| File name: | 3389E.exe |
| Full analysis: | https://app.any.run/tasks/f0733829-4a82-4c8d-a828-4528ad66c595 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2020, 11:02:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
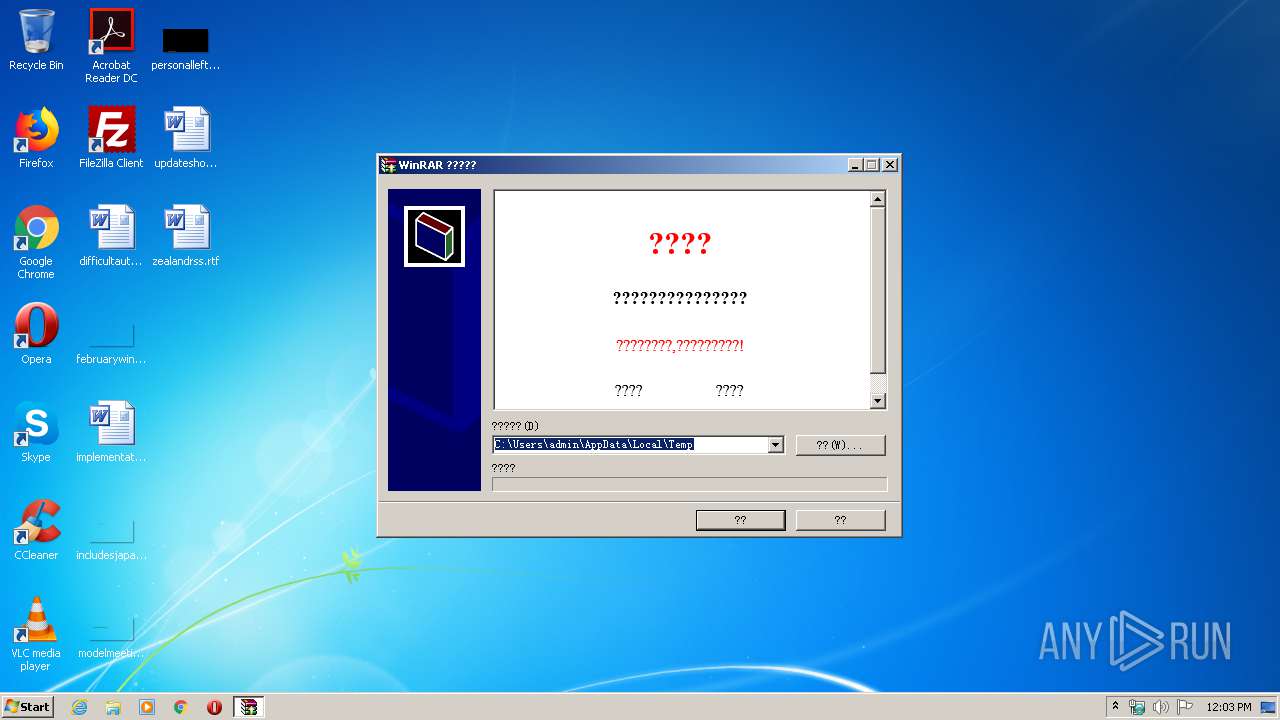
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 1A5D734EF5E3450239826EFA820BFFFE |
| SHA1: | 3D551BAA0ECEA18EB7340B2FE0021FE356486931 |
| SHA256: | 67F8B3795EC46A26F82931AD68B0ED4B30BC73892190A4B189CFF56730BE906F |
| SSDEEP: | 24576:szYXUSEN6FHLHNb7l+dpaYM7K1g71Mq4eTSy4q4cAISyiZ6newCLRxrO+pWsZ:FkSENUHLHNh+Dar7KVqPL4jT9ZCePDpF |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- 3389E.exe (PID: 3292)
Executable content was dropped or overwritten
- 3389E.exe (PID: 3292)
Executed via COM
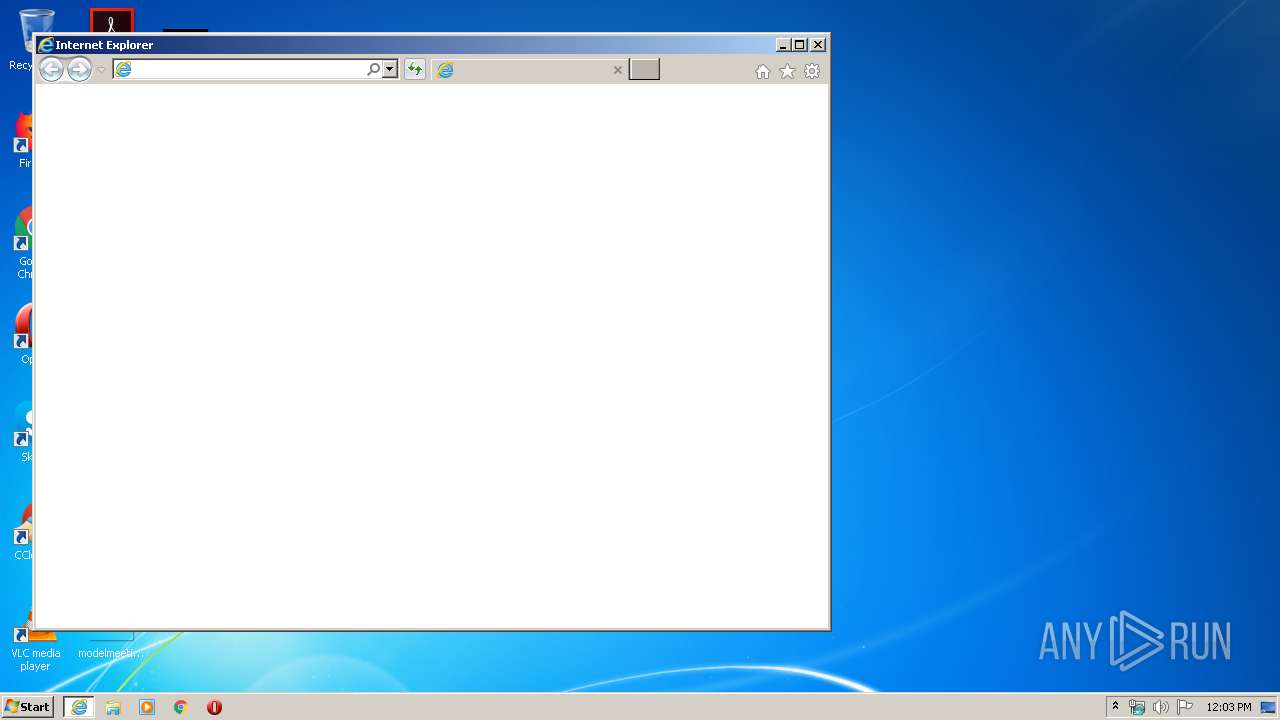
- iexplore.exe (PID: 2828)
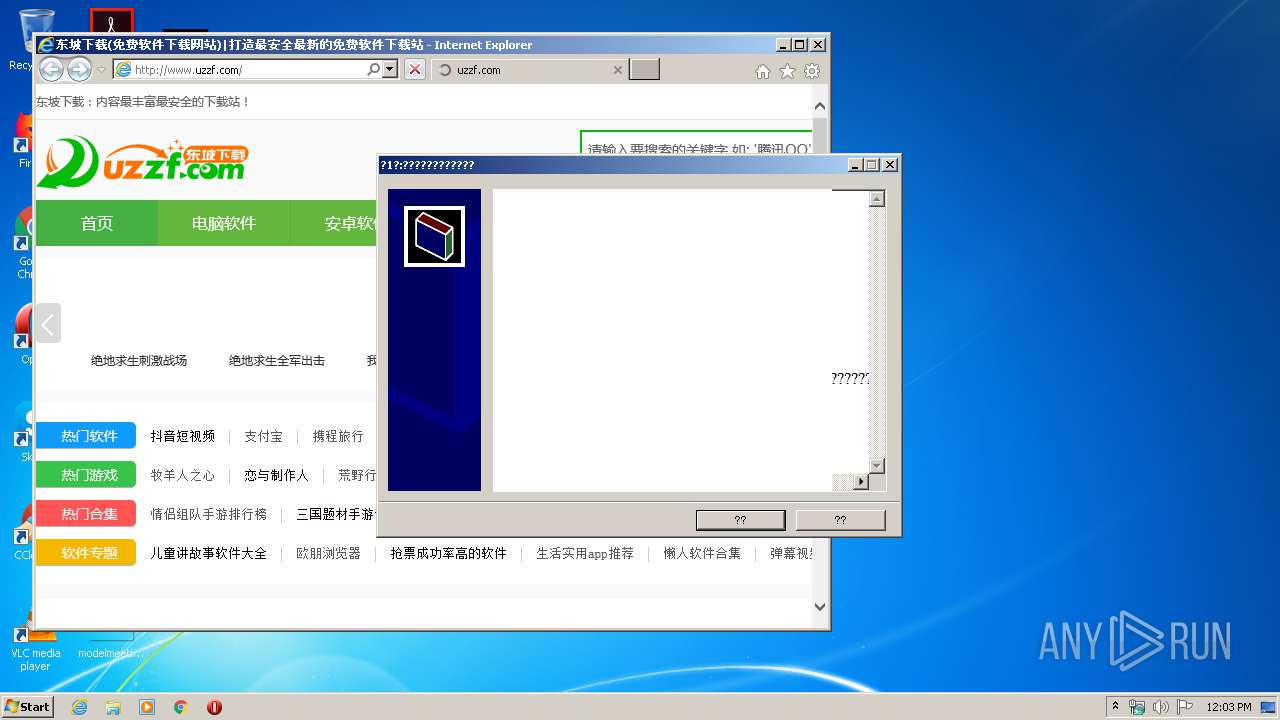
Starts Internet Explorer
- 3389E.exe (PID: 3292)
Reads internet explorer settings
- 3389E.exe (PID: 3292)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 3624)
Application launched itself
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 3624)
Reads Internet Cache Settings
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 3624)
- iexplore.exe (PID: 3740)
Reads internet explorer settings
- iexplore.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:12:03 10:53:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 19456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Dec-2006 09:53:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Dec-2006 09:53:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013000 | 0x00012E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45753 |
.data | 0x00014000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.76078 |
.idata | 0x0001B000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11047 |
.rsrc | 0x0001C000 | 0x000031E4 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14689 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10885 | 531 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 3.88998 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.31352 | 226 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.70413 | 360 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.51373 | 216 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 4.80037 | 420 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
100 | 2.6902 | 62 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
46
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2808 | "C:\Users\admin\AppData\Local\Temp\3389E.exe" | C:\Users\admin\AppData\Local\Temp\3389E.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 2828 | "C:\Program Files\Internet Explorer\iexplore.exe" -startmediumtab -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2828 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3292 | "C:\Users\admin\AppData\Local\Temp\3389E.exe" | C:\Users\admin\AppData\Local\Temp\3389E.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3624 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.xueshangwang.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | 3389E.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3624 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
558
Read events
444
Write events
109
Delete events
5
Modification events
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A2000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3292) 3389E.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2031858132 | |||
| (PID) Process: | (2828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30811633 | |||
Executable files
1
Suspicious files
4
Text files
53
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\index.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\0I6H4HT4.htm | html | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\count[1].js | html | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\20163291848534578[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\load[1].png | image | |
MD5:0F3C5636FFF4C8D94068046E9AD869A5 | SHA256:AE244C70017037B1BD9756B2331D72414AD1B88B9057B57A43A55781D8FC5B74 | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\jqbs.min[1].js | text | |
MD5:800B09ABFCF7CD09C260D166E6C2D2F9 | SHA256:CA5A5052E60D1B8DE3C96FD6023DDA81D02E1D299CD0C59483C516C189889C2C | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\sj_icon3[1].png | image | |
MD5:C2655A3FFD778BC824FEFCC935078606 | SHA256:83CE19BDDA4BD0840E1C2890B4FA55A49FA328EFC744CD5BD5A37D57F3742B38 | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\20132184722[1].jpg | image | |
MD5:FCEAD7F445D48B68E70DAECF1CA7F1C4 | SHA256:5B77B654E9FB1F6780B3A17A002A0F57CC422C9485168107473409558C06B4E5 | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\logo[1].png | image | |
MD5:16588074E1DF99EAA57DDD704648348E | SHA256:79CE57029404403736EECC214978DACD5AE3A8591BEB1C521D8E9B1500A3AAB2 | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\mredirect[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
8
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/skin/know/count.js | US | html | 1.90 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/public/dist/css/index.min.css | US | text | 10.5 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/inc/mredirect.js | US | text | 59.5 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/up/2016-3/20163282020525932.jpg | US | image | 63.8 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/public/dist/js/index.min.js | US | html | 2.63 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/inc/jqbs.min.js | US | text | 38.4 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/up/2014-11/20141111105719.jpg | US | image | 1.24 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/up/2013-2/20132184722.jpg | US | image | 1.27 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/up/2016-3/20163291848534578.jpg | US | image | 11.8 Kb | suspicious |
2932 | iexplore.exe | GET | 200 | 47.246.43.175:80 | http://www.uzzf.com/skin/uzzf2016/images/sj_icon3.png | US | image | 2.82 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | iexplore.exe | 47.246.43.175:80 | www.uzzf.com | — | US | suspicious |
— | — | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
2932 | iexplore.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.uzzf.com |
| suspicious |
pic.uzzf.com |
| malicious |
hm.baidu.com |
| whitelisted |
nz.qqtn.com |
| malicious |
www.xueshangwang.com |
| malicious |