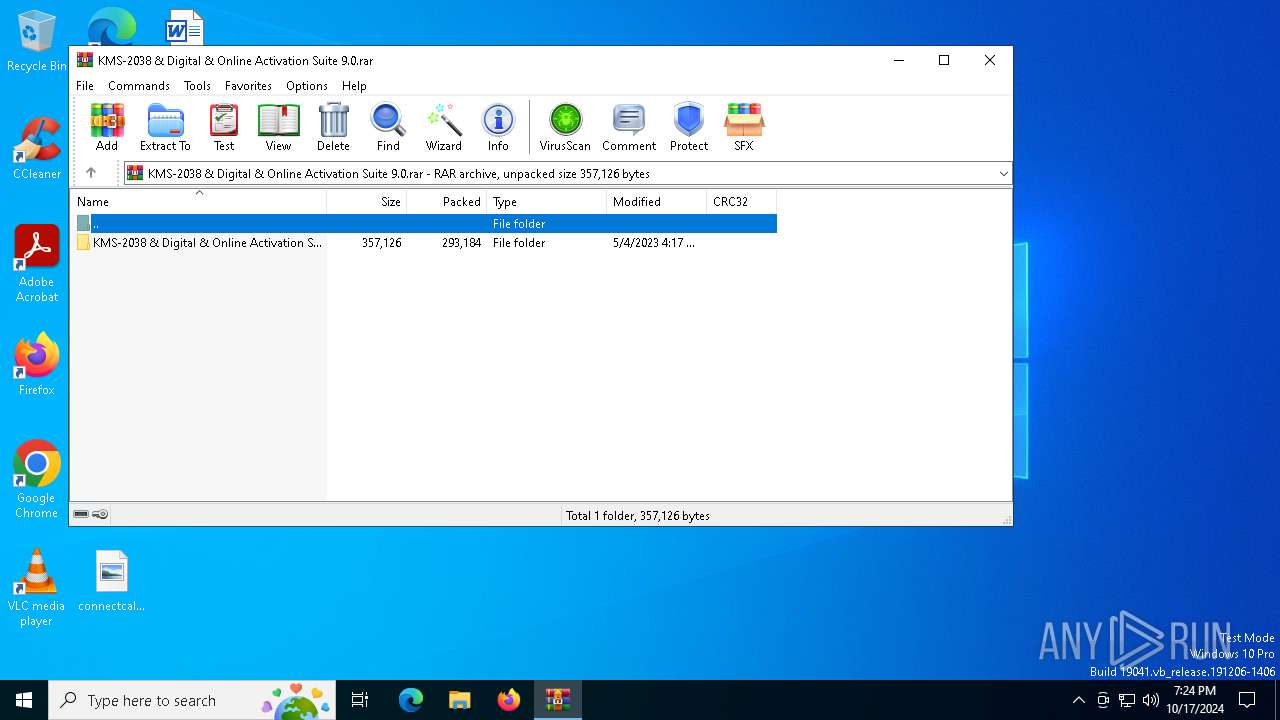
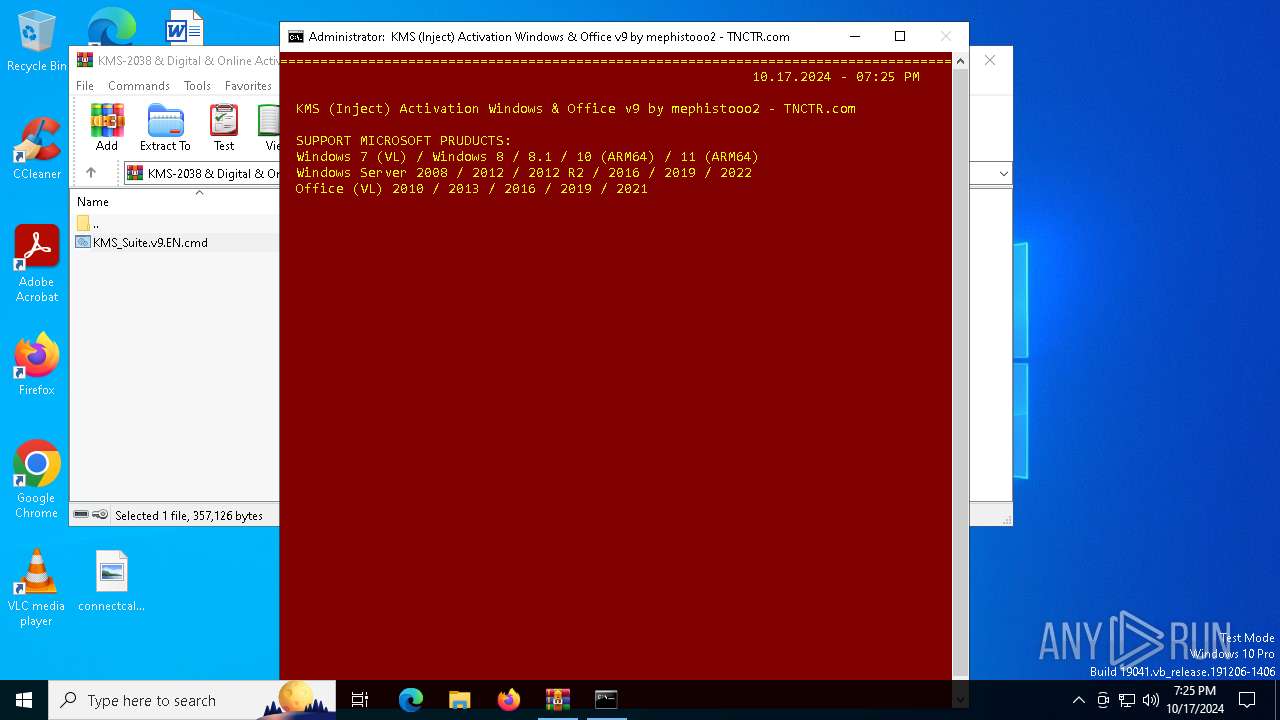
| File name: | KMS-2038 & Digital & Online Activation Suite 9.0.rar |
| Full analysis: | https://app.any.run/tasks/00597c60-a3c4-4831-80c4-8880e760dacd |
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2024, 19:24:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AC4D7A43A72966C236586D807086E021 |
| SHA1: | A5D6777F0F3D77CCAB51226F3B40E5227ECEA00E |
| SHA256: | 680FC77FB02F32DF4B6833D8FA0BBDF80D057404DE7756E93E871910803E334D |
| SSDEEP: | 12288:mEjTtHniZJIritsmALs4jEseD2zYPuM0a:mEjTtHniZJIrcsmALtgseKzYGM0a |
MALICIOUS
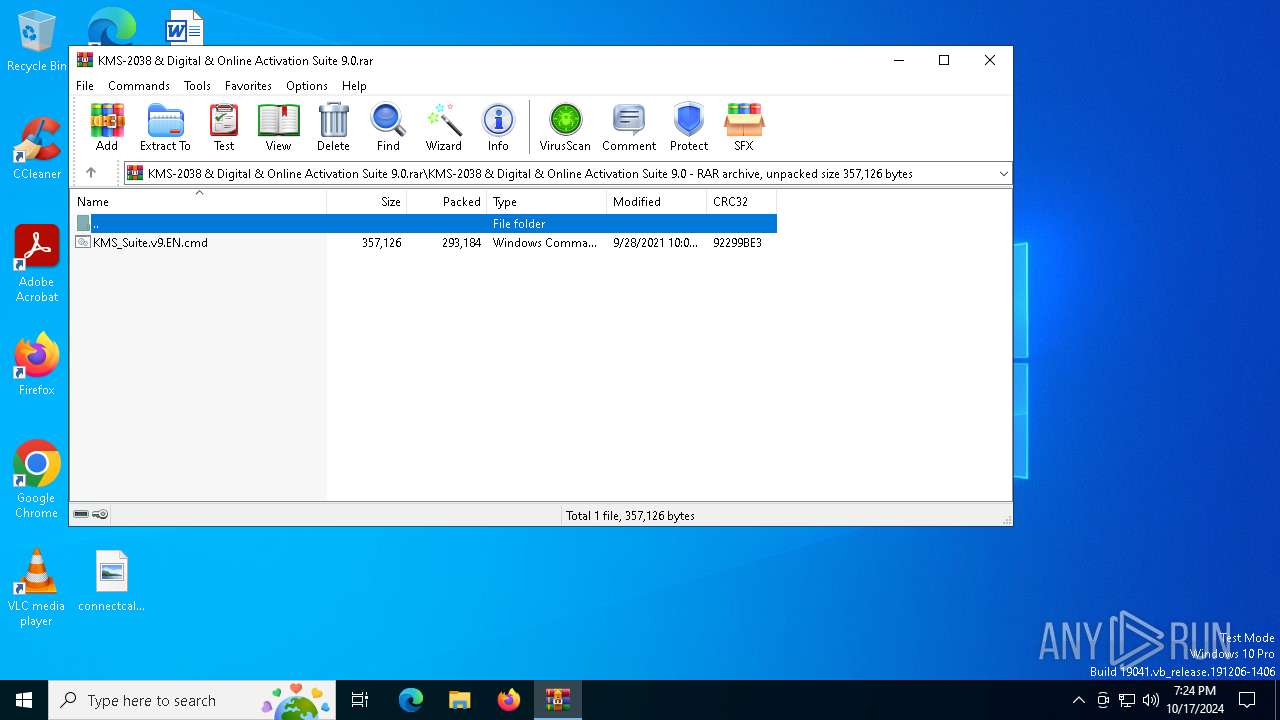
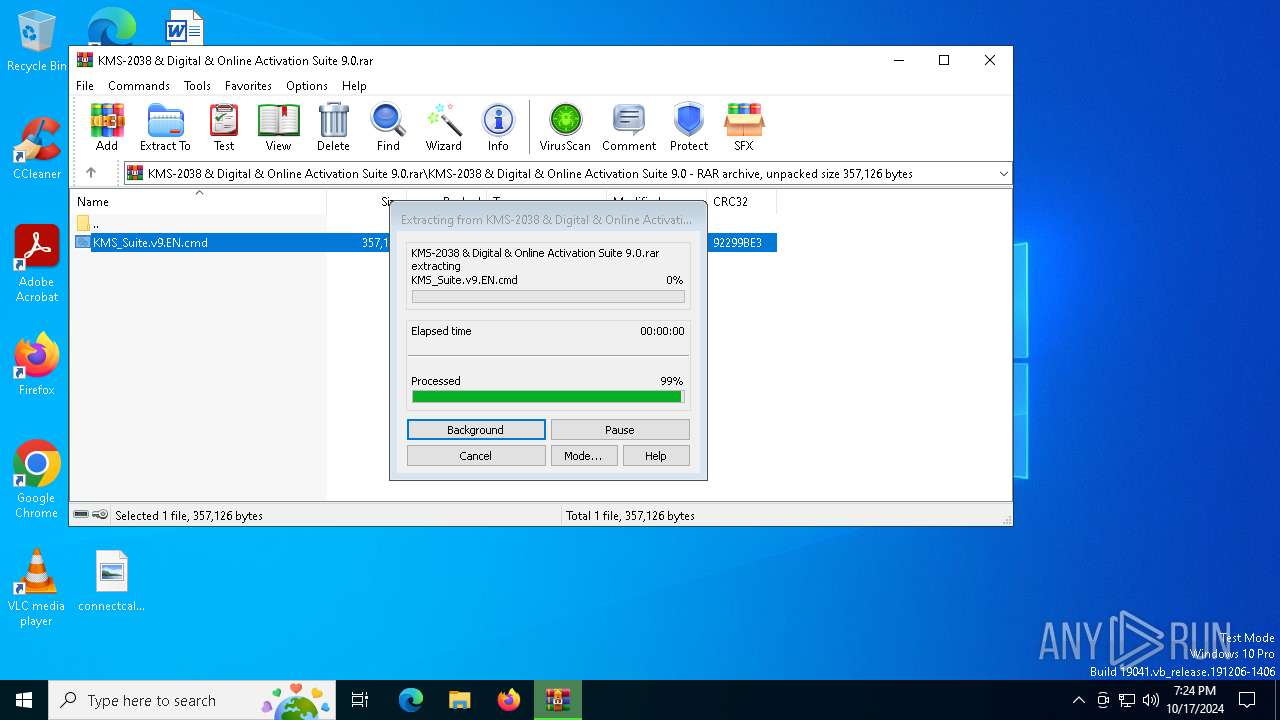
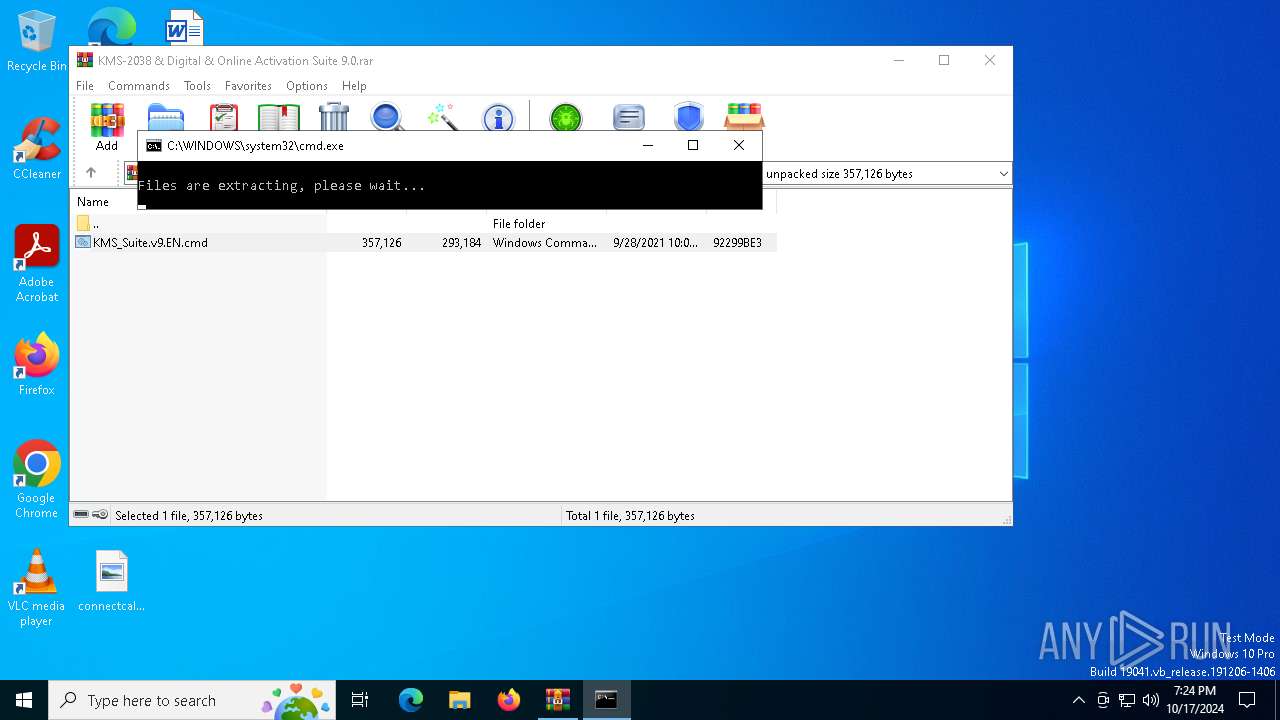
Generic archive extractor
- WinRAR.exe (PID: 5828)
SUSPICIOUS
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 3912)
- cmd.exe (PID: 5616)
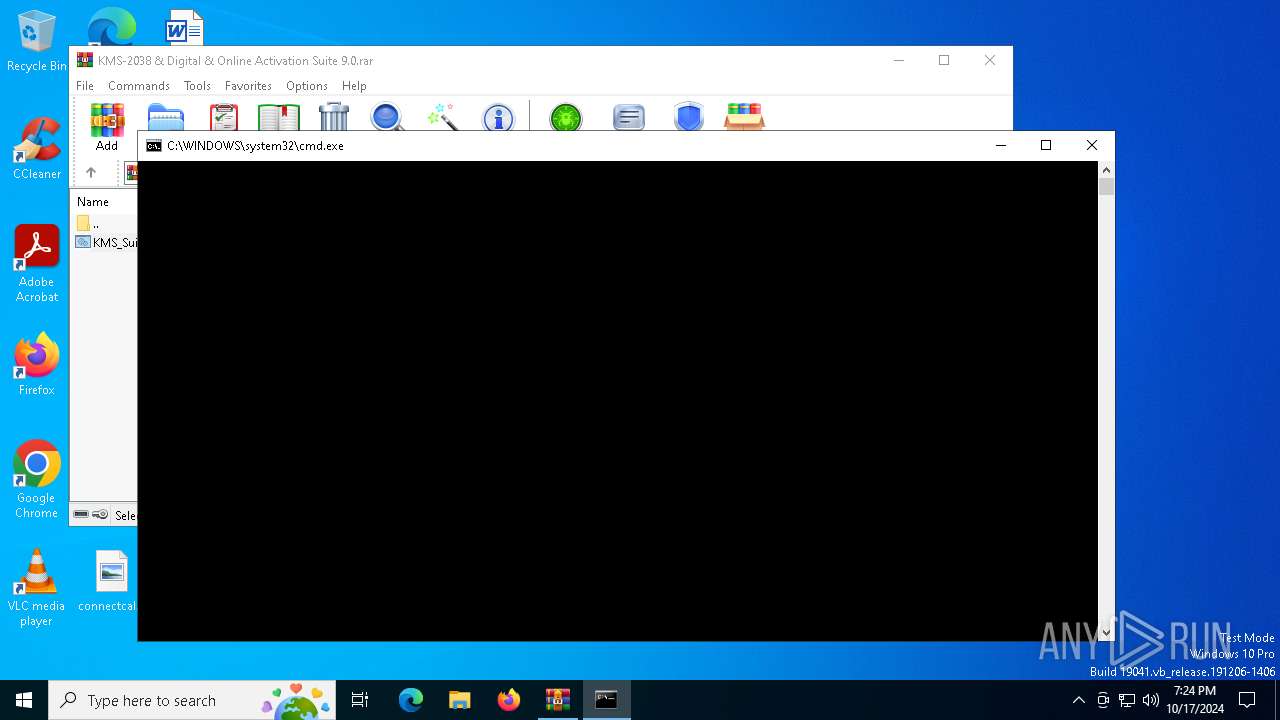
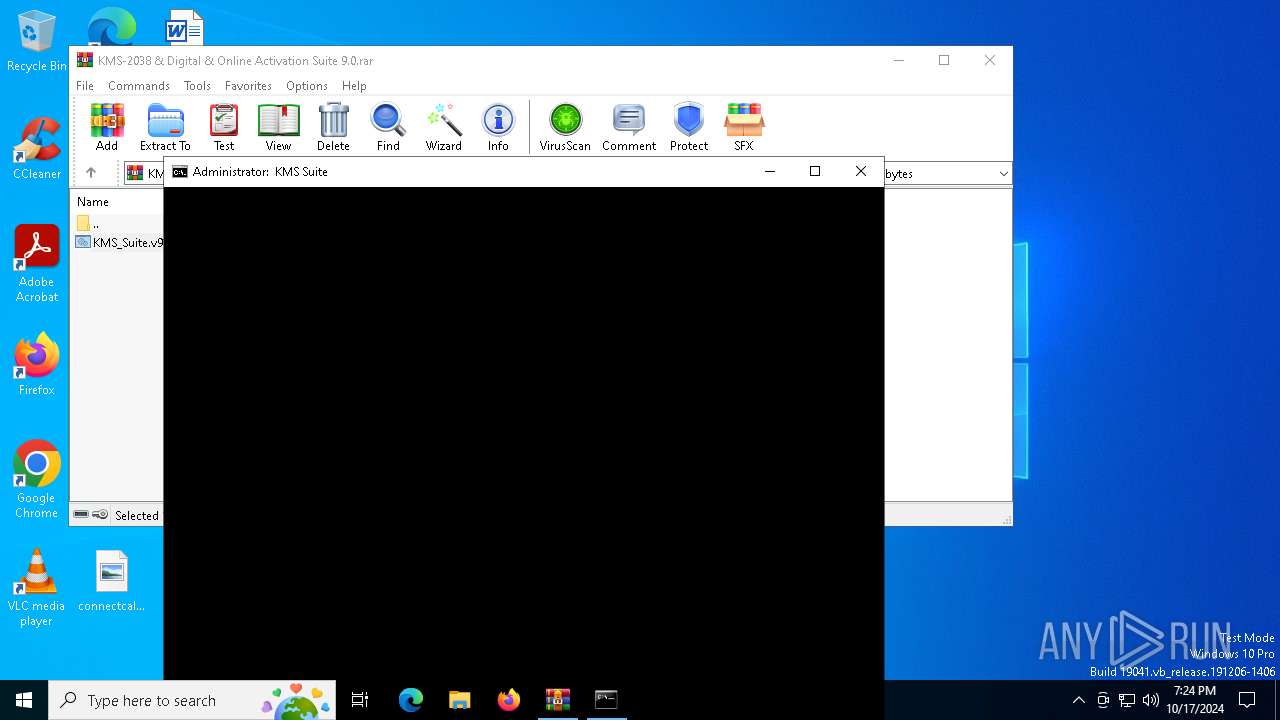
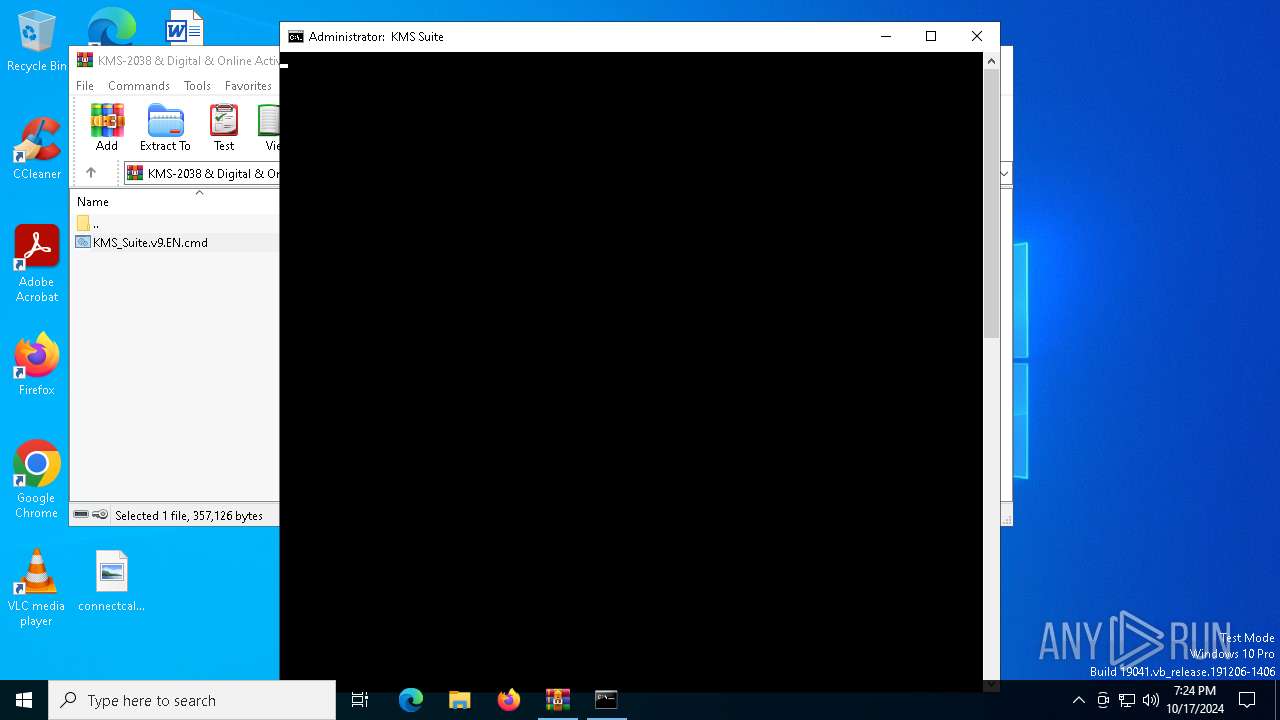
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 5828)
- cmd.exe (PID: 5616)
- powershell.exe (PID: 6180)
- cmd.exe (PID: 6128)
Executing commands from ".cmd" file
- WinRAR.exe (PID: 5828)
- cmd.exe (PID: 5616)
- powershell.exe (PID: 6180)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5616)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6128)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5616)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5616)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6128)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5616)
Manipulates environment variables
- powershell.exe (PID: 6100)
CSC.EXE is used to compile C# code
- csc.exe (PID: 920)
Unpacks CAB file
- expand.exe (PID: 3108)
Executable content was dropped or overwritten
- csc.exe (PID: 920)
- expand.exe (PID: 3108)
- xcopy.exe (PID: 6356)
Process drops legitimate windows executable
- expand.exe (PID: 3108)
Application launched itself
- cmd.exe (PID: 5616)
- cmd.exe (PID: 6128)
Powershell scripting: start process
- cmd.exe (PID: 7128)
The process executes VB scripts
- cmd.exe (PID: 6128)
The executable file from the user directory is run by the CMD process
- center.exe (PID: 7052)
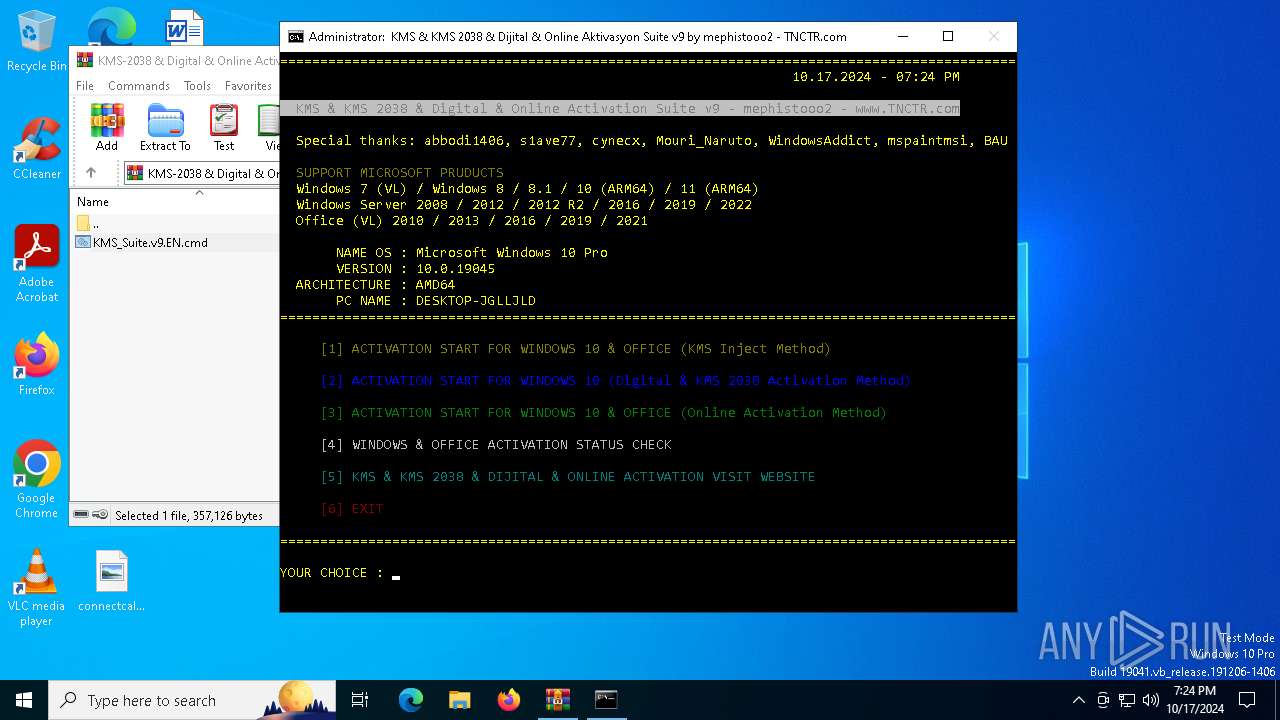
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6852)
- cmd.exe (PID: 5516)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 540)
- cmd.exe (PID: 5220)
- cmd.exe (PID: 4312)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6128)
INFO
Starts MODE.COM to configure console settings
- mode.com (PID: 5624)
- mode.com (PID: 3824)
- mode.com (PID: 5036)
- mode.com (PID: 2376)
- mode.com (PID: 6124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
190
Monitored processes
56
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\5911\bin\DisableX.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 540 | C:\WINDOWS\system32\cmd.exe /c "wmic Path Win32_OperatingSystem Get Version /format:LIST" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | findstr /R "[| ` ~ ! @ % \ / ^ & ( ) \[ \] { } + = ; : ' , |]*^" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\3ekxbpcm.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 920 | wmic Path Win32_OperatingSystem Get Version /format:LIST | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2376 | mode con cols=92 lines=35 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2376 | C:\WINDOWS\system32\cmd.exe /c time /t | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2660 | cmd /v:on /c echo(^!param^! | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 489
Read events
18 482
Write events
7
Delete events
0
Modification events
| (PID) Process: | (5828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMS-2038 & Digital & Online Activation Suite 9.0.rar | |||
| (PID) Process: | (5828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6128) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
28
Suspicious files
4
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 920 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC34D45373CD84AC09CD2A48D41BABFDA.TMP | binary | |
MD5:2C70A082220082927C69FD6DE65EC73C | SHA256:9FA8DBB7DE5CD283699816C128E256C8A988FC53E24C3F15477D2E33C04B04B5 | |||
| 6100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3ekxbpcm.cmdline | text | |
MD5:25D3829B640CEB273807424E28F15D7B | SHA256:5548D640AF872814E57CC894ECB47B0030188E8420671E811EF6D1EAB3A361E9 | |||
| 920 | csc.exe | C:\Users\admin\AppData\Local\Temp\3ekxbpcm.dll | executable | |
MD5:F54836F5816C388F70AA455E72A06BF7 | SHA256:71F3A30B5EC132B08F736D6ED339CE5731B55CAC9798DA6E55D6A3BCF8210E68 | |||
| 6100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3ekxbpcm.0.cs | text | |
MD5:047F0CF592670E8FCA358F12E4CD5A89 | SHA256:32E77D9085AD9EA0FD1EB5A9556E29CB42F5D3016CCF9853F3C39D358F479978 | |||
| 6100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gdwcbjal.ilw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1 | compressed | |
MD5:2F3B771C22DB25813A4530B5BAE62636 | SHA256:9B6B0BDEDBC8B408D93F5FC4FC69605CE6547894D9B0A263920CD8911D2B44B4 | |||
| 920 | csc.exe | C:\Users\admin\AppData\Local\Temp\3ekxbpcm.out | text | |
MD5:1C513822D98C0045453D5AB8155AF7E0 | SHA256:DAD7BD6CCBA7B182ECB405F7B3644C8540F2C1AE2E626F6B45F987E56F857C1C | |||
| 3108 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\DisableX.vbs | text | |
MD5:C2206C9C9B0C97F7C5DB4F473E96E9A3 | SHA256:F1CEC878CD1DB36CA4CCB68296CD47CE039054E2ECE4CD22D9933B90C8625C1F | |||
| 3108 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\center.exe | executable | |
MD5:0A847EAFDDC4529388E1A1B291354CF8 | SHA256:69533D9B66B840B4764F901CD6A502D12453B604617A841F4C2C602FC87DF255 | |||
| 3108 | expand.exe | C:\Users\admin\AppData\Local\Temp\KMS_Suite\bin\DisableX.exe | executable | |
MD5:00C9837407663587C69DF18793248D52 | SHA256:09933212238BC7D0CCE57469F9927C0325D5670B21FC7787428574C4A52E5F6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
55
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4292 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 2.23.9.218:80 | www.microsoft.com | AKAMAI-AS | CZ | whitelisted |
4360 | SearchApp.exe | 23.212.110.144:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
7028 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |