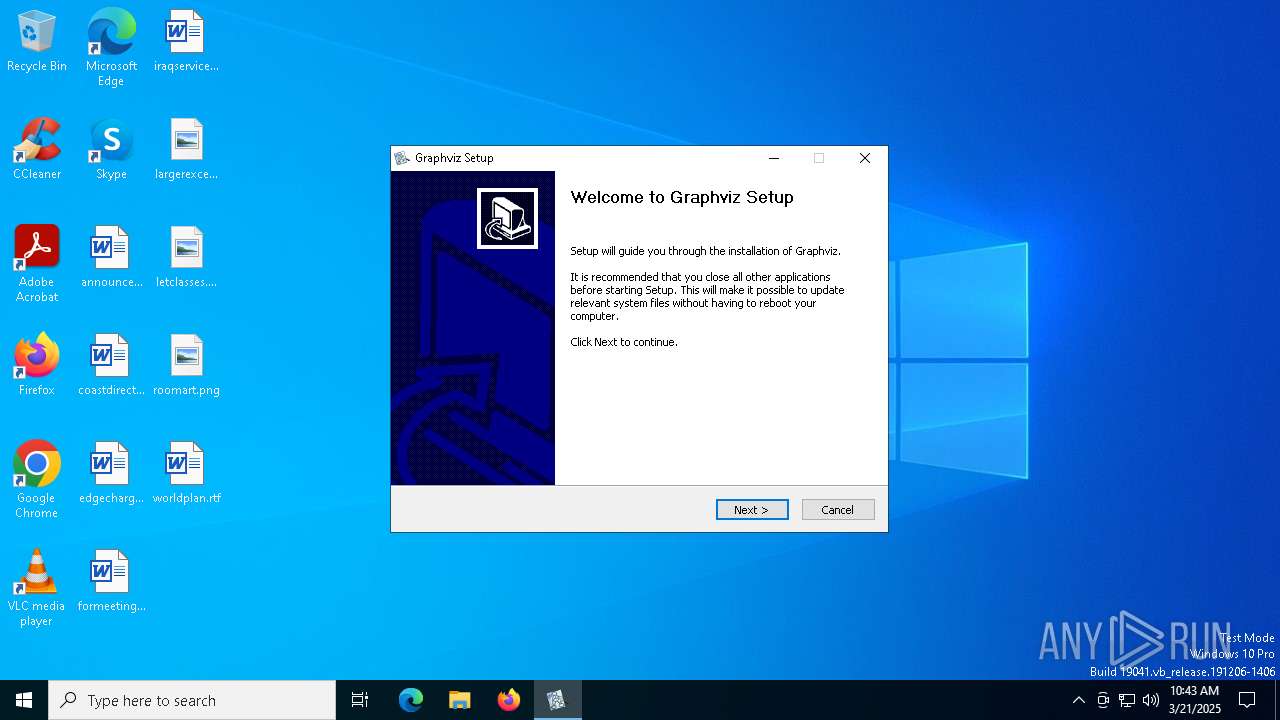
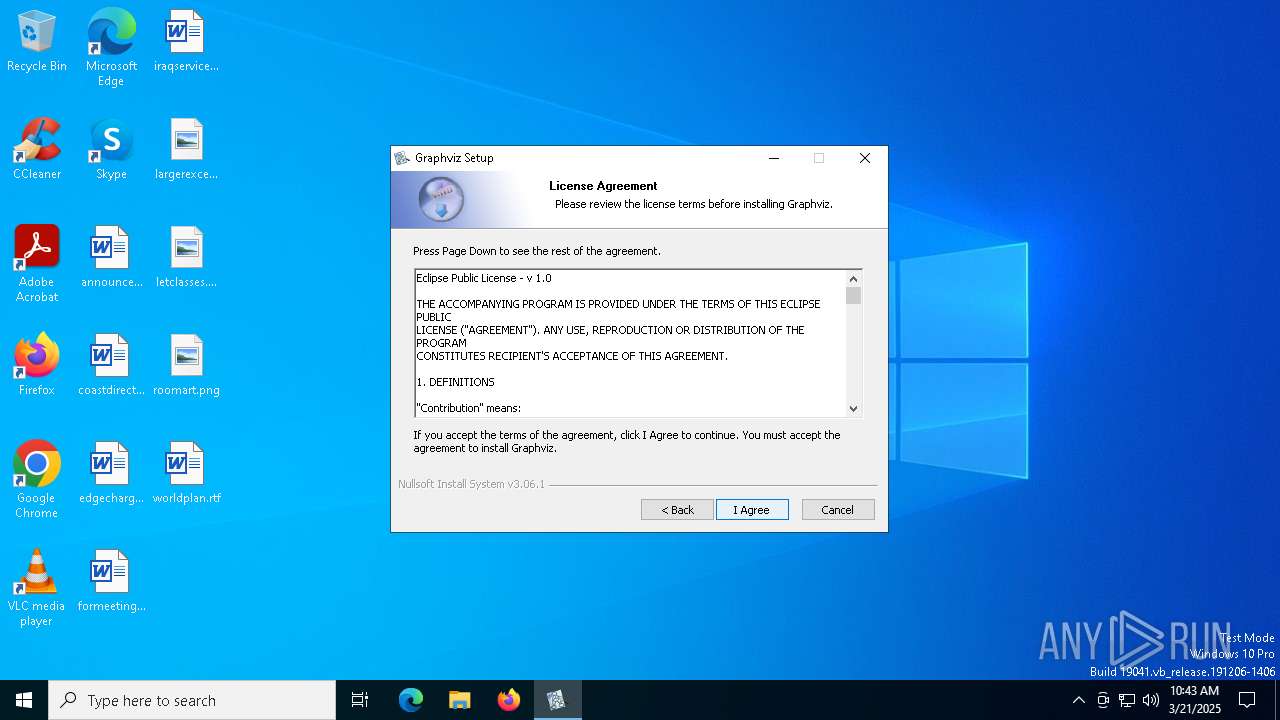
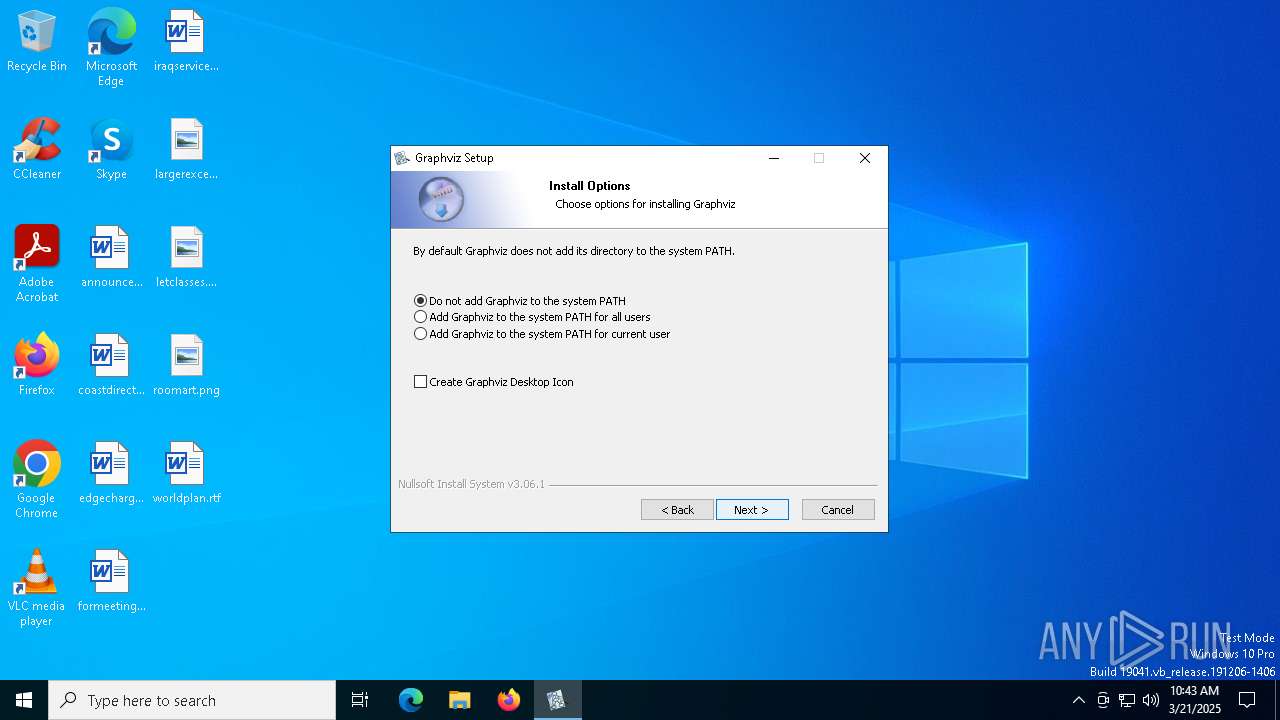
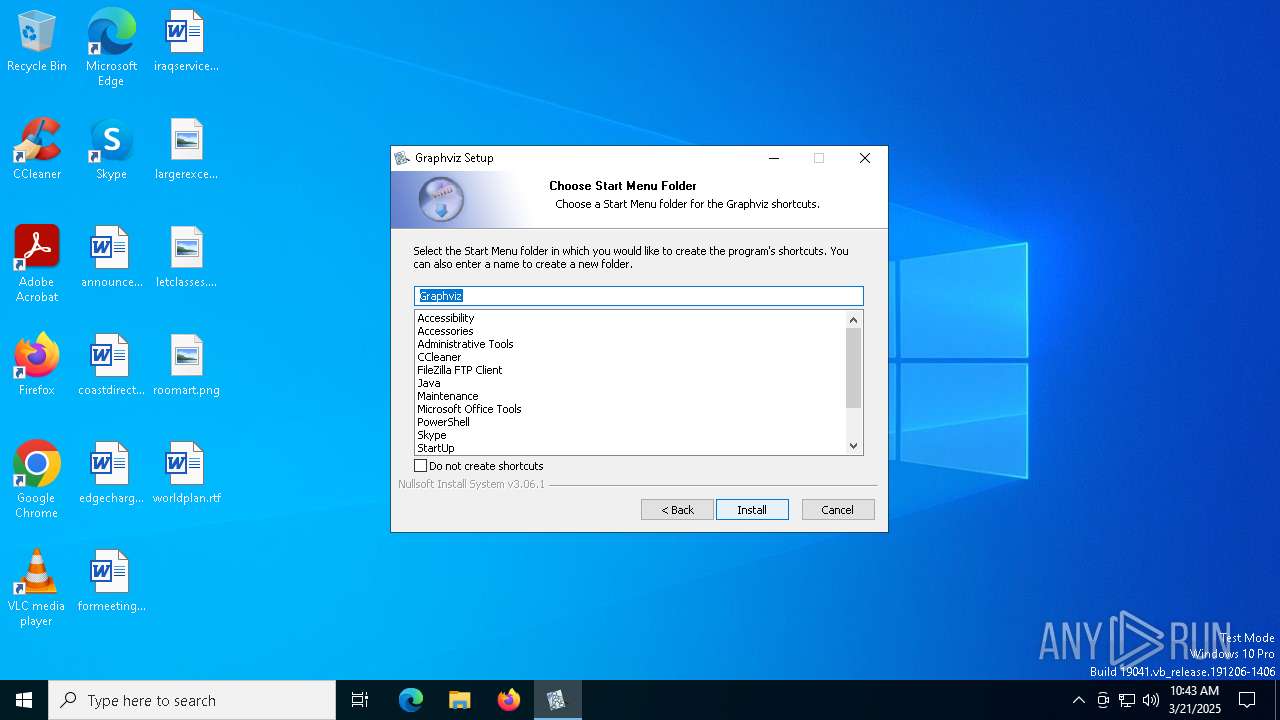
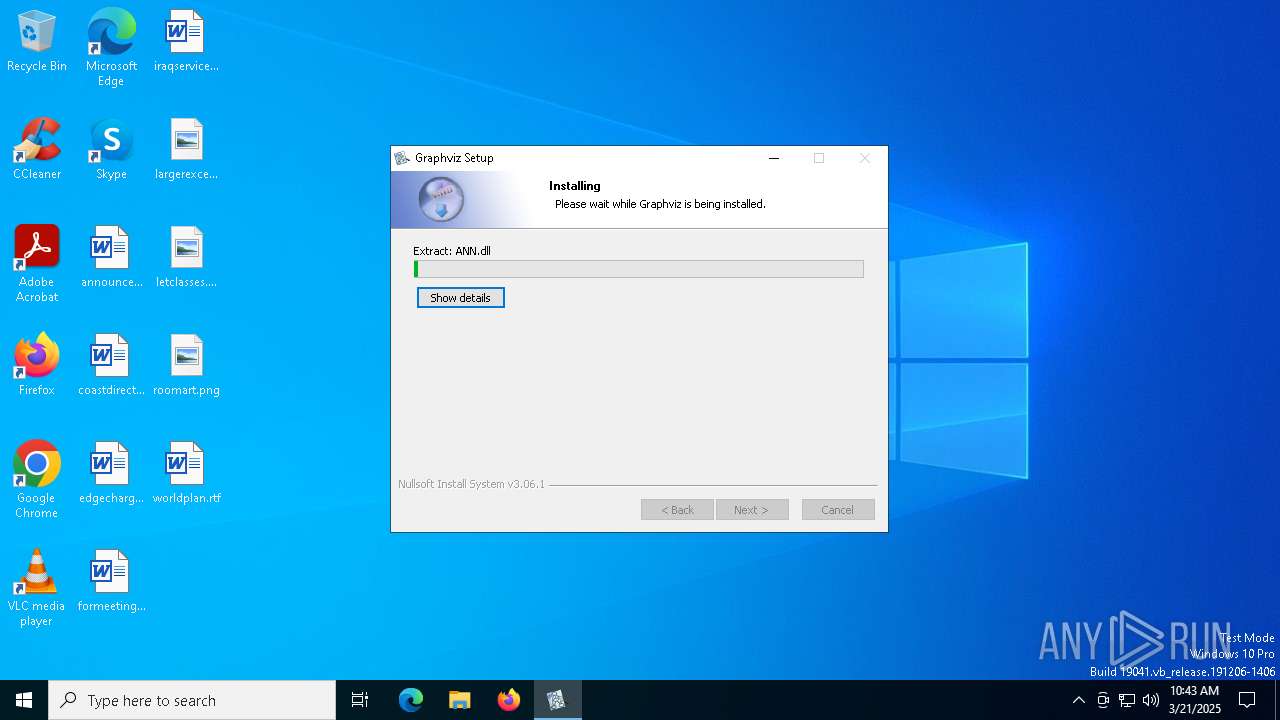
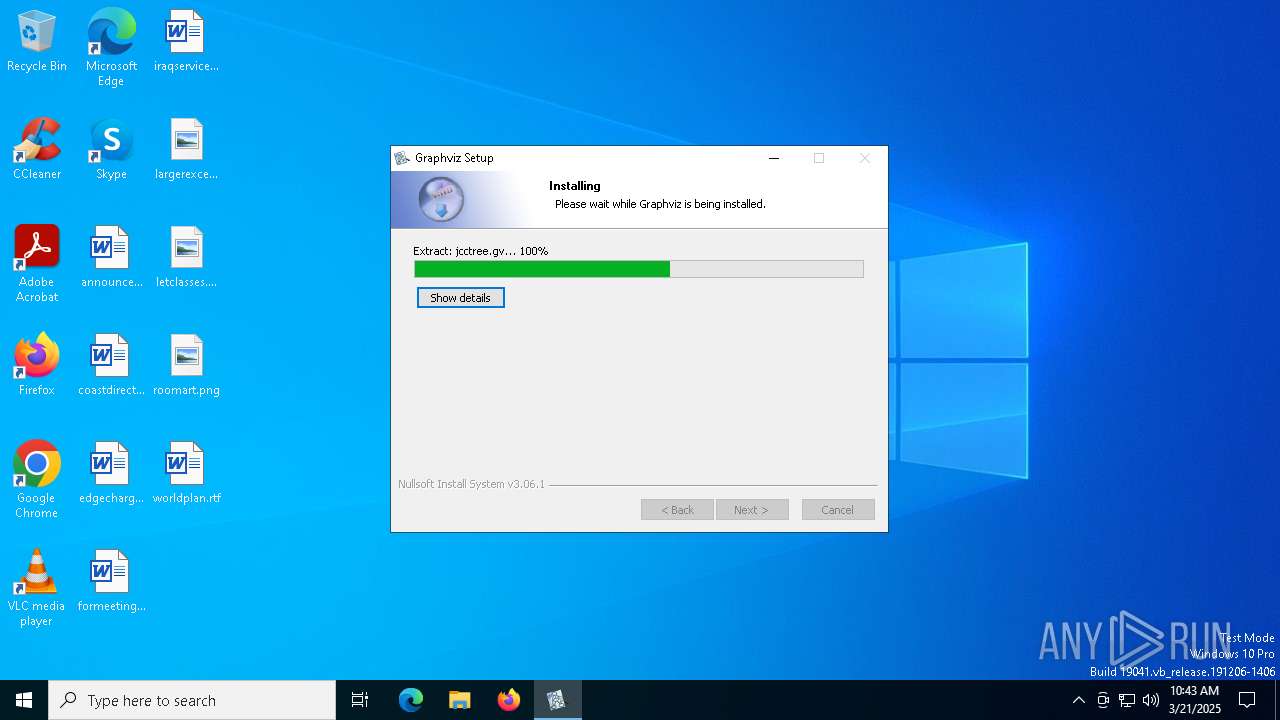
| File name: | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe |
| Full analysis: | https://app.any.run/tasks/8a15fd0c-58b4-4358-b4d8-dc0d1f2a2d92 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2025, 10:43:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 83D886ABB9C200CCD44F0ECD904DA0CD |
| SHA1: | 71BA4F5E2E506109DBEF840405E8F9ED4F83AC6D |
| SHA256: | 6809D0095919844A6C557092D2005605450D8AD2EF69ED89D7BC3EE791B6F9DA |
| SSDEEP: | 98304:sI8nj8Kaoll8QycJHQfLjNT6NirvTABuwWEuW8+tPVdws/izqOhw3+B1PdIGSwWg:ze01yk7xBe2fnk6f |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
The process drops C-runtime libraries
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Creates a software uninstall entry
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Malware-specific behavior (creating "System.dll" in Temp)
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Process drops legitimate windows executable
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
The process creates files with name similar to system file names
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
There is functionality for taking screenshot (YARA)
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
INFO
Reads the computer name
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Create files in a temporary directory
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Checks supported languages
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
The sample compiled with english language support
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Creates files in the program directory
- windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe (PID: 6388)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:01 02:53:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 262144 |
| UninitializedDataSize: | 8192 |
| EntryPoint: | 0x3312 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5324 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6068 | "C:\Users\admin\AppData\Local\Temp\windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe" | C:\Users\admin\AppData\Local\Temp\windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6388 | "C:\Users\admin\AppData\Local\Temp\windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe" | C:\Users\admin\AppData\Local\Temp\windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6712 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 826
Read events
1 796
Write events
30
Delete events
0
Modification events
| (PID) Process: | (664) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (664) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (664) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1128) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1128) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1128) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5324) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5324) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5324) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6712) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
105
Suspicious files
25
Text files
135
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1128 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\5b5289f9-8c40-481c-8ebf-daed31511cf5.down_data | — | |
MD5:— | SHA256:— | |||
| 6388 | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsrBA0C.tmp\NSIS.InstallOptions.ini | text | |
MD5:7DB6AE6FB6E11CE14465C21470CC5080 | SHA256:F9E0B0FCD3CF9DFABEE7F9A7542E3831D22F49312584088516402A420F19AE84 | |||
| 1128 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\6f516694-3651-482d-9584-ae76e4c1127d.up_meta_secure | binary | |
MD5:67E8A42147AA92EF118818F1A05CA513 | SHA256:FDE2E2BFB72890DB001A336C04517A8B13CE1E3BE5984B707B26387658903901 | |||
| 6388 | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsrBA0C.tmp\InstallOptions.dll | executable | |
MD5:5F35212D7E90EE622B10BE39B09BD270 | SHA256:31944B93E44301974D9C6F810D2DA792E34A53DCACD619A08CB0385AC59E513D | |||
| 6388 | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | C:\Program Files\Graphviz\bin\acyclic.exe | executable | |
MD5:4CF5E3A4AD5B325FE405C8A1C82A0C0E | SHA256:7B80CD01E76767FB75692C748C3CC00136E965EE6E8D55E1DF6C467F7D551D73 | |||
| 1128 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\5b5289f9-8c40-481c-8ebf-daed31511cf5.68f25e6c-1758-4cfc-8c29-59f1a43c7bbc.down_meta | binary | |
MD5:71E19340EC59E715E3806F234CCEF142 | SHA256:380ABCC44E200357ABB06A029D7BF383E631FD015E67A65C6C70FF56851246A0 | |||
| 6388 | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsrBA0C.tmp\modern-header.bmp | image | |
MD5:940C56737BF9BB69CE7A31C623D4E87A | SHA256:766A893FE962AEFD27C574CB05F25CF895D3FC70A00DB5A6FA73D573F571AEFC | |||
| 1128 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:B97E400964900BC2D8274B887D5AA1F4 | SHA256:9EE0020FE1FECDEEE0309A80F5EB6BC02AF0793E11C4A230C7931D4C6BC662ED | |||
| 6388 | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | C:\Program Files\Graphviz\bin\bz2.dll | executable | |
MD5:DC3AEE8E0253B90330235EE20EFC8961 | SHA256:85E3BE4D6BCBD3685B1A5362100CE8F907E9FE9DC92D6FA53703A8DA9ACA5CFF | |||
| 6388 | windows_10_cmake_Release_graphviz-install-12.2.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsrBA0C.tmp\StartMenu.dll | executable | |
MD5:26836307758E048D1CE0AFE754D6A972 | SHA256:A6919F5F3B53A9C8C015413BABE7A9872491A2583E49BB3C261E60785C3C3534 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1128 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5800 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6592 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6592 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5800 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |