| File name: | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef |
| Full analysis: | https://app.any.run/tasks/30471776-a194-4ddd-acbc-ae2a0157bca0 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 12:36:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 19 sections |
| MD5: | 264216FC86A0B123A37B234478D83158 |
| SHA1: | 7B1788410590F47E5654C11CA8B63CC47887D276 |
| SHA256: | 67DF661FF72FC94F477BD55F43AD52192B05EA73EA50FDB041AFB708FA4171EF |
| SSDEEP: | 24576:JpRRwPdVyxuWSgYOqO3drRPcu6RyyppTipOlb+Ec0xMkl81sU3AoZlMXWKIy+z+U:jRRwPdVyxuWSgYOnPcu44lMXWKIy+z+U |
MALICIOUS
Changes Windows Defender settings
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Adds path to the Windows Defender exclusion list
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Create files in the Startup directory
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
SUSPICIOUS
Reads security settings of Internet Explorer
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7812)
Reads the date of Windows installation
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7812)
Application launched itself
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7812)
Executable content was dropped or overwritten
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Script adds exclusion path to Windows Defender
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Starts POWERSHELL.EXE for commands execution
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Starts itself from another location
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Connects to unusual port
- EdgeUpdate.exe (PID: 7148)
INFO
Checks supported languages
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7812)
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
- EdgeUpdate.exe (PID: 7148)
Reads the computer name
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7812)
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Process checks computer location settings
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7812)
Creates files in the program directory
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8060)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8060)
Creates files or folders in the user directory
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Auto-launch of the file from Startup directory
- Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe (PID: 7980)
Reads the software policy settings
- slui.exe (PID: 1180)
Checks proxy server information
- slui.exe (PID: 1180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:09 18:14:43+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.4 |
| CodeSize: | 858112 |
| InitializedDataSize: | 1139712 |
| UninitializedDataSize: | 3584 |
| EntryPoint: | 0x1125 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
134
Monitored processes
8
Malicious processes
2
Suspicious processes
0
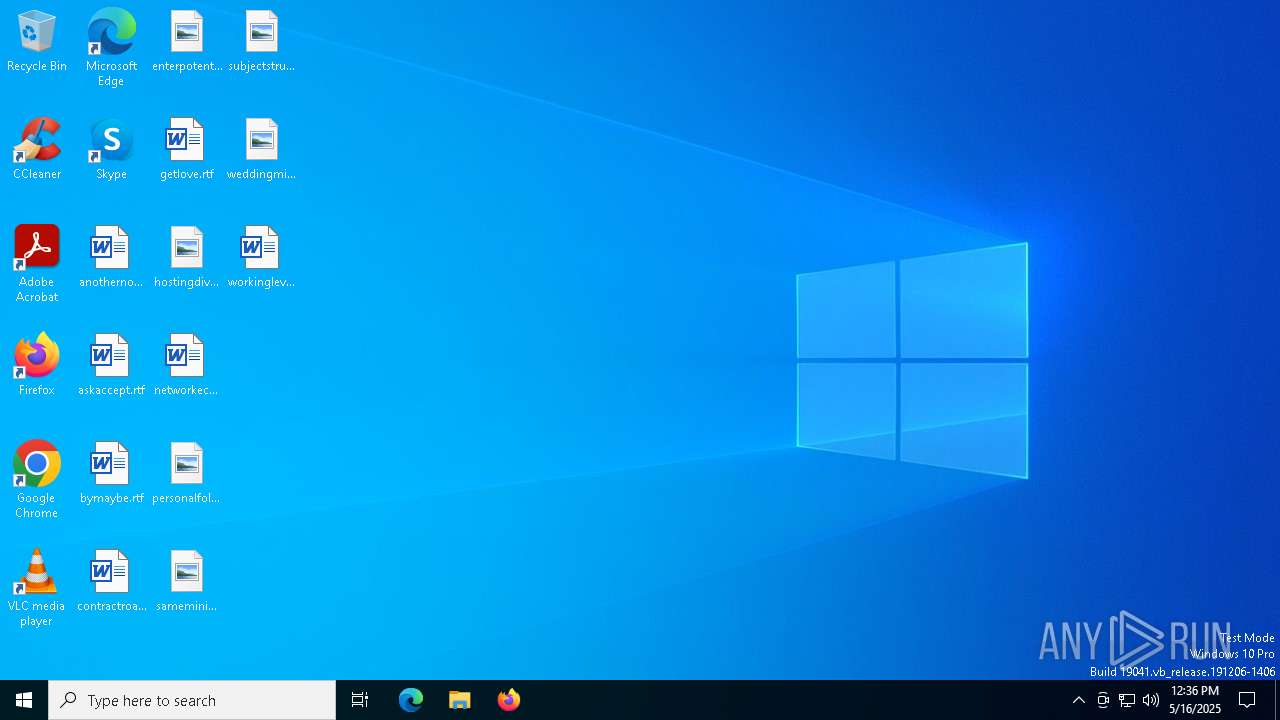
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7148 | "C:\ProgramData\Microsoft\EdgeUpdate\EdgeUpdate.exe" | C:\ProgramData\Microsoft\EdgeUpdate\EdgeUpdate.exe | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7812 | "C:\Users\admin\Desktop\Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe" | C:\Users\admin\Desktop\Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7980 | "C:\Users\admin\Desktop\Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe" 35.158.159.254 18309 5000 | C:\Users\admin\Desktop\Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 8008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8060 | powershell.exe -Command "Add-MpPreference -ExclusionPath 'C:\ProgramData\Microsoft\EdgeUpdate\EdgeUpdate.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8068 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 274
Read events
9 274
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8060 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_utql0tel.vn2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7980 | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | C:\ProgramData\Microsoft\EdgeUpdate\EdgeUpdate.exe | executable | |
MD5:264216FC86A0B123A37B234478D83158 | SHA256:67DF661FF72FC94F477BD55F43AD52192B05EA73EA50FDB041AFB708FA4171EF | |||
| 8060 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fck2csmk.ocb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8060 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D11B94AD0559B94C1032C792E9141219 | SHA256:2E7497D7915C2105AB9AFCBE87120A6F1C85AEA9A8A9274141829094FD398C35 | |||
| 7980 | Sigmanly_67df661ff72fc94f477bd55f43ad52192b05ea73ea50fdb041afb708fa4171ef.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\EdgeUpdate.lnk | binary | |
MD5:BE1AA0D92A633D0D41E46EBF0E715BD8 | SHA256:71AA52EE3203F445762CB08CC2318F3F4C22D911BECB44984460AA94FAF81DAF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
55
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 23.216.77.26:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 23.216.77.26:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
904 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7148 | EdgeUpdate.exe | 35.158.159.254:18309 | — | AMAZON-02 | DE | unknown |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |