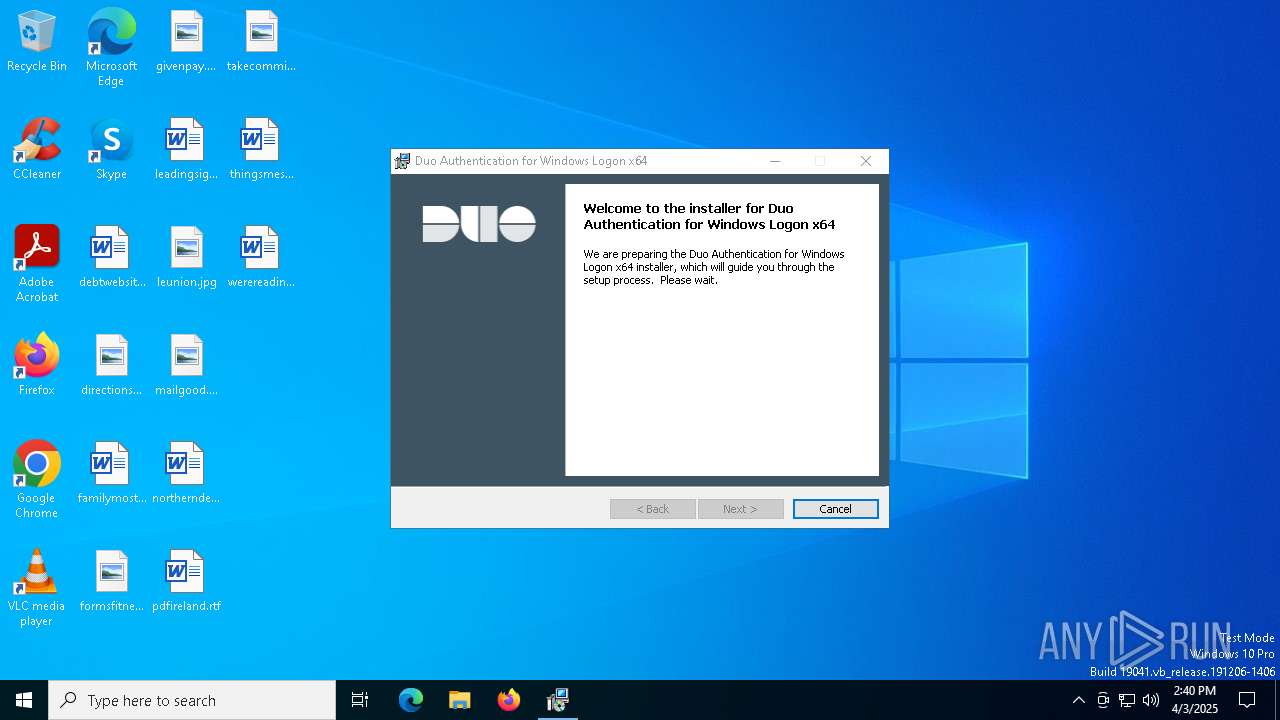
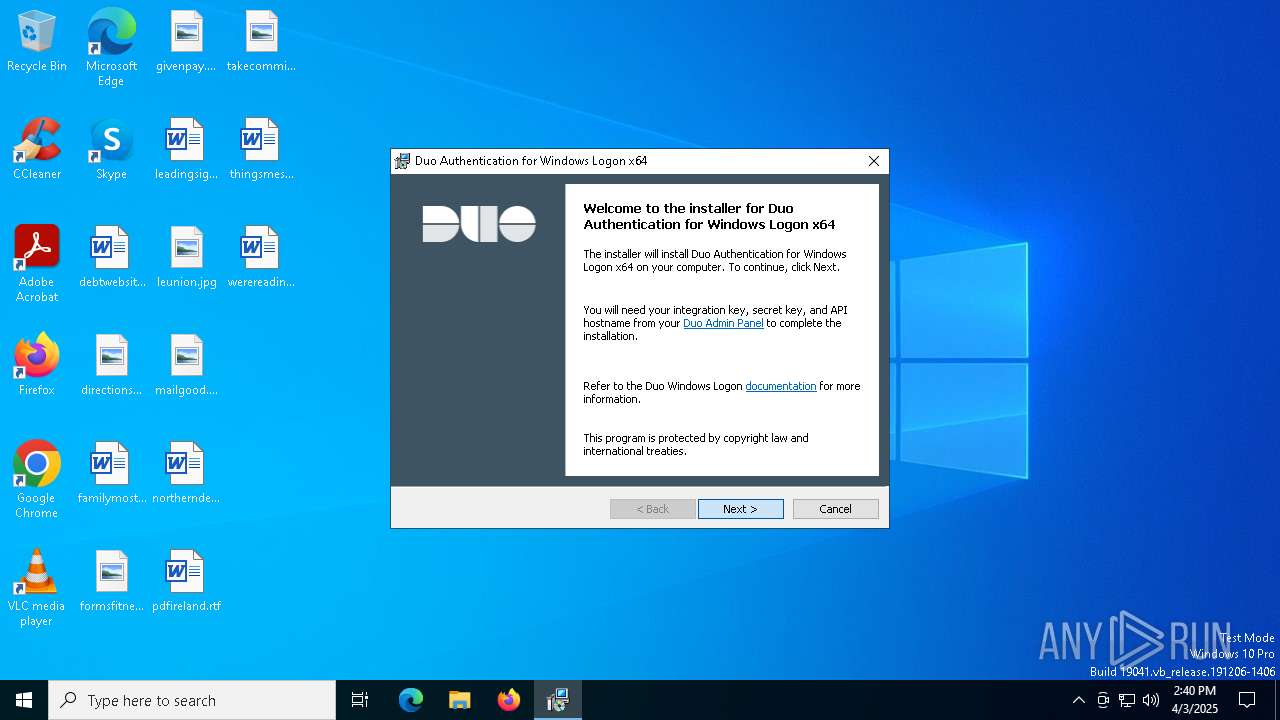
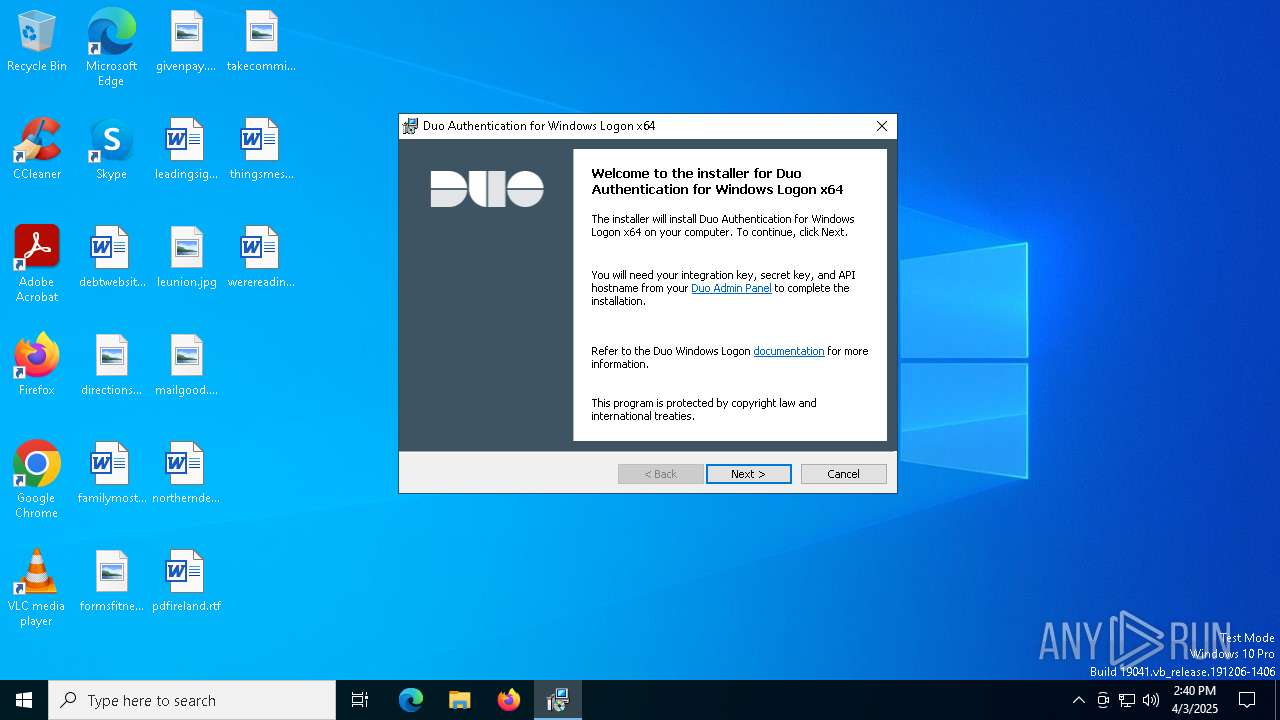
| File name: | duo-win-login-4.3.0.exe |
| Full analysis: | https://app.any.run/tasks/c3d08f35-1b1c-4e91-91b5-d044fa922c1b |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2025, 14:39:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 1B96728DB163CD787AD96700D1F423A5 |
| SHA1: | 07B7913A12D91377F705745CEEA65C5F6538289B |
| SHA256: | 67EB371488F23B643875FCD9274F1F8C8D184BAEDE884CAF739A90FC9A02D855 |
| SSDEEP: | 98304:dtLbkHLWqniKHqvAIhkZ3Q5FON2Rnx08/wO9IcJ6TrI/IlTfnxHmbhI4Miy/NtQm:JFu2eQ4f7KnQartjp+7R |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- DUOD0FE.tmp (PID: 7524)
- duo-win-login-4.3.0.exe (PID: 7500)
- DUOD0FE.tmp (PID: 7548)
- Setup64.exe (PID: 7656)
Starts application with an unusual extension
- DUOD0FE.tmp (PID: 7524)
- duo-win-login-4.3.0.exe (PID: 7500)
Reads security settings of Internet Explorer
- DUOD0FE.tmp (PID: 7548)
- msiexec.exe (PID: 1012)
The process creates files with name similar to system file names
- DUOD0FE.tmp (PID: 7548)
Searches for installed software
- DUOD0FE.tmp (PID: 7548)
- dllhost.exe (PID: 7788)
Starts itself from another location
- DUOD0FE.tmp (PID: 7548)
Executes as Windows Service
- VSSVC.exe (PID: 7836)
Runs shell command (SCRIPT)
- msiexec.exe (PID: 1012)
INFO
Checks supported languages
- duo-win-login-4.3.0.exe (PID: 7500)
- DUOD0FE.tmp (PID: 7524)
- DUOD0FE.tmp (PID: 7548)
- Setup64.exe (PID: 7656)
- msiexec.exe (PID: 1012)
The sample compiled with english language support
- duo-win-login-4.3.0.exe (PID: 7500)
- DUOD0FE.tmp (PID: 7548)
- Setup64.exe (PID: 7656)
Create files in a temporary directory
- duo-win-login-4.3.0.exe (PID: 7500)
- DUOD0FE.tmp (PID: 7548)
Reads the computer name
- DUOD0FE.tmp (PID: 7548)
- Setup64.exe (PID: 7656)
- msiexec.exe (PID: 5956)
Reads the machine GUID from the registry
- DUOD0FE.tmp (PID: 7548)
- Setup64.exe (PID: 7656)
Process checks computer location settings
- DUOD0FE.tmp (PID: 7548)
Manages system restore points
- SrTasks.exe (PID: 6728)
Checks proxy server information
- Setup64.exe (PID: 7656)
Creates files or folders in the user directory
- Setup64.exe (PID: 7656)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2420)
Application launched itself
- msiexec.exe (PID: 5956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:26 15:44:27+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 70144 |
| InitializedDataSize: | 7583232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1849 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.3.0.4367 |
| ProductVersionNumber: | 4.3.0.4367 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Duo Security |
| FileDescription: | Duo Windows Logon protection |
| FileVersion: | 4.3.0.4367 |
| InternalName: | duo-win-login.exe |
| LegalCopyright: | Copyright (C) 2021 |
| OriginalFileName: | duo-win-login.exe |
| ProductName: | Duo Two-Factor Authentication for Windows |
| ProductVersion: | 4.3.0.4367-dc7f3c4fb2 |
Total processes
150
Monitored processes
17
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Windows\System32\net.exe" sessions | C:\Windows\System32\net.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | C:\Windows\System32\MsiExec.exe -Embedding 272C92F282A2195DFC3699A33D3875A7 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | C:\Windows\syswow64\MsiExec.exe -Embedding 9F12C2EA0A5E2433E690F44A01BC45E0 C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5956 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6728 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7400 | "C:\Users\admin\AppData\Local\Temp\duo-win-login-4.3.0.exe" | C:\Users\admin\AppData\Local\Temp\duo-win-login-4.3.0.exe | — | explorer.exe | |||||||||||
User: admin Company: Duo Security Integrity Level: MEDIUM Description: Duo Windows Logon protection Exit code: 3221226540 Version: 4.3.0.4367 Modules
| |||||||||||||||
| 7500 | "C:\Users\admin\AppData\Local\Temp\duo-win-login-4.3.0.exe" | C:\Users\admin\AppData\Local\Temp\duo-win-login-4.3.0.exe | explorer.exe | ||||||||||||
User: admin Company: Duo Security Integrity Level: HIGH Description: Duo Windows Logon protection Version: 4.3.0.4367 Modules
| |||||||||||||||
| 7524 | "C:\Users\admin\AppData\Local\Temp\DUOD0FE.tmp" | C:\Users\admin\AppData\Local\Temp\DUOD0FE.tmp | duo-win-login-4.3.0.exe | ||||||||||||
User: admin Company: Duo Security Inc. Integrity Level: HIGH Description: Duo Authentication for Windows Logon x64 Version: 4.3.0.4367 Modules
| |||||||||||||||
Total events
6 619
Read events
6 400
Write events
199
Delete events
20
Modification events
| (PID) Process: | (7788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000622D8B4AA6A4DB016C1E0000801E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7656) Setup64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000005ECA884AA6A4DB01E81D0000EC1D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005BBAE54AA6A4DB016C1E0000801E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005BBAE54AA6A4DB016C1E0000801E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000BB82EA4AA6A4DB016C1E0000801E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000BEC8F14AA6A4DB016C1E0000801E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7836) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006598C24BA6A4DB019C1E00003C1F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7836) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006598C24BA6A4DB019C1E0000B81E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7836) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006598C24BA6A4DB019C1E0000BC1E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
11
Suspicious files
10
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | duo-win-login-4.3.0.exe | C:\Users\admin\AppData\Local\Temp\DUOD0FE.tmp | executable | |
MD5:259FA7C9C00F1F5BA033054641BF177D | SHA256:5FFAA0653EF666580BDF344EAC2FB503C25607AA340144D0097DEA89AF008C78 | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\mbapreq.wxl | xml | |
MD5:4D2C8D10C5DCCA6B938B71C8F02CA8A8 | SHA256:C63DE5F309502F9272402587A6BE22624D1BC2FEACD1BD33FB11E44CD6614B96 | |||
| 7524 | DUOD0FE.tmp | C:\Windows\Temp\{66B2766A-5419-444F-902E-4A760F4D5350}\.cr\DUOD0FE.tmp | executable | |
MD5:4AA2CFAD99F91C8E6DC70D77D15916EB | SHA256:30DFF8AB1B30F13E4C6EAF3F05230C1A17AFD47C2D4D525D27D40ED1154F59B1 | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\1032\mbapreq.wxl | xml | |
MD5:074D5921AF07E6126049CB45814246ED | SHA256:B8E90E20EDF110AAAAEA54FBC8533872831777BE5589E380CFDD17E1F93147B5 | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\1038\mbapreq.wxl | xml | |
MD5:17FB605A2F02DA203DF06F714D1CC6DE | SHA256:55CF62D54EFB79801A9D94B24B3C9BA221C2465417A068950D40A67C52BA66EF | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\mbahost.dll | executable | |
MD5:C59832217903CE88793A6C40888E3CAE | SHA256:9DFA1BC5D2AB4C652304976978749141B8C312784B05CB577F338A0AA91330DB | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\1028\mbapreq.wxl | xml | |
MD5:1D4B831F77EFEC96FFBC70BC4B59B8B5 | SHA256:1B93556F07C35AC0564D57E0743CCBA231950962C6506C8D4A74A31CD66FD04C | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\mbapreq.png | image | |
MD5:A356956FD269567B8F4612A33802637B | SHA256:A401A225ADDAF89110B4B0F6E8CF94779E7C0640BCDD2D670FFCF05AAB0DAD03 | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\1060\mbapreq.wxl | xml | |
MD5:5836F0C655BDD97093F68AAF69AB2BAB | SHA256:C015247D022BDC108B4FFCAE89CB55D1E313034D7E6EED18744C1BB55F108F8C | |||
| 7548 | DUOD0FE.tmp | C:\Windows\Temp\{3C75FB3A-256D-4DBF-A80E-E3C49722FA3C}\.ba\1043\mbapreq.wxl | xml | |
MD5:67F28BCDB3BA6774CD66AA198B06FF38 | SHA256:226B778604236931B4AE45F6F272586C884A11517444A34BF45CD5CAE49BE62E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4040 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7656 | Setup64.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7656 | Setup64.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7656 | Setup64.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuaoG9ZqTY4lYojhO9jYhM%3D | unknown | — | — | whitelisted |
4040 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.7.1.246:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6480 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |