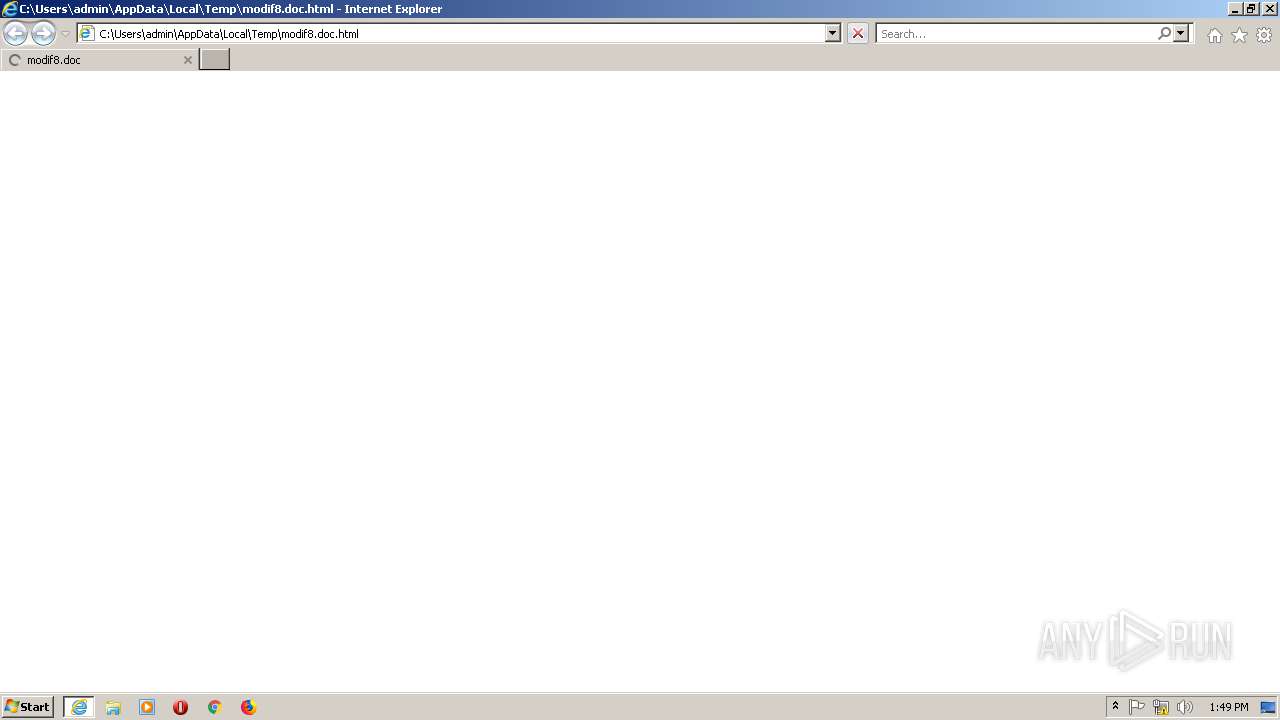
| download: | modif8.doc |
| Full analysis: | https://app.any.run/tasks/be275217-7b81-4843-9c14-8df65b1a9edf |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 13:49:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | C59EB77FC35C9894A432B85B861D9151 |
| SHA1: | DCE3B2B561993D28C0CBB4E88A7E620993C2938A |
| SHA256: | 68280197CB1421961ADFCD99631981689A80A7EB00FCFC4710D55A4EECFBB6DC |
| SSDEEP: | 192:ElVZHCkA26xd3Q4JRveuTtMy47R/Ga0kVhFuPwf8Pn9wHHyJ0b:EJvVGaRF8I8q |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2748)
Reads the machine GUID from the registry
- iexplore.exe (PID: 2748)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2496)
Changes internet zones settings
- iexplore.exe (PID: 2748)
Reads settings of System Certificates
- iexplore.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
| CacheControl: | no-cache |
| Pragma: | no-cache |
| Expires: | - |
| viewport: | width=device-width, initial-scale=1.0 |
| Title: | Account Suspended |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2496 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2748 CREDAT:144385 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\modif8.doc.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
446
Read events
375
Write events
70
Delete events
1
Modification events
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 2 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 281916848 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30739237 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 582080598 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30739237 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\favicon[2].ico | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3817913940D12843.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF60FF6F79ACE8D724.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7A917184CBB59117.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{4E6C10BB-7718-11E9-9B0A-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF171D86C7A186699F.TMP | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{0155F336-8C1D-11E8-9711-5254004AAD21}.dat | binary | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4E6C10BD-7718-11E9-9B0A-5254004AAD21}.dat | binary | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{561D671E-7718-11E9-9B0A-5254004AAD21}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2748 | iexplore.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2748 | iexplore.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 23.111.9.35:139 | use.fontawesome.com | netDNA | US | suspicious |
4 | System | 23.111.9.35:445 | use.fontawesome.com | netDNA | US | suspicious |
2748 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
use.fontawesome.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |