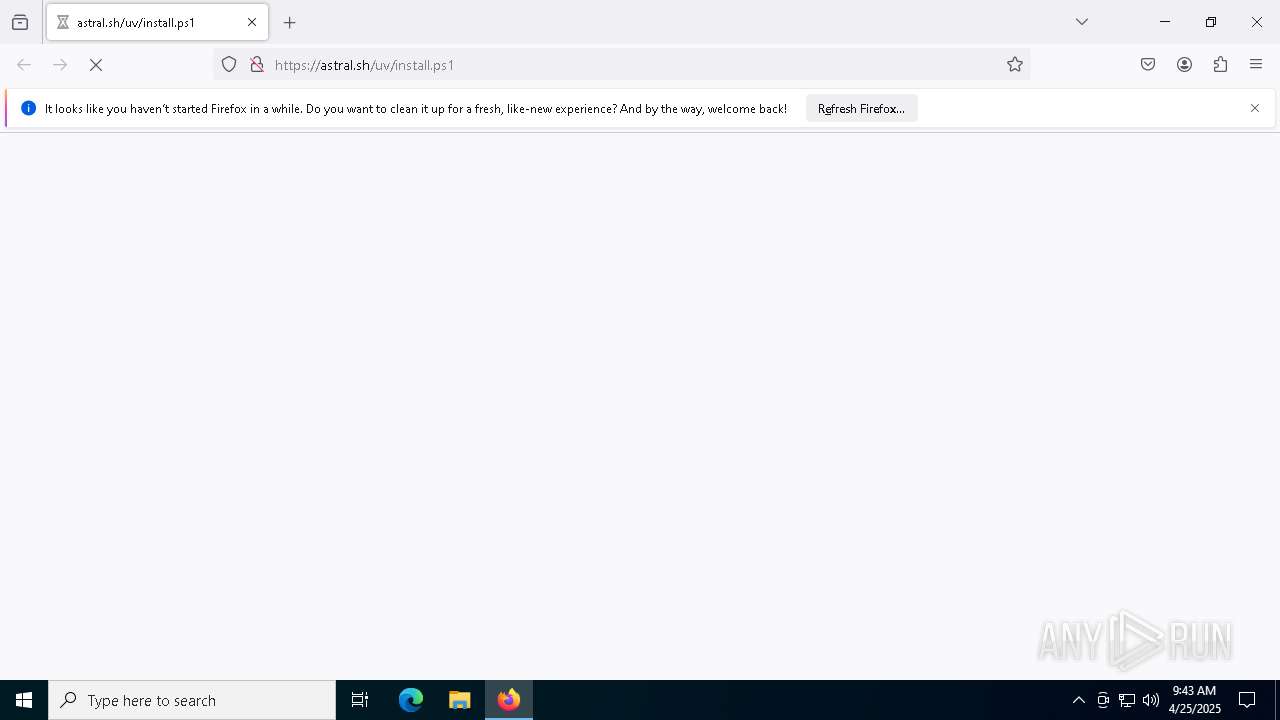
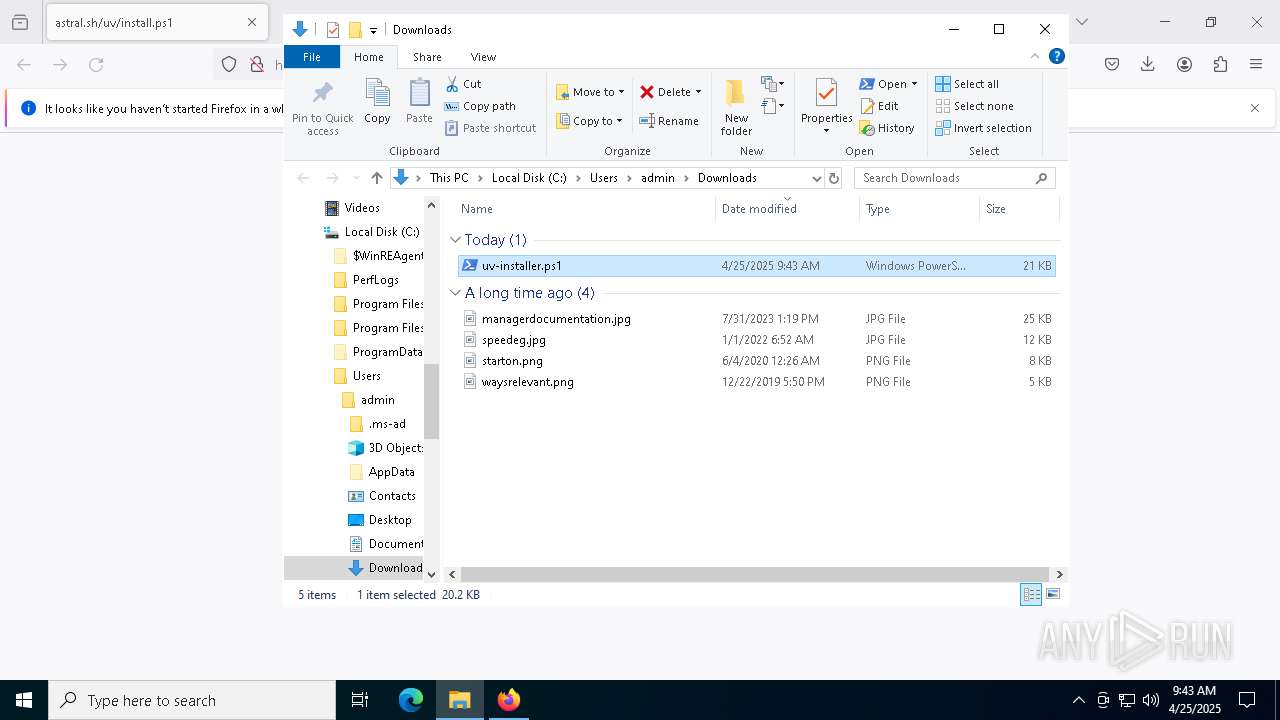
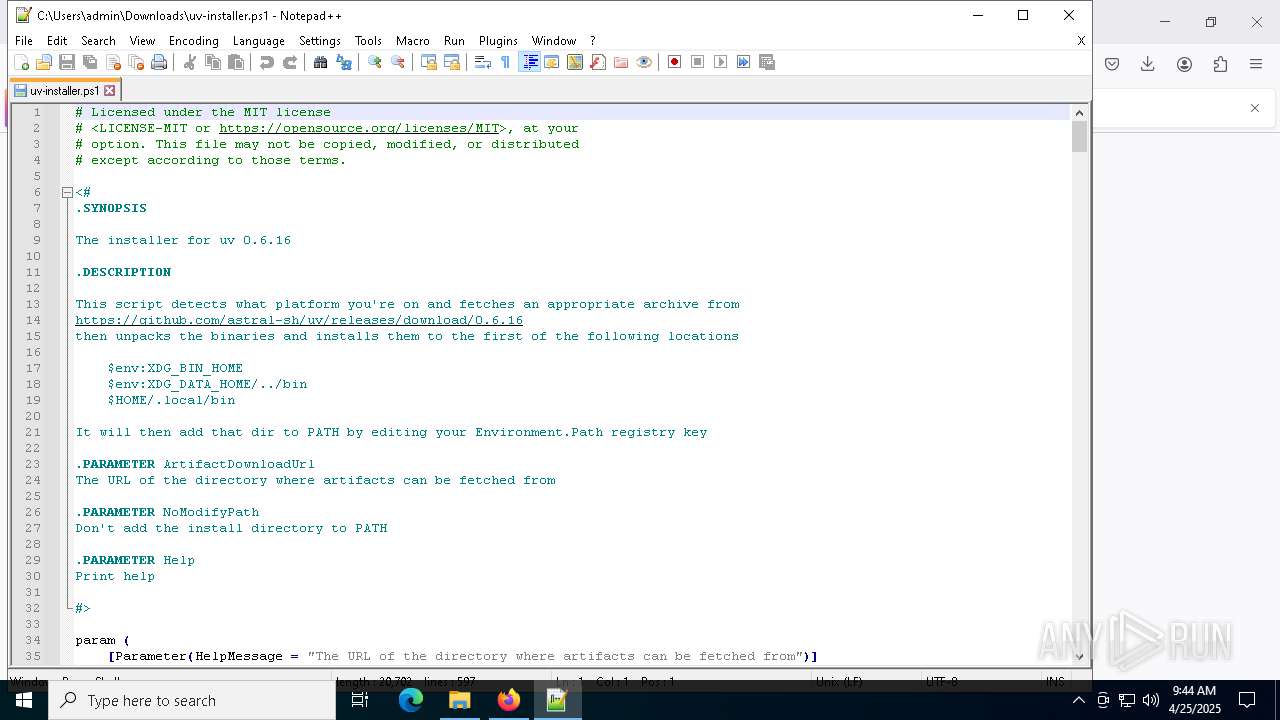
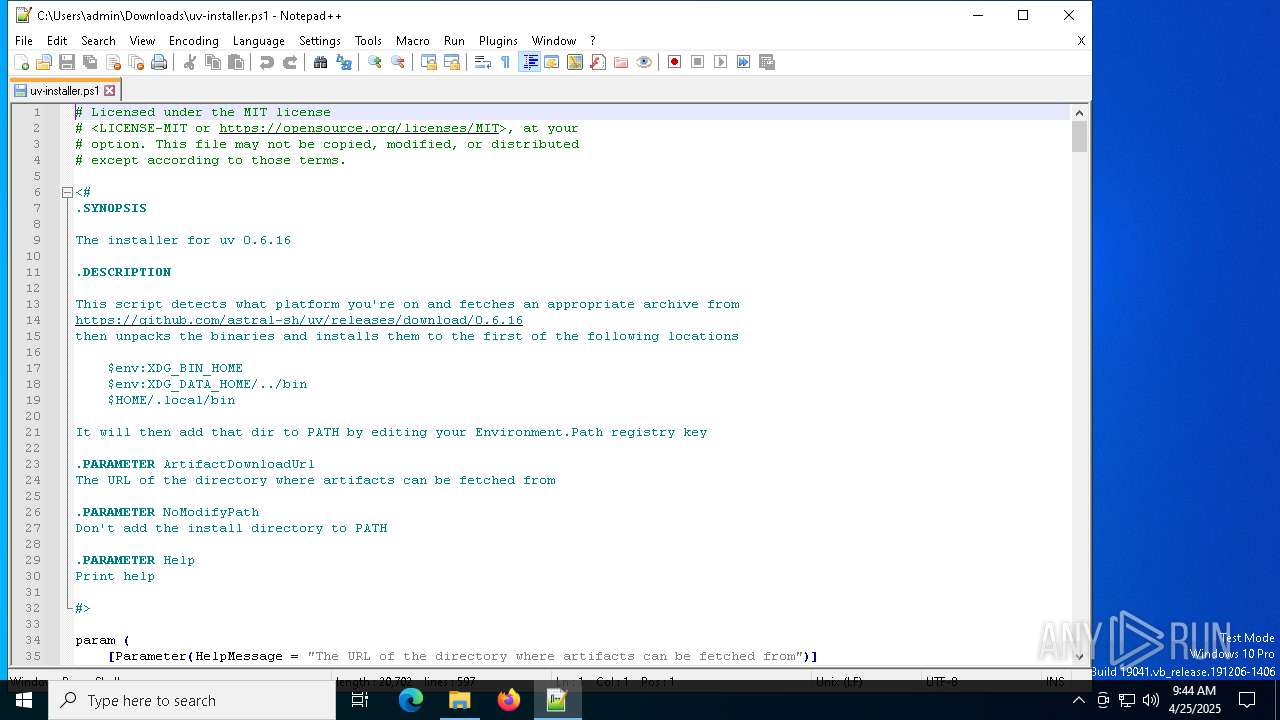
| URL: | https://astral.sh/uv/install.ps1 |
| Full analysis: | https://app.any.run/tasks/8c40525e-43c0-4c59-9a27-01dff146f43d |
| Verdict: | Malicious activity |
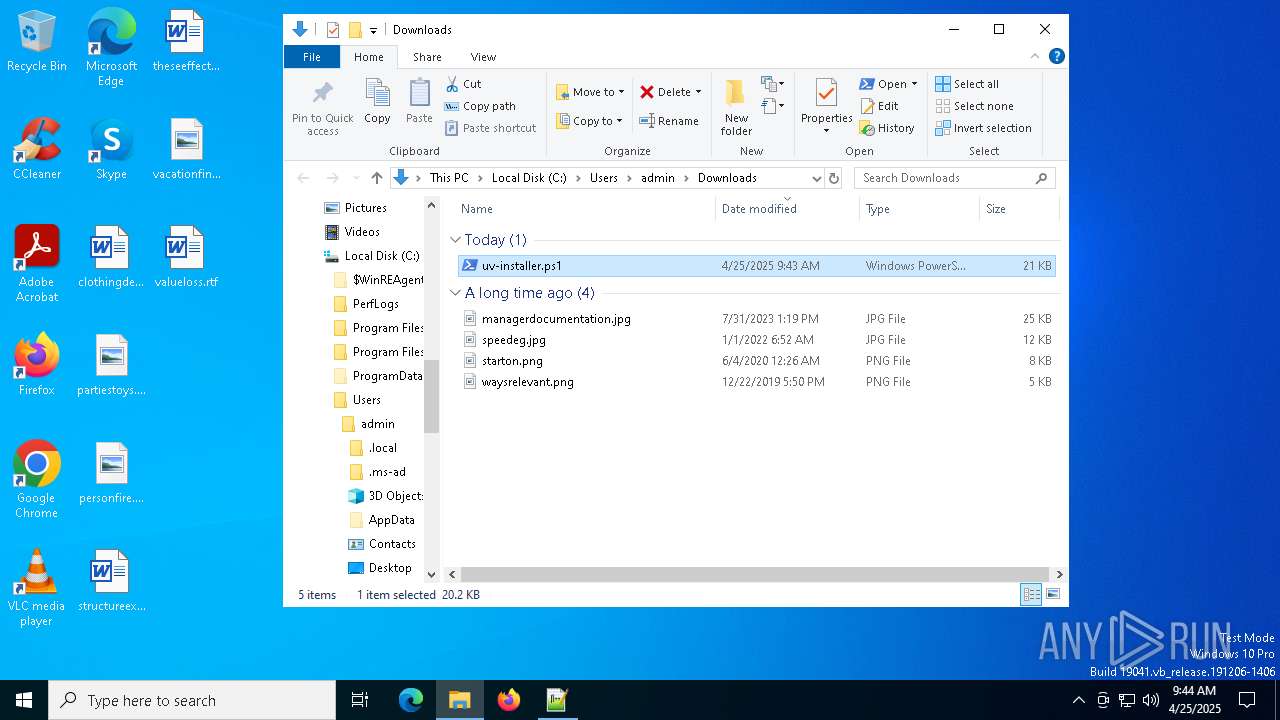
| Analysis date: | April 25, 2025, 09:43:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EB488A674695A36B4037759DDF8C32F9 |
| SHA1: | 982076D50687BFDDDD4A22E3DE32276CD05F6F57 |
| SHA256: | 680FC58F3A8D5DF3F85877EE680C1D31275214002F2BAF9883CE926E6268D2BC |
| SSDEEP: | 3:N8jDKQTbWgF8U:2vLTp7 |
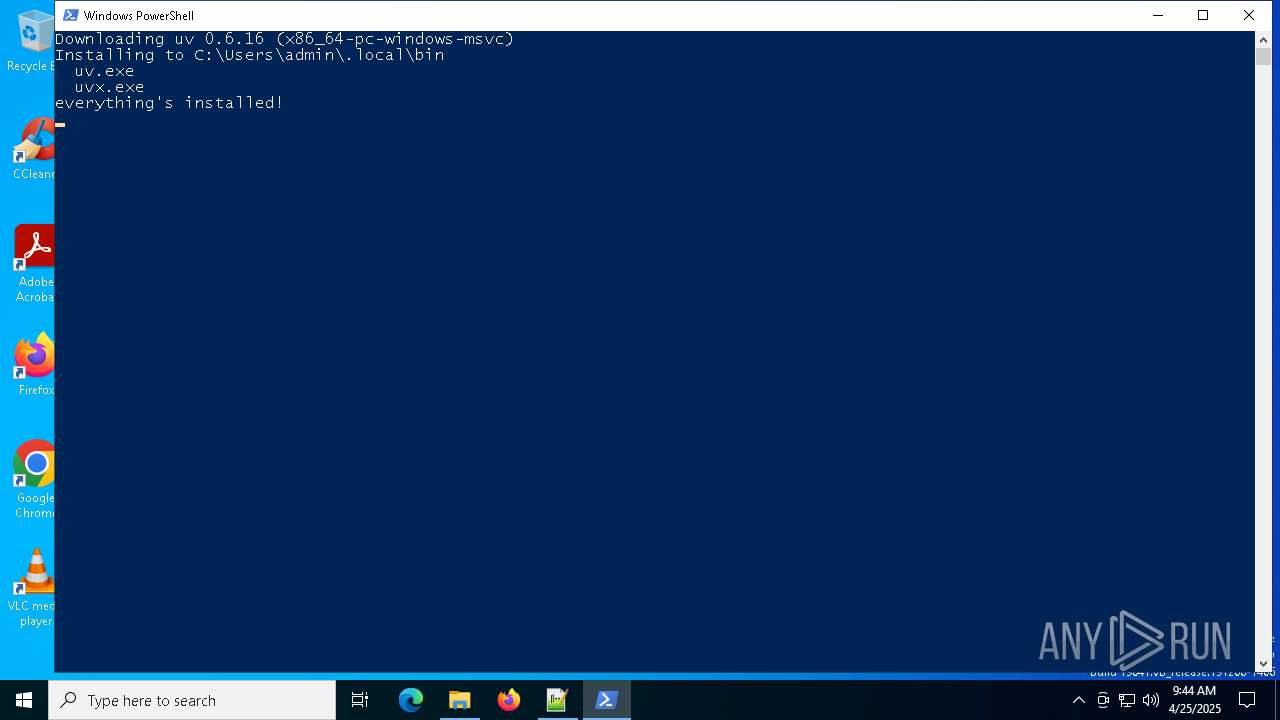
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6132)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6132)
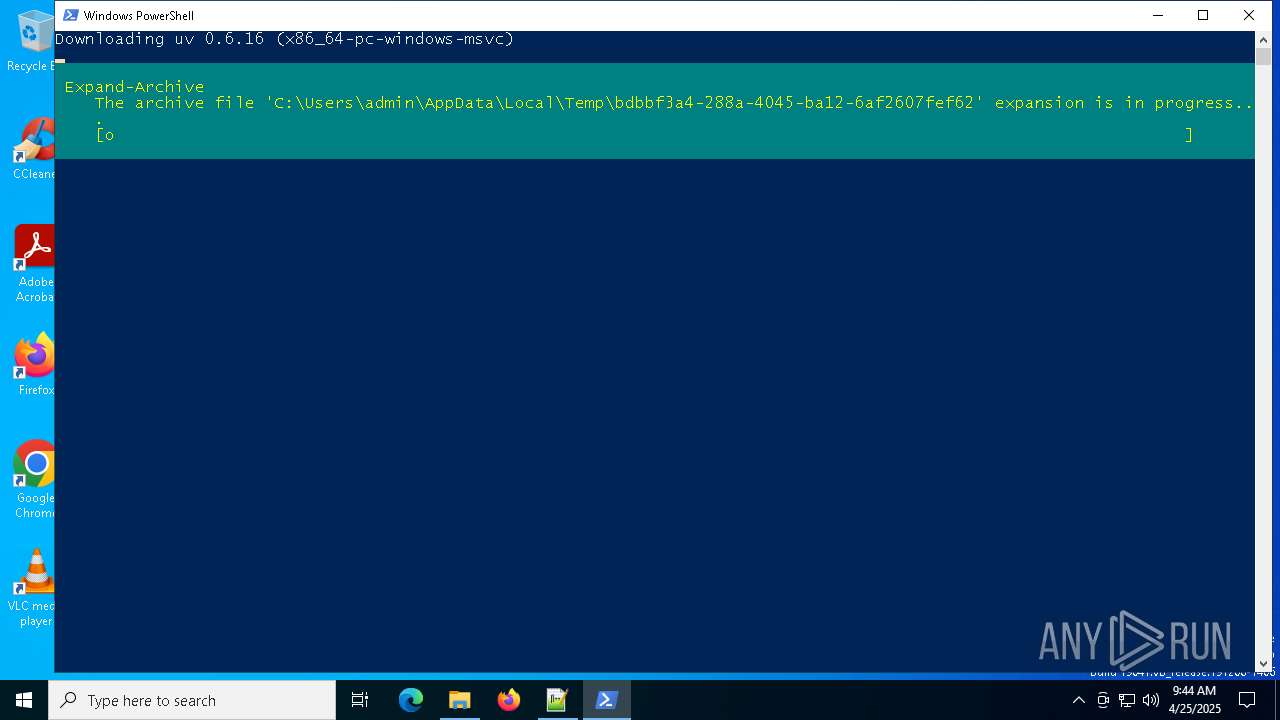
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6132)
SUSPICIOUS
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6132)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6132)
Executable content was dropped or overwritten
- powershell.exe (PID: 6132)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6132)
INFO
Application launched itself
- firefox.exe (PID: 1272)
- firefox.exe (PID: 4944)
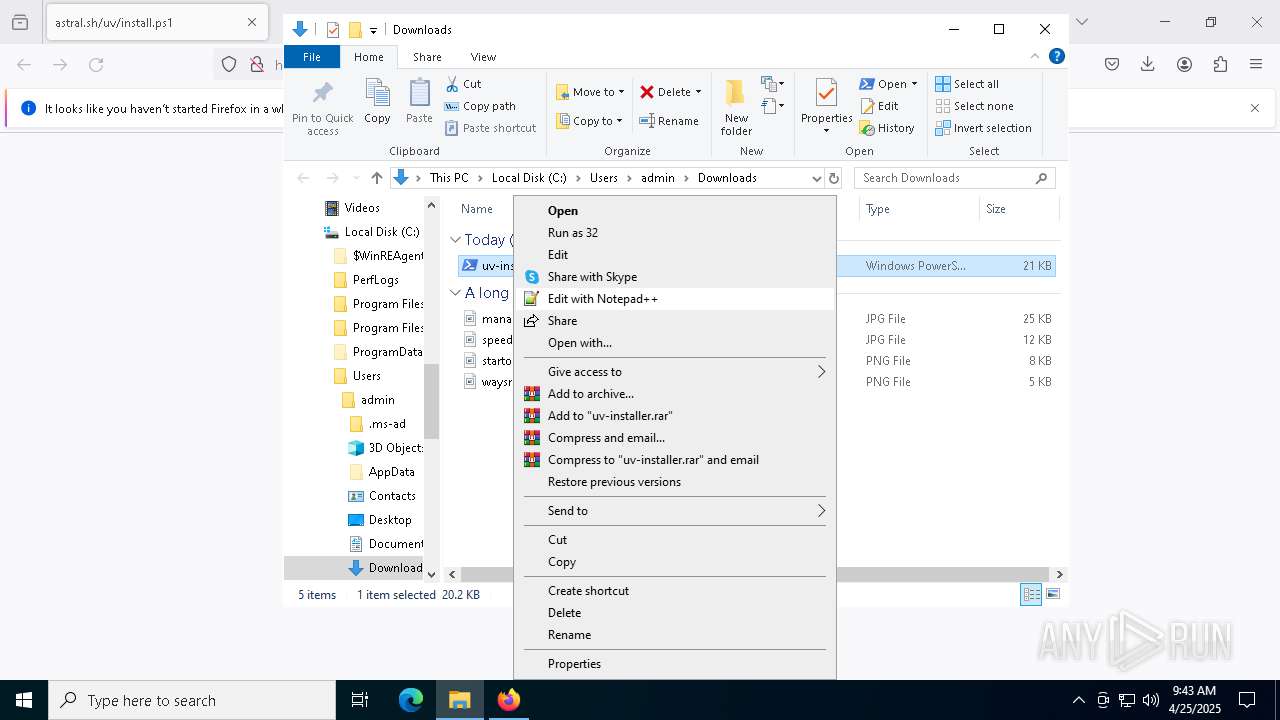
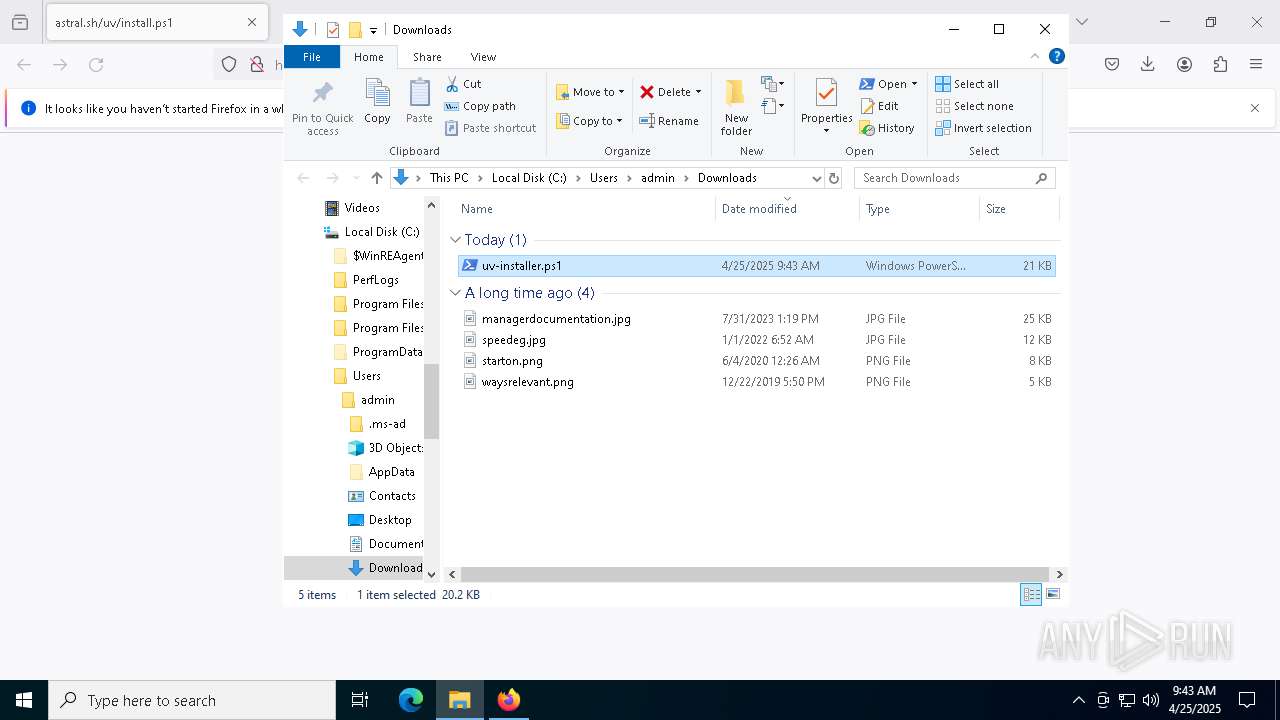
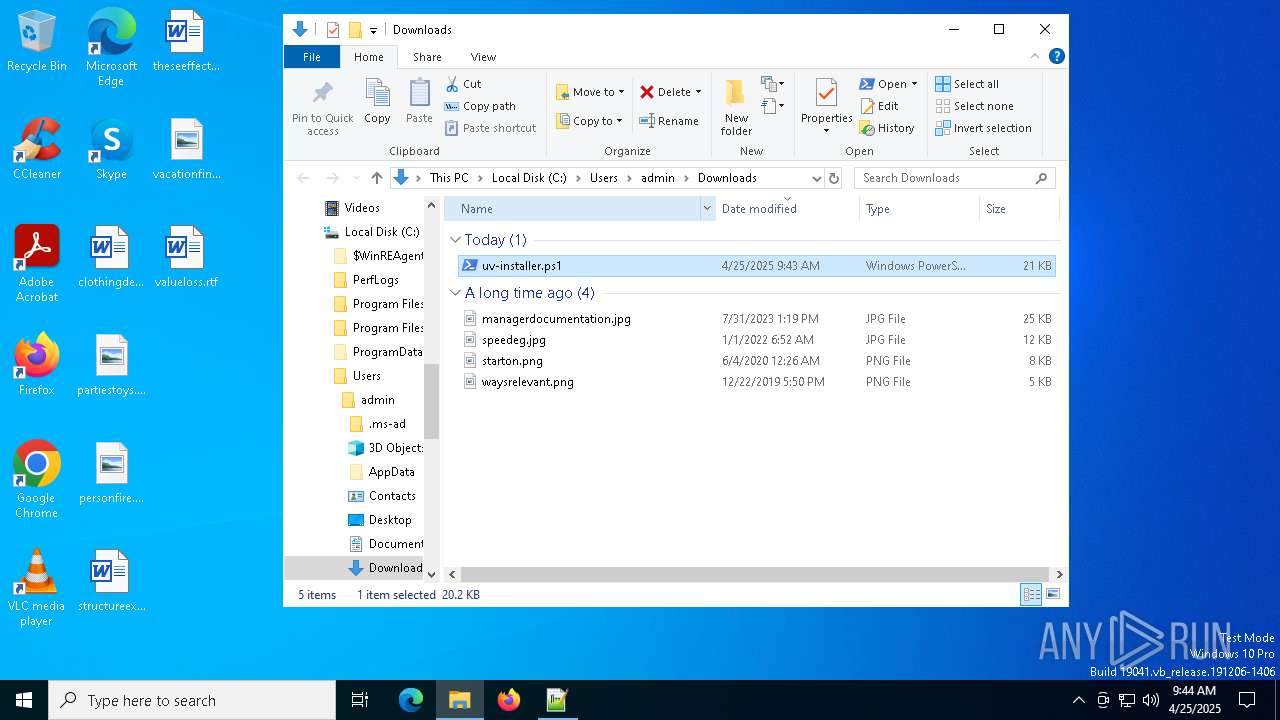
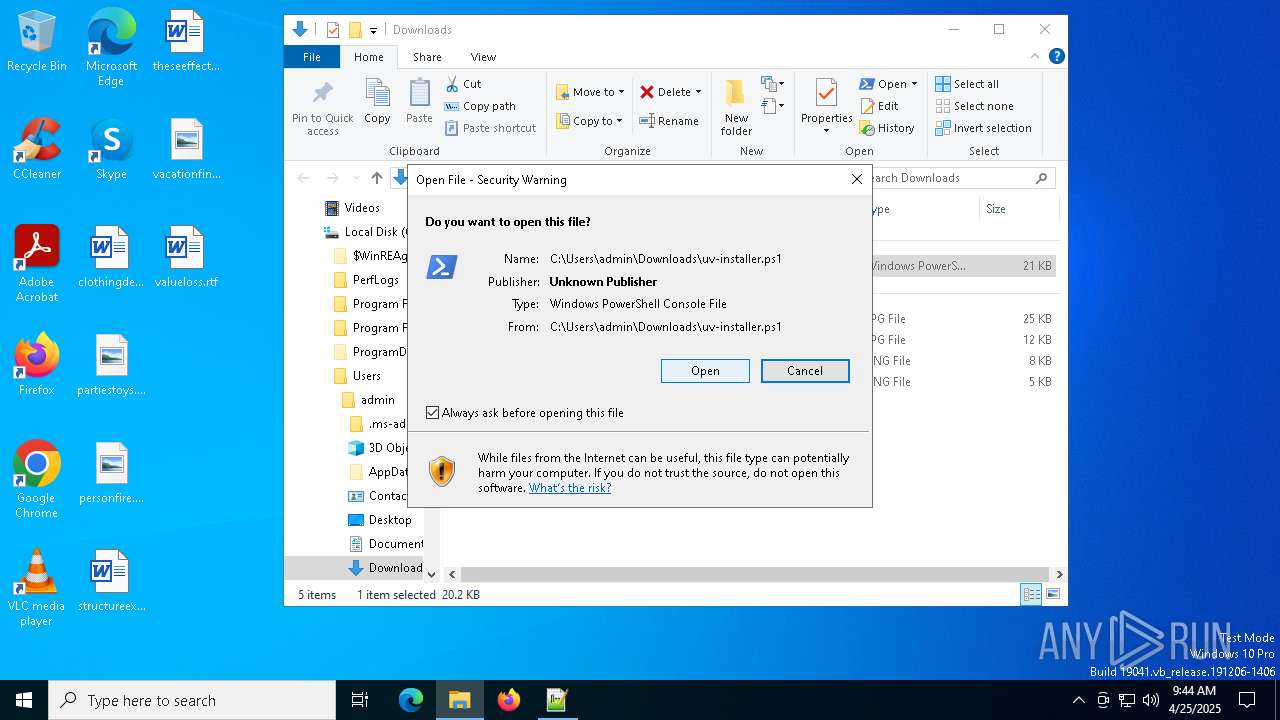
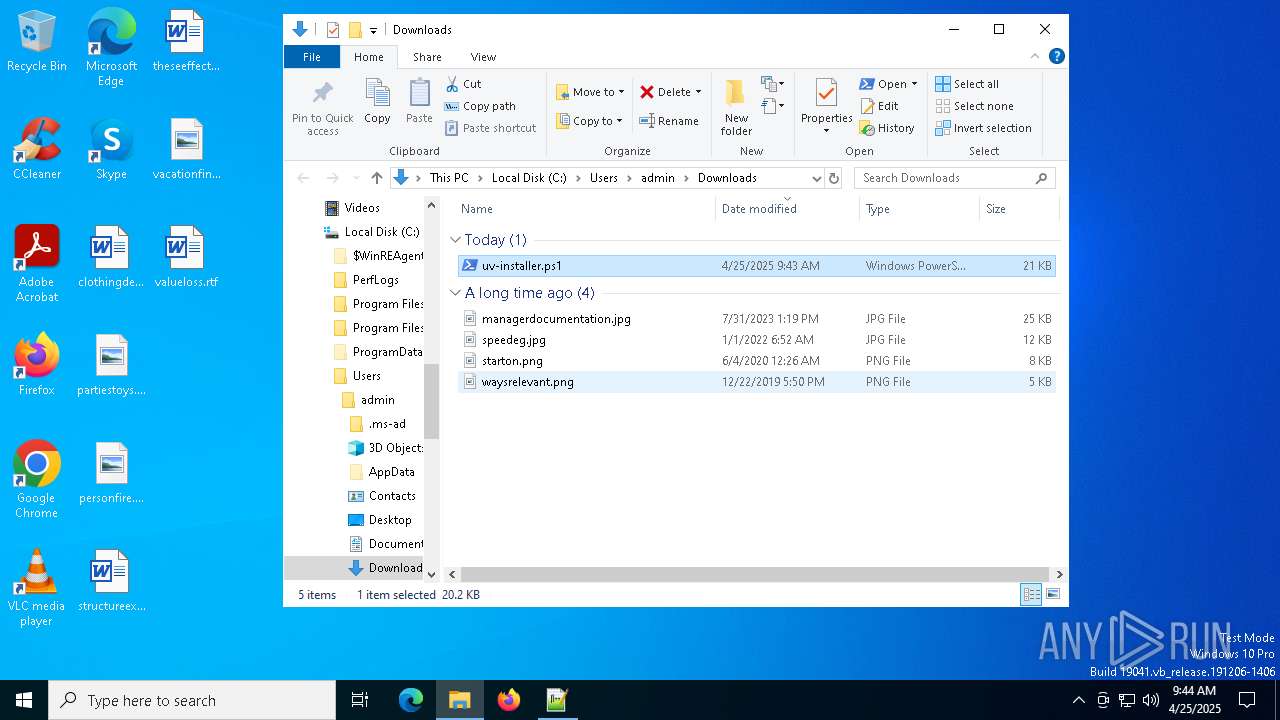
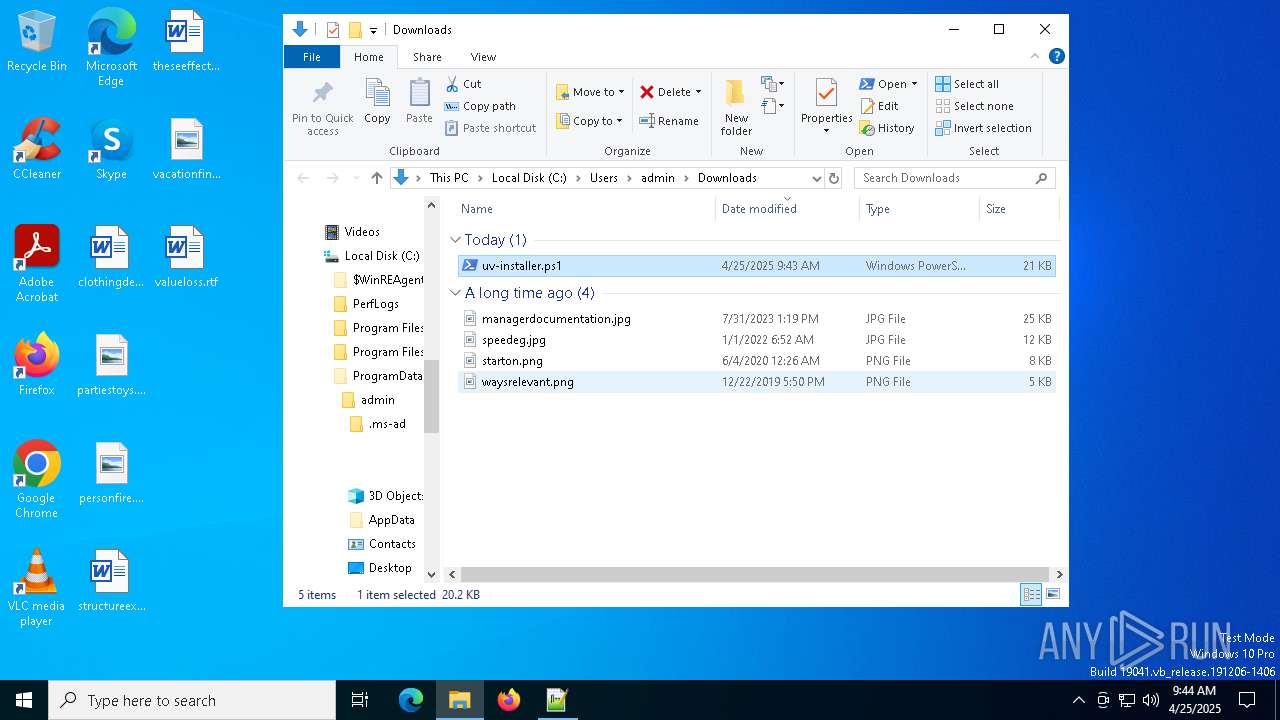
Manual execution by a user
- notepad++.exe (PID: 1328)
- powershell.exe (PID: 6132)
Disables trace logs
- powershell.exe (PID: 6132)
Checks proxy server information
- powershell.exe (PID: 6132)
- slui.exe (PID: 1676)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6132)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6132)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6132)
Reads the software policy settings
- slui.exe (PID: 7844)
- slui.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
159
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://astral.sh/uv/install.ps1" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\uv-installer.ps1" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 1676 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://astral.sh/uv/install.ps1 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4976 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1836 -parentBuildID 20240213221259 -prefsHandle 1764 -prefMapHandle 1756 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {223ea45f-6346-4dd9-bee6-6d51c6f541ec} 4944 "\\.\pipe\gecko-crash-server-pipe.4944" 21fb56ece10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 6132 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Downloads\uv-installer.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6872 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7152 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2096 -parentBuildID 20240213221259 -prefsHandle 2088 -prefMapHandle 2076 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b684eb6b-b8b3-42e0-9813-bf840f14ed51} 4944 "\\.\pipe\gecko-crash-server-pipe.4944" 21fa977f910 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 7372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 286
Read events
21 282
Write events
3
Delete events
1
Modification events
| (PID) Process: | (4944) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
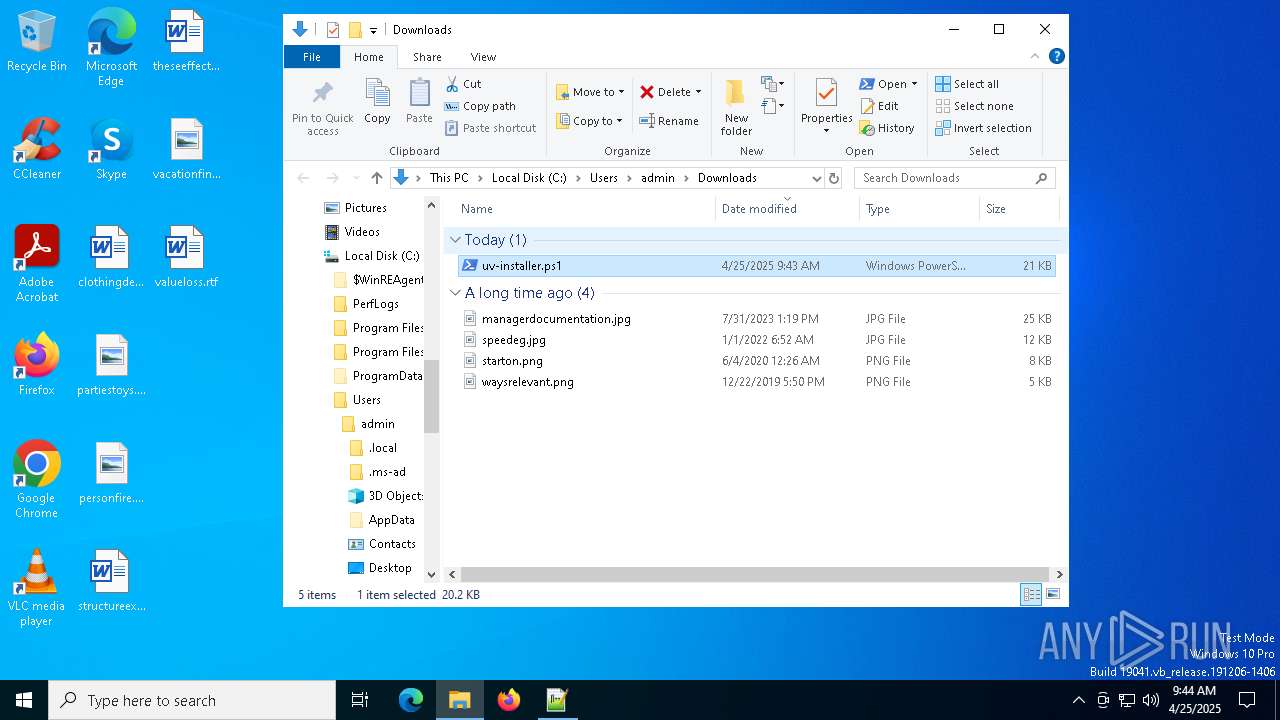
| (PID) Process: | (6132) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\.local\bin;%USERPROFILE%\AppData\Local\Microsoft\WindowsApps | |||
| (PID) Process: | (6132) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | cargo-dist-cba00530-ca6d-4084-98f0-98461d749337 |
Value: cargo-dist-dummy | |||
| (PID) Process: | (6132) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | delete value | Name: | cargo-dist-cba00530-ca6d-4084-98f0-98461d749337 |
Value: cargo-dist-dummy | |||
Executable files
2
Suspicious files
162
Text files
27
Unknown types
0
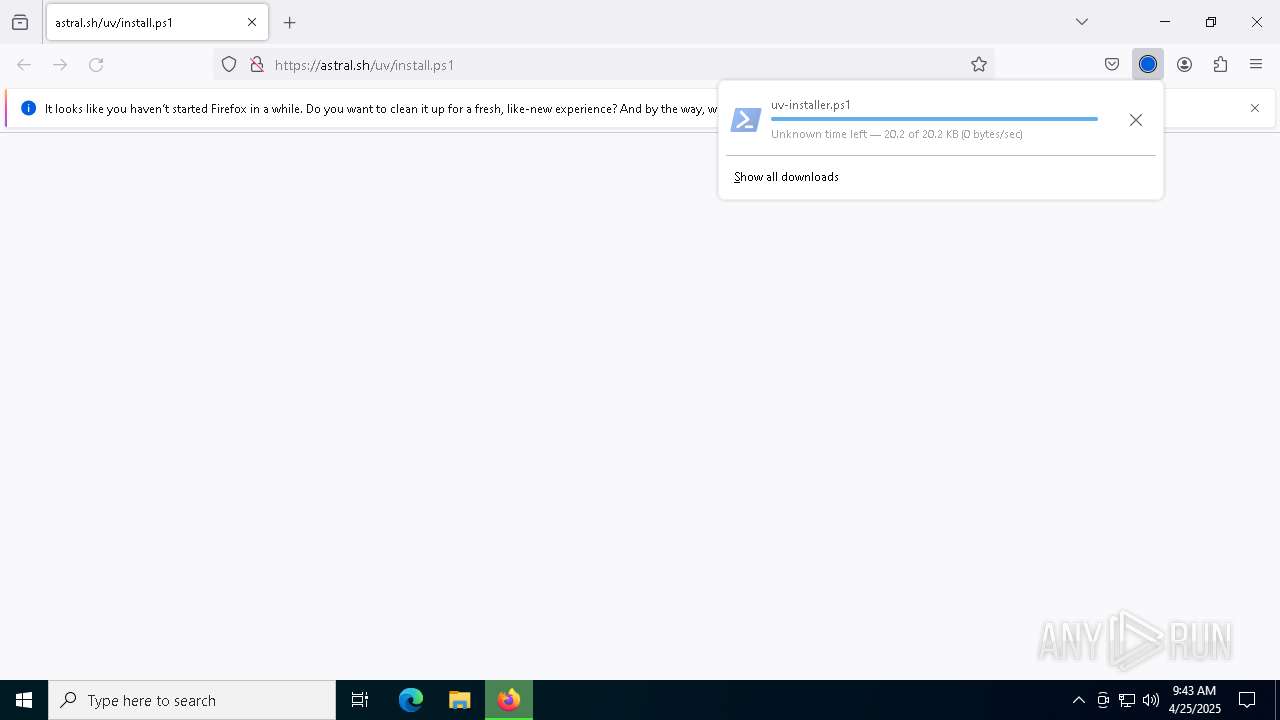
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:3096E71D8CCCD8B37ECF9607595C5431 | SHA256:BFDCC90F03F23F12436955463579FBCDF36DBB791C9C73CB597819527A429790 | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4944 | firefox.exe | C:\Users\admin\Downloads\uv-installer.xXoA0oZb.ps1.part | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
83
DNS requests
100
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.34.33:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4944 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4944 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4944 | firefox.exe | POST | 200 | 92.122.244.51:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
4944 | firefox.exe | POST | 200 | 92.122.244.51:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
4944 | firefox.exe | POST | — | 142.250.186.163:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
4944 | firefox.exe | POST | 200 | 92.122.244.32:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
4944 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
4944 | firefox.exe | POST | 200 | 92.122.244.32:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 95.101.34.33:80 | crl.microsoft.com | Akamai International B.V. | IT | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4944 | firefox.exe | 104.21.68.235:443 | astral.sh | CLOUDFLARENET | — | unknown |
4944 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
4944 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
astral.sh |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |