| File name: | nssm.exe |
| Full analysis: | https://app.any.run/tasks/a10315ff-2d13-47a1-bbed-50352ccbd45e |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2021, 22:26:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BD3B9DAC9198C57238D236435BF391CA |
| SHA1: | E0B966CFBE9E804319CFD3B756B12AD8A2294B24 |
| SHA256: | 682F1025B4C410AE78B1C5BDC4DE7AD315F2EFF292C66947C13969930028C98D |
| SSDEEP: | 6144:H1NJihCejVOjAG7awRtleN6A7kWxzGAnw+iPSWSHCGXkJqKLWr4ZrDosNX0:V8OywRszGAQGXkJqKSbsNX0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- nssm.exe (PID: 3544)
- nssm.exe (PID: 3356)
- cmd.exe (PID: 1608)
- nssm.exe (PID: 2664)
- nssm.exe (PID: 2232)
- nssm.exe (PID: 3776)
- nssm.exe (PID: 3836)
Reads the computer name
- nssm.exe (PID: 3356)
- nssm.exe (PID: 2664)
- cmd.exe (PID: 1608)
- nssm.exe (PID: 2232)
- nssm.exe (PID: 3776)
- nssm.exe (PID: 3836)
Application launched itself
- nssm.exe (PID: 3356)
- nssm.exe (PID: 3836)
Reads internet explorer settings
- mmc.exe (PID: 3356)
Reads Microsoft Outlook installation path
- mmc.exe (PID: 3356)
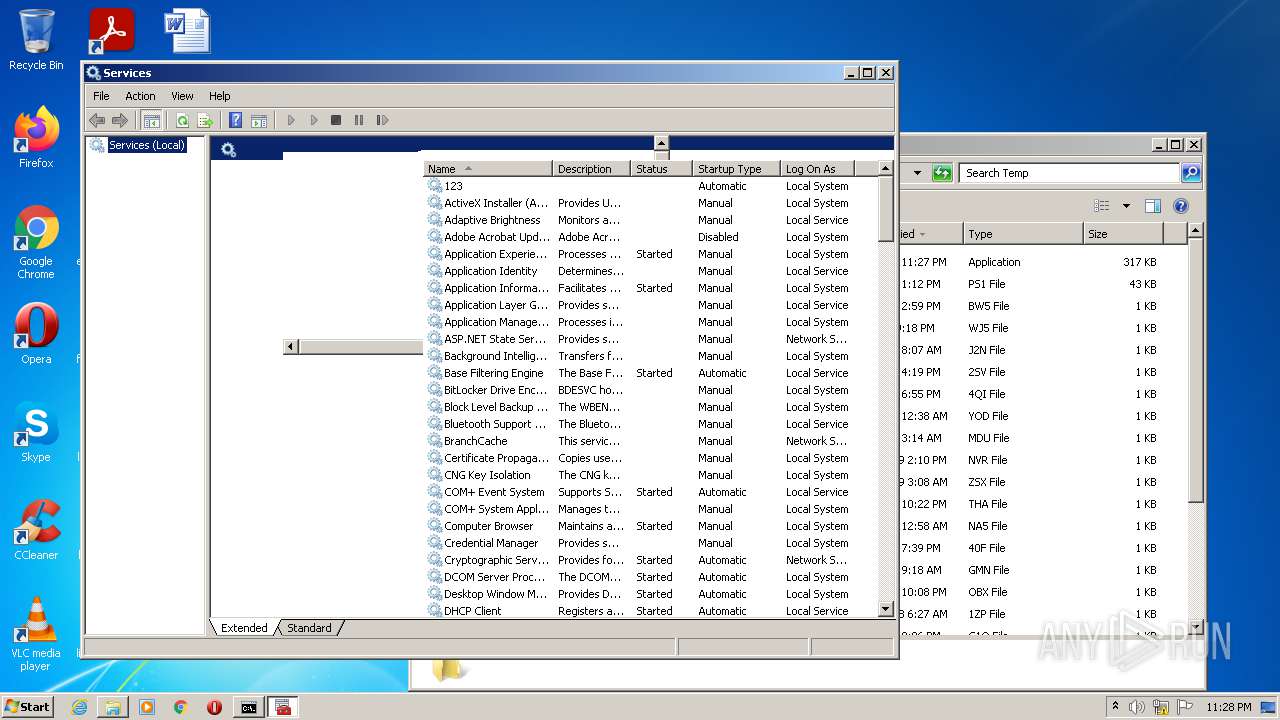
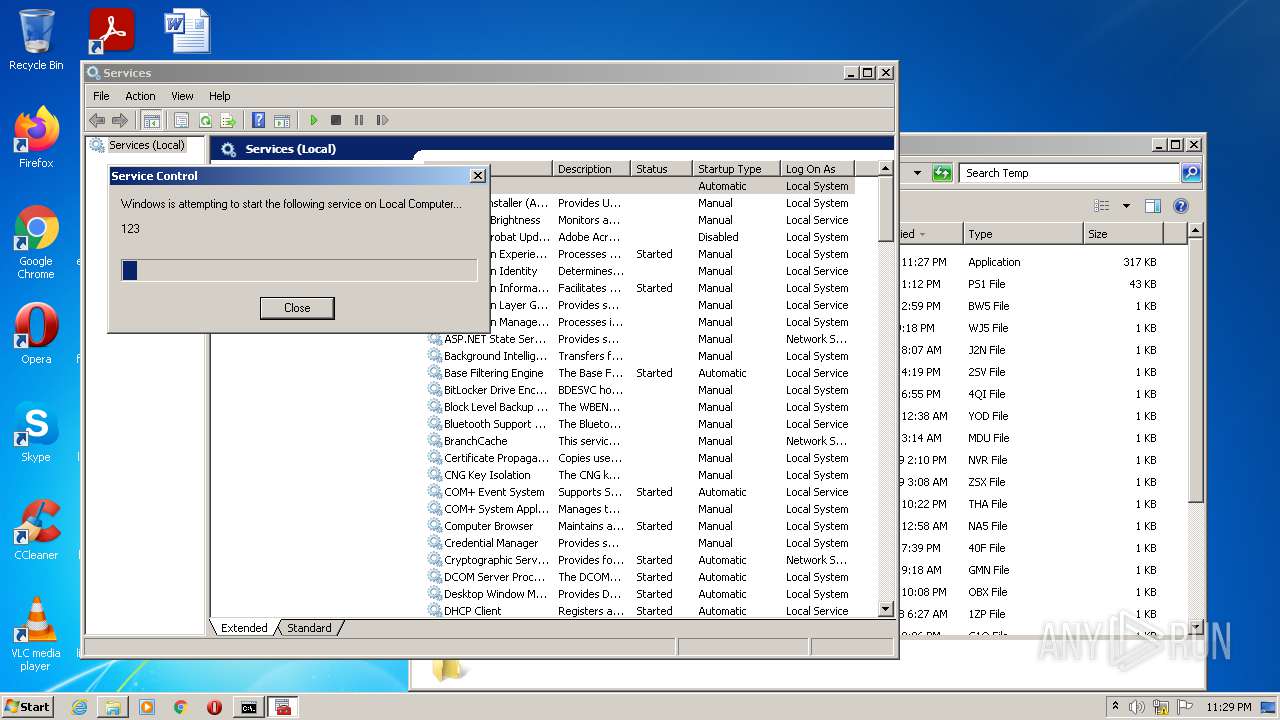
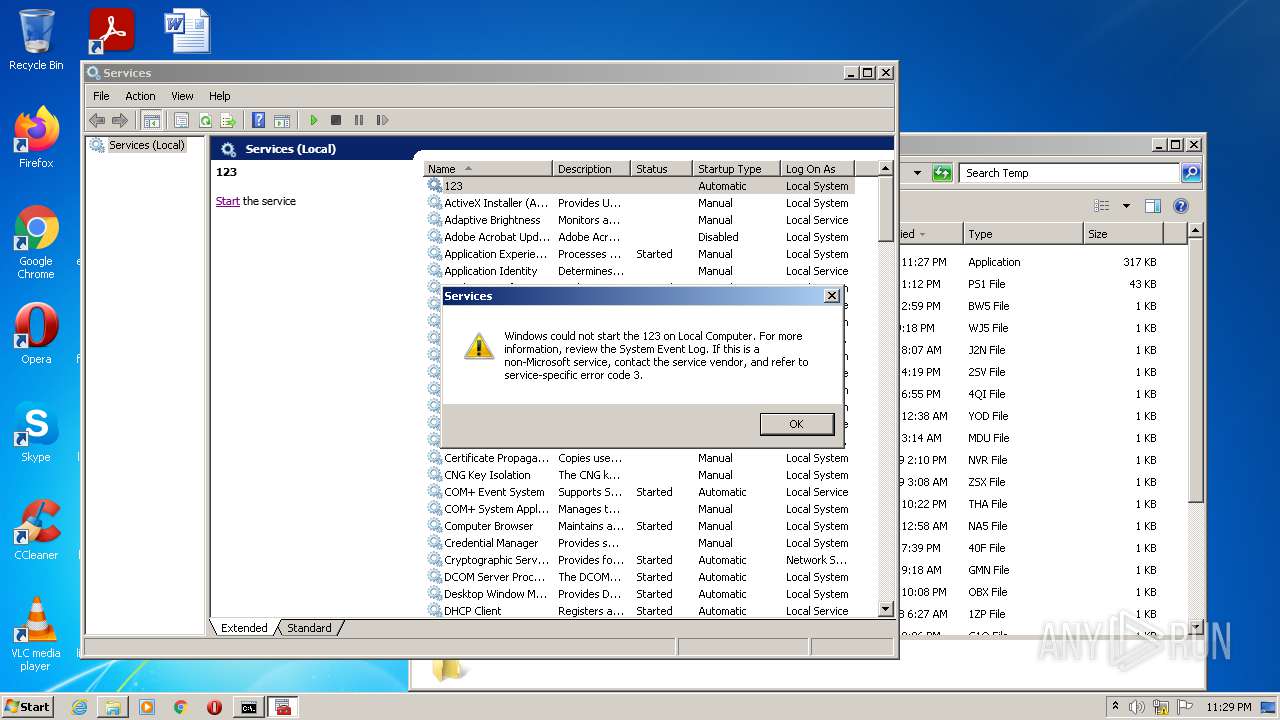
Executed as Windows Service
- nssm.exe (PID: 3776)
INFO
Checks supported languages
- explorer.exe (PID: 280)
- mmc.exe (PID: 3356)
Reads the computer name
- explorer.exe (PID: 280)
- mmc.exe (PID: 3356)
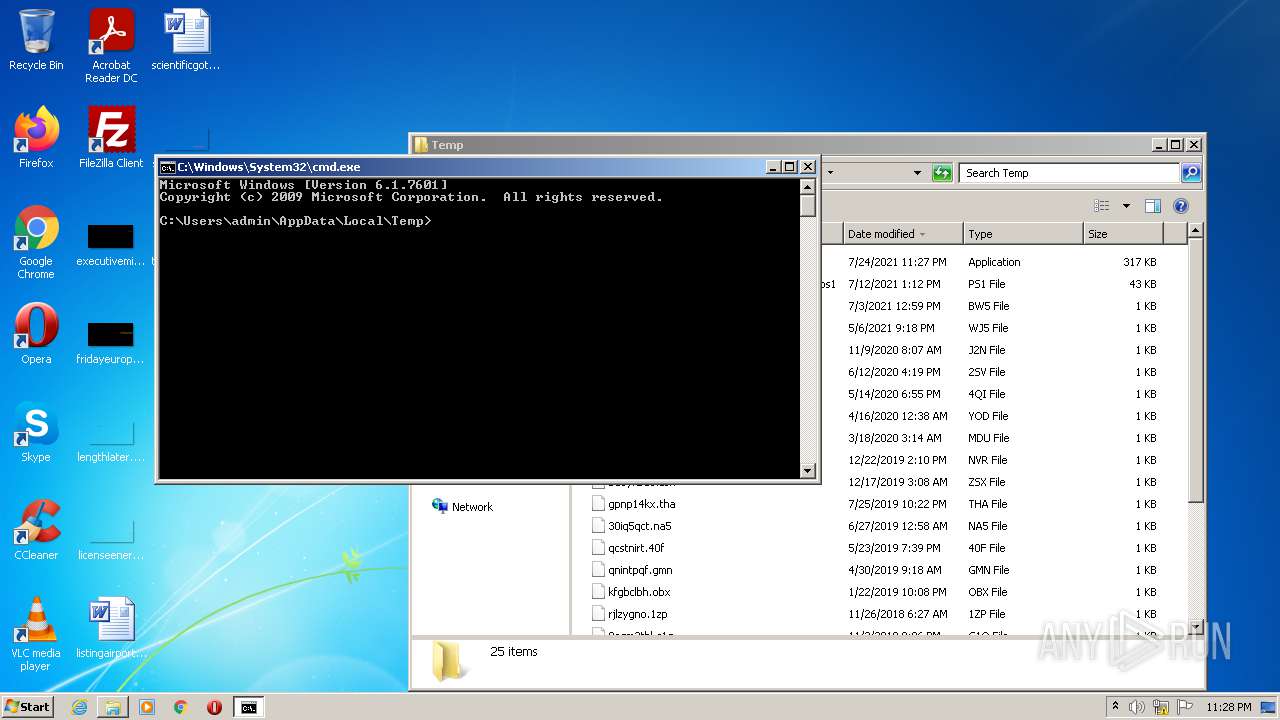
Manual execution by user
- cmd.exe (PID: 1608)
- explorer.exe (PID: 280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
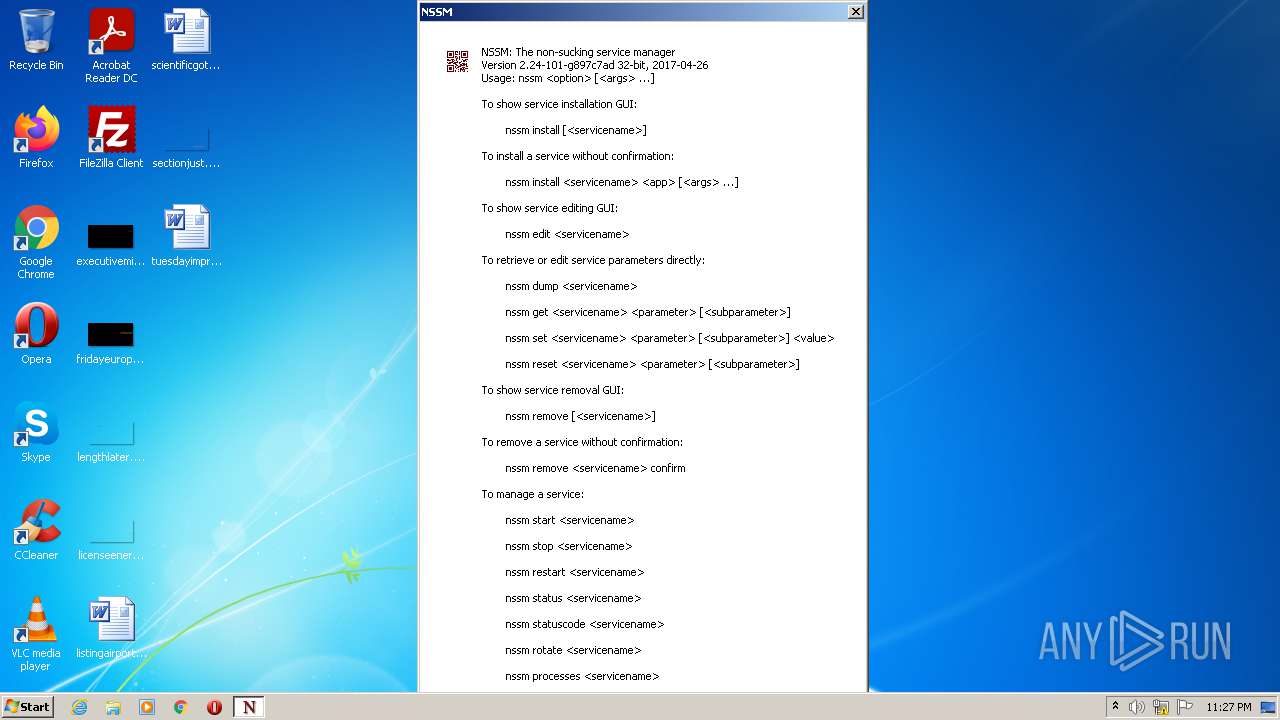
| ProductVersion: | 2.24-101-g897c7ad |
|---|---|
| ProductName: | NSSM 32-bit |
| OriginalFileName: | nssm.exe |
| LegalCopyright: | Public Domain; Author Iain Patterson 2003-2017 |
| FileVersion: | 2.24-101-g897c7ad |
| FileDescription: | The non-sucking service manager |
| CompanyName: | Iain Patterson |
| Comments: | http://nssm.cc/ |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | Pre-release |
| FileFlagsMask: | 0x0003 |
| ProductVersionNumber: | 2.24.101.101 |
| FileVersionNumber: | 2.24.101.101 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x15df6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 194048 |
| CodeSize: | 129536 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2017:04:26 16:15:15+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 26-Apr-2017 14:15:15 |
| Detected languages: |
|
| Comments: | http://nssm.cc/ |
| CompanyName: | Iain Patterson |
| FileDescription: | The non-sucking service manager |
| FileVersion: | 2.24-101-g897c7ad |
| LegalCopyright: | Public Domain; Author Iain Patterson 2003-2017 |
| OriginalFileName: | nssm.exe |
| ProductName: | NSSM 32-bit |
| ProductVersion: | 2.24-101-g897c7ad |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Apr-2017 14:15:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F9F8 | 0x0001FA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49432 |
.rdata | 0x00021000 | 0x00006074 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81988 |
.data | 0x00028000 | 0x00033384 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.60954 |
.rsrc | 0x0005C000 | 0x00027C84 | 0x00027E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.29009 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.42533 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.04044 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.91209 | 16938 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.44608 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
102 | 3.3417 | 352 | Latin 1 / Western European | Italian - Italy | RT_DIALOG |
103 | 3.20755 | 246 | Latin 1 / Western European | Italian - Italy | RT_DIALOG |
104 | 3.33488 | 344 | Latin 1 / Western European | Italian - Italy | RT_DIALOG |
105 | 3.37278 | 402 | Latin 1 / Western European | Italian - Italy | RT_DIALOG |
106 | 3.32635 | 354 | Latin 1 / Western European | Italian - Italy | RT_DIALOG |
Imports
ADVAPI32.dll |
COMDLG32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
58
Monitored processes
10
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
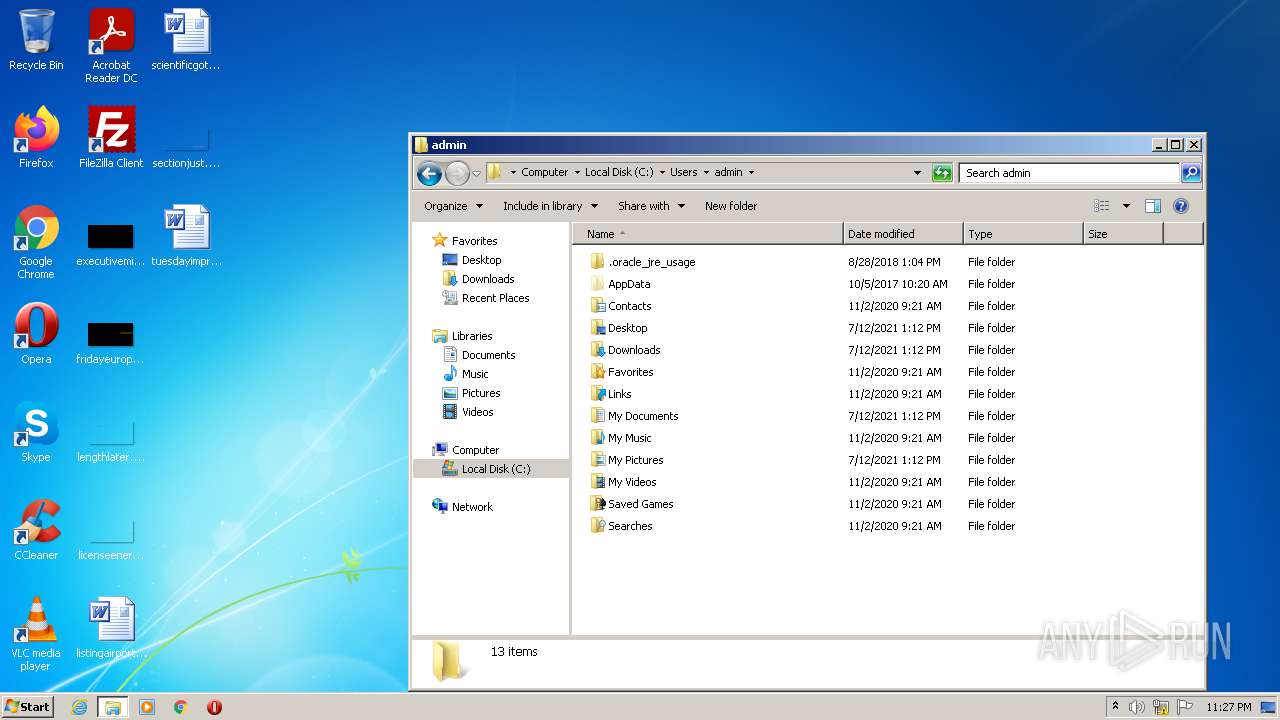
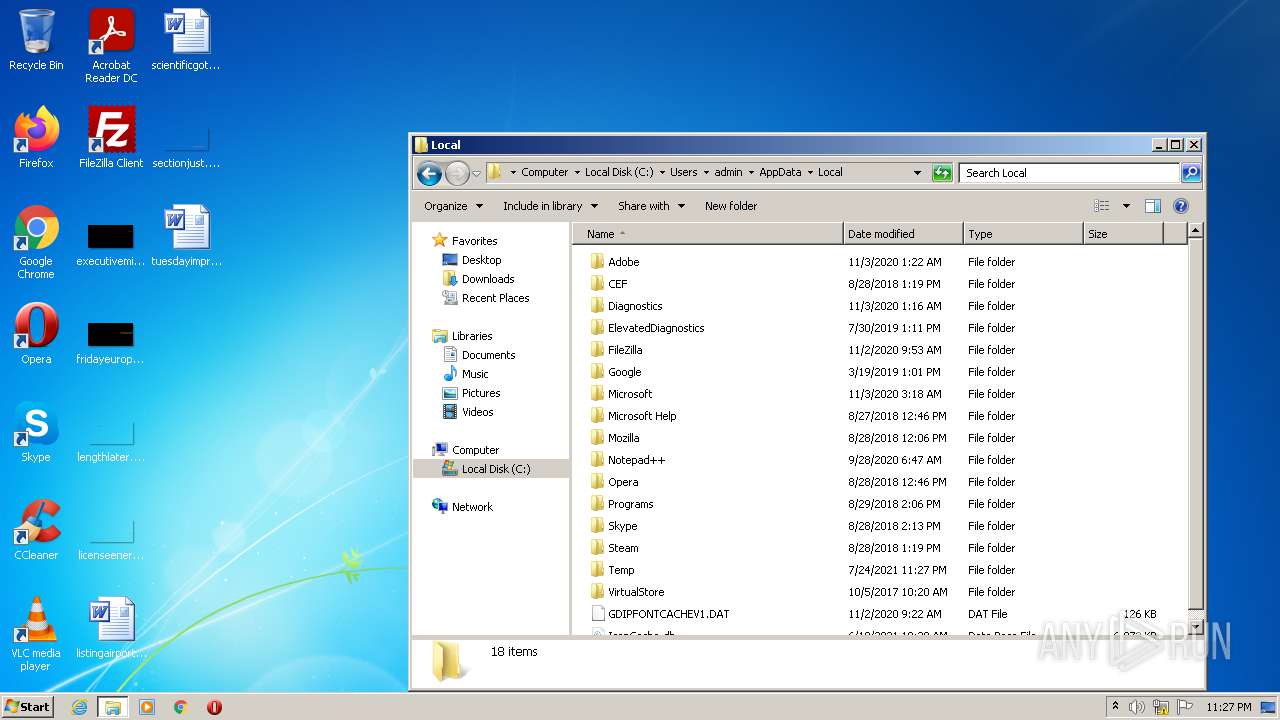
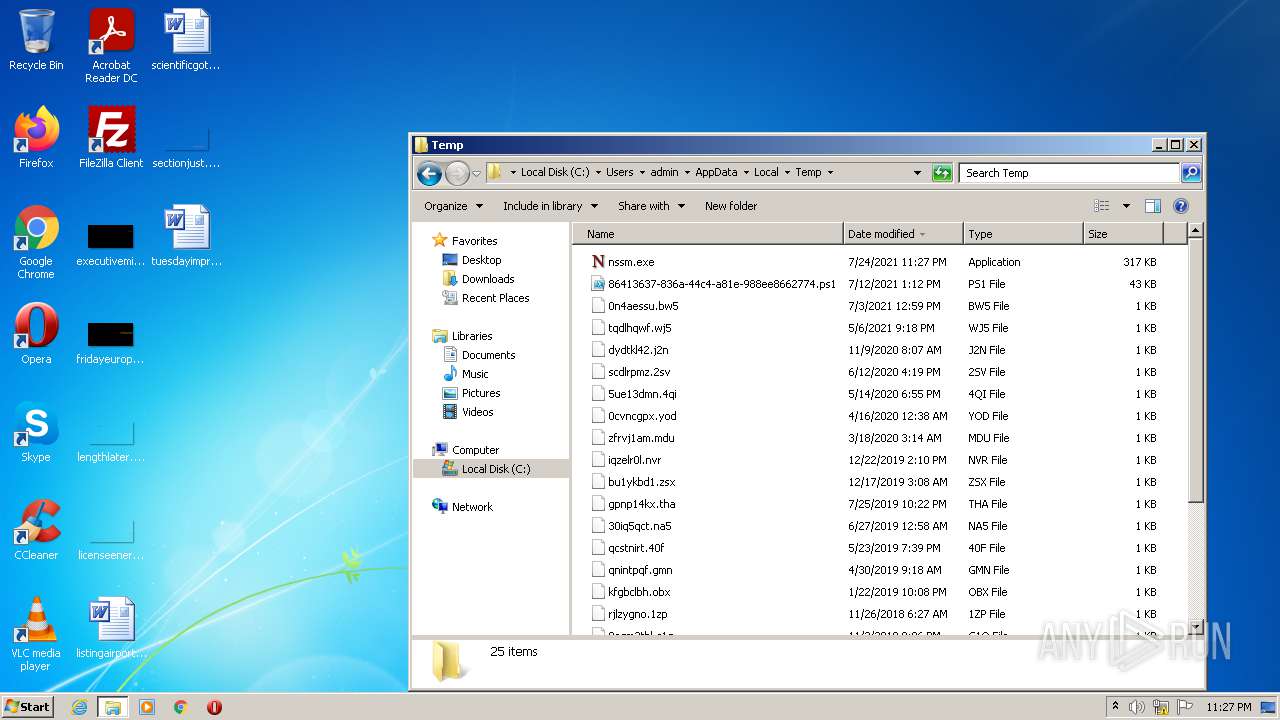
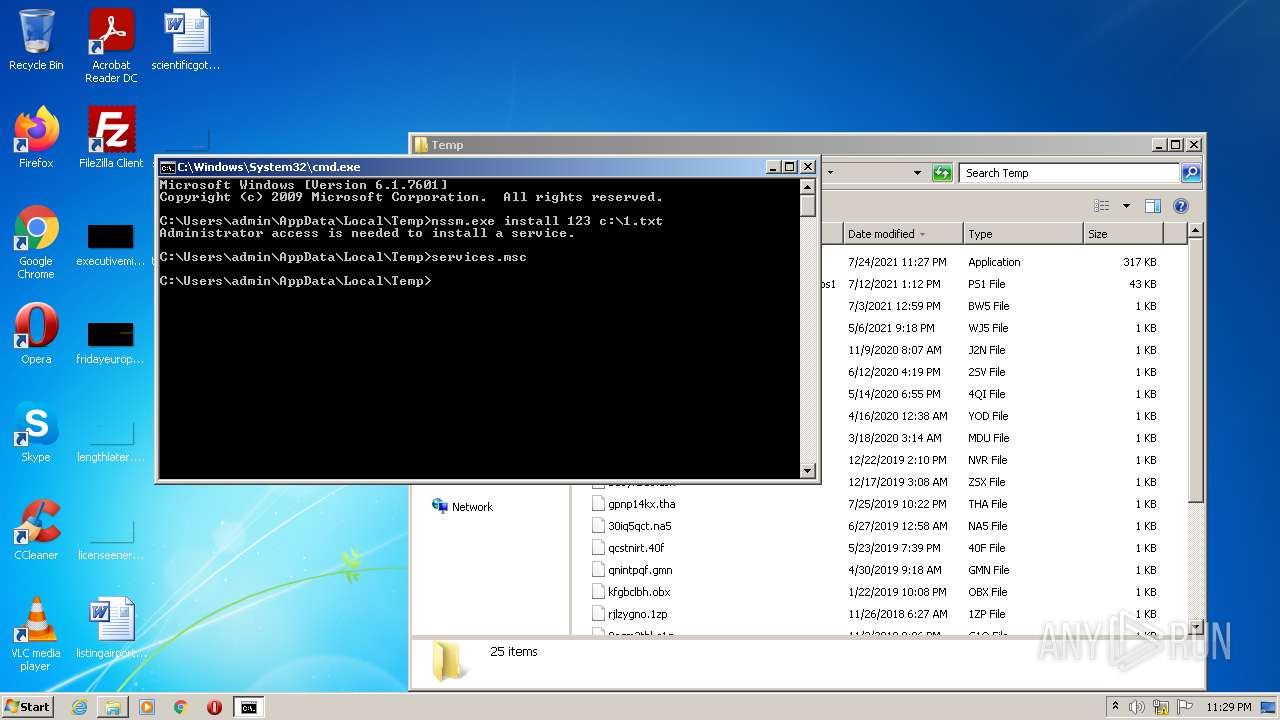
| 2232 | "C:\Users\admin\AppData\Local\Temp\nssm.exe" install 1a23 c:\1.txt | C:\Users\admin\AppData\Local\Temp\nssm.exe | nssm.exe | ||||||||||||
User: admin Company: Iain Patterson Integrity Level: HIGH Description: The non-sucking service manager Exit code: 0 Version: 2.24-101-g897c7ad Modules
| |||||||||||||||
| 2664 | "C:\Users\admin\AppData\Local\Temp\nssm.exe" install 123 c:\1.txt | C:\Users\admin\AppData\Local\Temp\nssm.exe | nssm.exe | ||||||||||||
User: admin Company: Iain Patterson Integrity Level: HIGH Description: The non-sucking service manager Exit code: 0 Version: 2.24-101-g897c7ad Modules
| |||||||||||||||
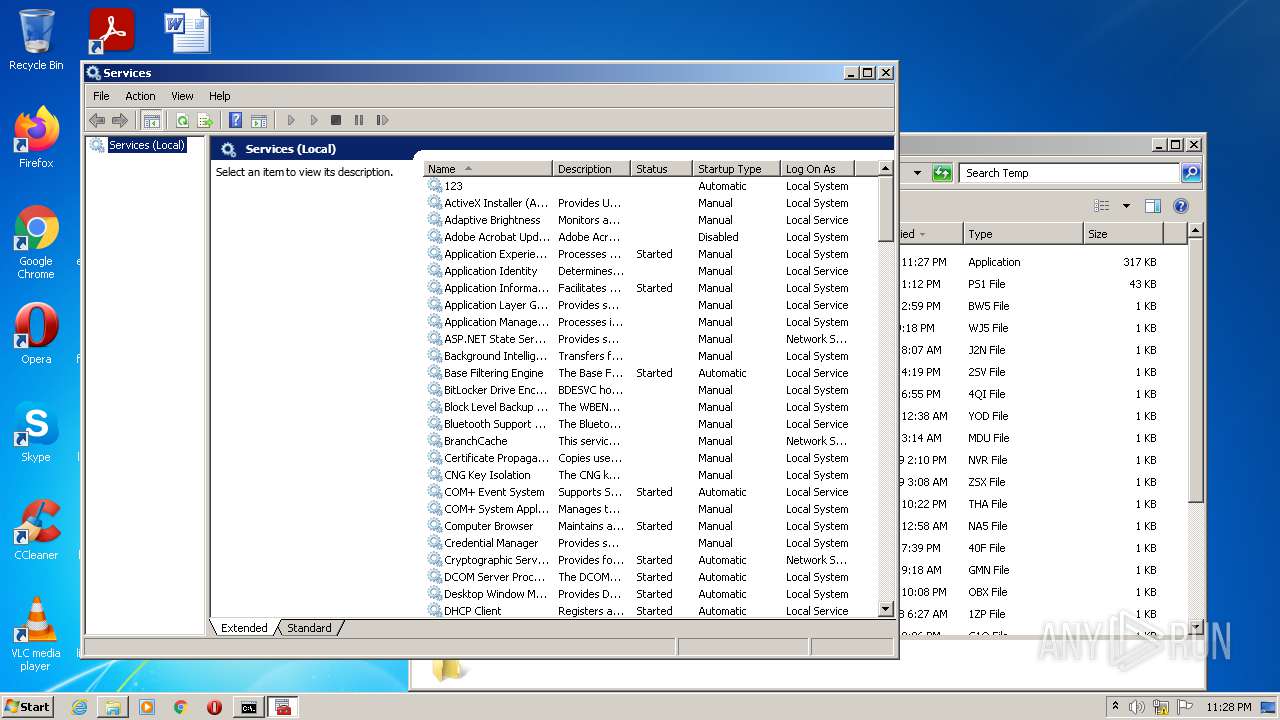
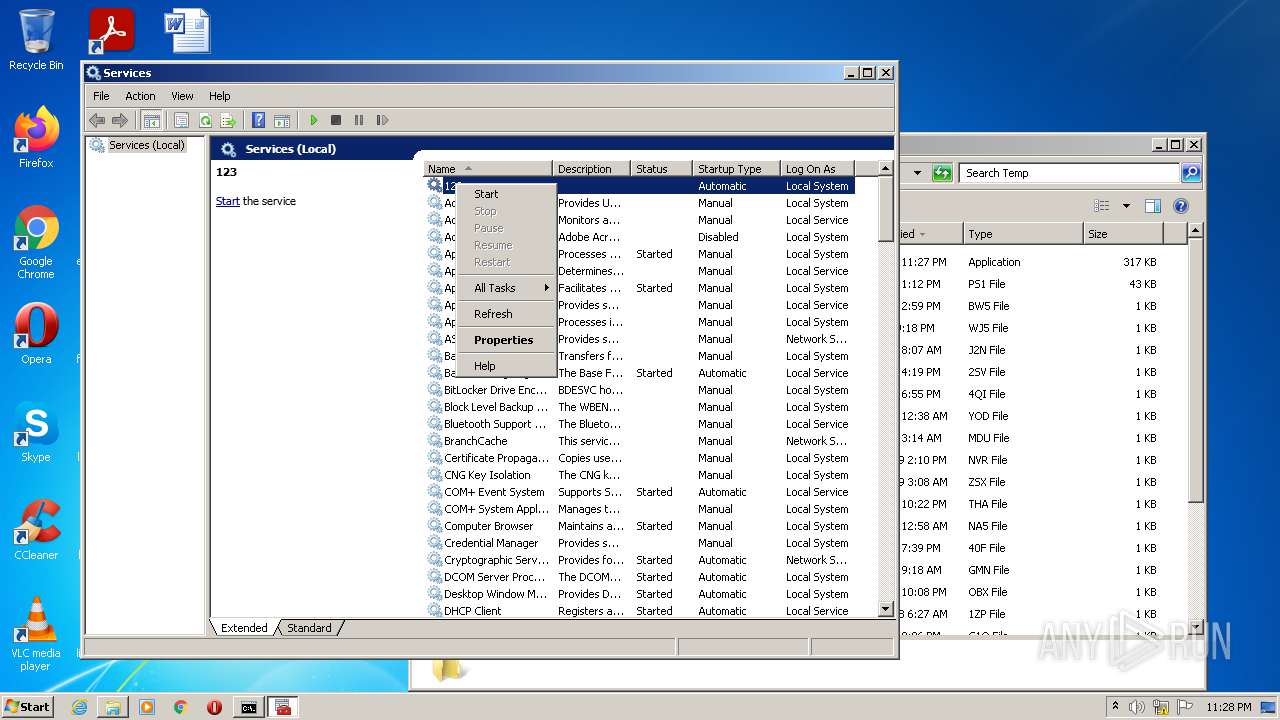
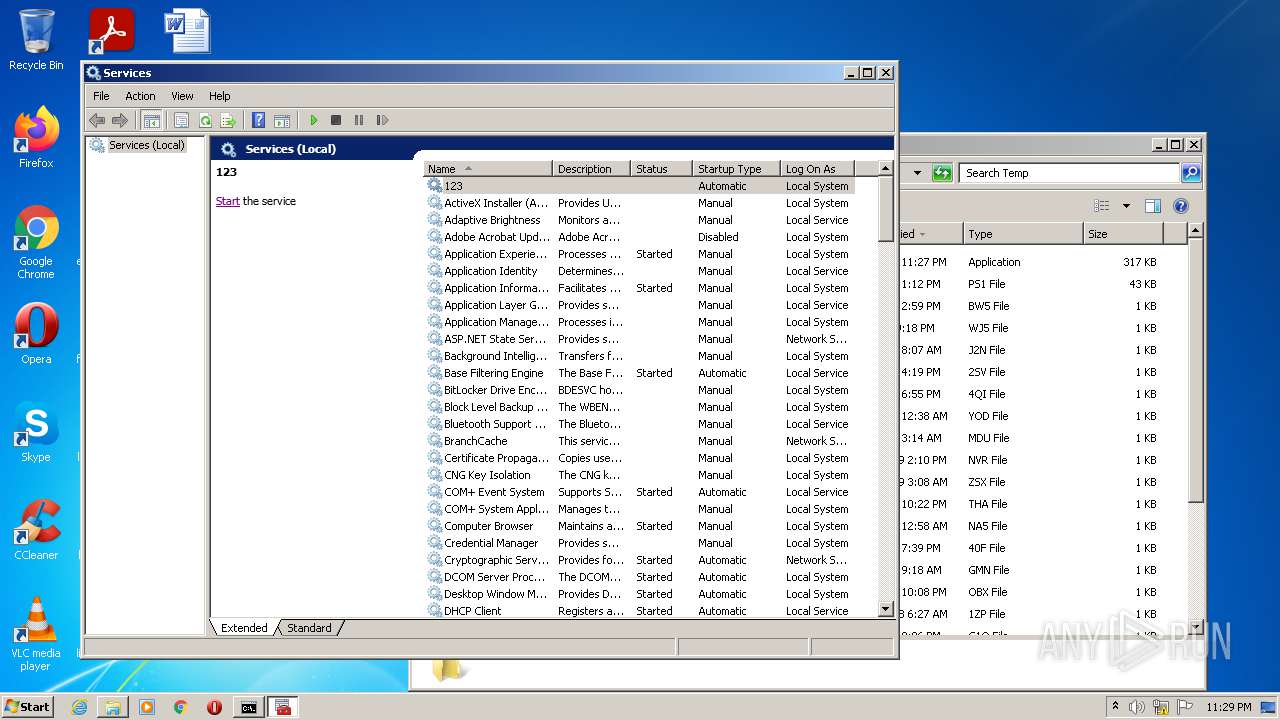
| 3356 | nssm.exe install 123 c:\1.txt | C:\Users\admin\AppData\Local\Temp\nssm.exe | — | cmd.exe | |||||||||||
User: admin Company: Iain Patterson Integrity Level: MEDIUM Description: The non-sucking service manager Exit code: 0 Version: 2.24-101-g897c7ad Modules
| |||||||||||||||
| 3356 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\AppData\Local\Temp\nssm.exe" | C:\Users\admin\AppData\Local\Temp\nssm.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Iain Patterson Integrity Level: MEDIUM Description: The non-sucking service manager Exit code: 1 Version: 2.24-101-g897c7ad Modules
| |||||||||||||||
| 3776 | C:\Users\admin\AppData\Local\Temp\nssm.exe | C:\Users\admin\AppData\Local\Temp\nssm.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Iain Patterson Integrity Level: SYSTEM Description: The non-sucking service manager Exit code: 0 Version: 2.24-101-g897c7ad Modules
| |||||||||||||||
| 3836 | nssm.exe install 1a23 c:\1.txt | C:\Users\admin\AppData\Local\Temp\nssm.exe | — | cmd.exe | |||||||||||
User: admin Company: Iain Patterson Integrity Level: MEDIUM Description: The non-sucking service manager Exit code: 3221225547 Version: 2.24-101-g897c7ad Modules
| |||||||||||||||
| 4024 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 362
Read events
2 308
Write events
53
Delete events
1
Modification events
| (PID) Process: | (3356) nssm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3356) nssm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3356) nssm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3356) nssm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2664) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Users\admin\AppData\Local\Temp\nssm.exe | |||
| (PID) Process: | (2664) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (2664) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\123\Parameters |
| Operation: | write | Name: | Application |
Value: c:\1.txt | |||
| (PID) Process: | (2664) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\123\Parameters |
| Operation: | write | Name: | AppParameters |
Value: | |||
| (PID) Process: | (2664) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\123\Parameters |
| Operation: | write | Name: | AppDirectory |
Value: c:\ | |||
| (PID) Process: | (2664) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\123\Parameters\AppExit |
| Operation: | write | Name: | (default) |
Value: Restart | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report