| File name: | OInstall.exe |
| Full analysis: | https://app.any.run/tasks/12361bb7-6eb2-4b09-99be-958fcf00c88b |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2020, 10:05:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 4C506F1B0E46ED1442EB0CAEB2812244 |
| SHA1: | 0E30EBB3E77B976CBEEAFC6CA93582BAE629CA44 |
| SHA256: | 6808EE2072914FC368B6027A3C7966A969704559DF7C47C6191941825DD37B70 |
| SSDEEP: | 196608:oQ5r7OVbShX98QUYWFUrXxuKp4dEOWwx+mDyJ3VAn0viePKMdN1Q547ittEZ5b:l52bSHUYlj0Kp+xOFA/uKMfE47ikz |
MALICIOUS
Loads dropped or rewritten executable
- OfficeClickToRun.exe (PID: 1332)
- OfficeClickToRun.exe (PID: 3100)
- SearchProtocolHost.exe (PID: 3548)
- OfficeC2RClient.exe (PID: 3552)
Application was dropped or rewritten from another process
- setup.exe (PID: 1632)
- OfficeClickToRun.exe (PID: 3100)
- OfficeClickToRun.exe (PID: 1332)
- OfficeC2RClient.exe (PID: 3552)
Changes settings of System certificates
- setup.exe (PID: 1632)
SUSPICIOUS
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 3972)
Executable content was dropped or overwritten
- OfficeClickToRun.exe (PID: 1332)
- files.dat (PID: 3428)
- OInstall.exe (PID: 3972)
- OfficeClickToRun.exe (PID: 3100)
- setup.exe (PID: 1632)
Creates files in the user directory
- powershell.exe (PID: 2208)
Executed as Windows Service
- OfficeClickToRun.exe (PID: 3100)
Executes PowerShell scripts
- setup.exe (PID: 1632)
Starts application with an unusual extension
- cmd.exe (PID: 2352)
Reads Internet Cache Settings
- setup.exe (PID: 1632)
- OfficeClickToRun.exe (PID: 1332)
- OfficeC2RClient.exe (PID: 3552)
Searches for installed software
- setup.exe (PID: 1632)
Creates files in the Windows directory
- OfficeClickToRun.exe (PID: 3100)
Creates files in the program directory
- OfficeClickToRun.exe (PID: 3100)
- setup.exe (PID: 1632)
Removes files from Windows directory
- OfficeClickToRun.exe (PID: 3100)
Adds / modifies Windows certificates
- setup.exe (PID: 1632)
INFO
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 1332)
- OfficeC2RClient.exe (PID: 3552)
- OfficeClickToRun.exe (PID: 3100)
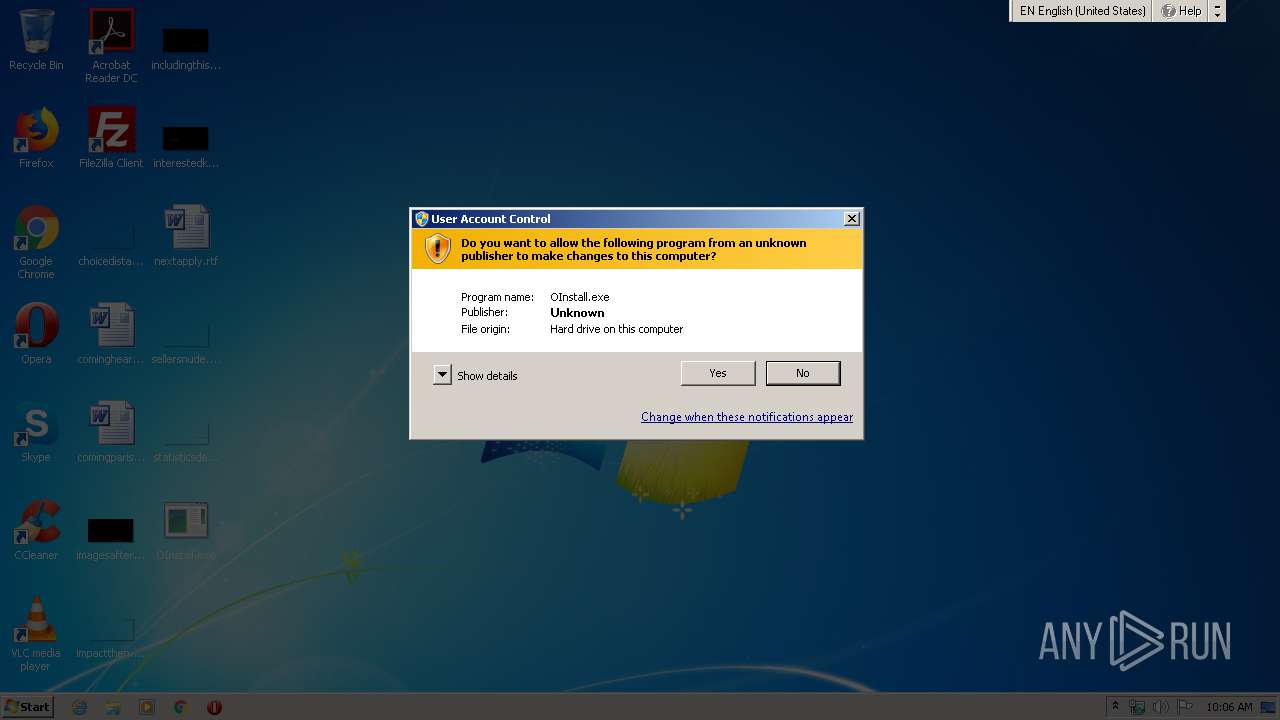
Manual execution by user
- OfficeC2RClient.exe (PID: 3552)
Reads settings of System Certificates
- setup.exe (PID: 1632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:21 00:12:09+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 9740288 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 10829824 |
| EntryPoint: | 0x139e7b0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.4.0 |
| ProductVersionNumber: | 7.0.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
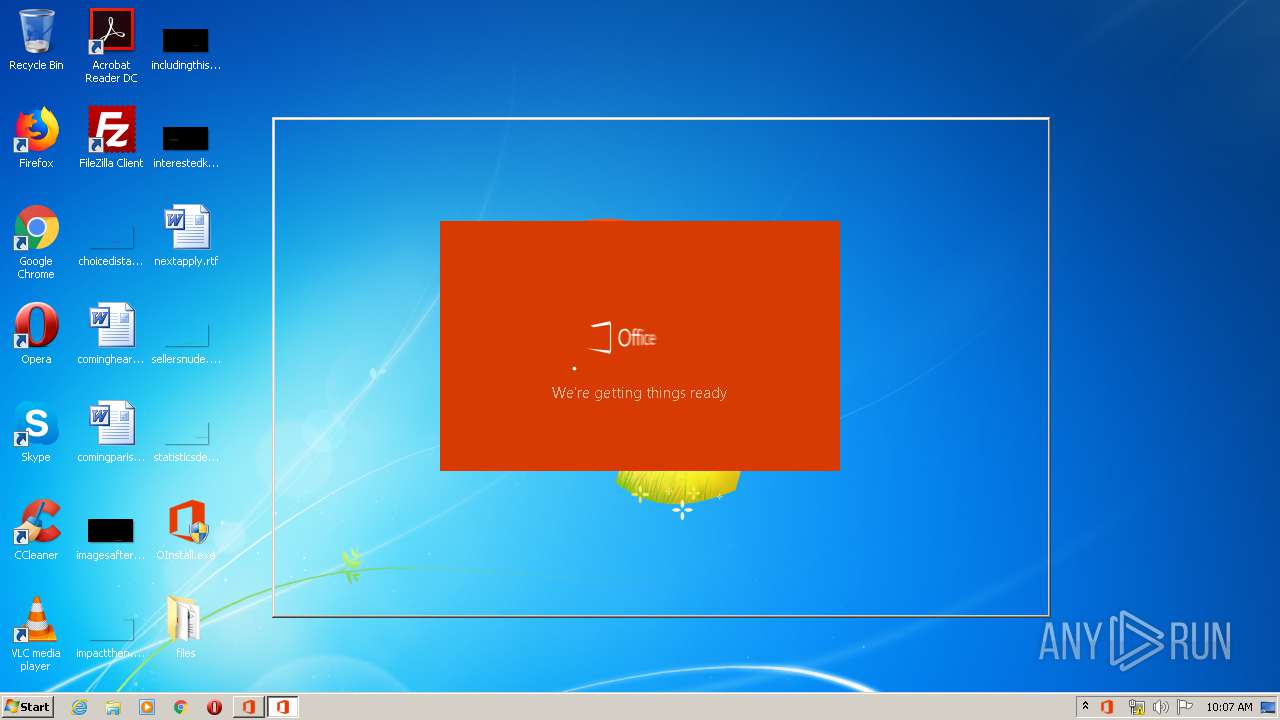
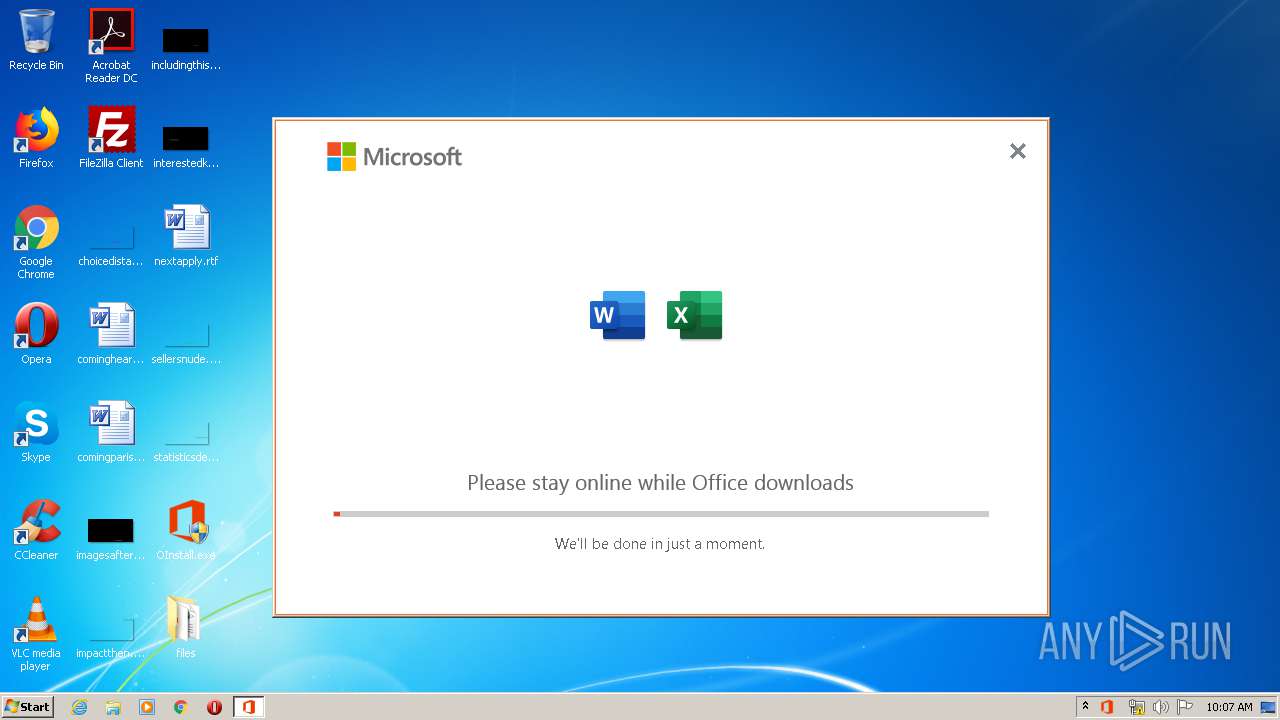
| ProductName: | Office 2013-2019 C2R Install |
| FileDescription: | Office 2013-2019 C2R Install |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jan-2020 23:12:09 |
| Detected languages: |
|
| ProductName: | Office 2013-2019 C2R Install |
| FileDescription: | Office 2013-2019 C2R Install |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Jan-2020 23:12:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00A54000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00A55000 | 0x0094A000 | 0x00949A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89625 |
.rsrc | 0x0139F000 | 0x00016000 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.96712 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
55
Monitored processes
12
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1332 | deliverymechanism=492350f6-3a01-4f97-b9c0-c7c6ddf67d60 platform=x86 productreleaseid=none forcecentcheck= culture=en-us defaultplatform=False storeid= lcid=1033 b= totalclientcabsize=21061894 productstoadd=ProplusRetail.16_en-us_x-none scenariosubtype=ODT scenario=unknown updatesenabled.16=True acceptalleulas.16=True cdnbaseurl.16=http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 version.16=16.0.12325.20344 mediatype.16=CDN proplusretail.excludedapps.16=access,publisher,groove,lync,onenote,outlook,powerpoint,onedrive baseurl.16=http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 sourcetype.16=CDN flt.useexptransportinplacepl=unknown flt.useoutlookshareaddon=unknown flt.useofficehelperaddon=unknown flt.usebingaddononinstall=unknown flt.usebingaddononupdate=unknown | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Click-to-Run (SxS) Exit code: 0 Version: 16.0.12325.20280 Modules
| |||||||||||||||
| 1632 | C:\Users\admin\Desktop\files\Setup.exe /configure Configure.xml | C:\Users\admin\Desktop\files\setup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Exit code: 0 Version: 16.0.12325.20276 Modules
| |||||||||||||||
| 2208 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile "$package = Get-AppxPackage Microsoft.Office.Desktop -allUsers; if (!$package) { $Error.Add(\"Package is not installed\")}; if ($error.Count -eq 0) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '1' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '0' -Encoding ascii; Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch' -InputObject $error -Encoding ascii;} " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2352 | "C:\Windows\System32\cmd.exe" /D /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\Desktop\OInstall.exe" | C:\Users\admin\Desktop\OInstall.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Office 2013-2019 C2R Install Exit code: 3221226540 Modules
| |||||||||||||||
| 3040 | "C:\Windows\System32\cmd.exe" /D /c C:\Users\admin\Desktop\files\Setup.exe /configure Configure.xml | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3044 | "C:\Windows\System32\cmd.exe" /D /c copy C:\Windows\system32\Tasks\OInstall "C:\Windows\Temp\OInstall.tmp" /Y | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3100 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Exit code: 0 Version: 16.0.12325.20280 Modules
| |||||||||||||||
| 3428 | files.dat -y -pkmsauto | C:\Users\admin\Desktop\files\files.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 439
Read events
1 497
Write events
1 942
Delete events
0
Modification events
| (PID) Process: | (3548) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3548) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
| (PID) Process: | (3972) OInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\Experiment\officeclicktorun |
| Operation: | write | Name: | FirstSessionTriggered |
Value: 1 | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | UIFallbackLanguages |
Value: x-none | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | HelpLanguageTag |
Value: en-US | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreviousPreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (1632) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordMailChangeInstallLanguage |
Value: No | |||
Executable files
197
Suspicious files
23
Text files
31
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | OInstall.exe | C:\Users\admin\Desktop\files\files.dat | — | |
MD5:— | SHA256:— | |||
| 1632 | setup.exe | C:\Users\admin\AppData\Local\Temp\CabF545.tmp | — | |
MD5:— | SHA256:— | |||
| 1632 | setup.exe | C:\Users\admin\AppData\Local\Temp\TarF546.tmp | — | |
MD5:— | SHA256:— | |||
| 1632 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2RDB0510C4-A8CF-4F98-9A28-0BA7BD3E4064OfficeC2R8C0AC3AA-EE39-42DC-8603-515F34416DAD\v32.hash | — | |
MD5:— | SHA256:— | |||
| 1632 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2RDB0510C4-A8CF-4F98-9A28-0BA7BD3E4064OfficeC2R8C0AC3AA-EE39-42DC-8603-515F34416DAD\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 1632 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2RDB0510C4-A8CF-4F98-9A28-0BA7BD3E4064\v32.hash | — | |
MD5:— | SHA256:— | |||
| 1632 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2RDB0510C4-A8CF-4F98-9A28-0BA7BD3E4064\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 2208 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8F05CFQMIHS3TXZ2ELPM.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch | — | |
MD5:— | SHA256:— | |||
| 2208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
19
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1632 | setup.exe | HEAD | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | US | — | — | whitelisted |
1632 | setup.exe | HEAD | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | US | — | — | whitelisted |
— | — | HEAD | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | US | — | — | whitelisted |
— | — | GET | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | US | — | — | whitelisted |
— | — | HEAD | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | US | — | — | whitelisted |
— | — | GET | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | US | — | — | whitelisted |
— | — | HEAD | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.12325.20344/i320.cab | US | — | — | whitelisted |
1632 | setup.exe | HEAD | 200 | 2.20.188.35:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | unknown | — | — | whitelisted |
— | — | GET | 301 | 72.247.224.69:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.12325.20344/i320.cab | US | — | — | whitelisted |
— | — | HEAD | 200 | 2.20.188.35:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12325.20344.cab | unknown | binary | 1 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1632 | setup.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
1632 | setup.exe | 52.109.88.44:443 | mrodevicemgr.officeapps.live.com | Microsoft Corporation | NL | whitelisted |
1632 | setup.exe | 72.247.224.69:80 | officecdn.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
— | — | 72.247.224.69:80 | officecdn.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
1632 | setup.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
1632 | setup.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
3100 | OfficeClickToRun.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3100 | OfficeClickToRun.exe | 72.247.224.69:80 | officecdn.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
3100 | OfficeClickToRun.exe | 2.20.188.52:80 | officecdn.microsoft.com.edgesuite.net | Akamai International B.V. | — | unknown |
3100 | OfficeClickToRun.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
mrodevicemgr.officeapps.live.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |