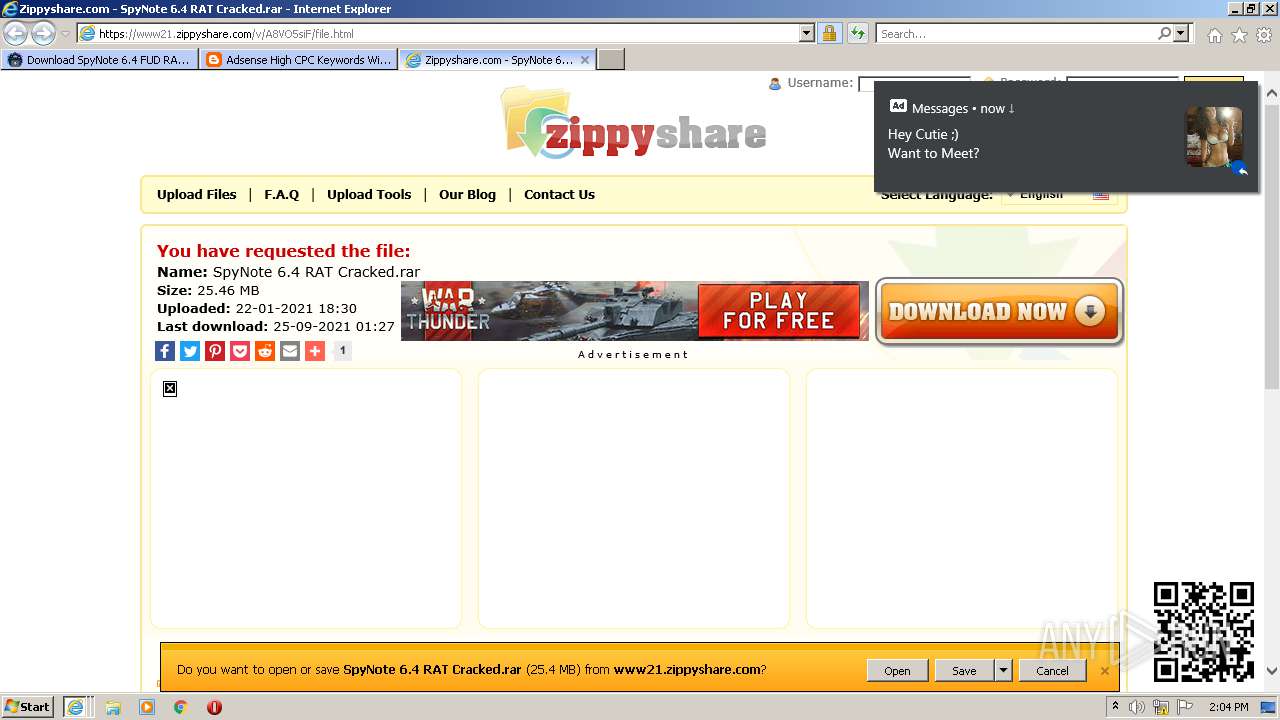
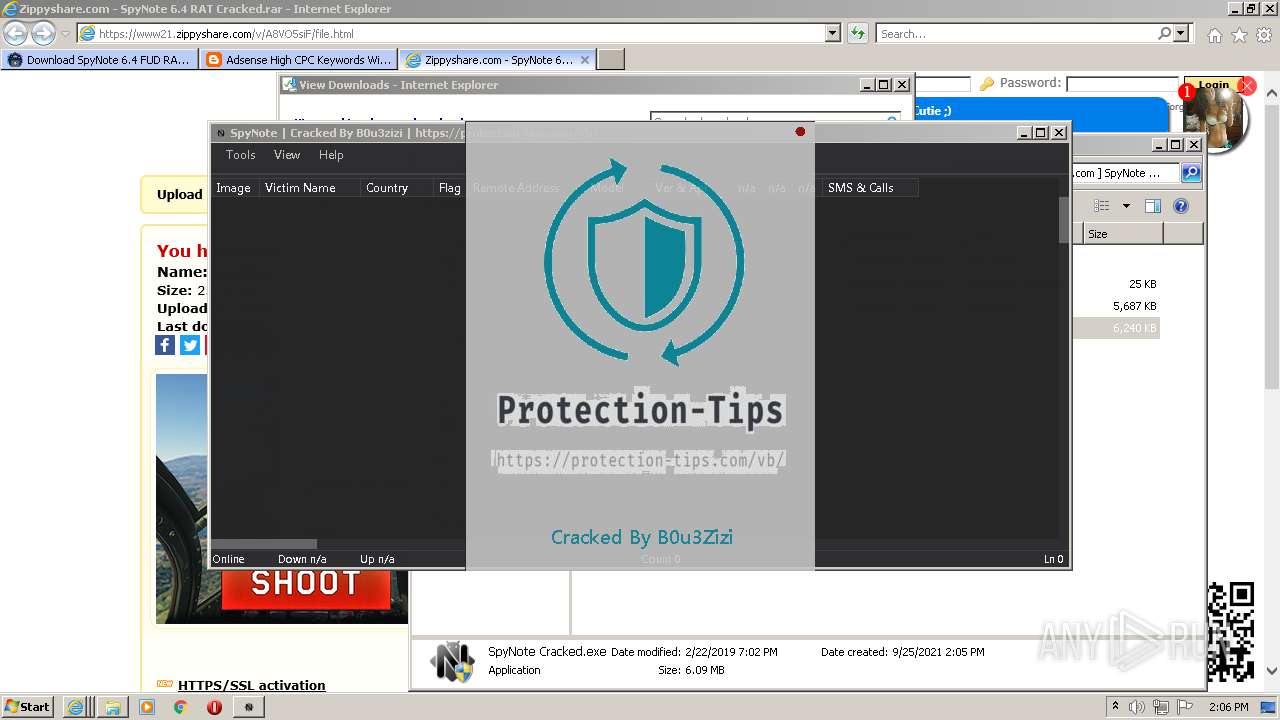
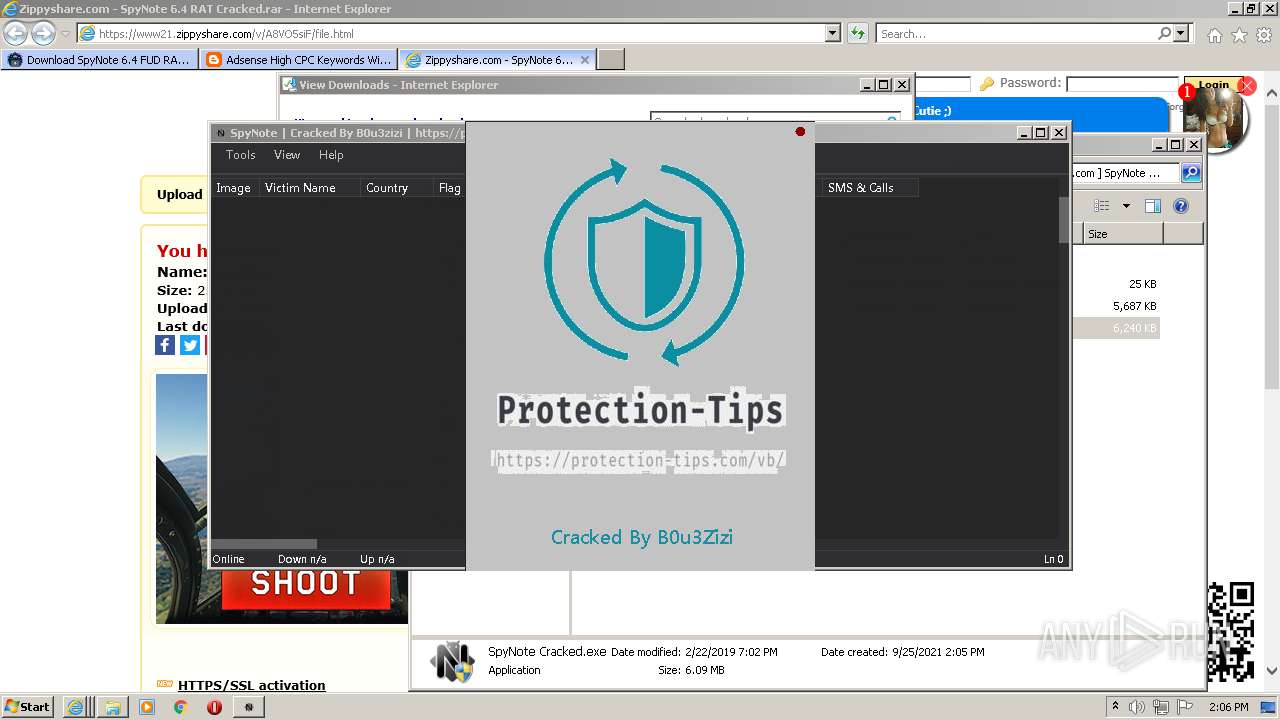
| URL: | https://www.majidzhacker.com/2021/01/download-spynote-6.4.html |
| Full analysis: | https://app.any.run/tasks/e8b08319-8d5c-4ae4-901a-fd272fc2939a |
| Verdict: | Malicious activity |
| Analysis date: | September 25, 2021, 13:02:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9EA49E291CF4A081DA2AAB7E1D03E45F |
| SHA1: | 2FCDBEDBCD6CDC07634A1BEB07B1D0A70337DFF0 |
| SHA256: | 6838208F6D2597C0D3359A6B10B1D9A1F5C4D15C55EC69B72A477399C35C858E |
| SSDEEP: | 3:N8DSLqLOAcuJAWV6YR5R0:2OLqLvRzd5G |
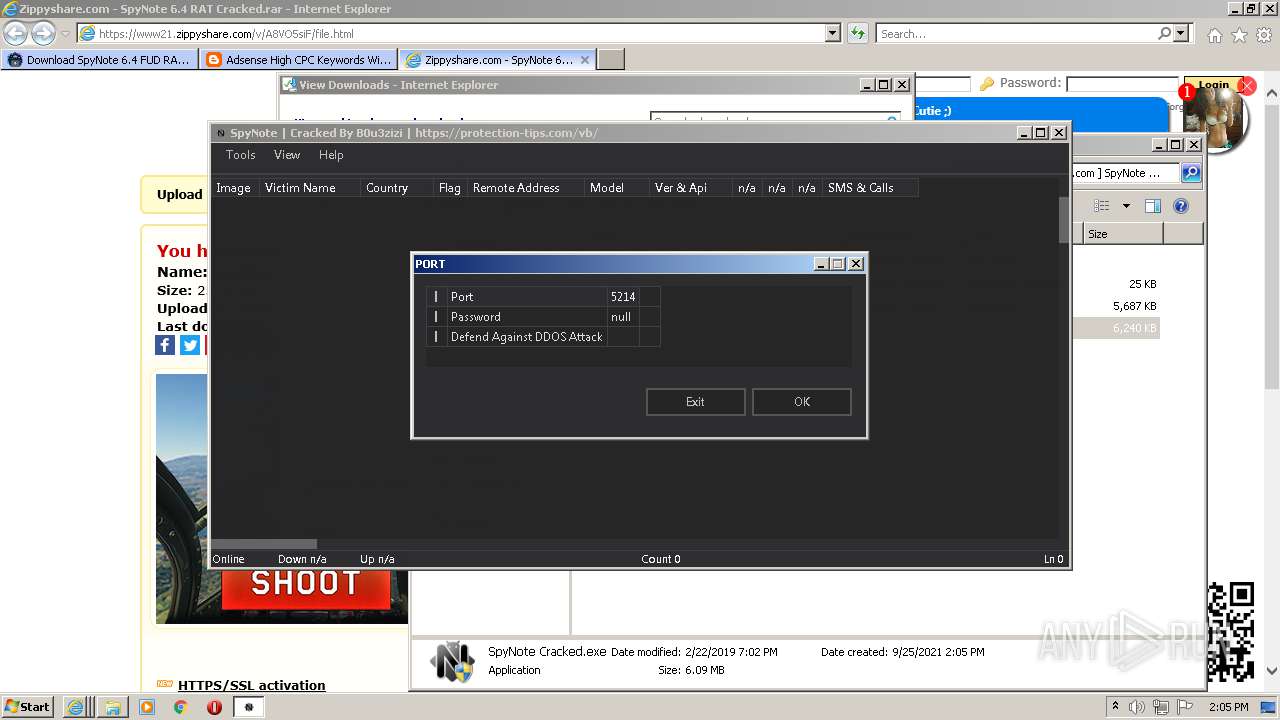
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2644)
Application was dropped or rewritten from another process
- SpyNote 6.4 RAT Cracked.exe (PID: 2108)
- SpyNote 6.4 RAT Cracked.exe (PID: 2220)
- SpyNote Cracked.exe (PID: 2056)
- program startup.exe (PID: 880)
- majid z hacker website.exe (PID: 4088)
- microsoft corporation.exe (PID: 2044)
Drops executable file immediately after starts
- SpyNote 6.4 RAT Cracked.exe (PID: 2108)
- majid z hacker website.exe (PID: 4088)
- program startup.exe (PID: 880)
Disables Windows Defender
- WScript.exe (PID: 3240)
Writes to a start menu file
- program startup.exe (PID: 880)
Changes the autorun value in the registry
- program startup.exe (PID: 880)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2824)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2260)
- WinRAR.exe (PID: 2440)
- SpyNote 6.4 RAT Cracked.exe (PID: 2108)
- majid z hacker website.exe (PID: 4088)
- SpyNote Cracked.exe (PID: 2056)
- program startup.exe (PID: 880)
- microsoft corporation.exe (PID: 2044)
- WScript.exe (PID: 2800)
- WScript.exe (PID: 3240)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 1076)
- powershell.exe (PID: 2872)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 3860)
- powershell.exe (PID: 3384)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 4072)
- WSCript.exe (PID: 3688)
- powershell.exe (PID: 584)
- powershell.exe (PID: 2440)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2260)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2260)
- SpyNote 6.4 RAT Cracked.exe (PID: 2108)
- WinRAR.exe (PID: 2440)
- SpyNote Cracked.exe (PID: 2056)
- majid z hacker website.exe (PID: 4088)
- program startup.exe (PID: 880)
- WScript.exe (PID: 2800)
- WScript.exe (PID: 3240)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 2872)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 1076)
- powershell.exe (PID: 3860)
- WSCript.exe (PID: 3688)
- microsoft corporation.exe (PID: 2044)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 2440)
- powershell.exe (PID: 584)
- powershell.exe (PID: 3384)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2260)
- program startup.exe (PID: 880)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 1076)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 2872)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 3860)
- powershell.exe (PID: 3384)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 2440)
- powershell.exe (PID: 584)
- powershell.exe (PID: 3792)
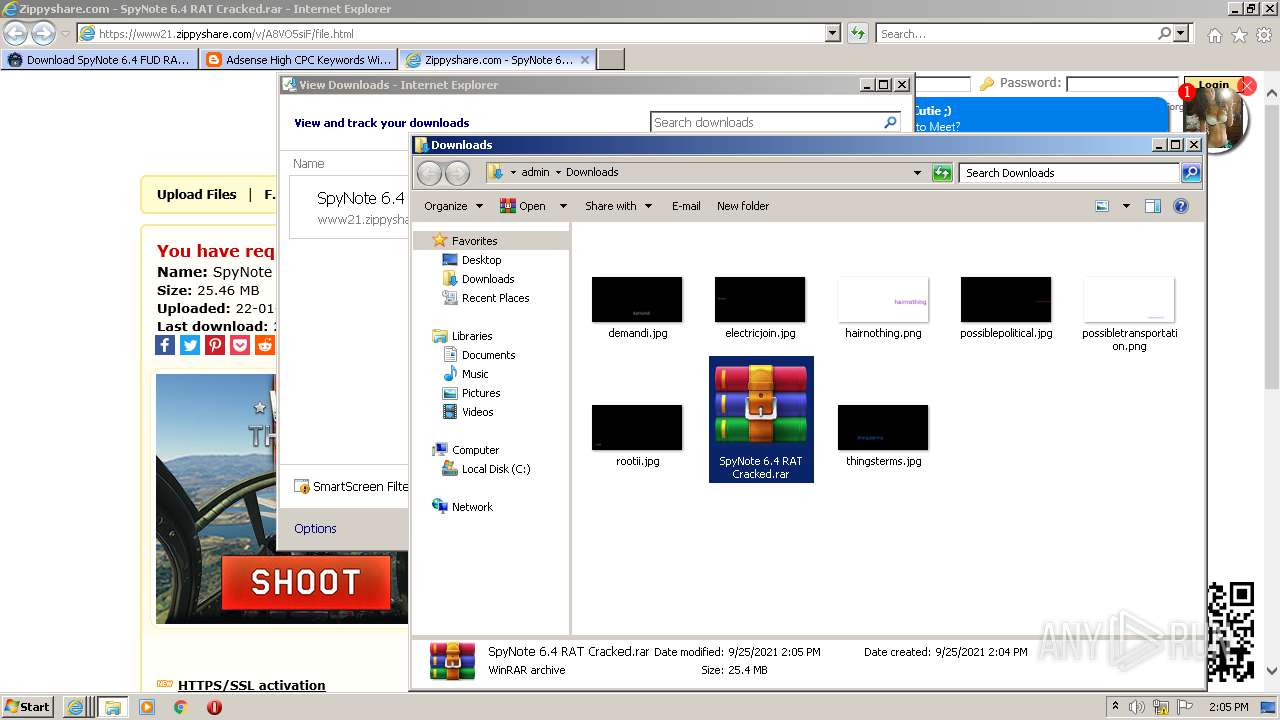
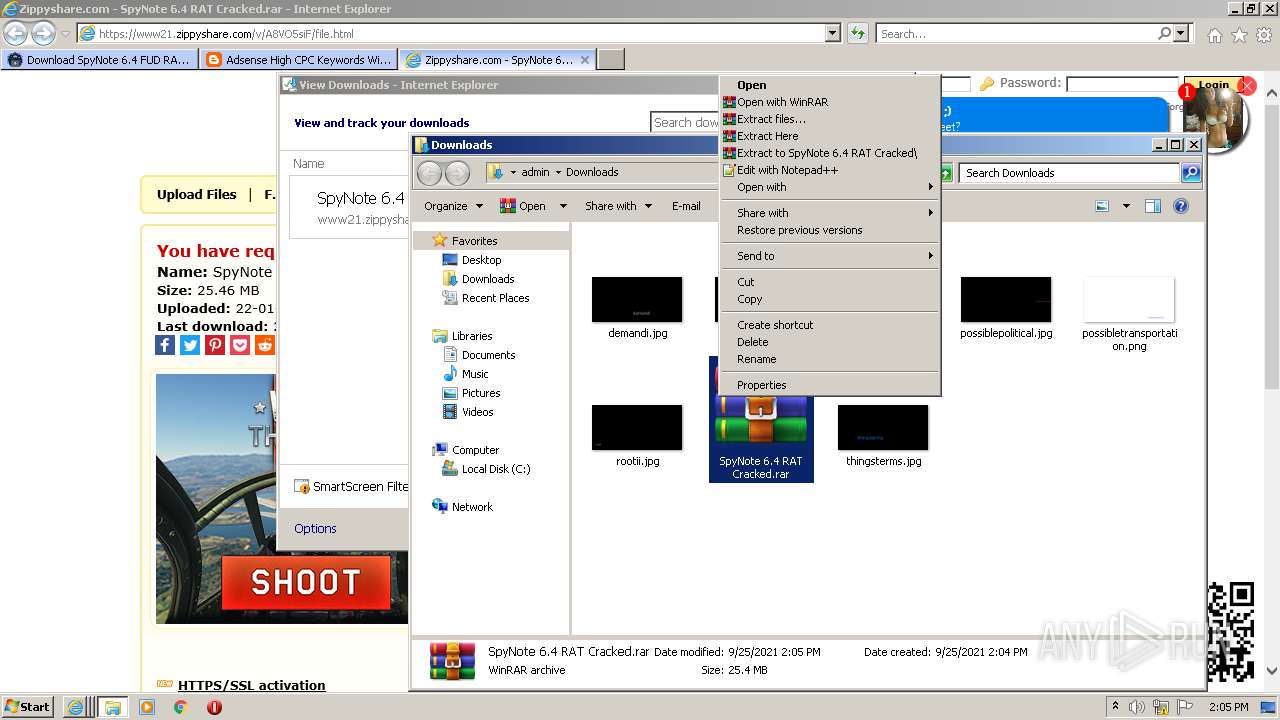
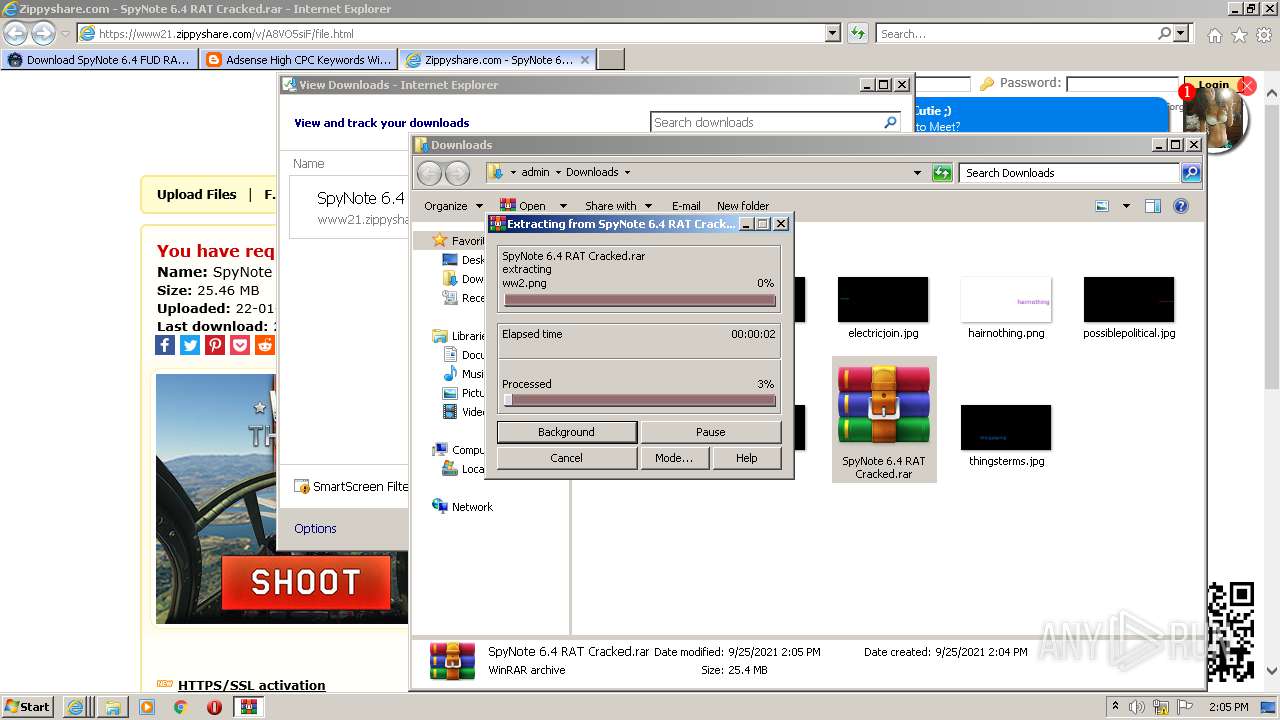
Drops a file with too old compile date
- WinRAR.exe (PID: 2440)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2440)
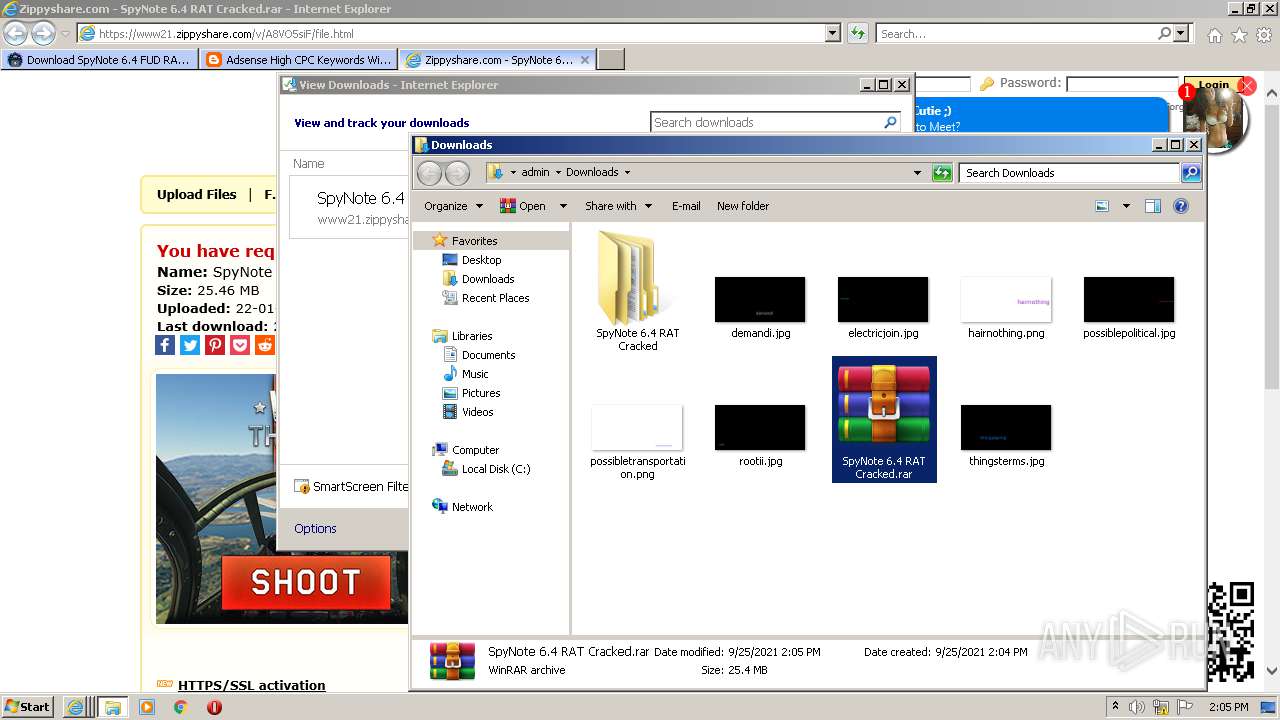
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2440)
- SpyNote 6.4 RAT Cracked.exe (PID: 2108)
- majid z hacker website.exe (PID: 4088)
- program startup.exe (PID: 880)
- microsoft corporation.exe (PID: 2044)
Reads mouse settings
- program startup.exe (PID: 880)
Executes scripts
- majid z hacker website.exe (PID: 4088)
- WScript.exe (PID: 2800)
- program startup.exe (PID: 880)
Application launched itself
- WScript.exe (PID: 2800)
Executes PowerShell scripts
- WScript.exe (PID: 3240)
Reads the date of Windows installation
- powershell.exe (PID: 1076)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 2872)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 3860)
- powershell.exe (PID: 3384)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 2440)
- powershell.exe (PID: 584)
Reads Environment values
- microsoft corporation.exe (PID: 2044)
Starts itself from another location
- microsoft corporation.exe (PID: 2044)
INFO
Checks supported languages
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2824)
- SearchProtocolHost.exe (PID: 2644)
Application launched itself
- iexplore.exe (PID: 2572)
Reads the computer name
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2824)
- SearchProtocolHost.exe (PID: 2644)
Changes internet zones settings
- iexplore.exe (PID: 2572)
Reads internet explorer settings
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2824)
Creates files in the user directory
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2824)
Checks Windows Trust Settings
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 2824)
- WScript.exe (PID: 2800)
- WScript.exe (PID: 3240)
- program startup.exe (PID: 880)
- WSCript.exe (PID: 3688)
Reads settings of System Certificates
- iexplore.exe (PID: 2116)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 2824)
- program startup.exe (PID: 880)
Changes settings of System certificates
- iexplore.exe (PID: 2572)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2572)
Reads CPU info
- iexplore.exe (PID: 1852)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2572)
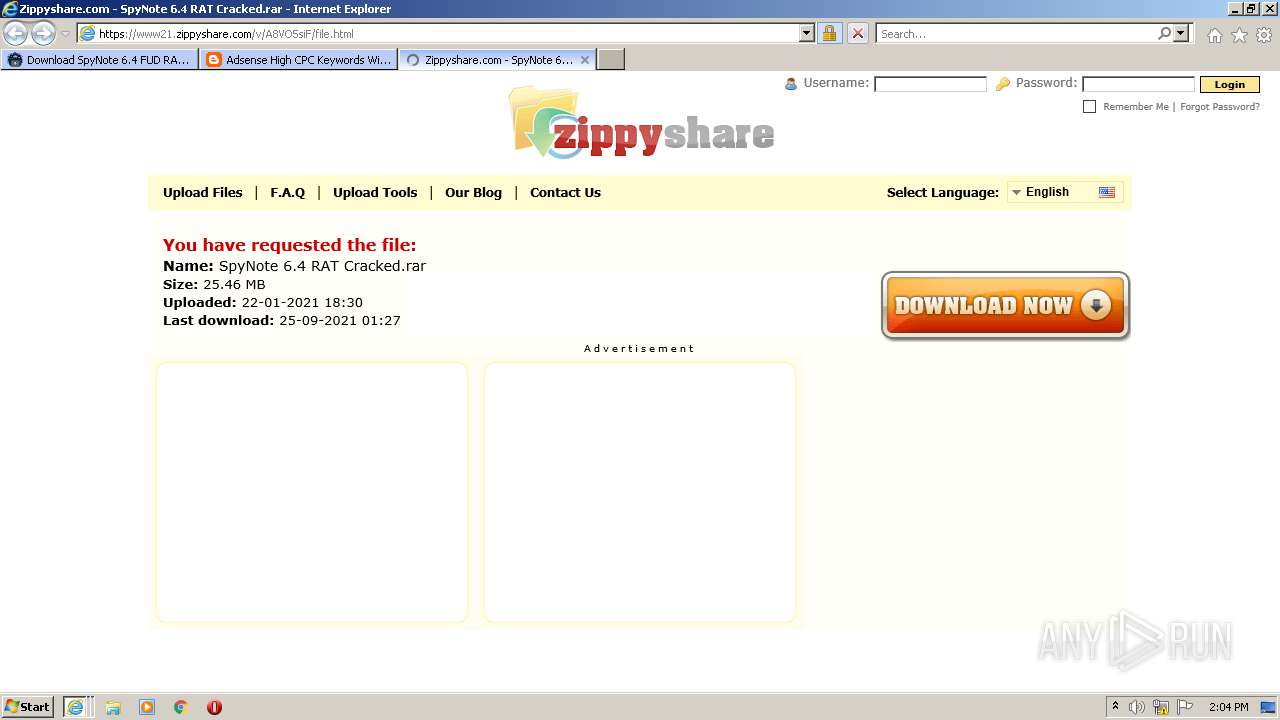
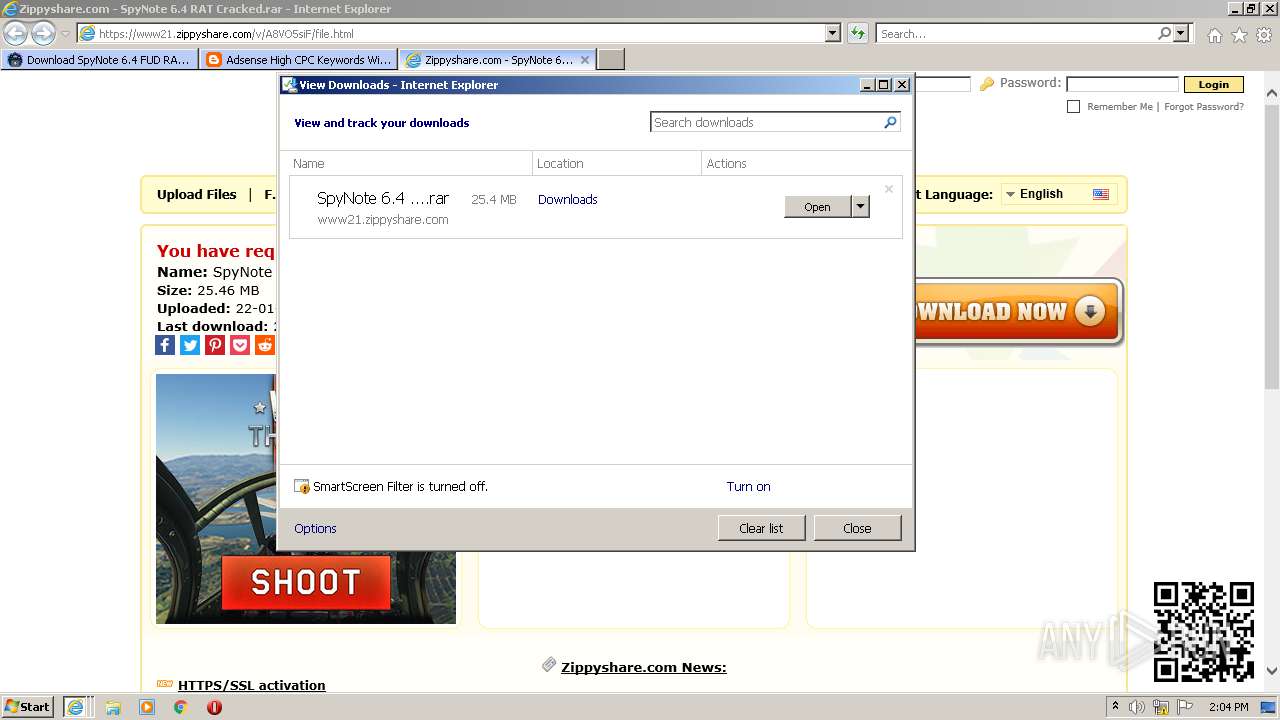
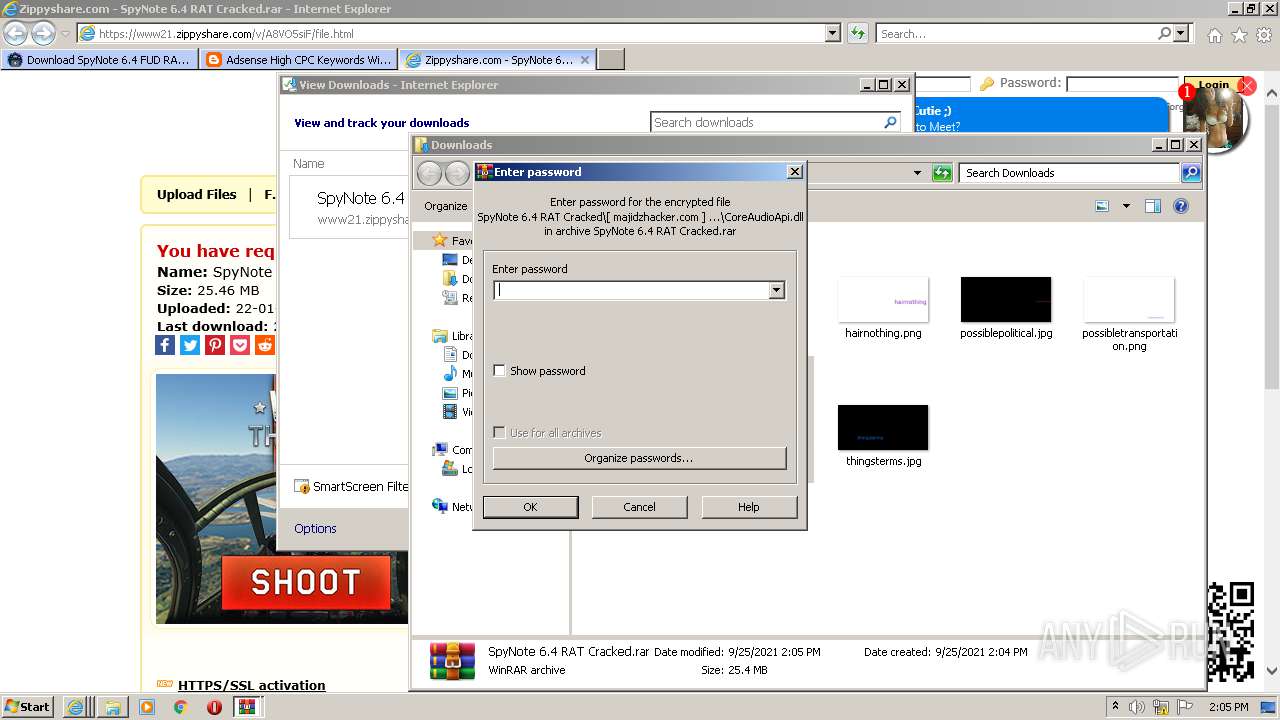
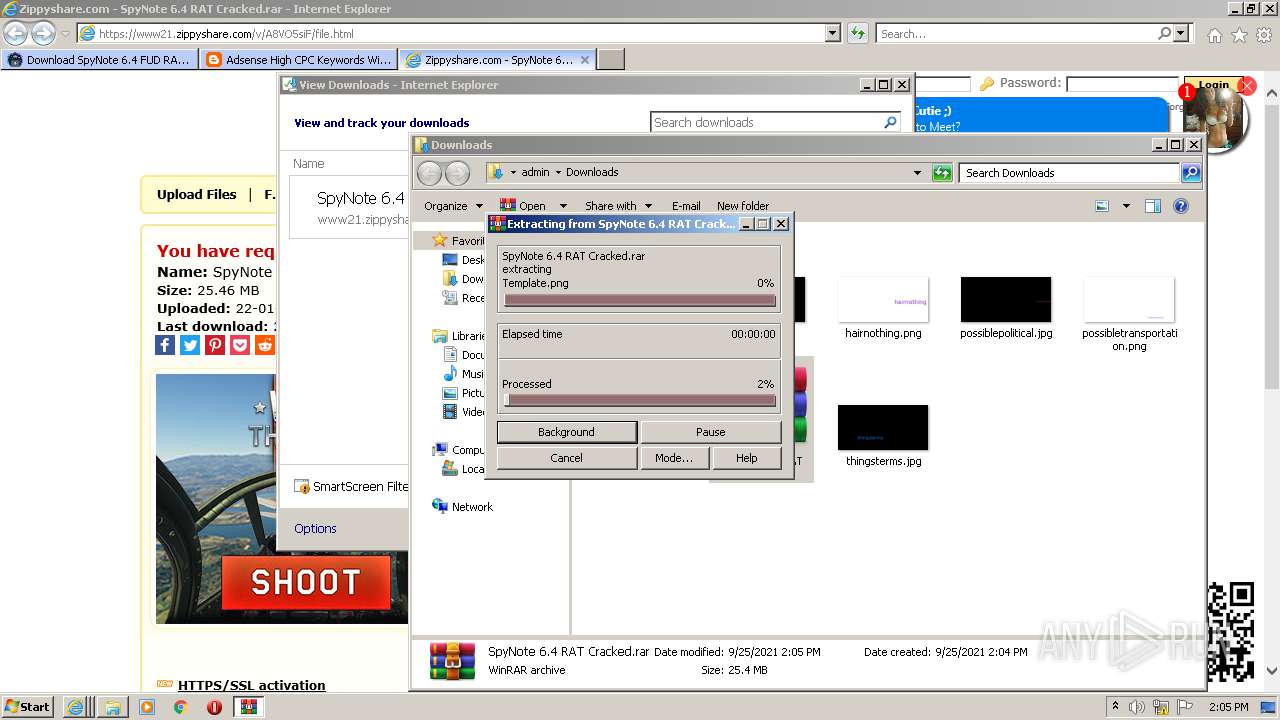
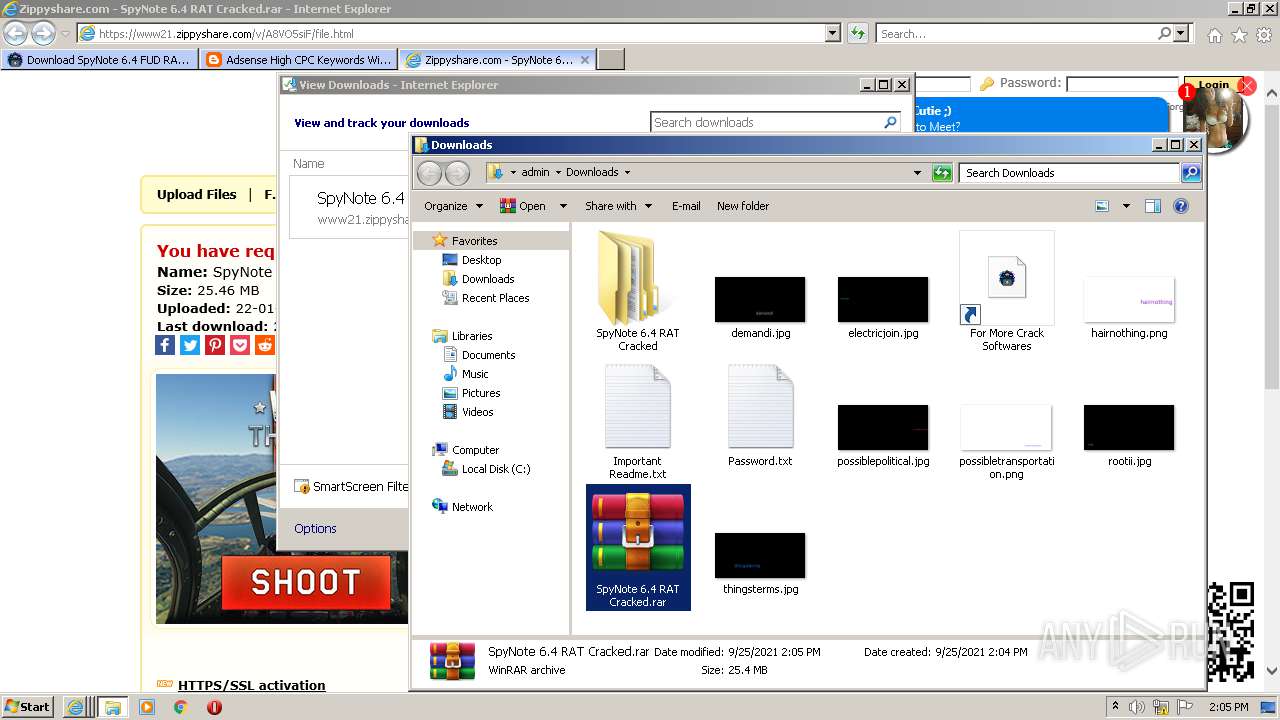
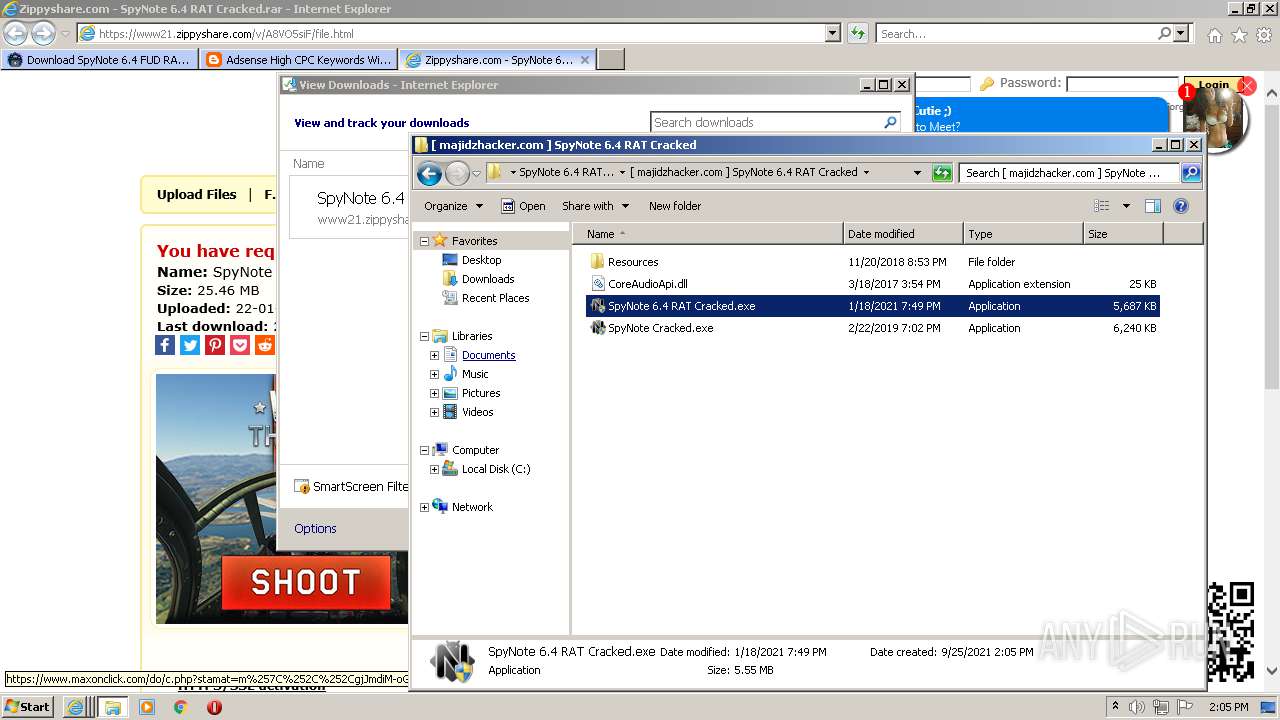
Manual execution by user
- SpyNote 6.4 RAT Cracked.exe (PID: 2108)
- SpyNote 6.4 RAT Cracked.exe (PID: 2220)
- WinRAR.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
29
Malicious processes
16
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Set-MpPreference -SevereThreatDefaultAction 6 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.2.9200.16398 (win8_gdr_oobssr.120820-1900) Modules
| |||||||||||||||
| 880 | "C:\Users\admin\AppData\Local\Temp\program startup.exe" | C:\Users\admin\AppData\Local\Temp\program startup.exe | majid z hacker website.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2572 CREDAT:726310 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1076 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Set-MpPreference -DisableScriptScanning $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.2.9200.16398 (win8_gdr_oobssr.120820-1900) Modules
| |||||||||||||||
| 1448 | "C:\ProgramData\microsoft corporation.exe" | C:\ProgramData\microsoft corporation.exe | — | microsoft corporation.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2572 CREDAT:1643797 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\AppData\Local\Temp\microsoft corporation.exe" | C:\Users\admin\AppData\Local\Temp\microsoft corporation.exe | majid z hacker website.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
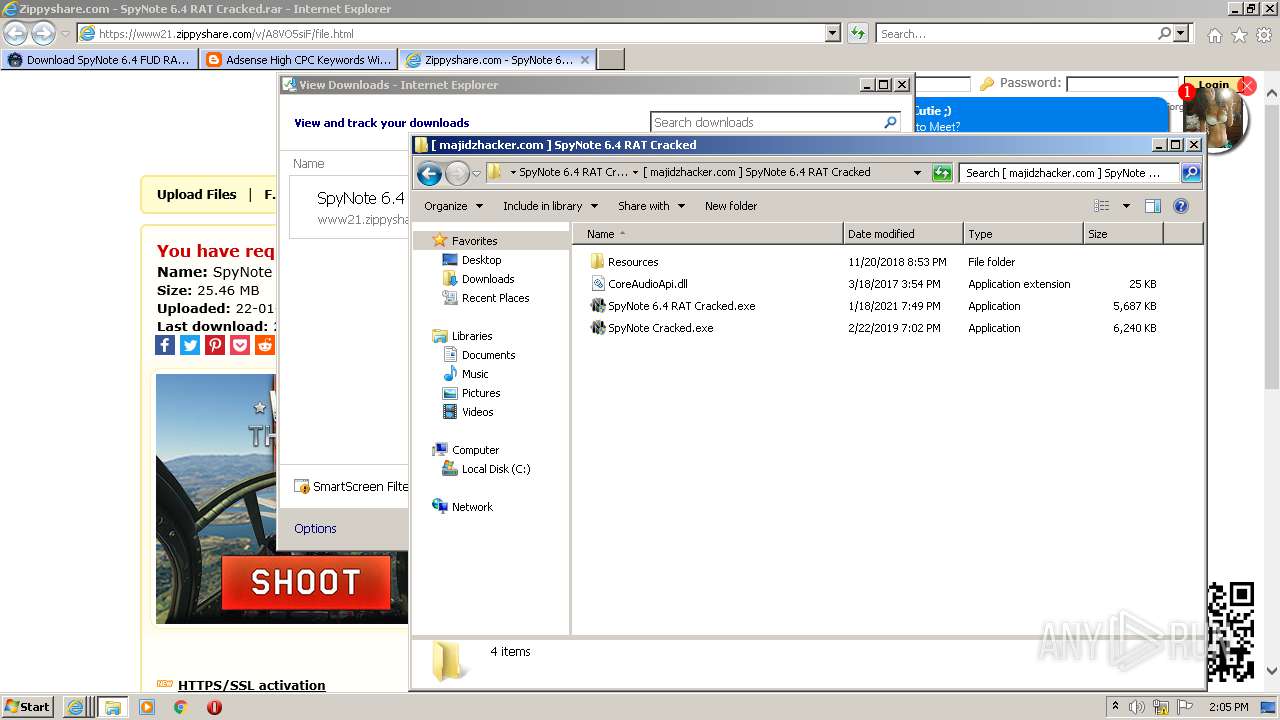
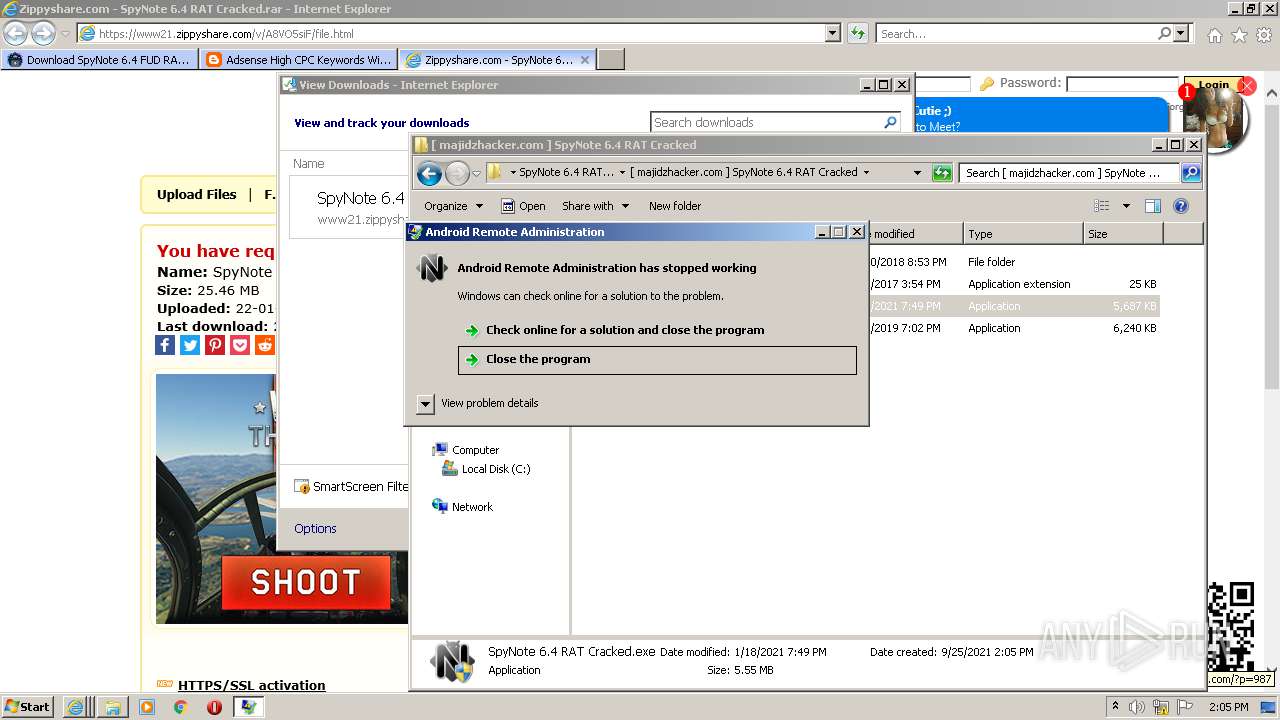
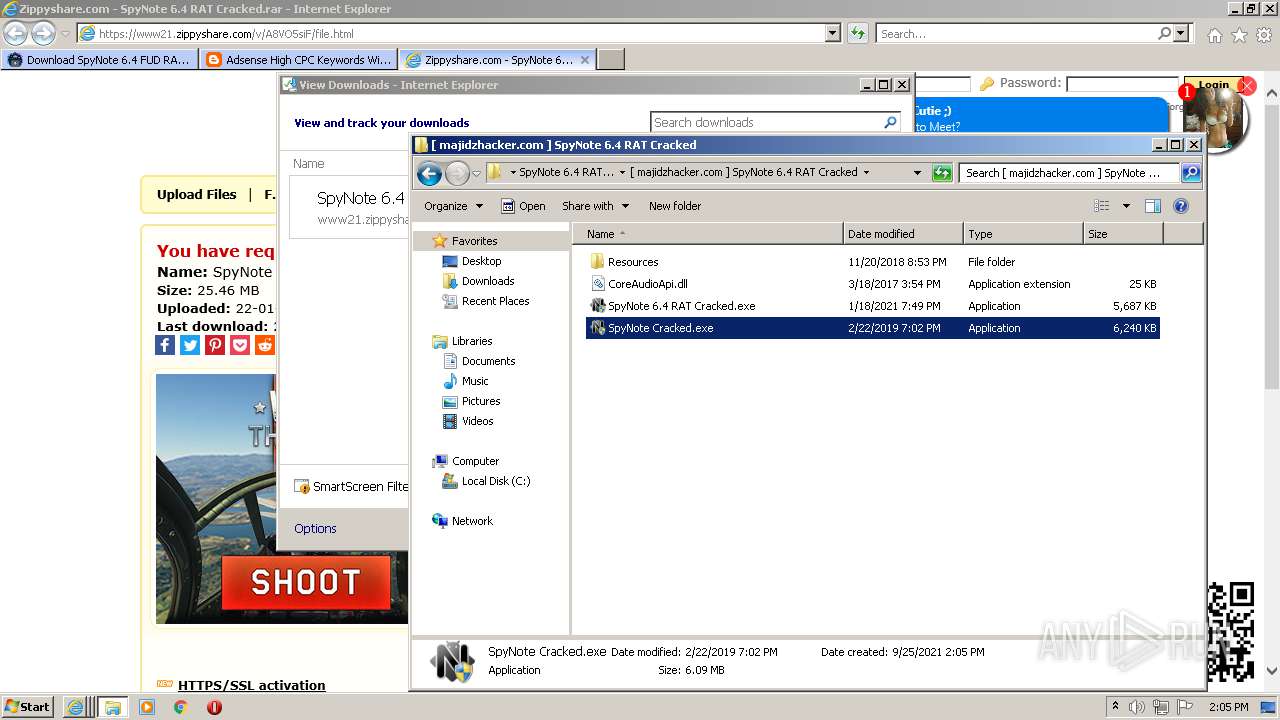
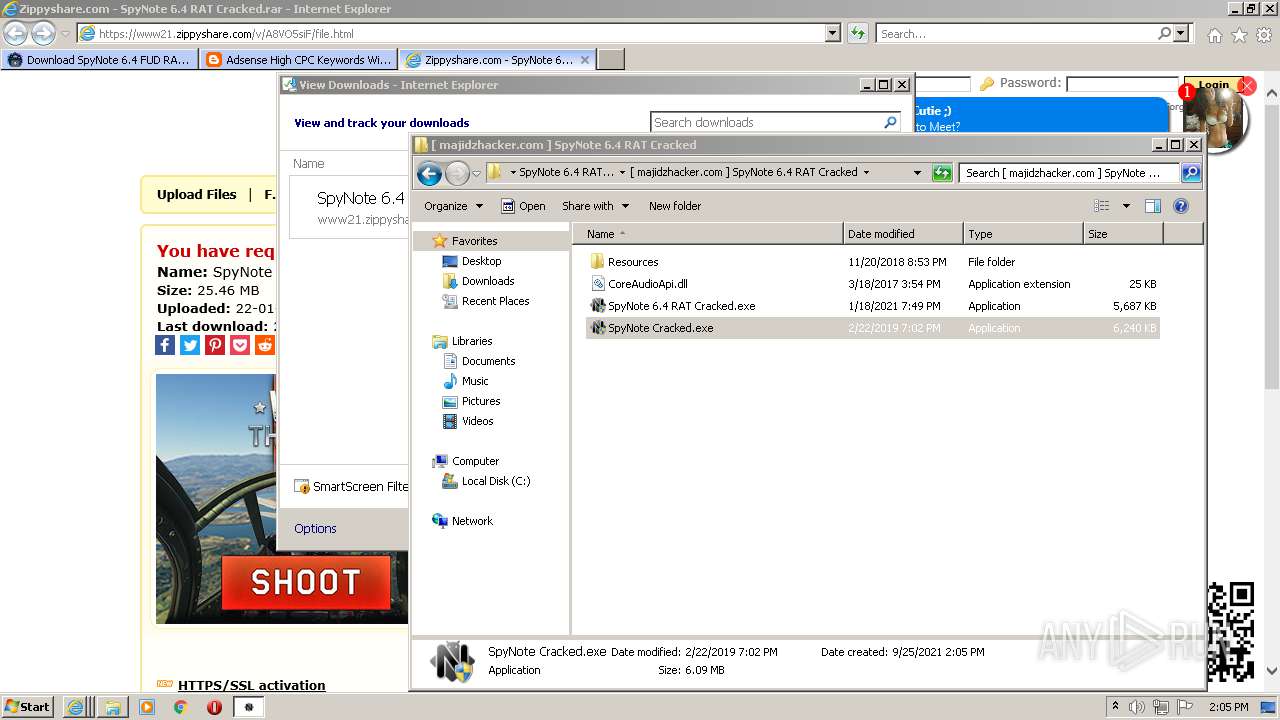
| 2056 | "C:\Users\admin\AppData\Local\Temp\SpyNote Cracked.exe" | C:\Users\admin\AppData\Local\Temp\SpyNote Cracked.exe | SpyNote 6.4 RAT Cracked.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Android Remote Administration Exit code: 3762504530 Version: 6.4.0.0 Modules
| |||||||||||||||
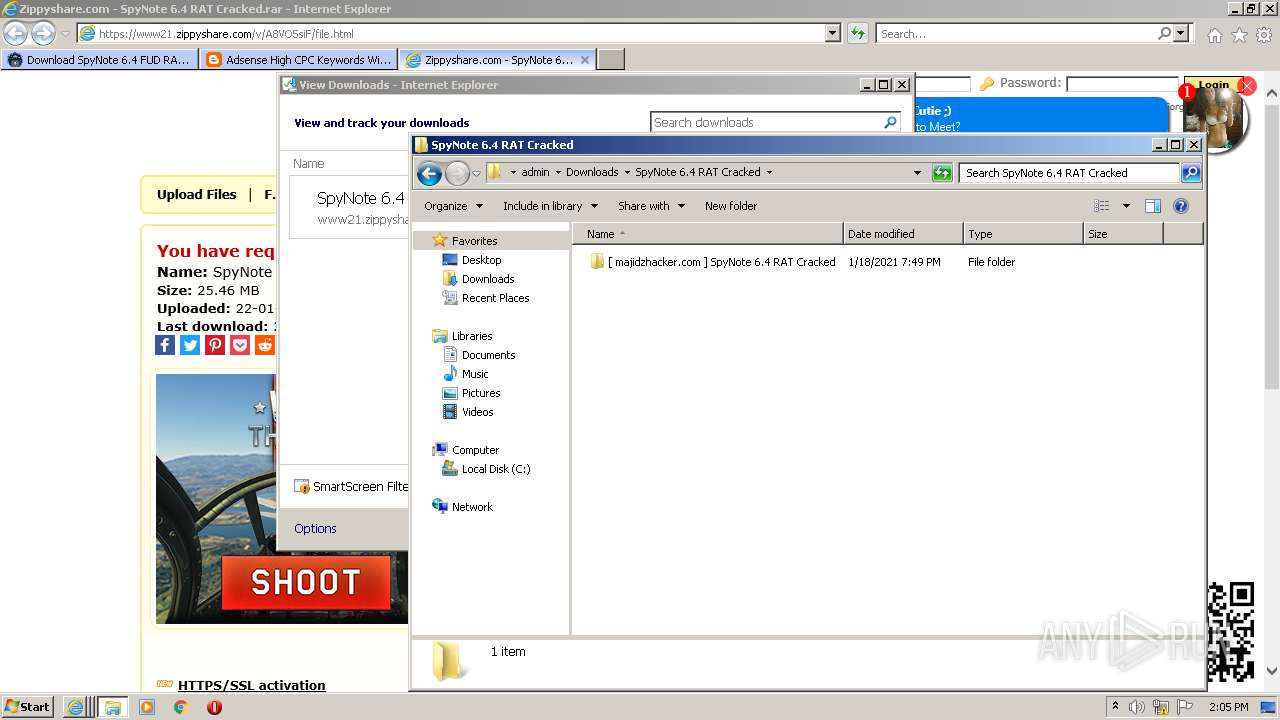
| 2108 | "C:\Users\admin\Downloads\SpyNote 6.4 RAT Cracked\[ majidzhacker.com ] SpyNote 6.4 RAT Cracked\SpyNote 6.4 RAT Cracked.exe" | C:\Users\admin\Downloads\SpyNote 6.4 RAT Cracked\[ majidzhacker.com ] SpyNote 6.4 RAT Cracked\SpyNote 6.4 RAT Cracked.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2572 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
71 041
Read events
69 385
Write events
1 649
Delete events
7
Modification events
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30913037 | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30913037 | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
14
Suspicious files
102
Text files
924
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:A5E233F27E486C2DC777CC1B1CF88F63 | SHA256:BA063A8576DD32CF5C06B54531D0E802B624FED86D692296C4454118710115BE | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:CA9146E96C6A1A75508063CB1E095461 | SHA256:0CD672274ECADFD3E43BBB8F97C121A1FD61593B0B98EE128462C90FF74E6C20 | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:DE27664DA1E04C94901FCC3880064613 | SHA256:7E59CE8A2D7D1E1201E535A3175BFAF239B9F5DA7BE265C18C5FF1E1BC696282 | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_3B9C2111EAE052C5BA0EC1CBB6D70DEA | der | |
MD5:AB25FC5FCE795DA1C76A5540377CE4A6 | SHA256:EF63F87B5EC8909D7992DA505BD34BE5DDA3BCC33B759E483FE334385940C9D7 | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download-spynote-6.4[1].htm | html | |
MD5:09320FDCA3FD6D03A4D186B9EC83D853 | SHA256:8E7AD66218E172C4A8C0F3A8A561BABD07104133067F0D493E528F193C237E3F | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:FF760B3A397D00A16AC964E9291066A8 | SHA256:2BE998D6EFC4664E44AE28AE247F1B28857E656B9294B1CB72F774BB4C9F4403 | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_BF5C002C0B47AC940D40DFFC532E4C71 | der | |
MD5:CB4F8B277F8A018BB294DA0FD2C3894E | SHA256:D03121181388B91F023AE4F692CDBF856DD7411C928CA6E0B1649711BD65CEAC | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\OneSignalSDK[1].js | text | |
MD5:CF0CBE7AADAADD0A12673A93AC7780E1 | SHA256:8E72AFCD1A38E3AB0BB322104A9238E75DDA48DF9C455E5471BBAAECE5207D83 | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_BF5C002C0B47AC940D40DFFC532E4C71 | binary | |
MD5:036AA78C39C2DD72B5ADDC46FEA210CC | SHA256:9B2C4D91E0EBAA4D8CCC731598DEBE071D871305A1ED070E44AE5F625FB3030C | |||
| 2116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\265C0DEB29181DD1891051371C5F863A_24AFAD6921EE0B67168612B7EFCCE1BD | binary | |
MD5:751B8BD0C2A44F67E3E1E7C3EE7686A9 | SHA256:BD4C9BD2E0C63C51BF82CF10D3F3382053C6742E9A5EF2A8CBEB1D783B586F0F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
479
DNS requests
126
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2116 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC2liiOyoDFcQoAAAAA%2FPOV | US | der | 472 b | whitelisted |
2116 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d76c80bebff411e2 | US | compressed | 4.70 Kb | whitelisted |
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEErZqGrRCV0dCgAAAAD87q4%3D | US | der | 471 b | whitelisted |
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2FlD3sEhDdGAoAAAAA%2FPSV | US | der | 472 b | whitelisted |
2116 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?54ebb8b525faaa2d | US | compressed | 4.70 Kb | whitelisted |
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDZ%2Fa9m7efDAwoAAAAA%2FO%2Fg | US | der | 472 b | whitelisted |
2116 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEF6zheUj6D92CgAAAAD87%2BI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2116 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2116 | iexplore.exe | 172.67.185.185:443 | www.majidzhacker.com | — | US | unknown |
2116 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2116 | iexplore.exe | 142.250.186.137:443 | www.blogger.com | Google Inc. | US | suspicious |
2116 | iexplore.exe | 104.18.226.52:443 | cdn.onesignal.com | Cloudflare Inc | US | malicious |
2116 | iexplore.exe | 142.250.185.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2116 | iexplore.exe | 142.250.186.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2116 | iexplore.exe | 104.18.11.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
2116 | iexplore.exe | 142.250.185.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2116 | iexplore.exe | 142.250.186.161:443 | 2.bp.blogspot.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.majidzhacker.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.blogger.com |
| shared |
cdn.onesignal.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
2.bp.blogspot.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |