| File name: | LBB.exe |
| Full analysis: | https://app.any.run/tasks/20ca2841-f287-48bf-8553-fa36bc66271f |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | January 22, 2024, 15:22:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3DF94BCDF20A47E67AC894788480F931 |
| SHA1: | 2A4D454AA31CEE3C8DB66301AFBD48786AA30839 |
| SHA256: | 68495CD89DB27E22650876B9A354E8F7FFF66F180B7EA3DC33065D5C9DC57A30 |
| SSDEEP: | 6144:99fakdv3IsoXzSlZNjqxx1PY8Qa7mIfYlmFj:95akRPZNjqxx1Qo7BEi |
MALICIOUS
Drops the executable file immediately after the start
- LBB.exe (PID: 2044)
- LBB.exe (PID: 316)
Known privilege escalation attack
- dllhost.exe (PID: 2416)
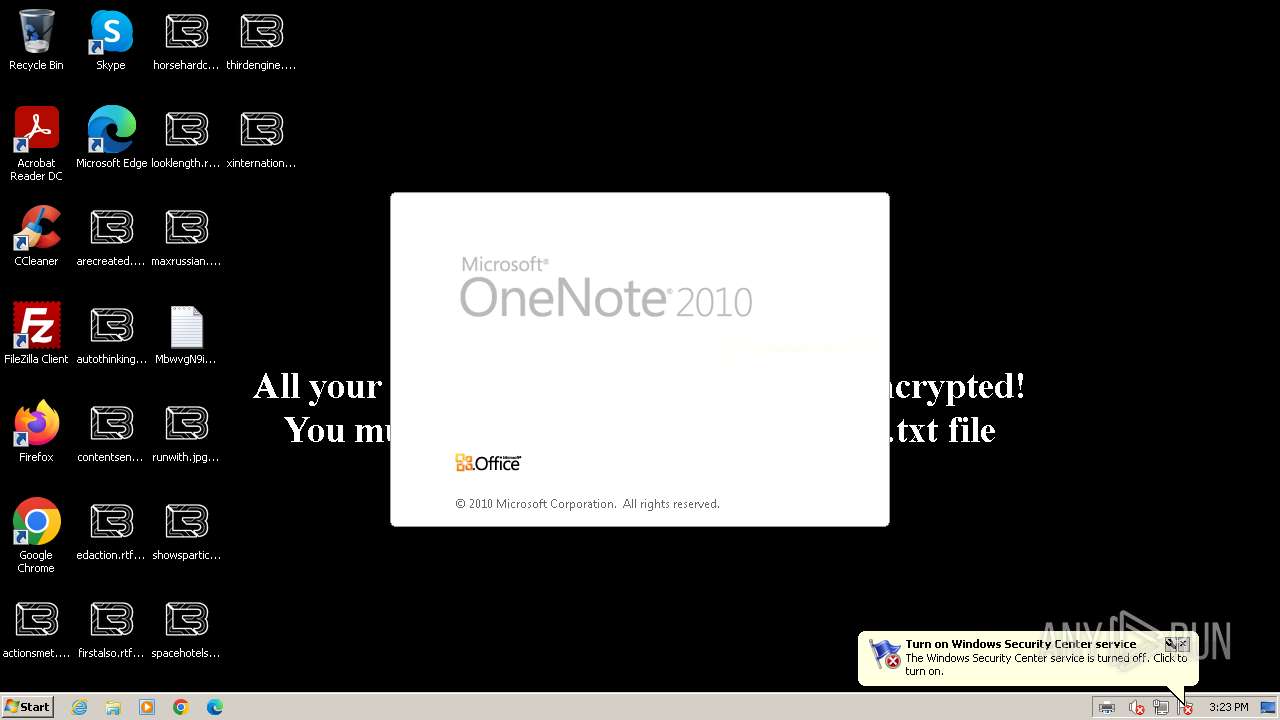
Renames files like ransomware
- LBB.exe (PID: 316)
Creates a writable file in the system directory
- printfilterpipelinesvc.exe (PID: 2632)
- LBB.exe (PID: 316)
[YARA] LockBit is detected
- LBB.exe (PID: 316)
Actions looks like stealing of personal data
- LBB.exe (PID: 2044)
SUSPICIOUS
Reads the Internet Settings
- LBB.exe (PID: 2044)
Executable content was dropped or overwritten
- LBB.exe (PID: 2044)
- LBB.exe (PID: 316)
Write to the desktop.ini file (may be used to cloak folders)
- LBB.exe (PID: 316)
Creates files like ransomware instruction
- LBB.exe (PID: 316)
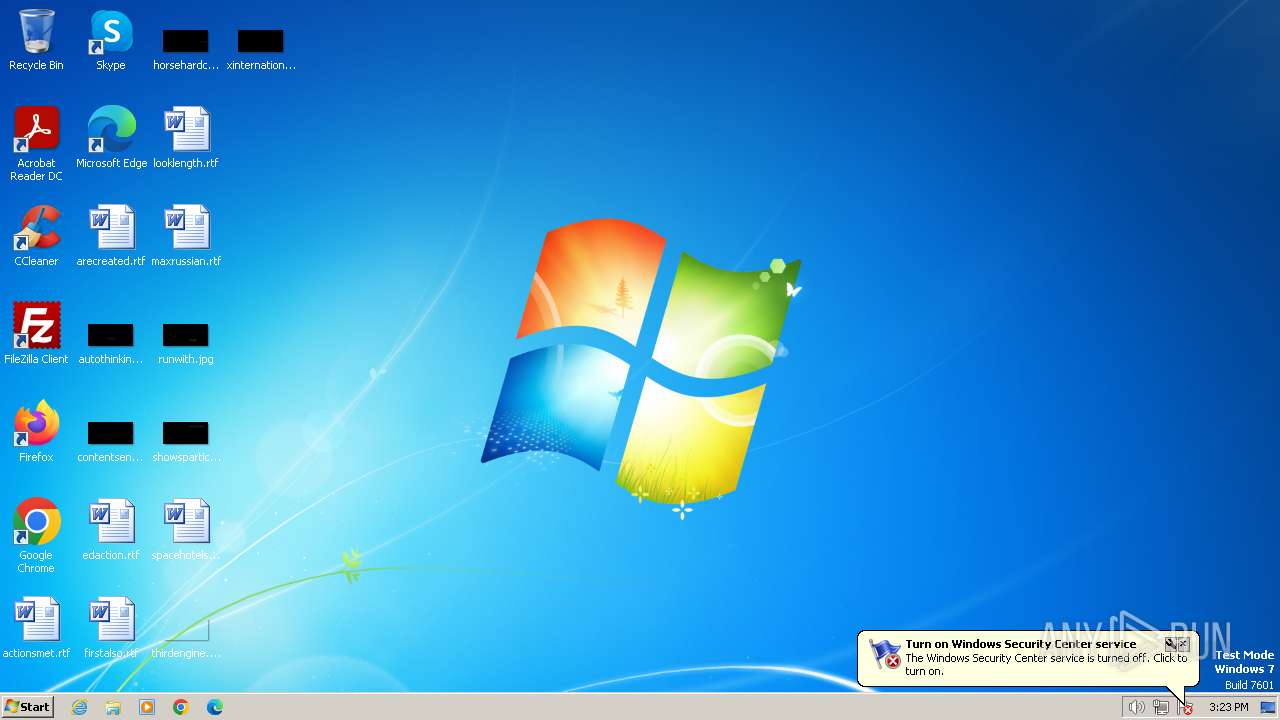
Changes the desktop background image
- LBB.exe (PID: 316)
Starts application with an unusual extension
- LBB.exe (PID: 316)
INFO
Checks supported languages
- LBB.exe (PID: 2044)
- LBB.exe (PID: 1432)
- LBB.exe (PID: 316)
- ONENOTE.EXE (PID: 1384)
- 436E.tmp (PID: 452)
Reads the computer name
- LBB.exe (PID: 2044)
- LBB.exe (PID: 1432)
- LBB.exe (PID: 316)
- ONENOTE.EXE (PID: 1384)
Checks transactions between databases Windows and Oracle
- LBB.exe (PID: 1432)
Create files in a temporary directory
- LBB.exe (PID: 2044)
- LBB.exe (PID: 316)
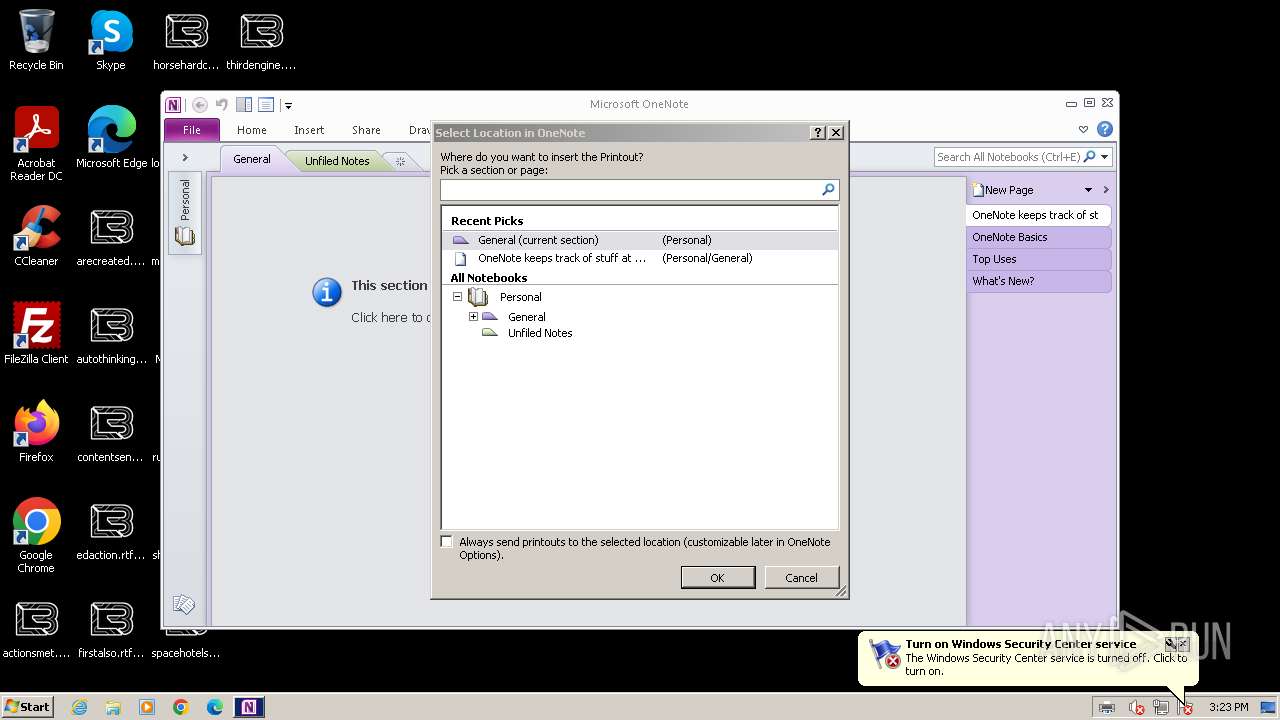
- ONENOTE.EXE (PID: 1384)
Reads the machine GUID from the registry
- LBB.exe (PID: 1432)
- LBB.exe (PID: 316)
- ONENOTE.EXE (PID: 1384)
Creates files in the program directory
- LBB.exe (PID: 316)
Creates files or folders in the user directory
- printfilterpipelinesvc.exe (PID: 2632)
Reads Environment values
- ONENOTE.EXE (PID: 1384)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 1384)
Dropped object may contain TOR URL's
- LBB.exe (PID: 316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (93.8) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (2.3) |
| .exe | | | Win32 Executable (generic) (1.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.7) |
| .exe | | | Generic Win/DOS Executable (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
48
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\AppData\Local\Temp\3582-490\LBB.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\LBB.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 452 | "C:\ProgramData\436E.tmp" | C:\ProgramData\436E.tmp | — | LBB.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
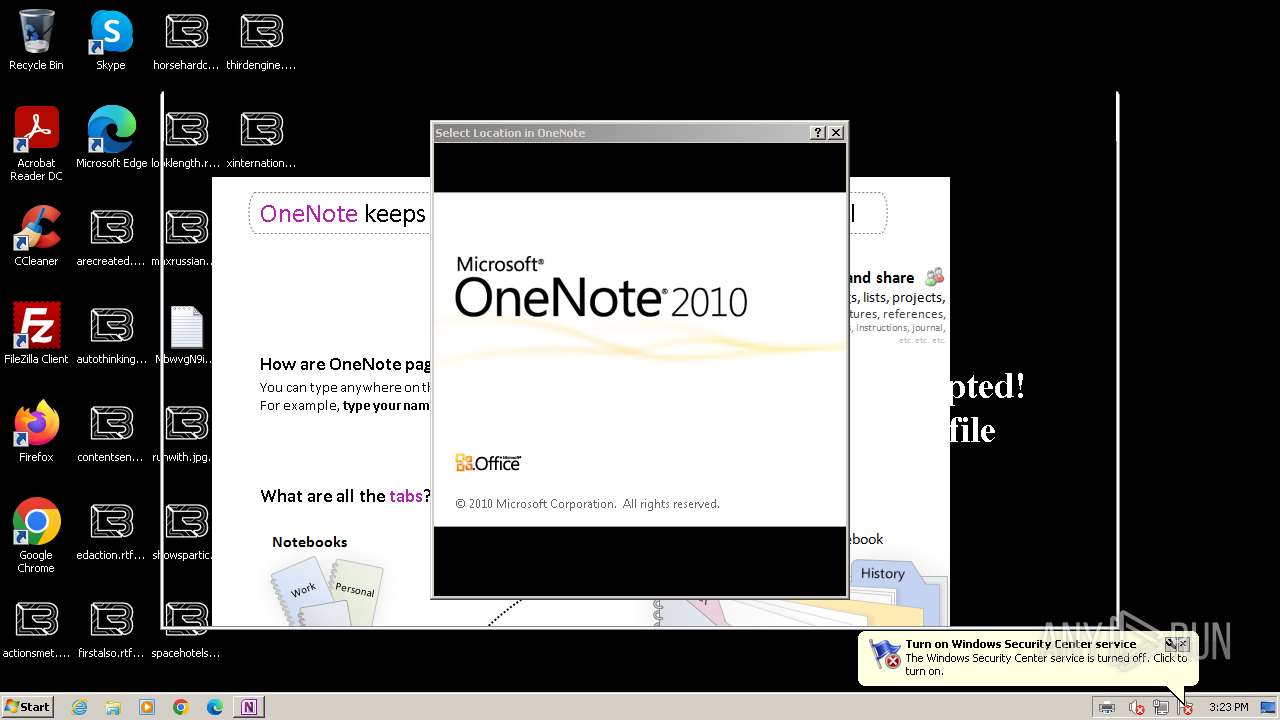
| 1384 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{966AA8CA-7706-41ED-A390-6AE89F1A912D}.xps" 133504105934290000 | C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE | — | printfilterpipelinesvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft OneNote Exit code: 0 Version: 14.0.6022.1000 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Temp\3582-490\LBB.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\LBB.exe | — | LBB.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\AppData\Local\Temp\LBB.exe" | C:\Users\admin\AppData\Local\Temp\LBB.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2416 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | C:\Windows\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\System32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Exit code: 0 Version: 6.1.7601.24537 (win7sp1_ldr_escrow.191114-1547) Modules
| |||||||||||||||
Total events
4 076
Read events
3 032
Write events
1 043
Delete events
1
Modification events
| (PID) Process: | (2044) LBB.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2044) LBB.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2044) LBB.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2044) LBB.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2416) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2416) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2416) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2416) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (316) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 115 | |||
| (PID) Process: | (316) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\Analytic |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
45
Suspicious files
209
Text files
102
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe | executable | |
MD5:566ED4F62FDC96F175AFEDD811FA0370 | SHA256:E17CD94C08FC0E001A49F43A0801CEA4625FB9AEE211B6DFEBEBEC446C21F460 | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0410-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0416-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0411-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0412-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2044 | LBB.exe | C:\MSOCache\All Users\{90140000-006E-0412-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |