /s /f /t 00 | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3956 | "C:\WINDOWS\crss.exe" | C:\Windows\crss.exe | — | svchost.exe | |||||||||||
User: admin Company: XenoUI Integrity Level: HIGH Description: XenoUI Exit code: 0 Version: 1.1.8.0 Modules
| |||||||||||||||
| 4180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4868 | "cmd" /c schtasks /create /f /sc minute /mo 30 /tn "Microsoft\MachineCore" /tr "C:\Program Files\CrashReports\RobloxCrashHandler.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | XenoUI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 623
Read events
14 543
Write events
79
Delete events
1
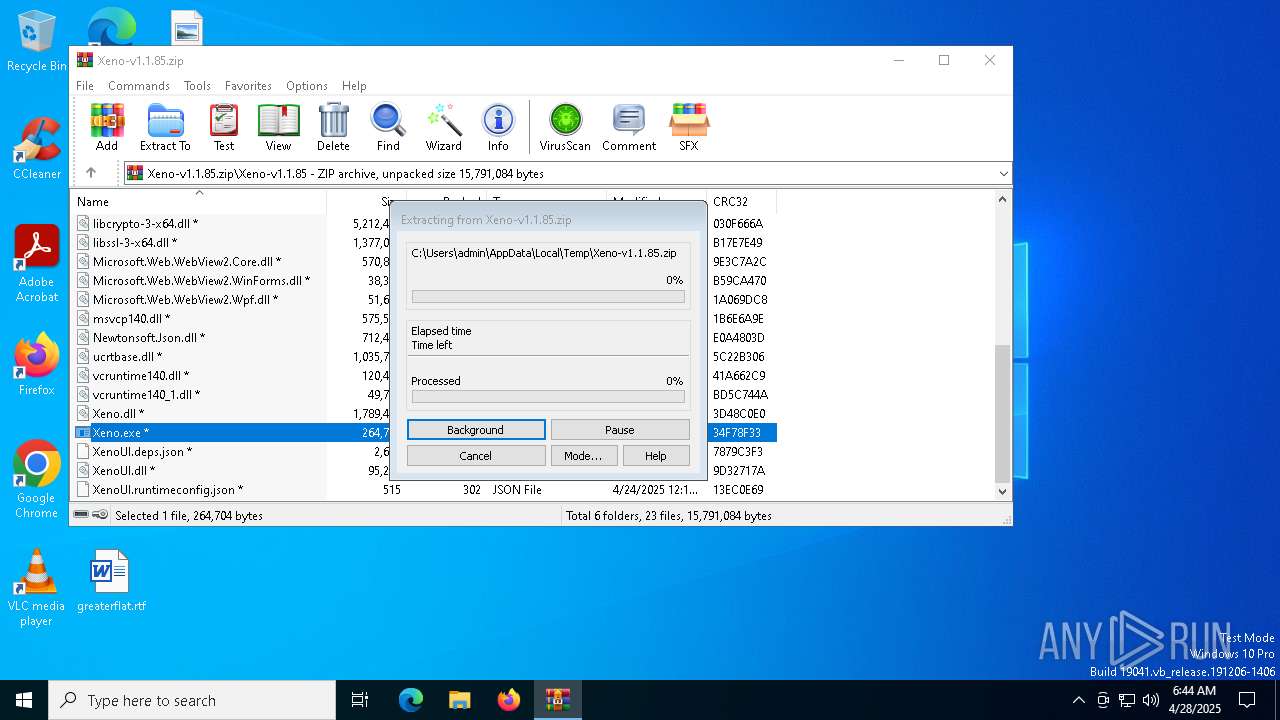
Modification events
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Xeno-v1.1.85.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
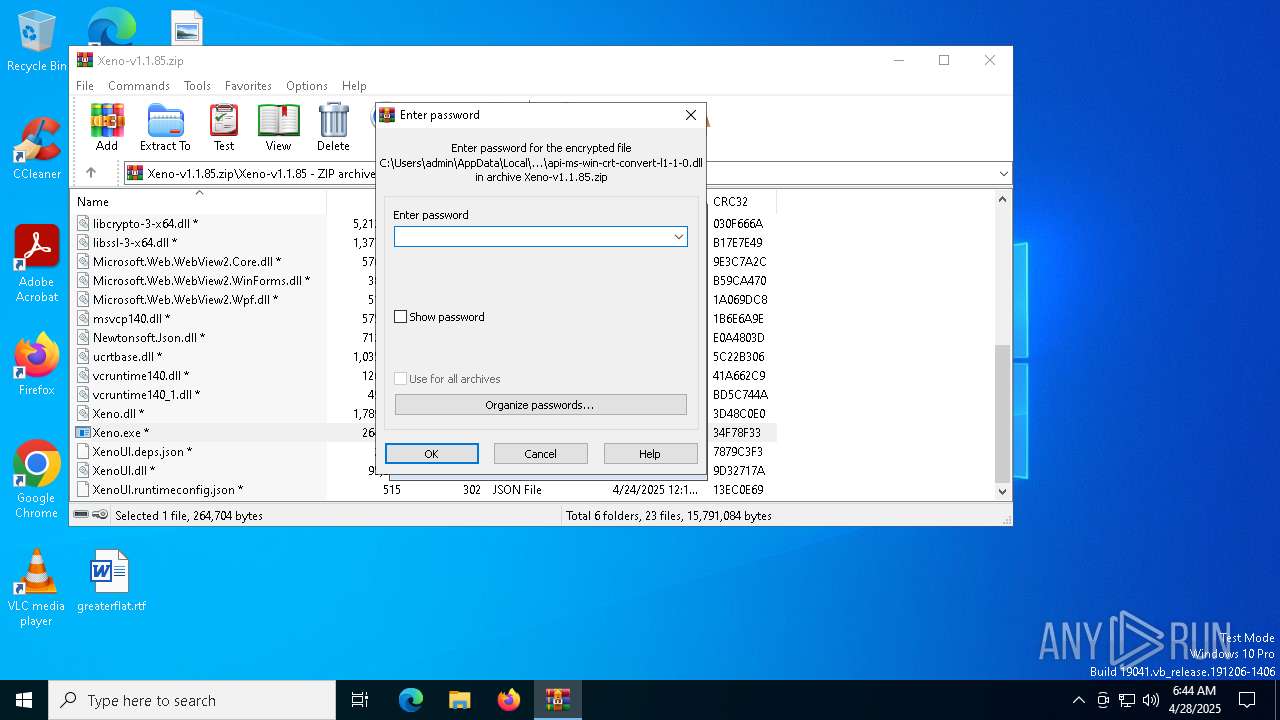
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6044) XenoUI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\System32\userinit.exe,C:\WINDOWS\crss.exe | |||
Executable files
30
Suspicious files
12
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\api-ms-win-crt-stdio-l1-1-0.dll | executable | |
MD5:429C26ED27A026442F89C95FF16CE8C2 | SHA256:2A466648AFFD3D51B944F563BB65046A3DA91006A0D90FB2C0B123487A1FC1B3 | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\api-ms-win-crt-filesystem-l1-1-0.dll | executable | |
MD5:42A2A95F1BB940D01F55EB1674A81FE2 | SHA256:51541EC6684B43157A85EA46A42EBED4555BE06BED0D0D07FF3EA6377301318D | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\api-ms-win-crt-heap-l1-1-0.dll | executable | |
MD5:98DA186FD7D7873C164A51C5D7B77F1A | SHA256:80139E4CAA379D87B1D1DAFC23ACE71D2B330368115F6314140D4AE59C2A78E8 | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\api-ms-win-crt-string-l1-1-0.dll | executable | |
MD5:0F593E50BE4715AA8E1F6EB39434EDD5 | SHA256:BF4EA10BE1B64C442AC0CCF4BDF69F6703467176A27E9E14A488D26448A6E179 | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\api-ms-win-crt-convert-l1-1-0.dll | executable | |
MD5:C8DBF0CA88FACFE87899168A7F7DB52C | SHA256:94B6E91B93C2202DABD659BFF294BEE87C22897A30A6B4930B49051C2FB502DC | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\bin\Monaco\vs\editor\editor.main.nls.ja.js | text | |
MD5:3BF851CC70F515CBBE1D39DA93E4F041 | SHA256:1F3556EA7233843B9E08B3C97B6727C533D702563E195C2090A438070DC85F0F | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\bin\Monaco\index.html | html | |
MD5:001DCBB8F41CDCBF9B4D1E3A0ED4B2D2 | SHA256:F1D2C52F2803C29585B81D2EFF74C56242D27E9619EE6D38081D5604C5BB1951 | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\bin\Monaco\vs\base\worker\workerMain.js | binary | |
MD5:D0AC5294C58E523CDDF25BC6D785FA48 | SHA256:E90D1A8F116FA74431117A3AD78DDE16DDE060A4BF7528DFE3D5A3AD6156504B | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\bin\Monaco\vs\editor\editor.main.nls.it.js | text | |
MD5:18E88F58301AD5AE926204507AB99C6B | SHA256:4FE2C4420294758883E134BDF7DA9E6C2ABF631D3A89C765F32F6C1D0F62653C | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7440.094\Xeno-v1.1.85\bin\Monaco\vs\editor\editor.main.css | text | |
MD5:23C7DB6E12F6454EF6E7FB98D17924D8 | SHA256:615824C59ED1E07F5924286E9F02F3120B9064D59E115D3F668A914E07839451 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
18
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
java-chassis.gl.at.ply.gg |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
920 | crss.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |