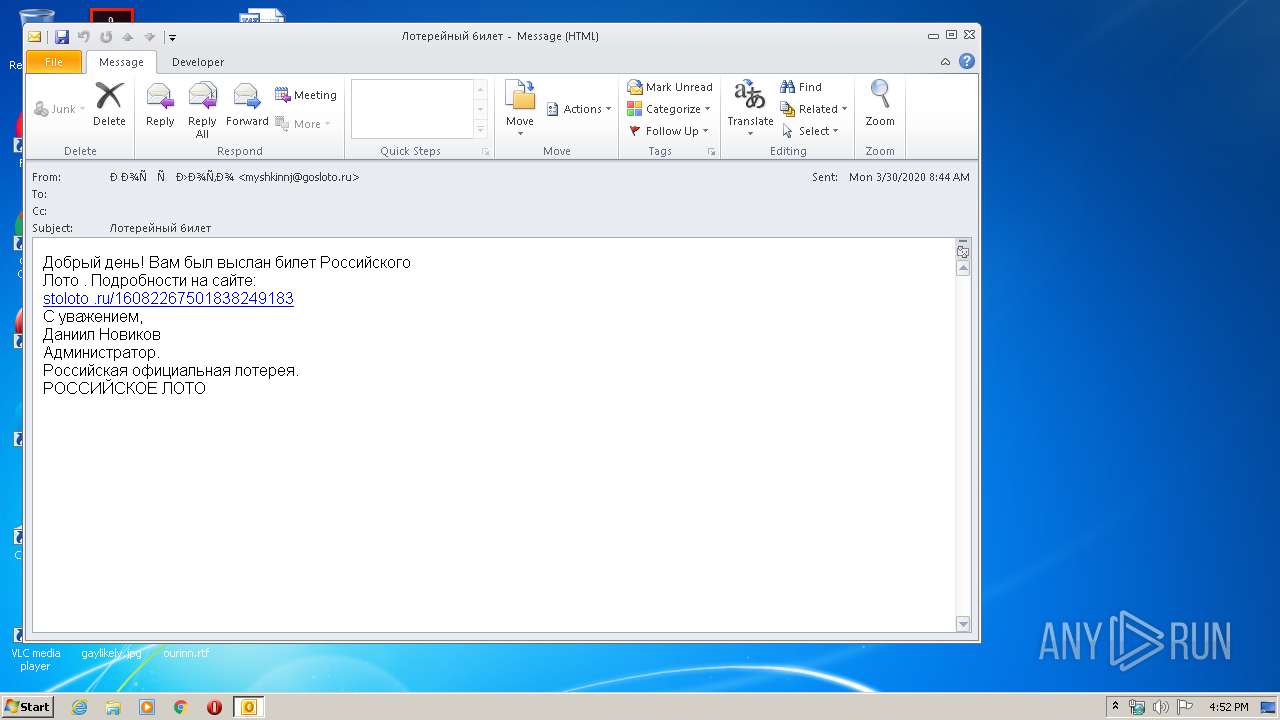
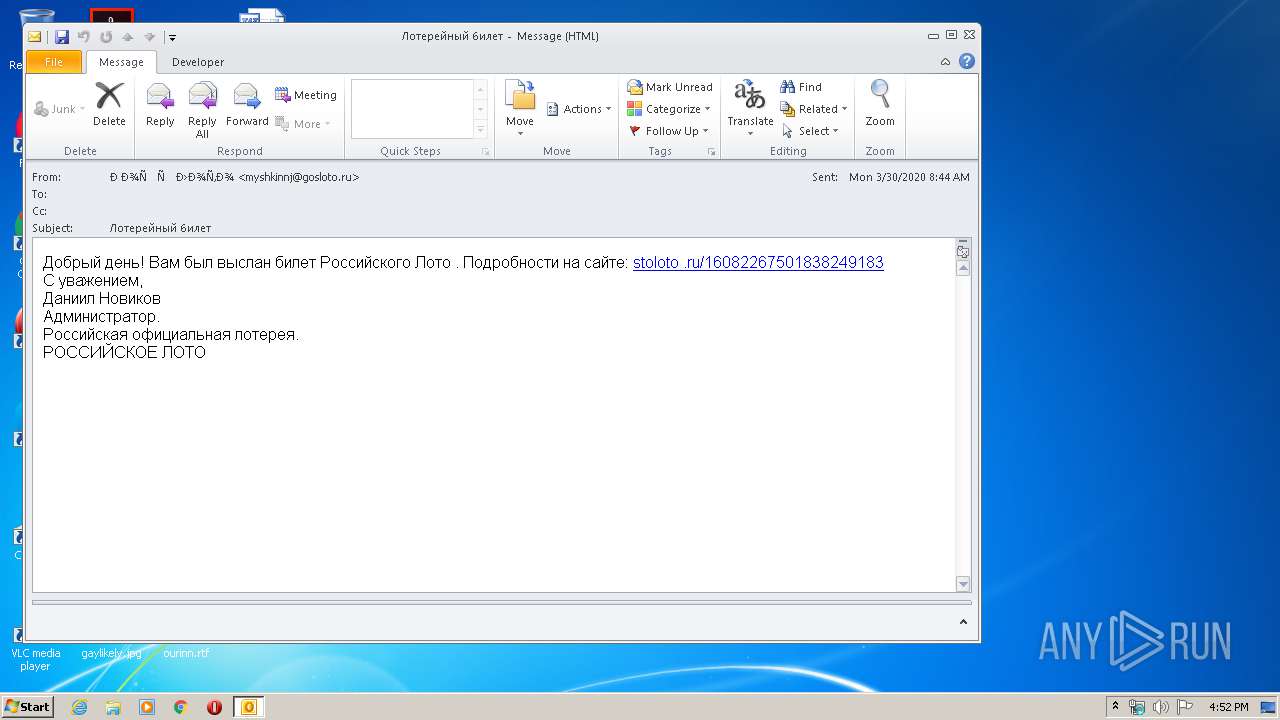
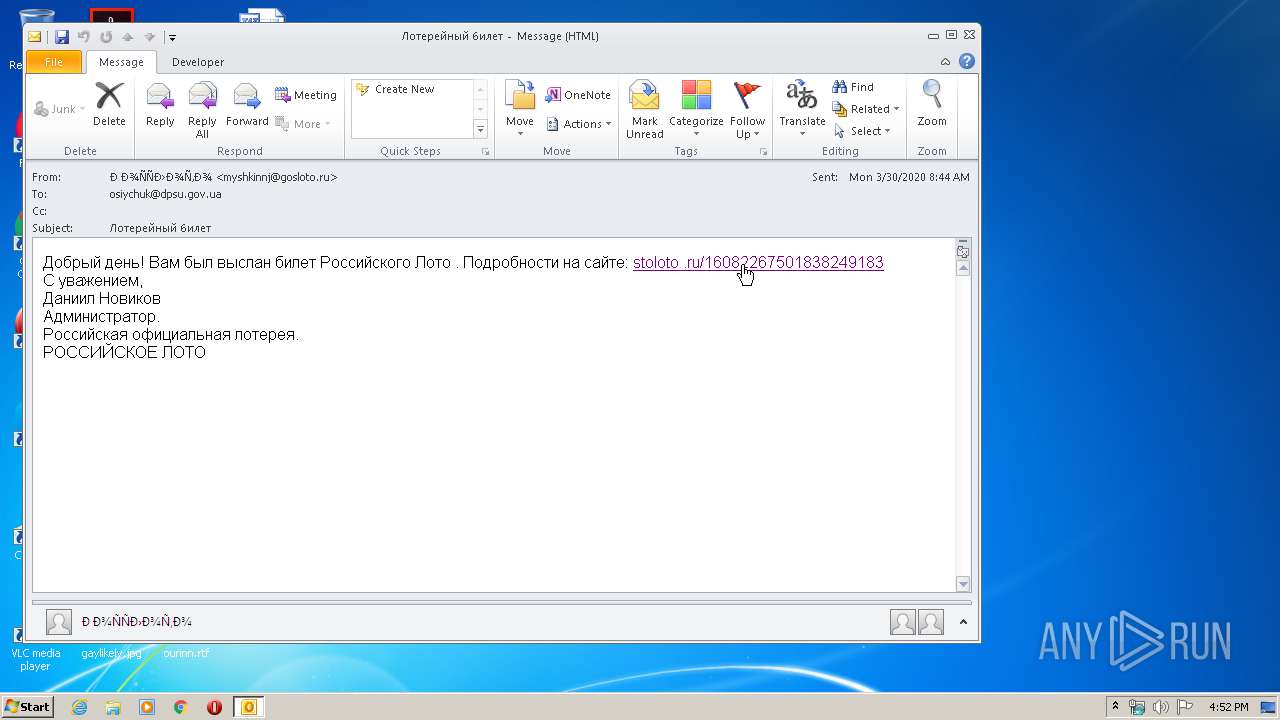
| File name: | Лотерейный билет.eml |
| Full analysis: | https://app.any.run/tasks/04cd0846-285e-4736-9025-56fc54e6cbce |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 15:51:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, UTF-8 Unicode text |
| MD5: | 4A208B33104FFD964DD03C62647FA8A9 |
| SHA1: | 4C071E42970934F944D1D17A14D73E3B99004CCA |
| SHA256: | 67E9D9BABA822D133D94A930ADBCA2055C821FB93D1151177F1209B361871430 |
| SSDEEP: | 48:STqeqw+KqtM+1LnsU5u1McJO3W9fvVT55RlbjZp9TWUiQLqyLRb+bVy40C/TsiB/:2qeqwQxjX9hEfdd5HbjHgUiQLDwYLE |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3000)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3000)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3000)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2612)
INFO
Application launched itself
- iexplore.exe (PID: 1760)
Reads Internet Cache Settings
- iexplore.exe (PID: 1760)
- iexplore.exe (PID: 3464)
Changes internet zones settings
- iexplore.exe (PID: 1760)
Reads internet explorer settings
- iexplore.exe (PID: 3464)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3000)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3464)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 3464)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2612)
- iexplore.exe (PID: 3464)
Changes settings of System certificates
- iexplore.exe (PID: 1760)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1760)
Reads settings of System Certificates
- iexplore.exe (PID: 1760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1760 | "C:\Program Files\Internet Explorer\iexplore.exe" http://pgvquantum.com/wp-content/themes/twentysixteen-child/template-parts/footer/3/ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2612 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3000 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Лотерейный билет.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1760 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 383
Read events
2 250
Write events
1 028
Delete events
105
Modification events
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3000) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
280
Text files
349
Unknown types
149
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8862.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1760 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabC57B.tmp | — | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarC57C.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3000 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 3000 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_C71056DEF74B014BA1351B690B4A89AD.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 3000 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 3000 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_3897D8D430ED3A46B85B7B56E9C8E89B.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
153
TCP/UDP connections
319
DNS requests
129
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3464 | iexplore.exe | GET | 302 | 112.213.89.7:80 | http://pgvquantum.com/wp-content/themes/twentysixteen-child/template-parts/footer/3/ | VN | — | — | suspicious |
3000 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAxOExpBxyqawIEpLt5RW6E%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAfPgrgEmbcjJexpgYUf%2BBU%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEA9Fw%2BeisXO35WtYpu%2BqoDw%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEA8Byg3xePJ2xAXD21b7Wg8%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 304 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCCwQAAAAAATGJxkTJ | US | der | 1.48 Kb | whitelisted |
3464 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAfPgrgEmbcjJexpgYUf%2BBU%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8DYx | US | der | 1.49 Kb | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAfPgrgEmbcjJexpgYUf%2BBU%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3464 | iexplore.exe | 217.69.139.36:443 | news.mail.ru | Limited liability company Mail.Ru | RU | unknown |
3000 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3464 | iexplore.exe | 112.213.89.7:80 | pgvquantum.com | SUPERDATA | VN | malicious |
3464 | iexplore.exe | 217.69.139.33:443 | news.mail.ru | Limited liability company Mail.Ru | RU | unknown |
1760 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3464 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3464 | iexplore.exe | 217.69.139.14:443 | likemore-go.imgsmail.ru | Limited liability company Mail.Ru | RU | unknown |
3464 | iexplore.exe | 94.100.180.36:443 | cp-filin.mail.ru | Limited liability company Mail.Ru | RU | unknown |
3464 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3464 | iexplore.exe | 217.69.139.165:443 | static.pulse.mail.ru | Limited liability company Mail.Ru | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
pgvquantum.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
news.mail.ru |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
likemore-go.imgsmail.ru |
| whitelisted |
mcdn.imgsmail.ru |
| unknown |
rs.mail.ru |
| whitelisted |