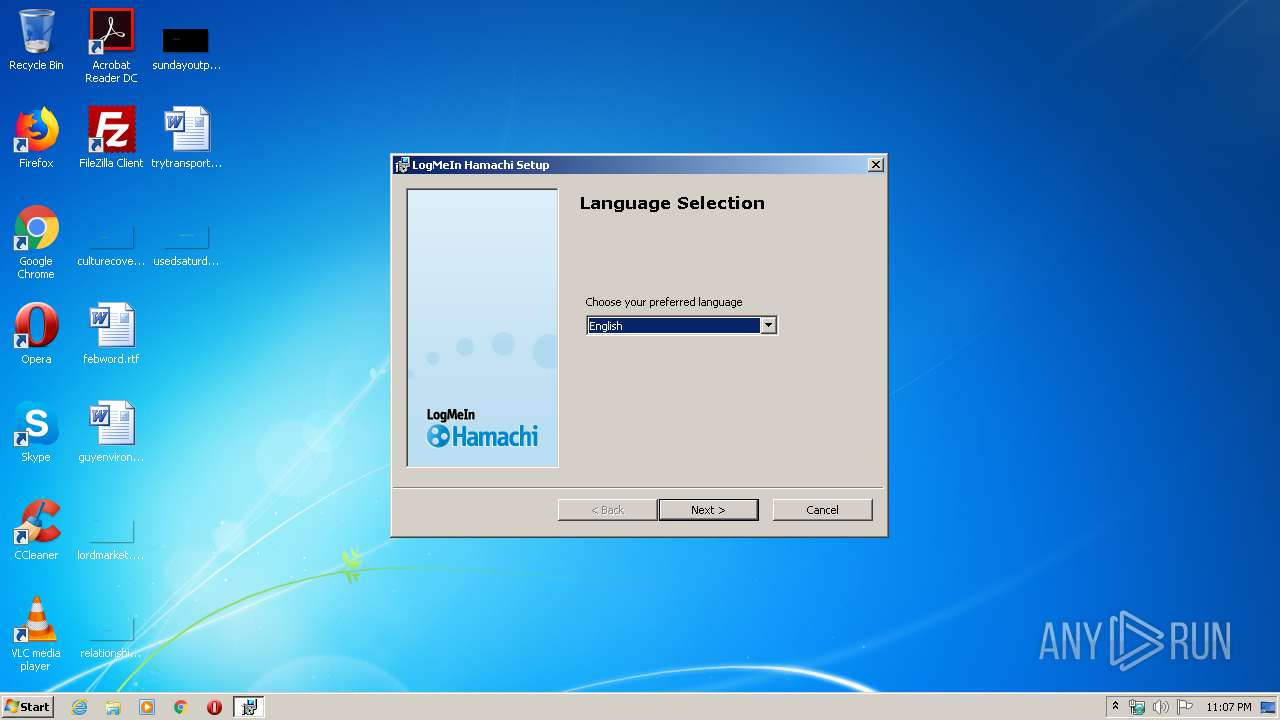
| File name: | hamachi.msi |
| Full analysis: | https://app.any.run/tasks/b1565415-4876-4d36-94e0-b2fdbf7e37ce |
| Verdict: | Malicious activity |
| Analysis date: | May 11, 2020, 22:07:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
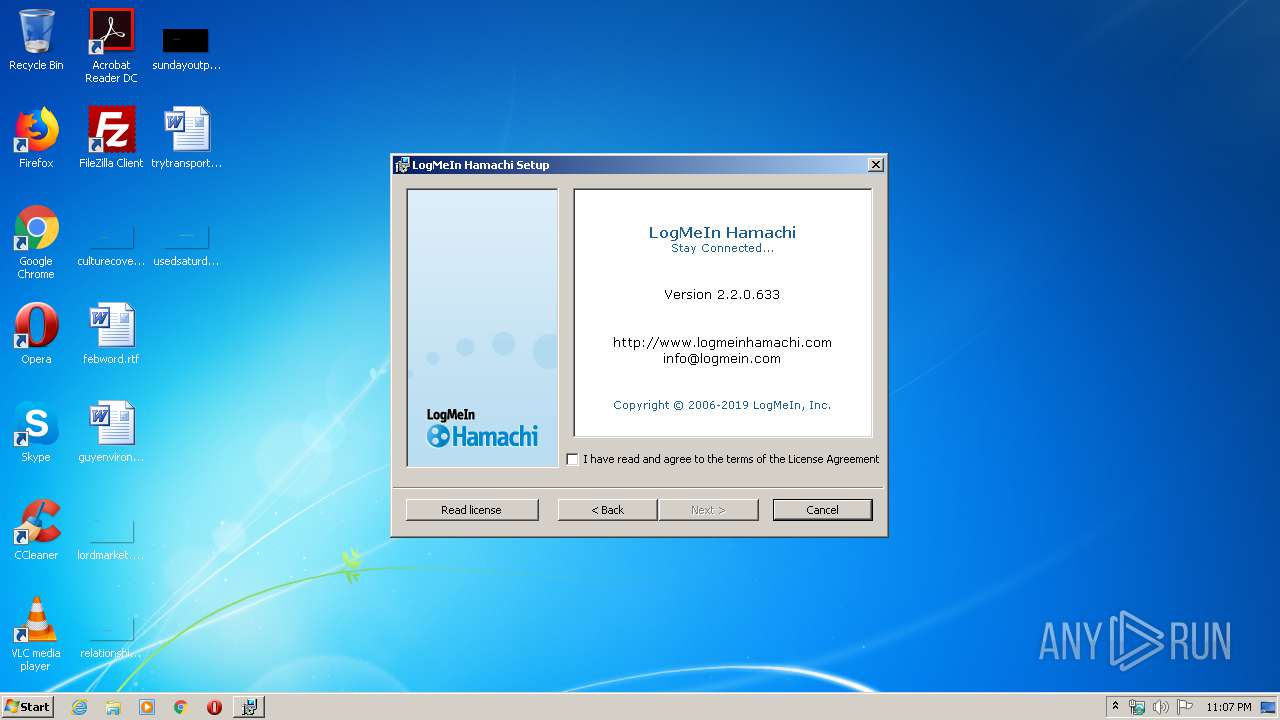
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: LogMeIn Hamachi Installer, Author: LogMeIn, Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install LogMeIn Hamachi., Template: ;1033, Number of Pages: 200, Number of Words: 2, Security: 2, Revision Number: {E4BBB2CD-A272-4101-AC58-931085DFCAEE}, Create Time/Date: Tue Apr 2 16:04:15 2019, Last Saved Time/Date: Tue Apr 2 16:04:15 2019, Name of Creating Application: Windows Installer XML v2.0.5805.0 (candle/light) |
| MD5: | 94E752CF7EB9999AAD359AC251914DEE |
| SHA1: | 5D9A27C1CE29501422D16E838399BA662D322B97 |
| SHA256: | 67EFB9AA0B7CA0166078EDD04EA5F09234C11AC45CB00D31367B9FBCE290C53F |
| SSDEEP: | 196608:+GBnMba+/B+Vmo3L5ImZech8ZyCzxMWWk0ez:jBnMba+/GF75ImZeZdWk0e |
MALICIOUS
Application was dropped or rewritten from another process
- LMIGuardianSvc.exe (PID: 304)
- hamachi-2.exe (PID: 2896)
- LMIGuardianSvc.exe (PID: 3616)
- LMIGuardianSvc.exe (PID: 3200)
- LMIGuardianSvc.exe (PID: 280)
- LMIGuardianSvc.exe (PID: 3292)
- hamachi-2.exe (PID: 3024)
- hamachi-2.exe (PID: 2472)
- LMIGuardianSvc.exe (PID: 3852)
- hamachi-2.exe (PID: 1388)
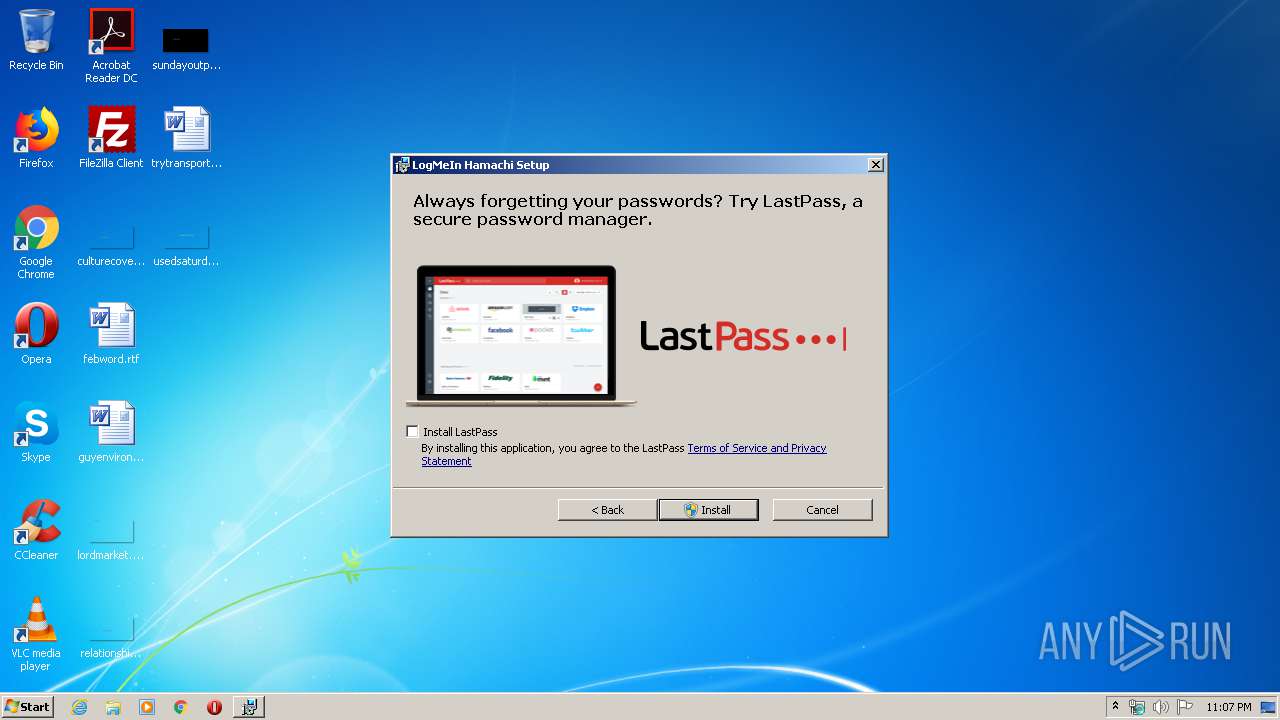
- lastpass_downloader.exe (PID: 3776)
Loads dropped or rewritten executable
- LMIGuardianSvc.exe (PID: 304)
- LMIGuardianSvc.exe (PID: 3616)
- LMIGuardianSvc.exe (PID: 3200)
- LMIGuardianSvc.exe (PID: 280)
- LMIGuardianSvc.exe (PID: 3292)
- LMIGuardianSvc.exe (PID: 3852)
Changes settings of System certificates
- hamachi-2.exe (PID: 2896)
SUSPICIOUS
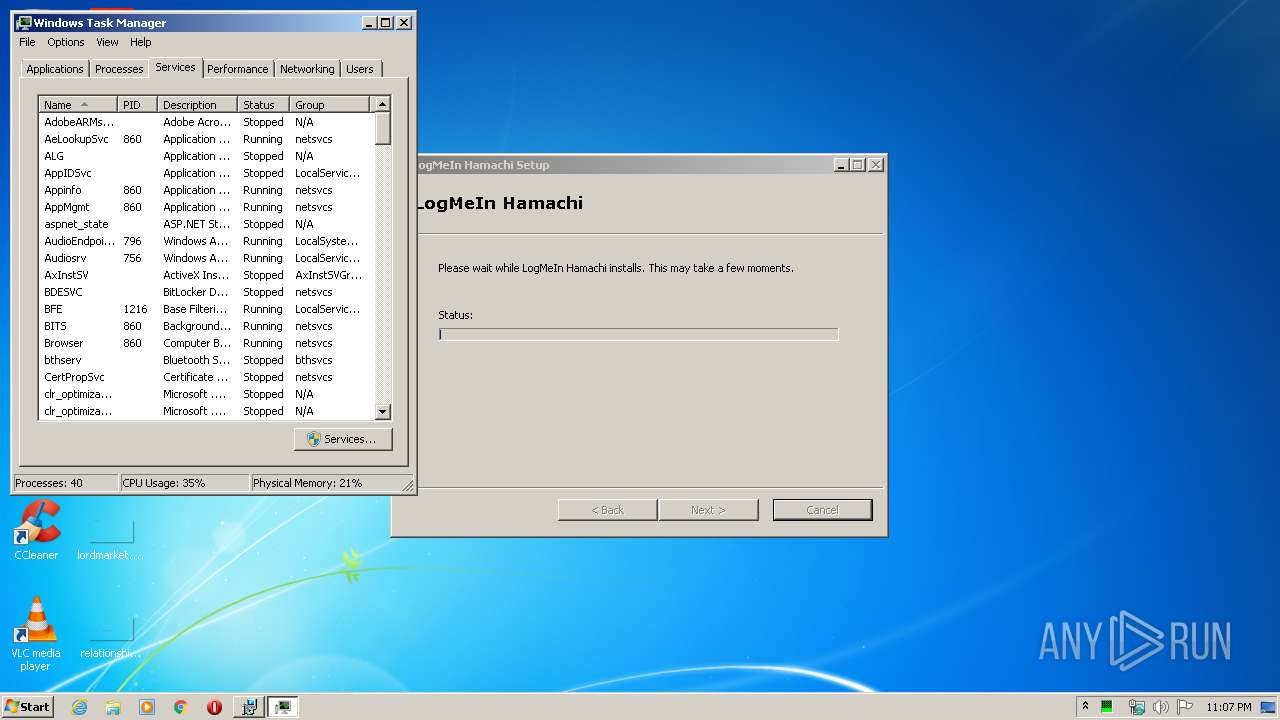
Starts SC.EXE for service management
- MsiExec.exe (PID: 4060)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2684)
- hamachi-2.exe (PID: 2896)
- MsiExec.exe (PID: 4060)
Executed as Windows Service
- LMIGuardianSvc.exe (PID: 3200)
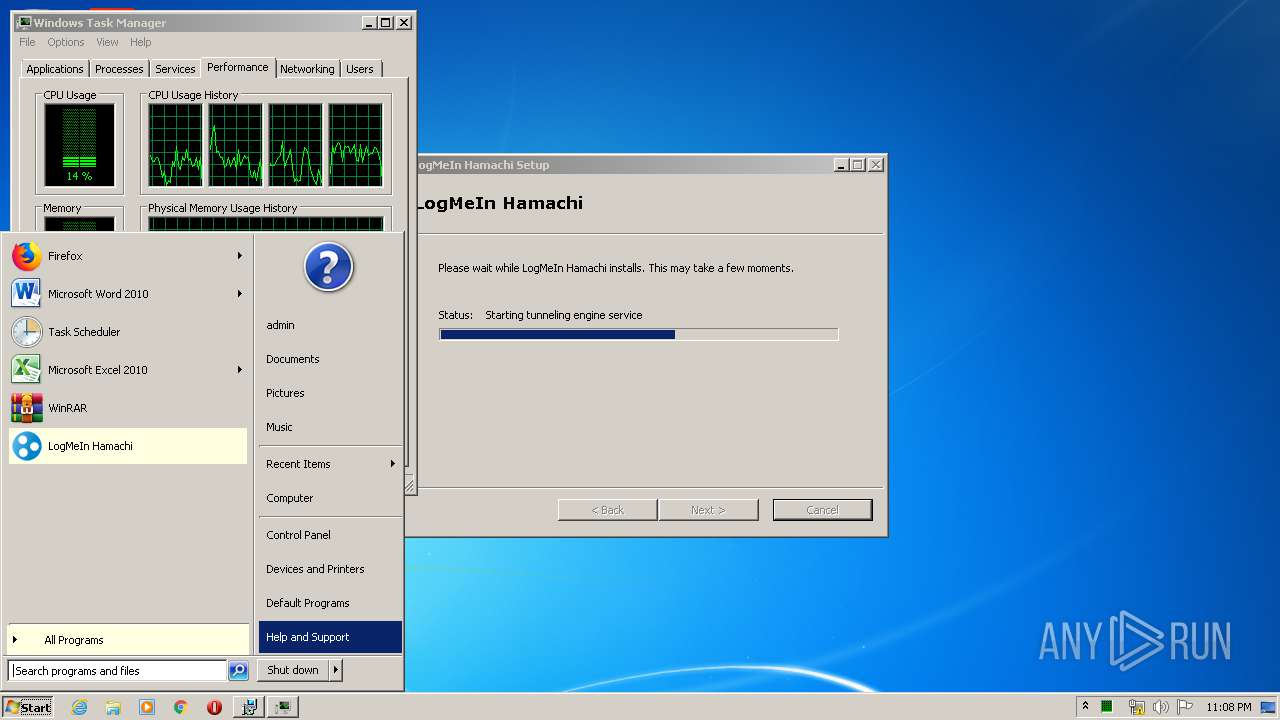
- hamachi-2.exe (PID: 3024)
- hamachi-2.exe (PID: 1388)
Executed via COM
- rundll32.exe (PID: 1468)
Uses NETSH.EXE for network configuration
- hamachi-2.exe (PID: 2896)
- hamachi-2.exe (PID: 2472)
Changes IE settings (feature browser emulation)
- MsiExec.exe (PID: 4060)
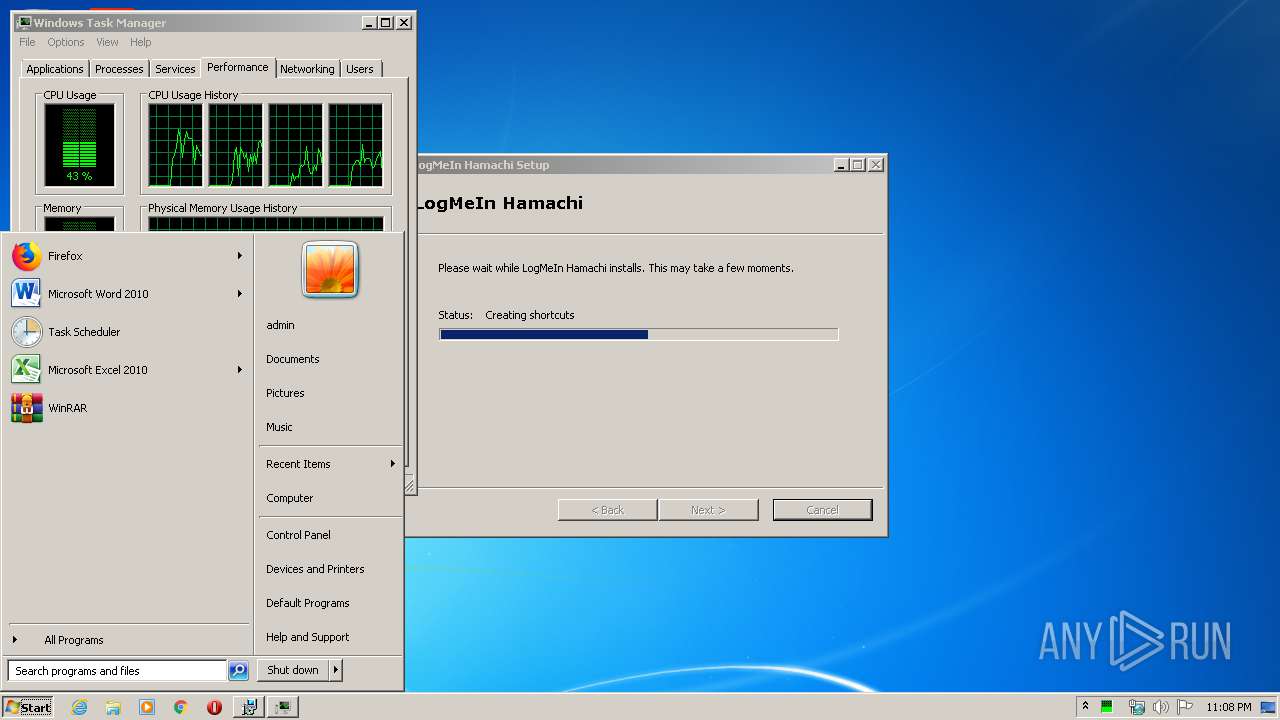
Creates files in the Windows directory
- hamachi-2.exe (PID: 1388)
- MsiExec.exe (PID: 4060)
- hamachi-2.exe (PID: 3024)
- lastpass_downloader.exe (PID: 3776)
- hamachi-2.exe (PID: 2896)
Removes files from Windows directory
- hamachi-2.exe (PID: 1388)
- hamachi-2.exe (PID: 2896)
Creates files in the driver directory
- hamachi-2.exe (PID: 2896)
Adds / modifies Windows certificates
- hamachi-2.exe (PID: 2896)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3796)
- MsiExec.exe (PID: 564)
- MsiExec.exe (PID: 4060)
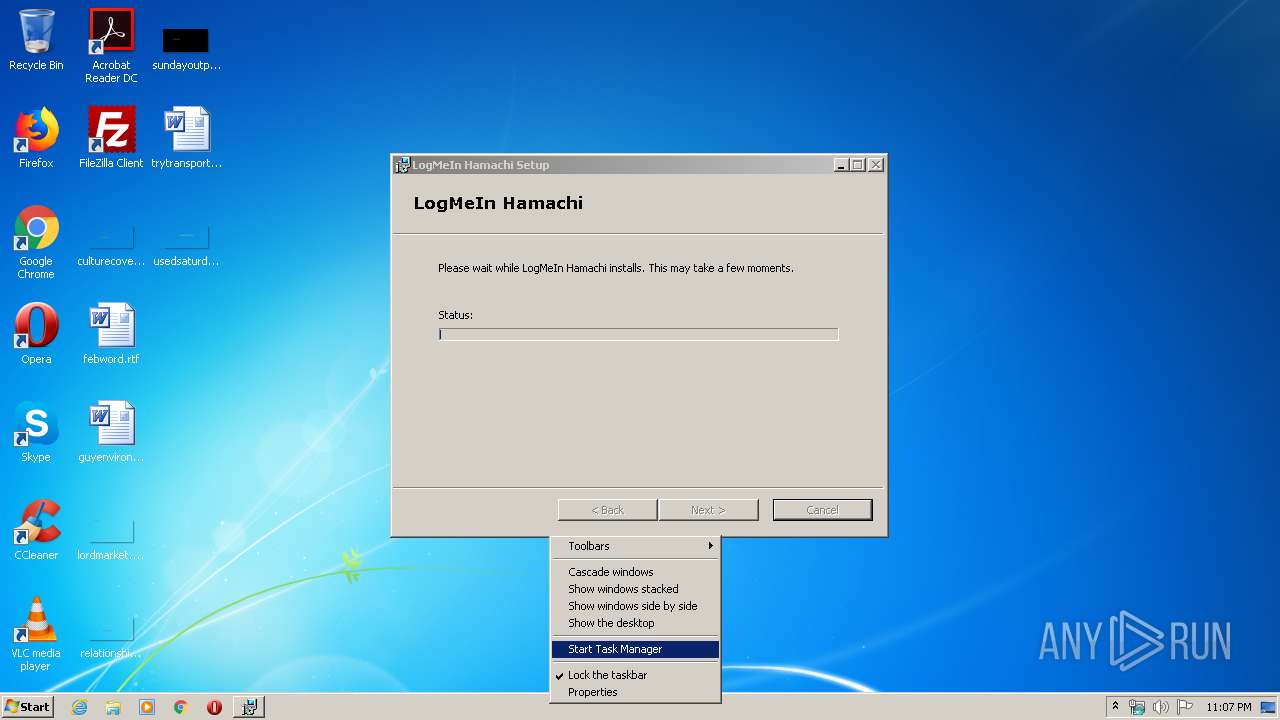
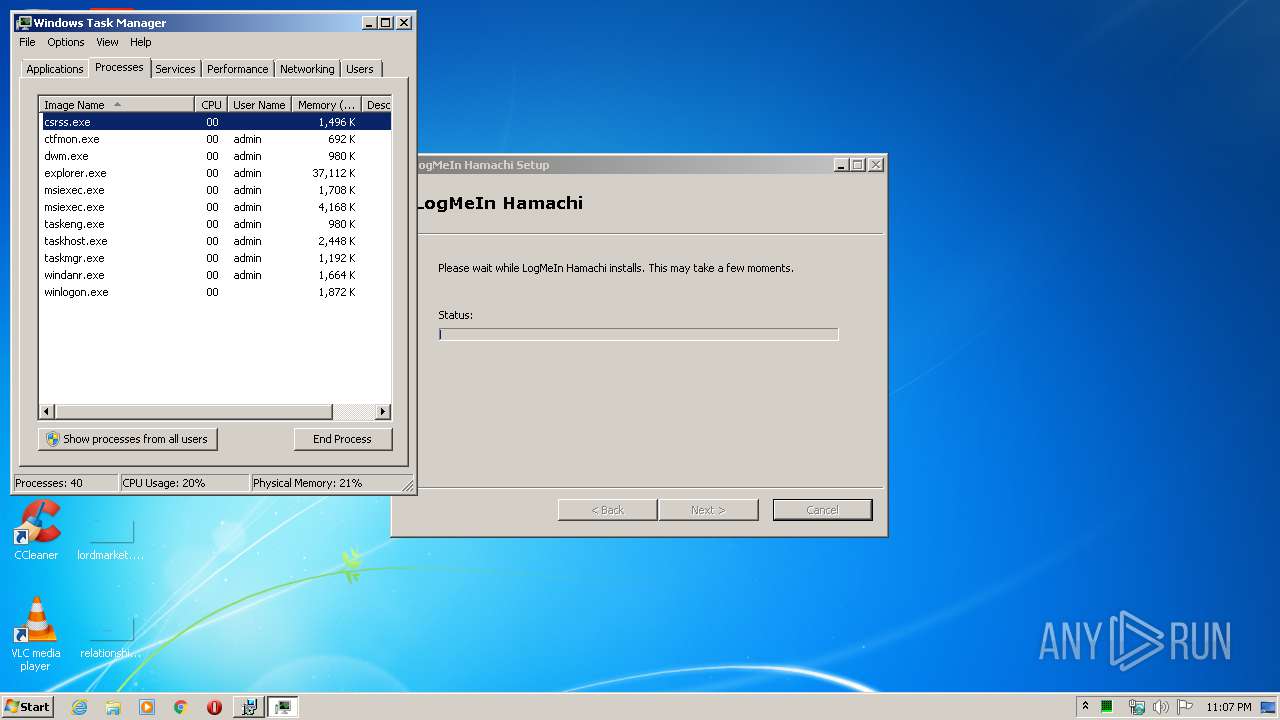
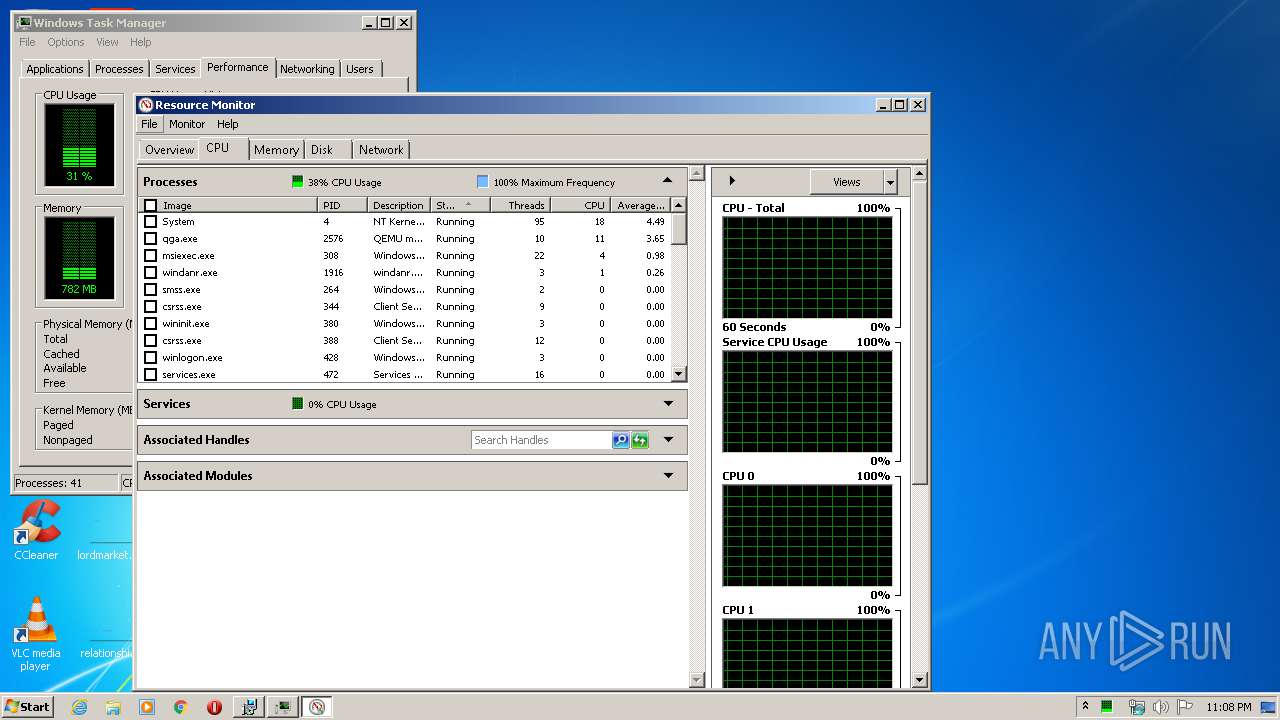
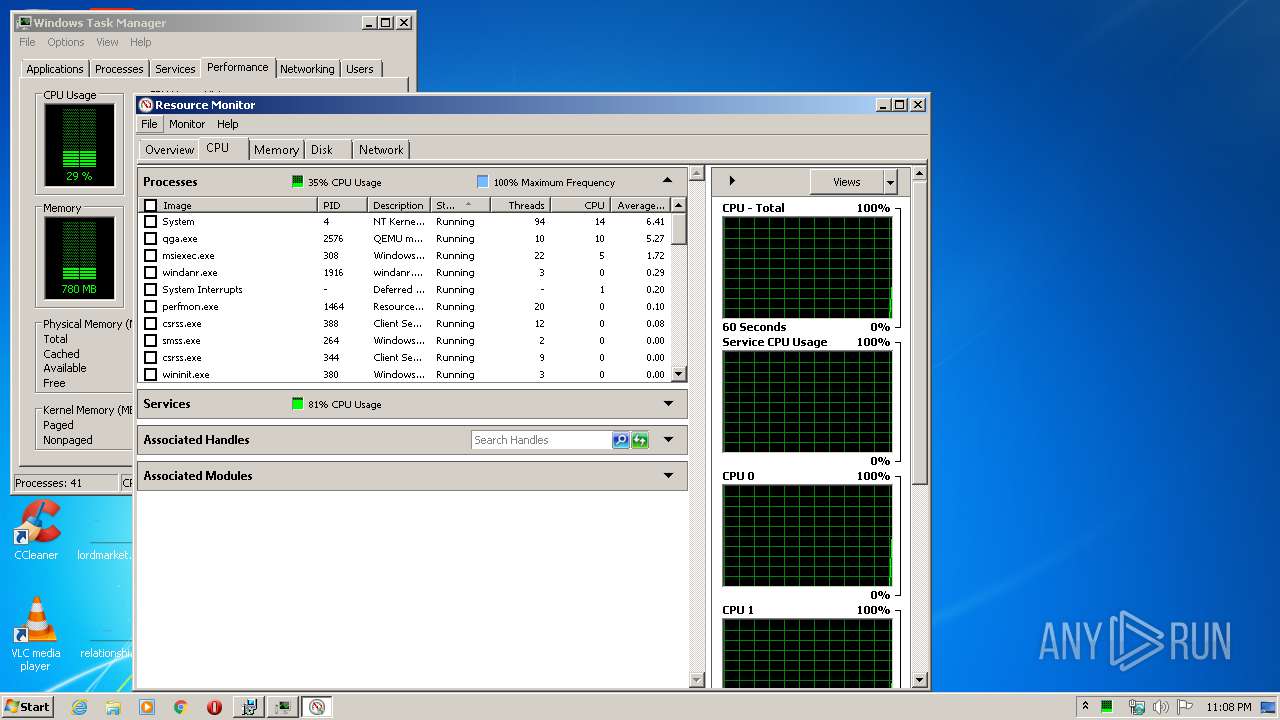
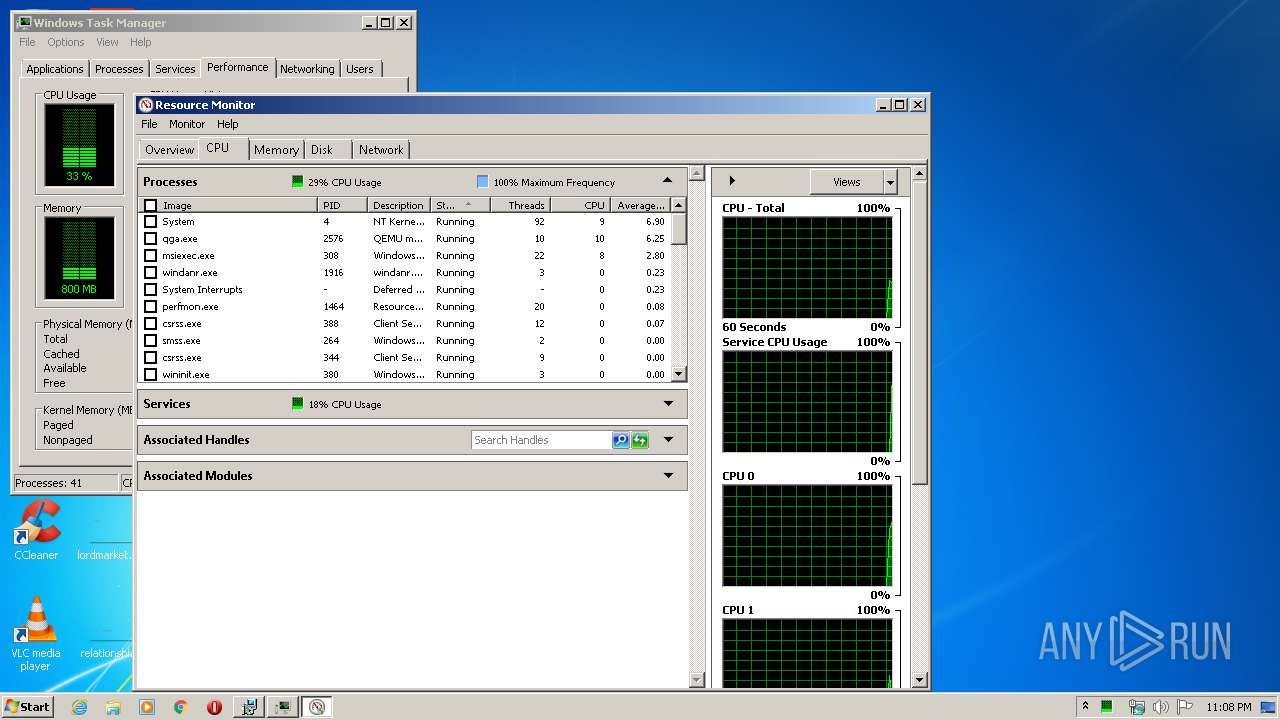
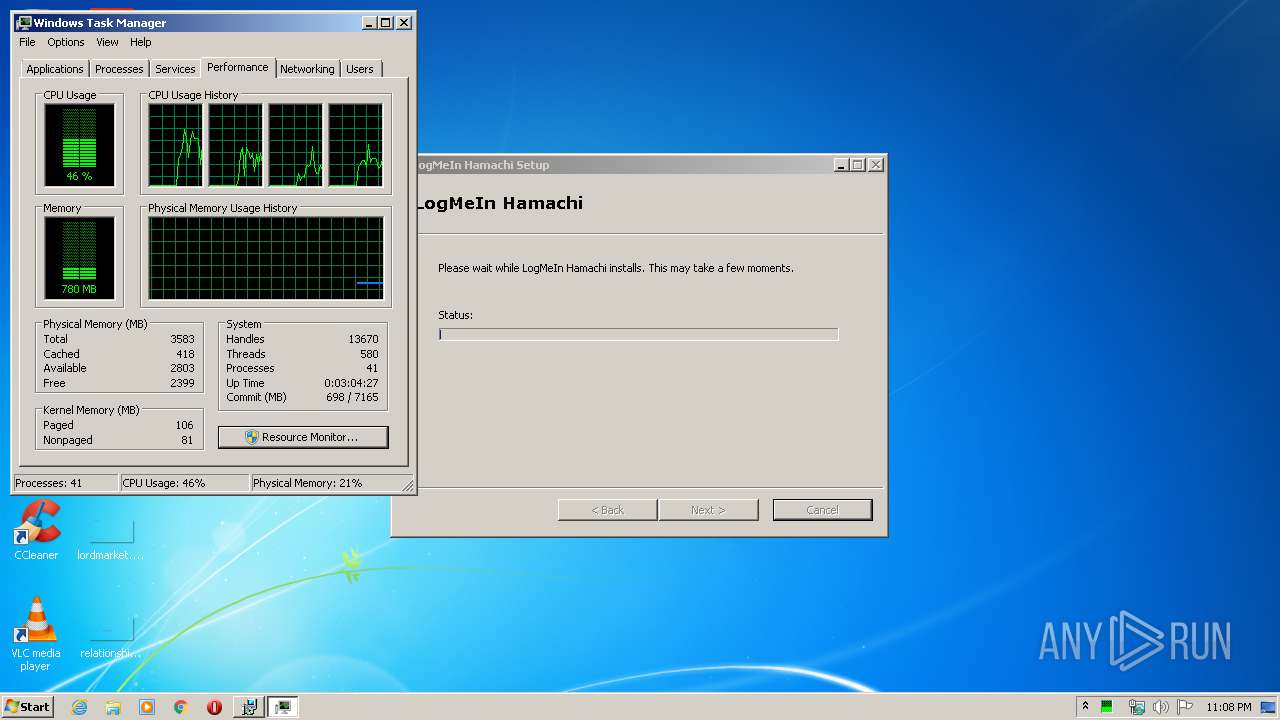
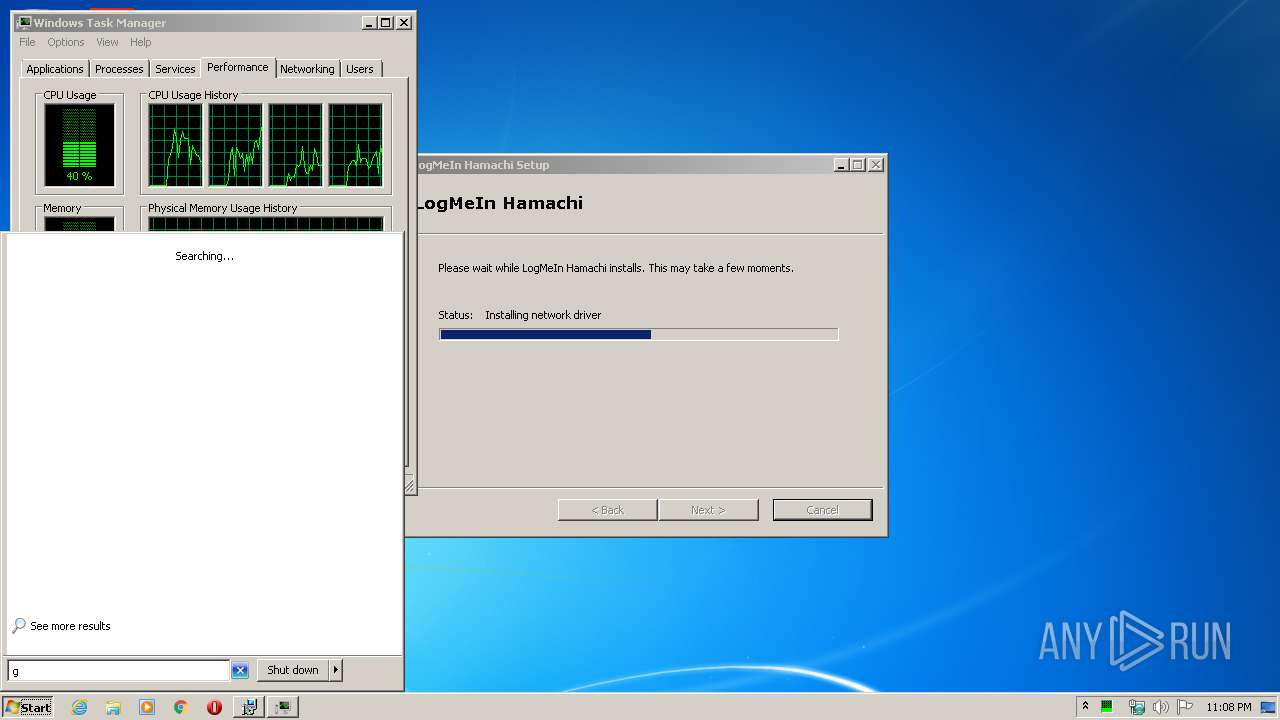
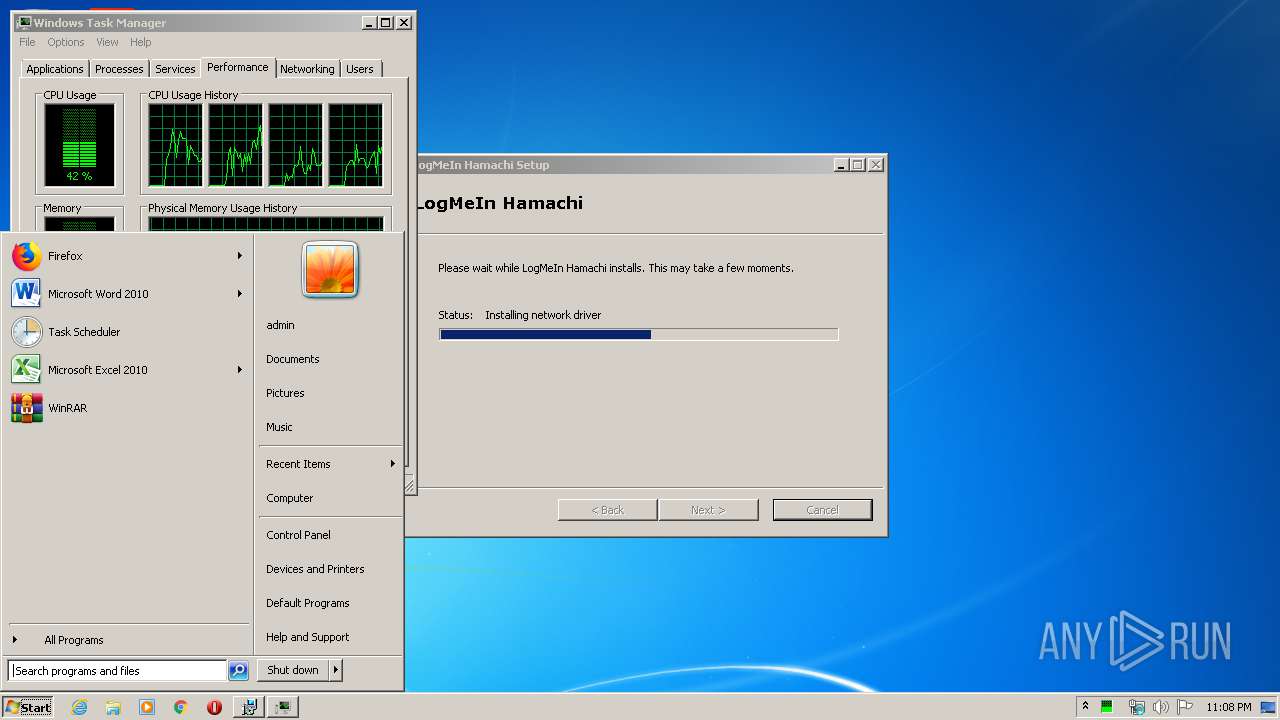
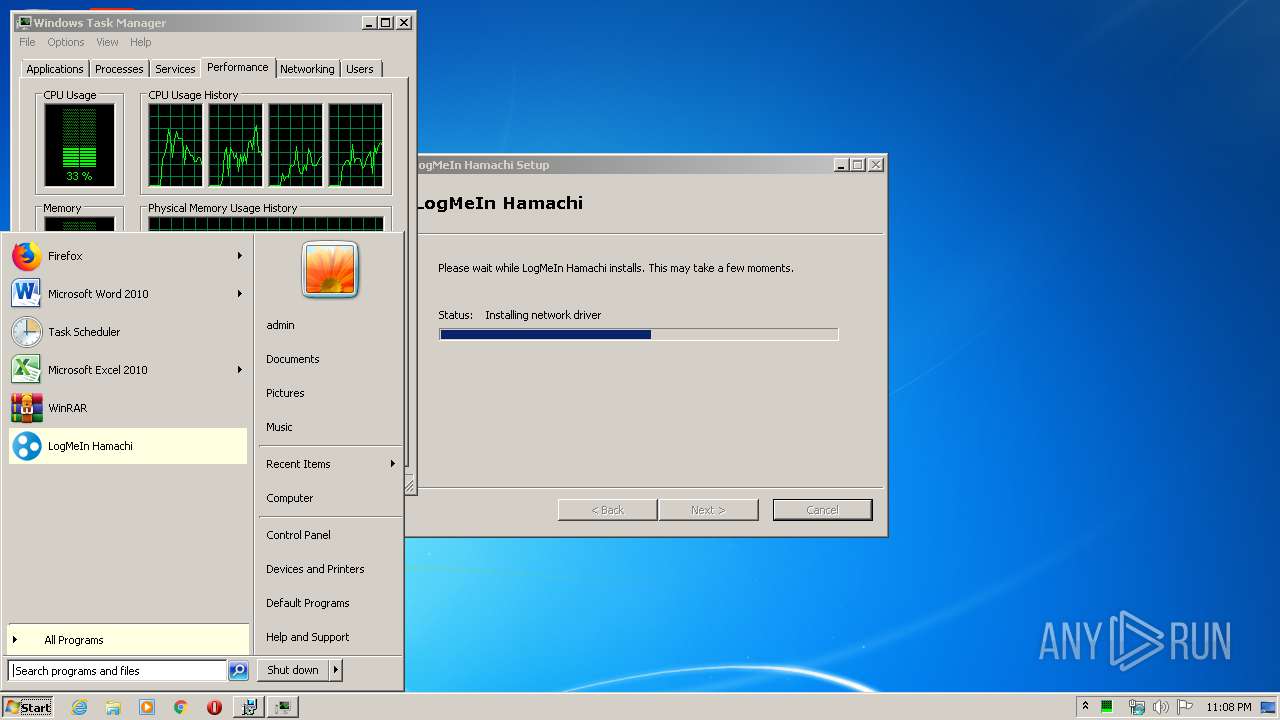
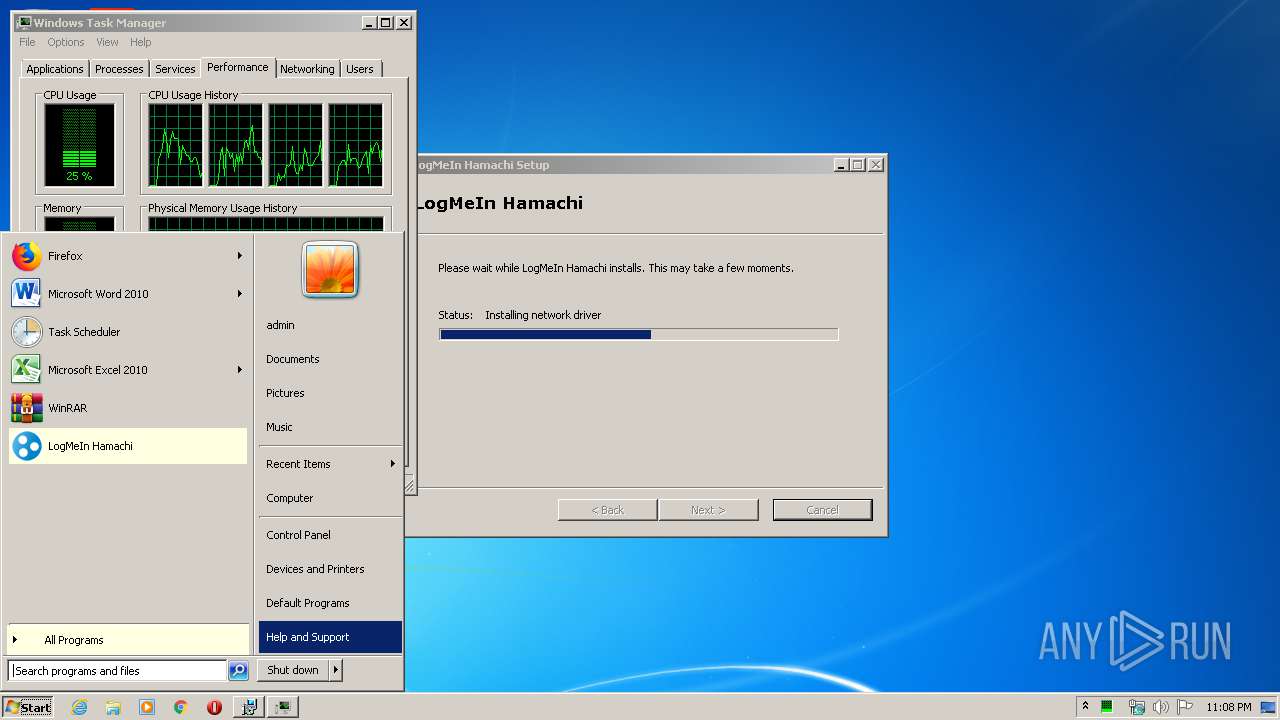
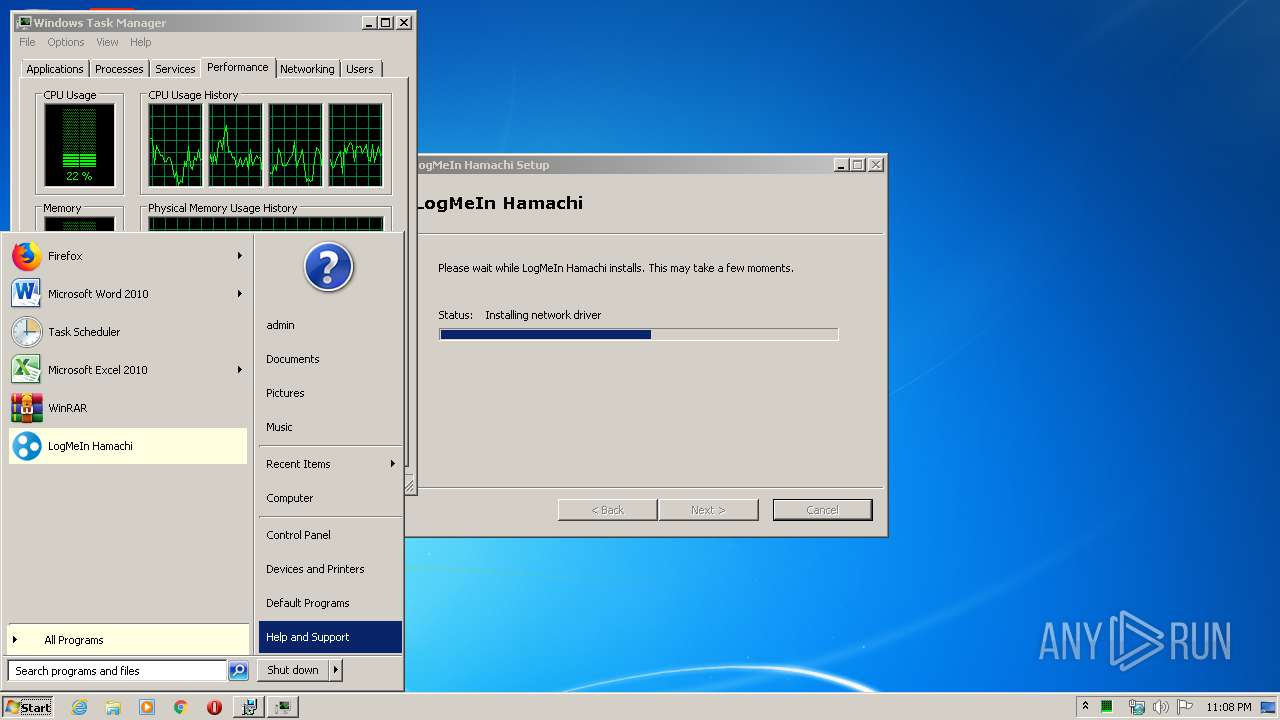
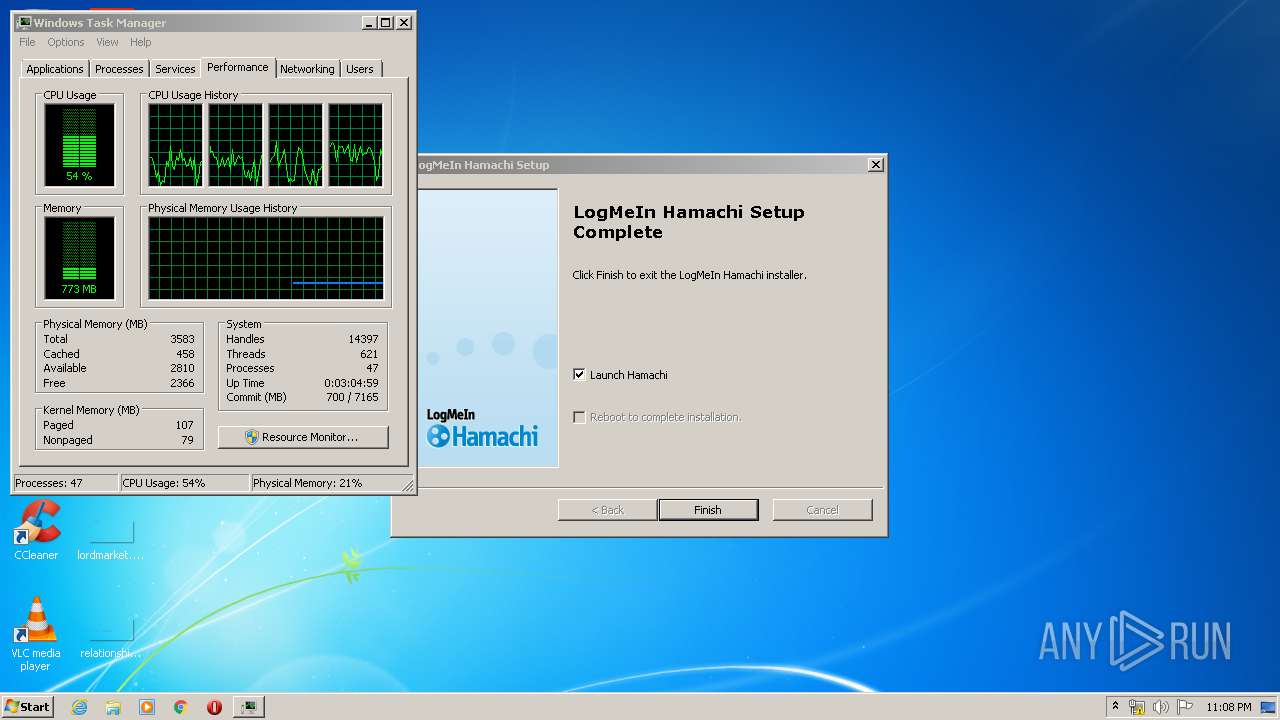
Manual execution by user
- taskmgr.exe (PID: 3172)
Creates or modifies windows services
- MsiExec.exe (PID: 4060)
Reads settings of System Certificates
- hamachi-2.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (93.6) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (5) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
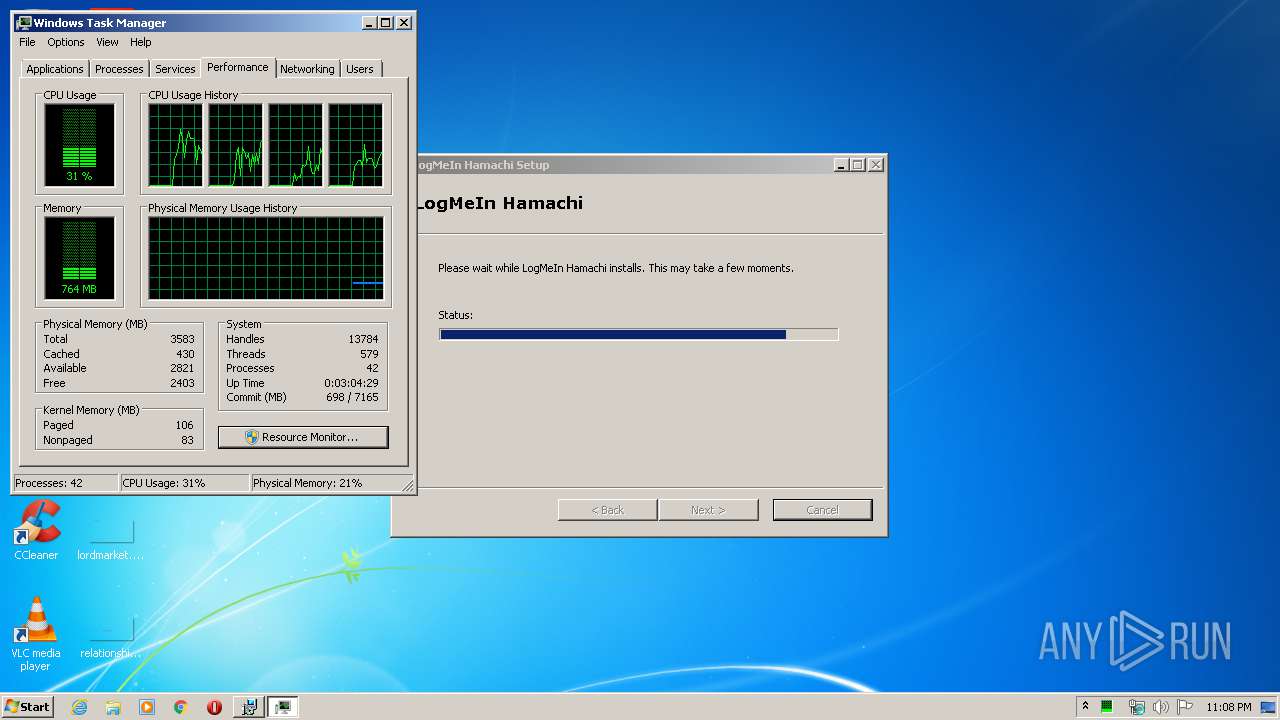
| Title: | Installation Database |
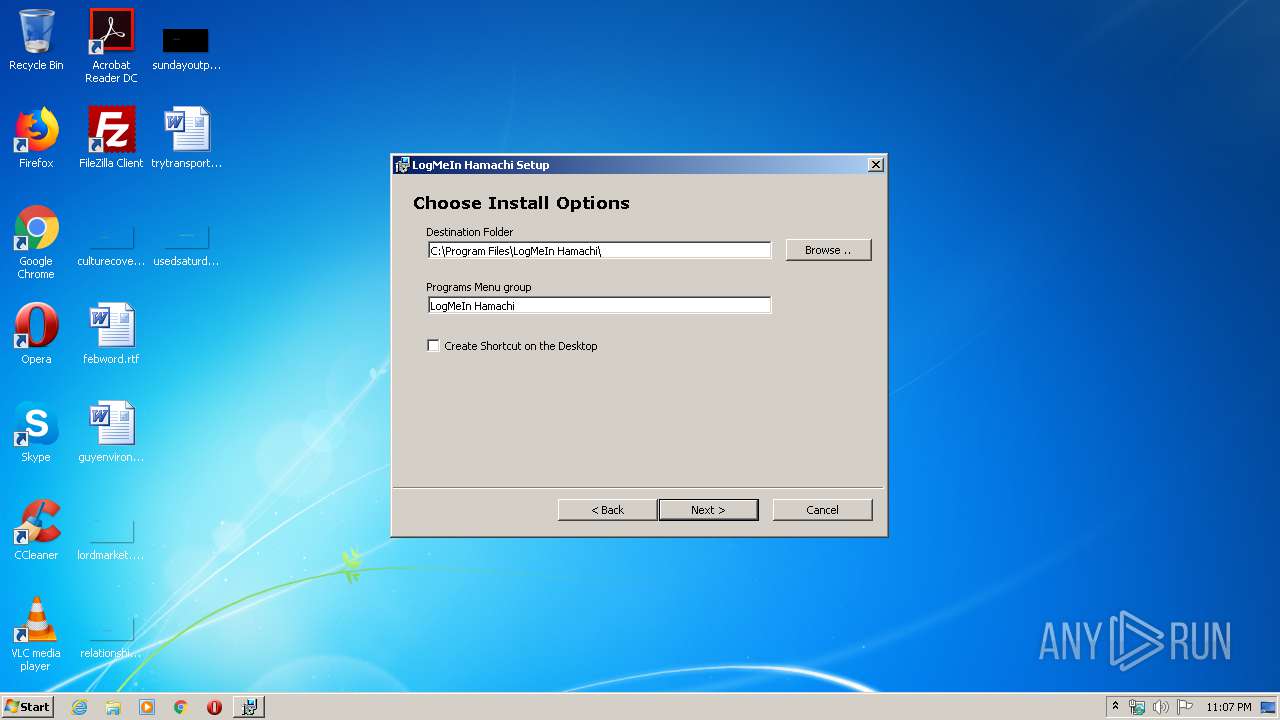
| Subject: | LogMeIn Hamachi Installer |
| Author: | LogMeIn, Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install LogMeIn Hamachi. |
| Template: | ;1033 |
| Pages: | 200 |
| Words: | 2 |
| Security: | Read-only recommended |
| RevisionNumber: | {E4BBB2CD-A272-4101-AC58-931085DFCAEE} |
| CreateDate: | 2019:04:02 15:04:15 |
| ModifyDate: | 2019:04:02 15:04:15 |
| Software: | Windows Installer XML v2.0.5805.0 (candle/light) |
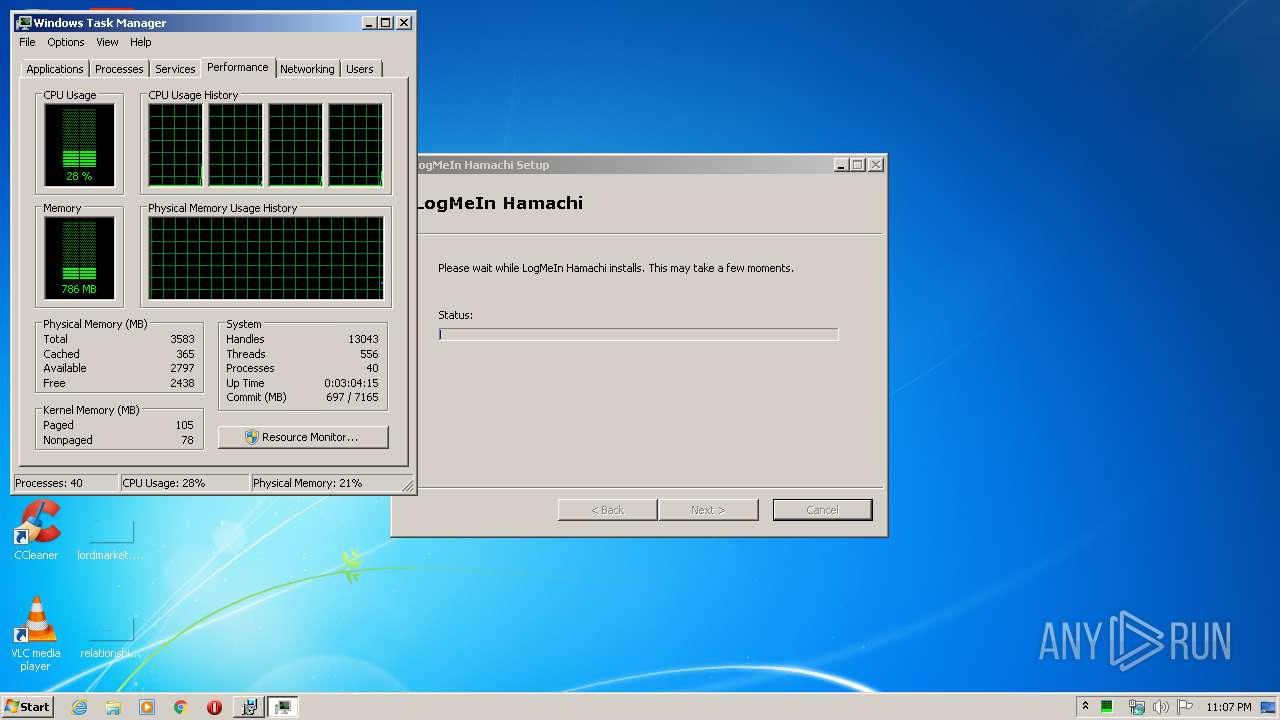
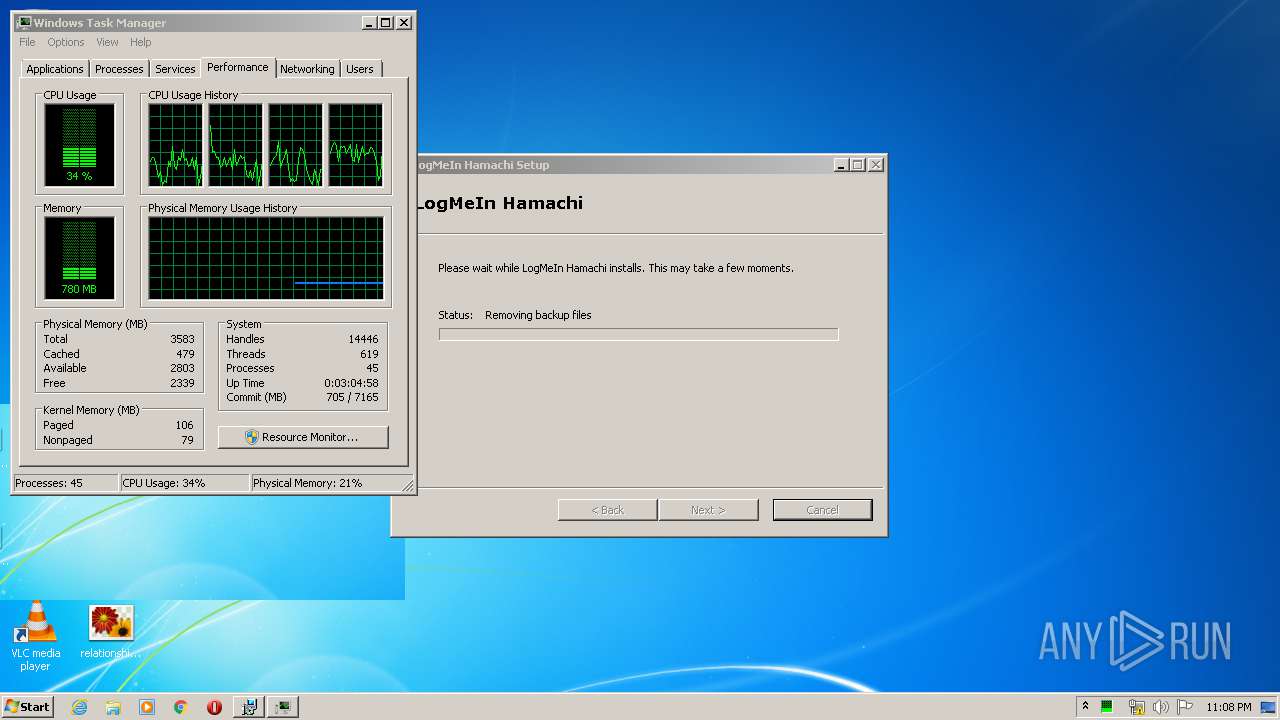
Total processes
82
Monitored processes
18
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe" /escort 2472 /CUSTOM Hamachi | C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: LogMeIn, Inc. Integrity Level: SYSTEM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
| 304 | "C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe" -Service | C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: LogMeIn, Inc. Integrity Level: SYSTEM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
| 564 | C:\Windows\system32\MsiExec.exe -Embedding 8EC786D485DF43D0A1A05E74D02CFCD9 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | "C:\Program Files\LogMeIn Hamachi\hamachi-2.exe" -s | C:\Program Files\LogMeIn Hamachi\hamachi-2.exe | services.exe | ||||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 0 Version: 2, 2, 0, 633 Modules
| |||||||||||||||
| 1464 | "C:\Windows\System32\perfmon.exe" /res | C:\Windows\System32\perfmon.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Resource and Performance Monitor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1468 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\LogMeIn Hamachi\hamachi-2.exe" --config Hamachi 25.0.0.1 | C:\Program Files\LogMeIn Hamachi\hamachi-2.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 0 Version: 2, 2, 0, 633 Modules
| |||||||||||||||
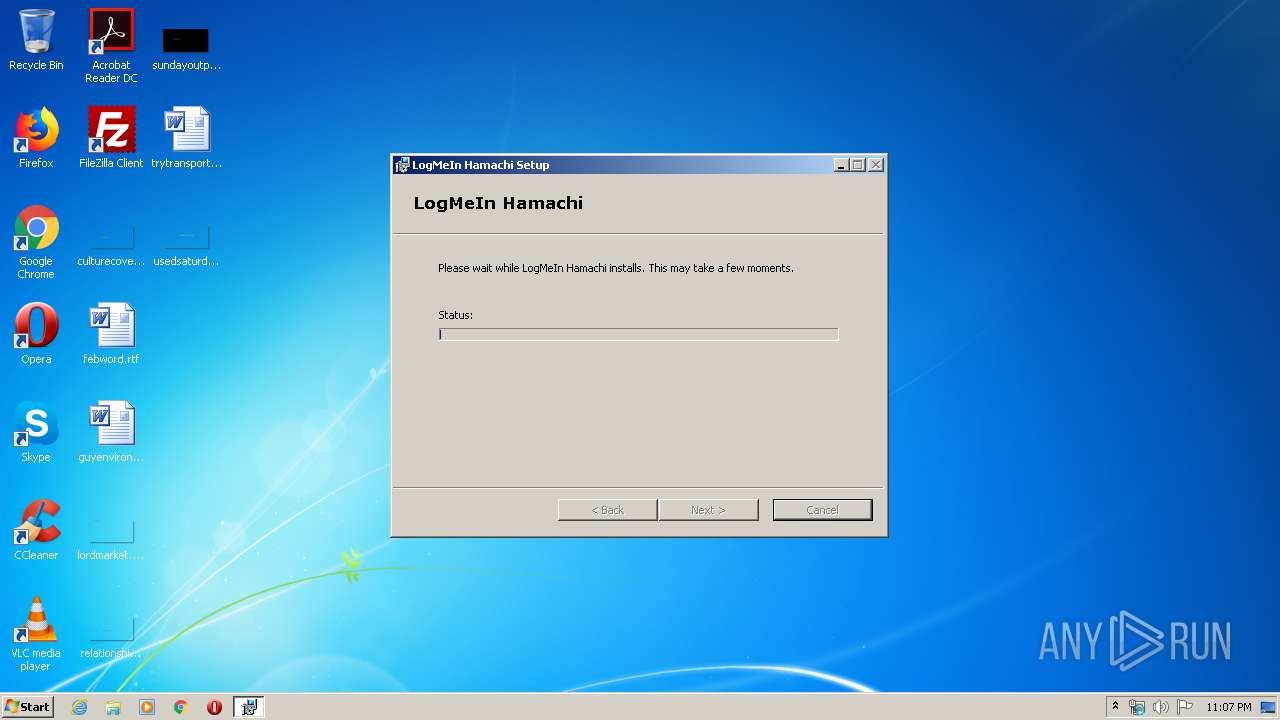
| 2684 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\hamachi.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\LogMeIn Hamachi\hamachi-2.exe" --add-tap-at-install Hamachi | C:\Program Files\LogMeIn Hamachi\hamachi-2.exe | MsiExec.exe | ||||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 0 Version: 2, 2, 0, 633 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\LogMeIn Hamachi\hamachi-2.exe" -s --get-config | C:\Program Files\LogMeIn Hamachi\hamachi-2.exe | — | services.exe | |||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 0 Version: 2, 2, 0, 633 Modules
| |||||||||||||||
Total events
2 768
Read events
1 042
Write events
1 644
Delete events
82
Modification events
| (PID) Process: | (2684) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3172) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3172) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1464) perfmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RPM |
| Operation: | write | Name: | Resmon |
Value: 840000005C000000A4030000B4020000 | |||
| (PID) Process: | (4060) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Hamachi2Svc |
| Operation: | write | Name: | DependOnService |
Value: winmgmt | |||
| (PID) Process: | (304) LMIGuardianSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{67E4A0D8-8675-4FBB-BC62-F10EC894327E} |
| Operation: | write | Name: | |
Value: LMIGuardianSvc | |||
| (PID) Process: | (304) LMIGuardianSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{67E4A0D8-8675-4FBB-BC62-F10EC894327E} |
| Operation: | write | Name: | AccessPermission |
Value: 010014807400000084000000140000003000000002001C000100000011001400010000000101000000000010001000000200440003000000000014000B000000010100000000000504000000000014000B00000001010000000000050B000000000014000B0000000101000000000005120000000102000000000005200000002002000001020000000000052000000020020000 | |||
| (PID) Process: | (304) LMIGuardianSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{67E4A0D8-8675-4FBB-BC62-F10EC894327E} |
| Operation: | write | Name: | LaunchPermission |
Value: 010014807400000084000000140000003000000002001C000100000011001400010000000101000000000010001000000200440003000000000014000B000000010100000000000504000000000014000B00000001010000000000050B000000000014000B0000000101000000000005120000000102000000000005200000002002000001020000000000052000000020020000 | |||
| (PID) Process: | (304) LMIGuardianSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\LMIGuardianSvc.EXE |
| Operation: | write | Name: | AppID |
Value: {67E4A0D8-8675-4FBB-BC62-F10EC894327E} | |||
| (PID) Process: | (304) LMIGuardianSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{67E4A0D8-8675-4FBB-BC62-F10EC894327E} |
| Operation: | write | Name: | LocalService |
Value: LMIGuardianSvc | |||
Executable files
3
Suspicious files
2
Text files
608
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI84B0.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI84C1.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI84F1.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8C45.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI9510.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI9C25.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI9C65.tmp | — | |
MD5:— | SHA256:— | |||
| 3796 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\HamachiSetup.log | text | |
MD5:— | SHA256:— | |||
| 564 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\HamachiSetup.log | text | |
MD5:— | SHA256:— | |||
| 2684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8432.tmp | executable | |
MD5:3B8CB5FDA4AC857DB29B43D765D650F6 | SHA256:8F4693C8030B74F32D828EFEDEAF997EE01C719A393EFAC179A51DF6004E41D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3776 | lastpass_downloader.exe | 104.98.132.96:443 | lastpass.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
255.100.168.192.in-addr.arpa |
| unknown |
252.0.0.224.in-addr.arpa |
| unknown |
3.0.0.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.f.f.ip6.arpa |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
lastpass.com |
| unknown |