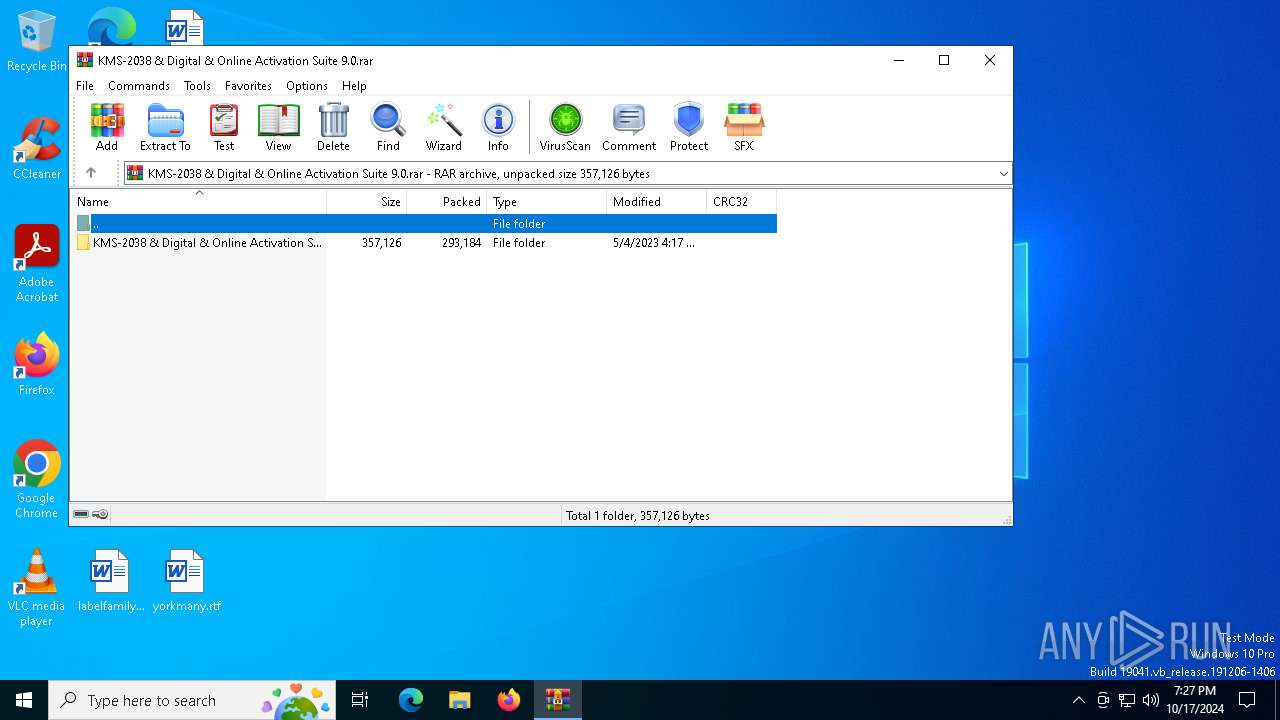
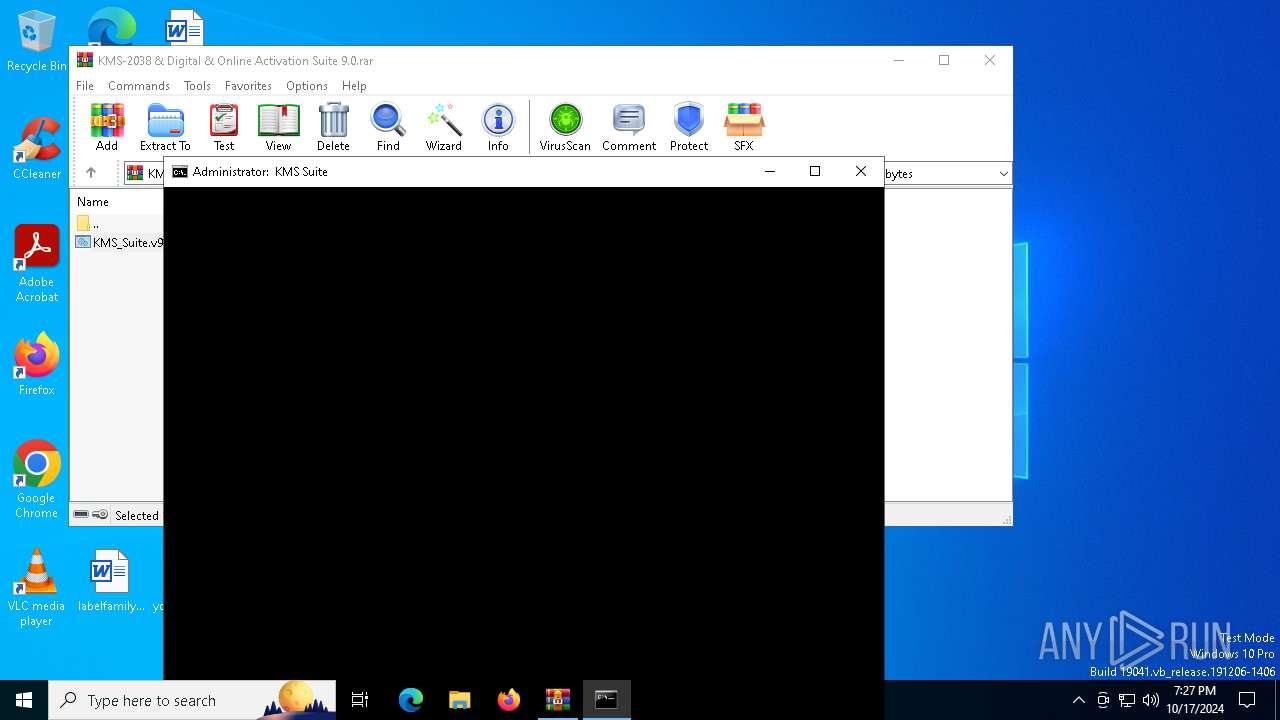
| File name: | KMS-2038 & Digital & Online Activation Suite 9.0.rar |
| Full analysis: | https://app.any.run/tasks/9c63fdb7-57d7-4bb4-99d5-b31d90b214da |
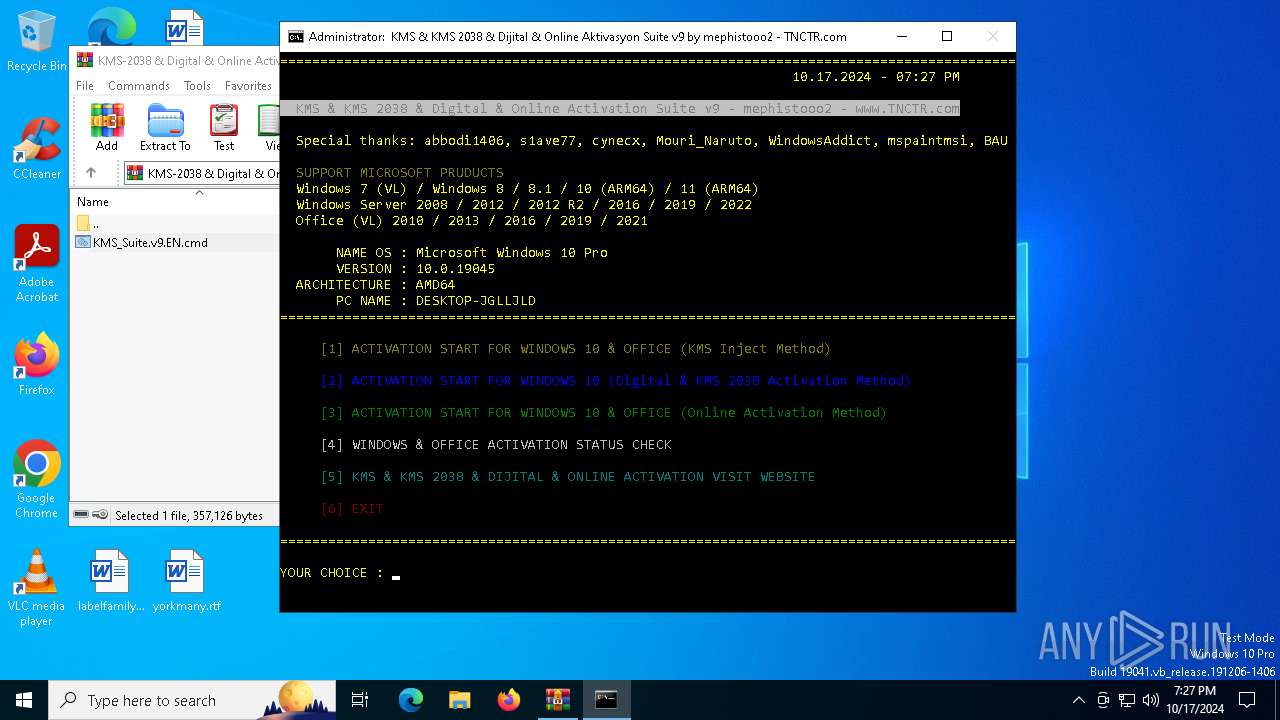
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2024, 19:26:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AC4D7A43A72966C236586D807086E021 |
| SHA1: | A5D6777F0F3D77CCAB51226F3B40E5227ECEA00E |
| SHA256: | 680FC77FB02F32DF4B6833D8FA0BBDF80D057404DE7756E93E871910803E334D |
| SSDEEP: | 12288:mEjTtHniZJIritsmALs4jEseD2zYPuM0a:mEjTtHniZJIrcsmALtgseKzYGM0a |
MALICIOUS
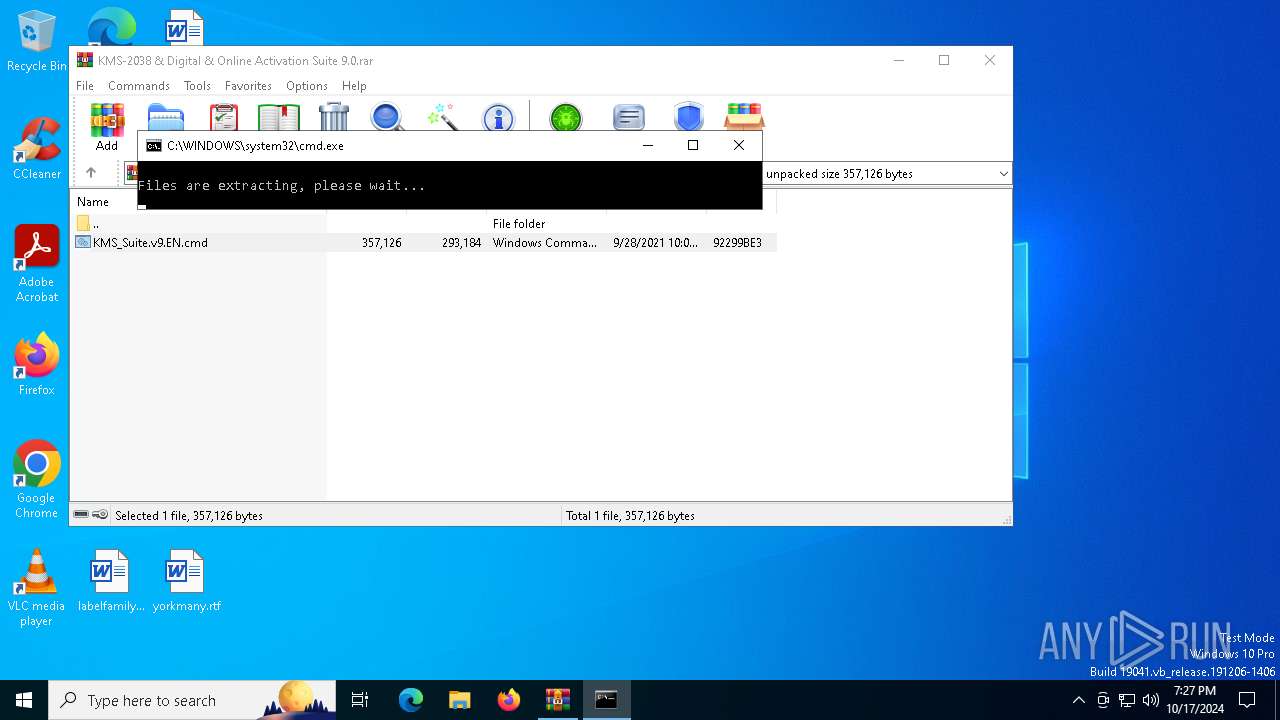
Generic archive extractor
- WinRAR.exe (PID: 6964)
Starts NET.EXE for service management
- cmd.exe (PID: 4836)
- net.exe (PID: 6448)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 6964)
- cmd.exe (PID: 3860)
- powershell.exe (PID: 3676)
- cmd.exe (PID: 4836)
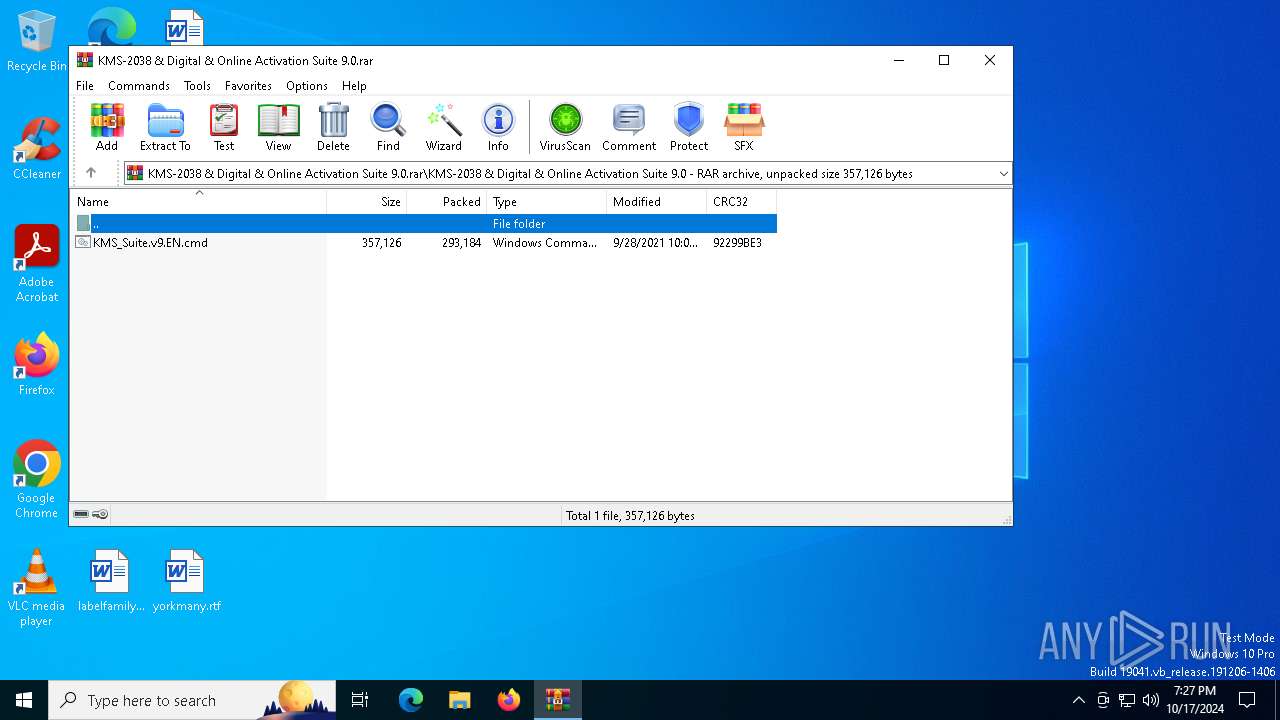
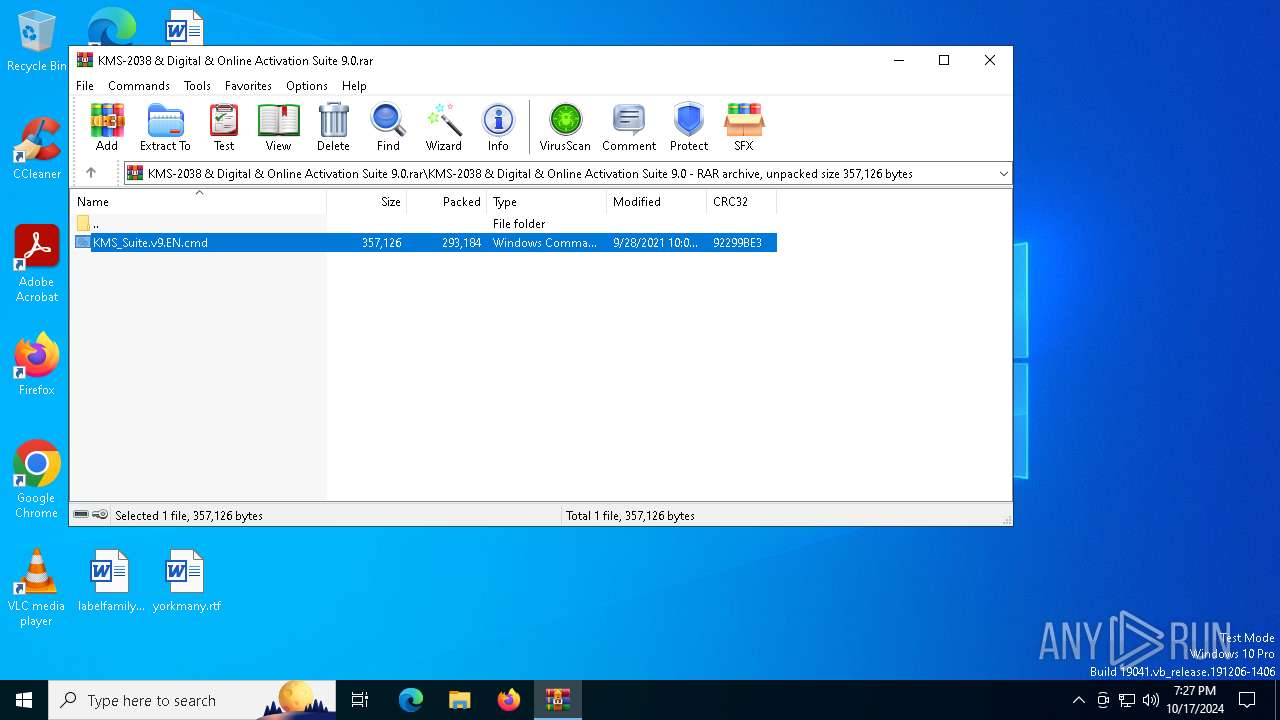
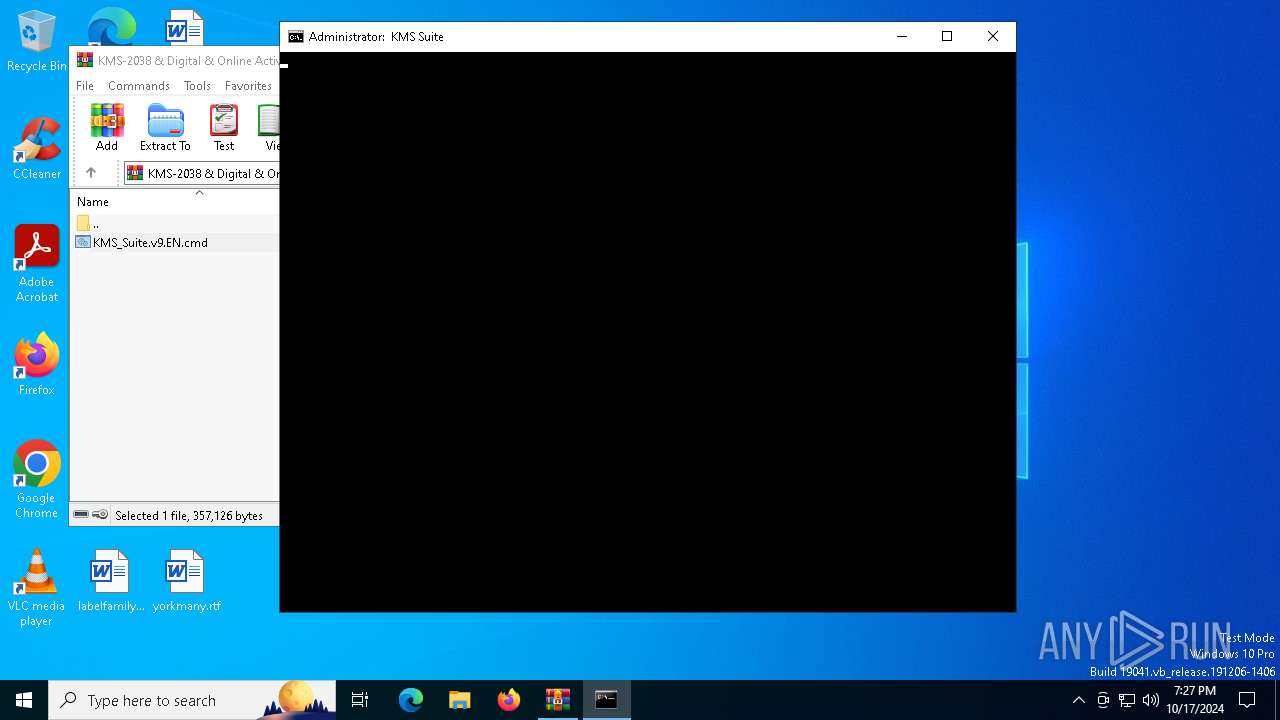
Executing commands from ".cmd" file
- WinRAR.exe (PID: 6964)
- cmd.exe (PID: 3860)
- powershell.exe (PID: 3676)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 1372)
- cmd.exe (PID: 3860)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3860)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3860)
- cmd.exe (PID: 4292)
- cmd.exe (PID: 4836)
Executable content was dropped or overwritten
- csc.exe (PID: 1572)
- expand.exe (PID: 4584)
- xcopy.exe (PID: 3396)
Manipulates environment variables
- powershell.exe (PID: 1332)
CSC.EXE is used to compile C# code
- csc.exe (PID: 1572)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3860)
Unpacks CAB file
- expand.exe (PID: 4584)
Process drops legitimate windows executable
- expand.exe (PID: 4584)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3860)
- cmd.exe (PID: 4836)
- cmd.exe (PID: 4292)
Application launched itself
- cmd.exe (PID: 3860)
- cmd.exe (PID: 4836)
Powershell scripting: start process
- cmd.exe (PID: 4292)
The process executes VB scripts
- cmd.exe (PID: 4836)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7076)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 7092)
- cmd.exe (PID: 5524)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 6956)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4836)
The executable file from the user directory is run by the CMD process
- center.exe (PID: 6112)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4836)
Starts SC.EXE for service management
- cmd.exe (PID: 4836)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4836)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 3844)
Hides command output
- cmd.exe (PID: 6024)
- cmd.exe (PID: 3844)
INFO
Starts MODE.COM to configure console settings
- mode.com (PID: 2660)
- mode.com (PID: 1344)
- mode.com (PID: 6340)
- mode.com (PID: 6956)
- mode.com (PID: 5740)
Checks operating system version
- cmd.exe (PID: 4836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
225
Monitored processes
93
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" /f /v KMS_Emulation /t REG_DWORD /d 1 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | findstr /v /a:2 /R "^f7f81a39-5f63-5b42-9efd-1f13b5431005quot; " [3] ACTIVATION START FOR WINDOWS 10 & OFFICE (Online Activation Method)" nul | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | cmd /v:on /c echo(^!param^! | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" /f /v KMS_ActivationInterval /t REG_DWORD /d 43200 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | wmic Path Win32_OperatingSystem Get Caption /format:LIST | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | wmic Path Win32_OperatingSystem Get Version /format:LIST | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | icacls "C:\WINDOWS\System32\KMS.dll" /grant *S-1-5-32-545:RX | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | find /i "KMS.dll" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | WMIC PATH SoftwareLicensingProduct WHERE (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' AND PartialProductKey is not NULL) GET LicenseFamily /VALUE | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 890
Read events
18 874
Write events
16
Delete events
0
Modification events
| (PID) Process: | (6964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMS-2038 & Digital & Online Activation Suite 9.0.rar | |||
| (PID) Process: | (6964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4836) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (4292) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\CurrentVersion\Software Protection Platform |
| Operation: | write | Name: | NoGenTicket |
Value: 1 | |||
| (PID) Process: | (5236) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | VerifierDlls |
Value: KMS.dll | |||
| (PID) Process: | (2076) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | VerifierDebug |
Value: 0 | |||
Executable files
28
Suspicious files
4
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dzvre0m2.clp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5532 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES19E5.tmp | o | |
MD5:6CF8F110088B85C07BB4FF4BEF43AE8C | SHA256:6AEC51361D240105A81113FA5039A130EB6AA8DF826B3D50E80DEC6F3BD3FB3D | |||
| 1332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ckqrk53x.cxs.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0mjc2wmy.0.cs | text | |
MD5:047F0CF592670E8FCA358F12E4CD5A89 | SHA256:32E77D9085AD9EA0FD1EB5A9556E29CB42F5D3016CCF9853F3C39D358F479978 | |||
| 6964 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6964.5212\KMS_Suite.v9.EN.cmd | text | |
MD5:F9906448D778C93D1B96F87E92E9B436 | SHA256:54C33E9C26EF68F0521CB6D6A416FCD2A6C22537D49ADE62DB6935CCC4129927 | |||
| 1332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0mjc2wmy.cmdline | text | |
MD5:A57D1E23F3B9445E80D54C50CFB79694 | SHA256:3385C08D8D309FF6147607712245F35FB6D9554C8EBC9D00C55D58E01033B4CF | |||
| 4584 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\Digital\bin\gatherosstate.exe | executable | |
MD5:15CE0753A16DD4F9B9F0F9926DD37C4E | SHA256:028C8FBE58F14753B946475DE9F09A9C7A05FD62E81A1339614C9E138FC2A21D | |||
| 4584 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\center.exe | executable | |
MD5:0A847EAFDDC4529388E1A1B291354CF8 | SHA256:69533D9B66B840B4764F901CD6A502D12453B604617A841F4C2C602FC87DF255 | |||
| 4584 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\DisableX.exe | executable | |
MD5:00C9837407663587C69DF18793248D52 | SHA256:09933212238BC7D0CCE57469F9927C0325D5670B21FC7787428574C4A52E5F6D | |||
| 4584 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\DisableX.vbs | text | |
MD5:C2206C9C9B0C97F7C5DB4F473E96E9A3 | SHA256:F1CEC878CD1DB36CA4CCB68296CD47CE039054E2ECE4CD22D9933B90C8625C1F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
51
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
7164 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
4004 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4904 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
7164 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6908 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.152:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |