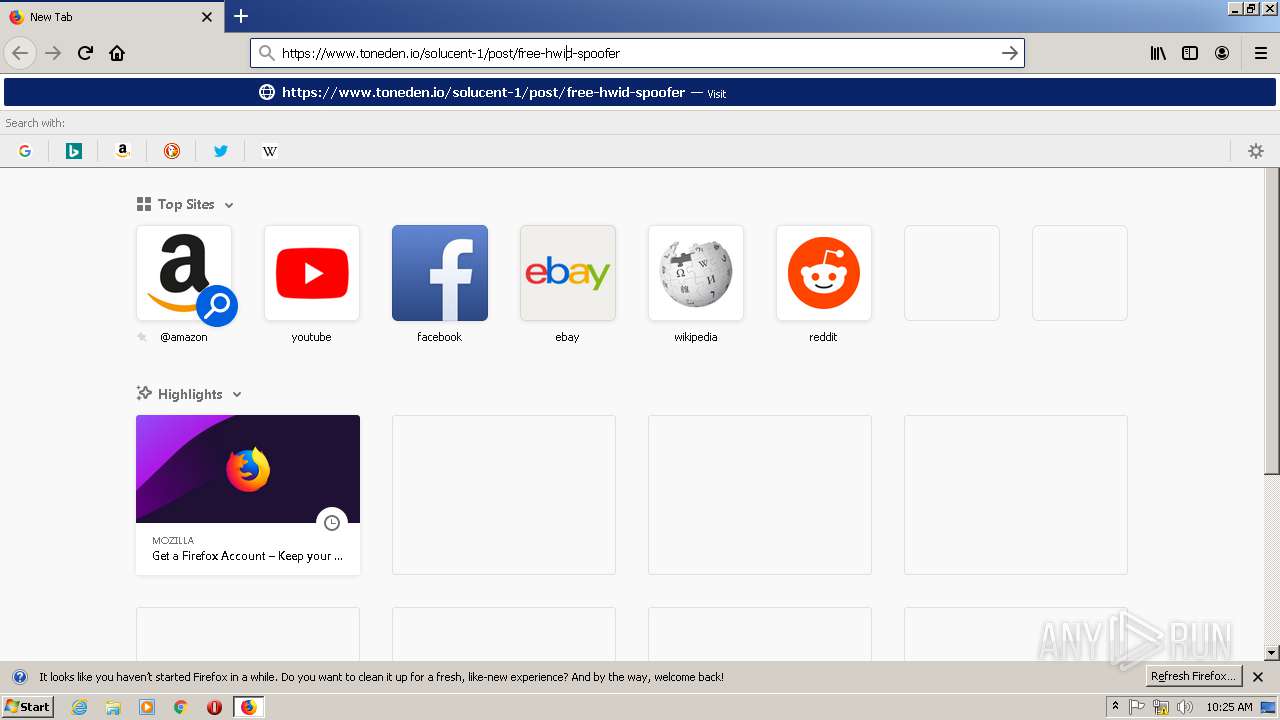
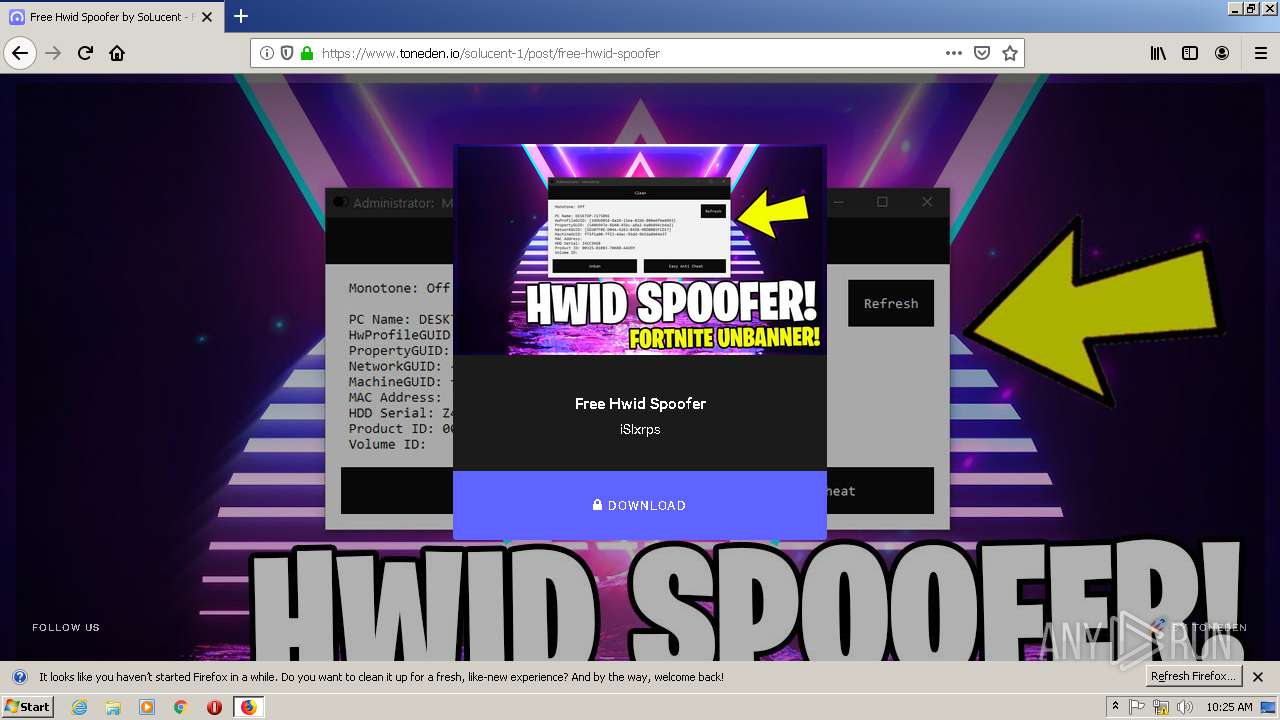
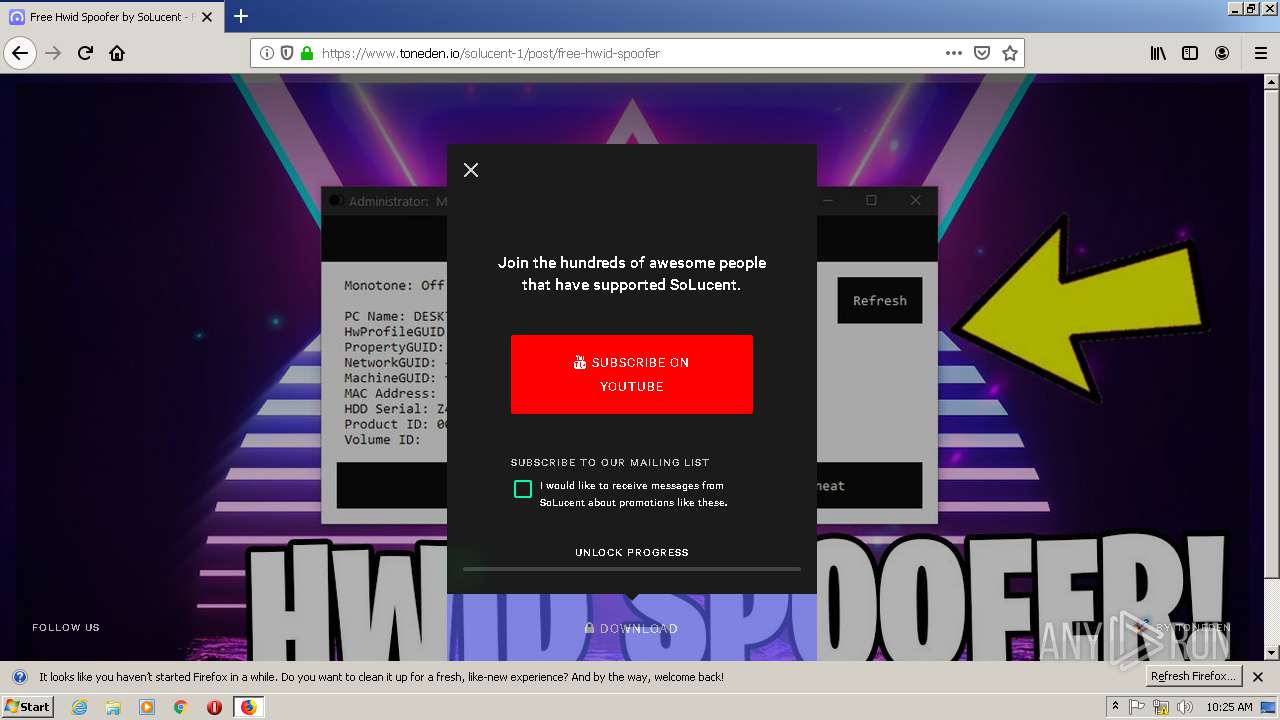
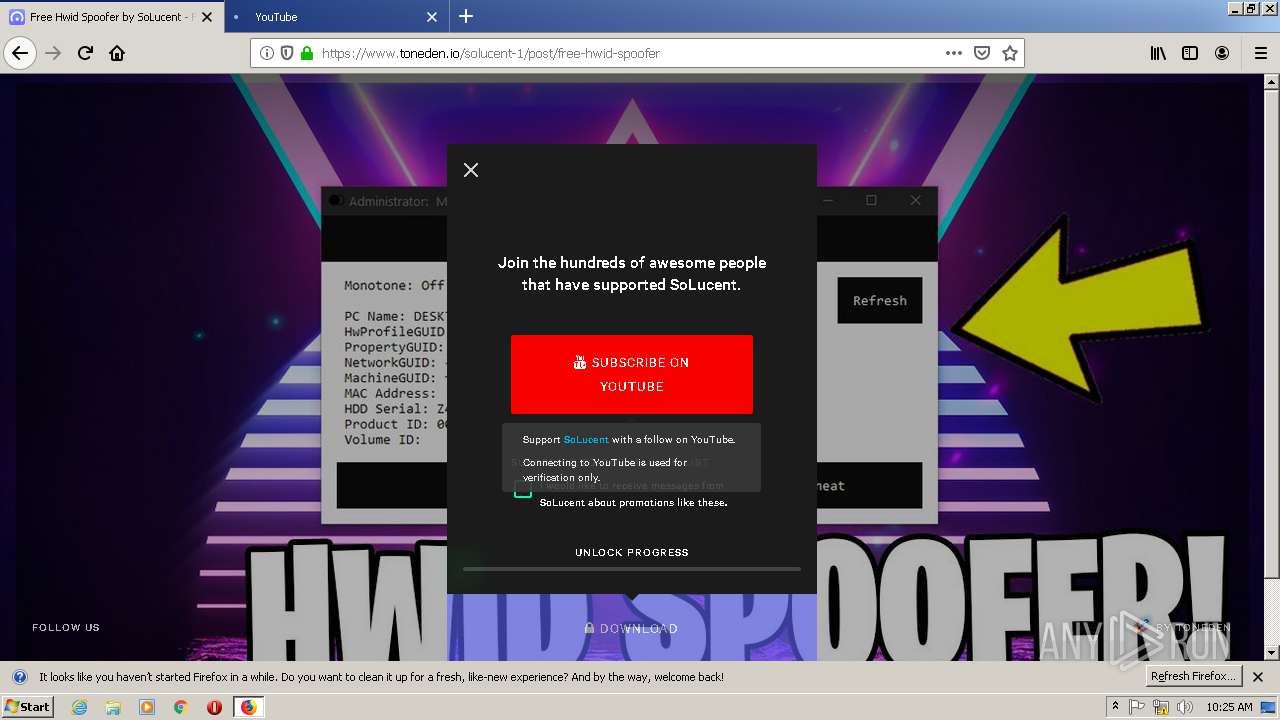
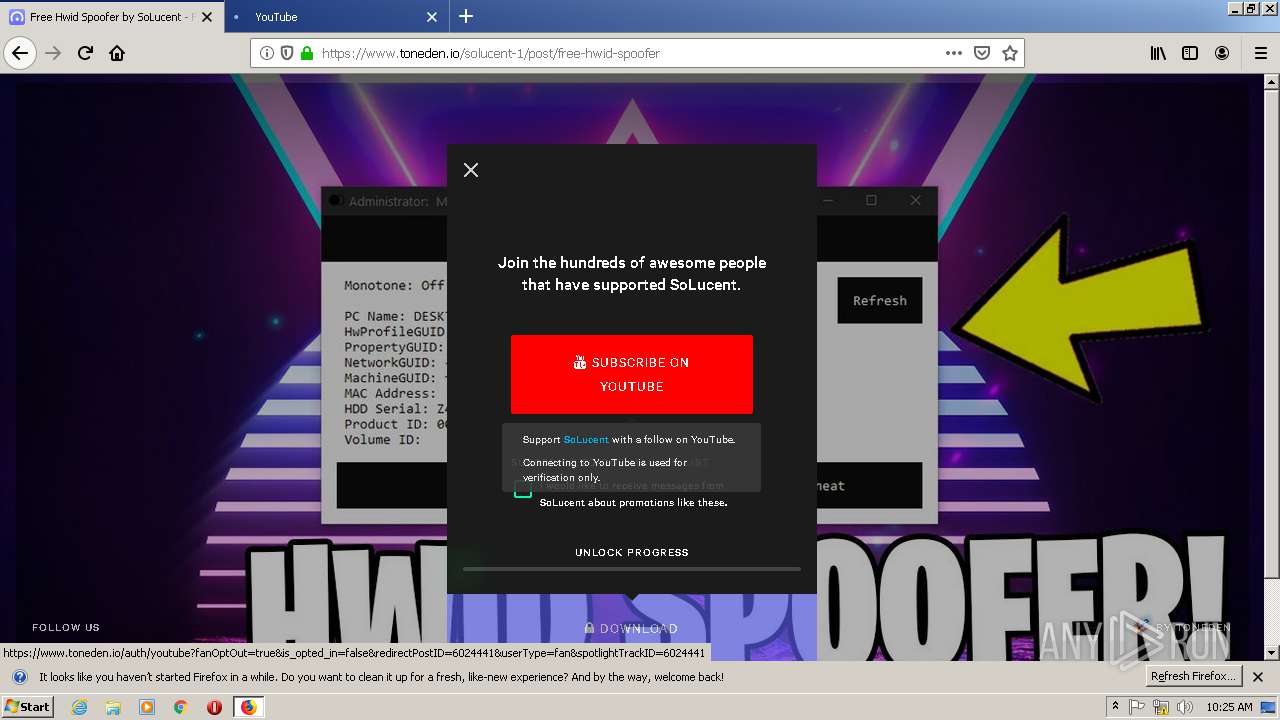
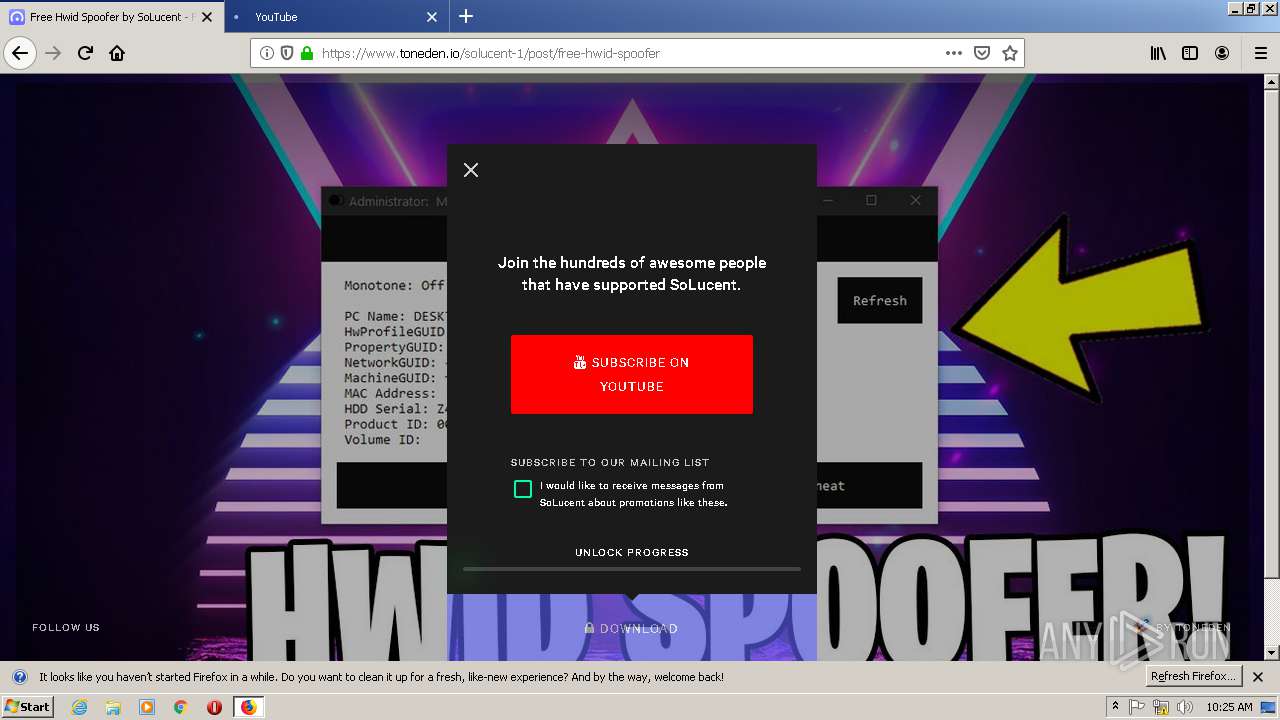
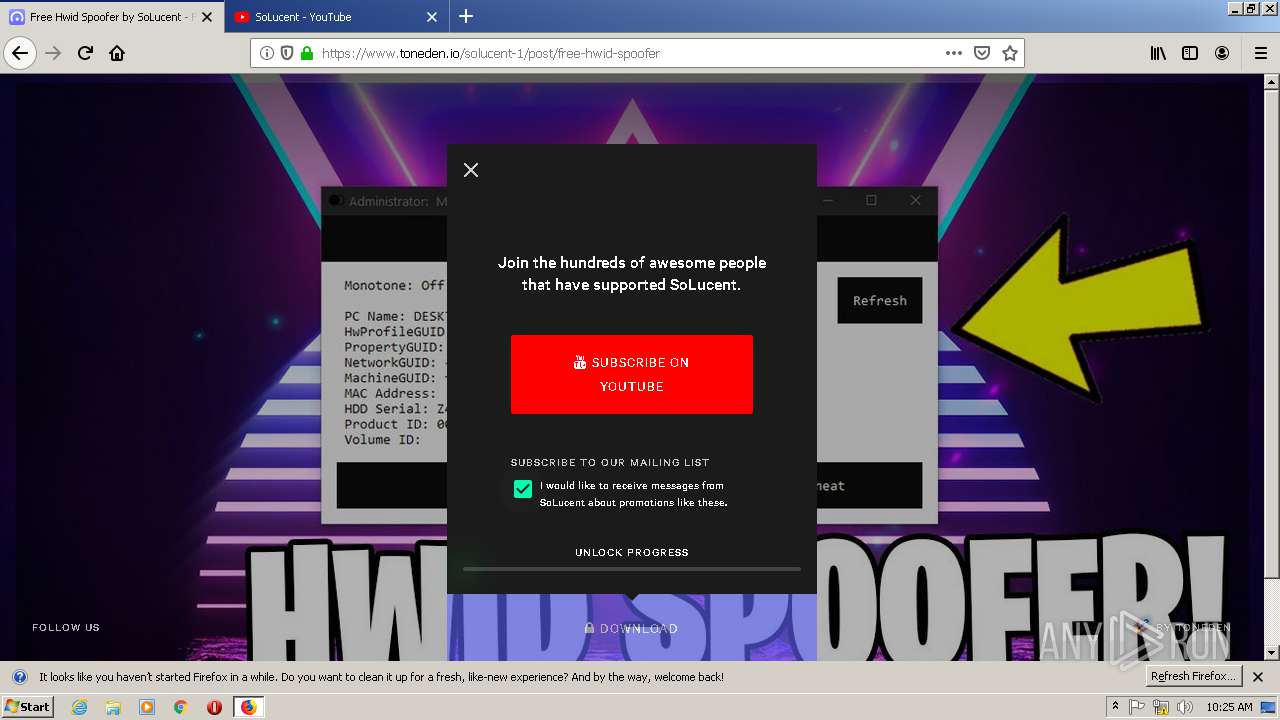
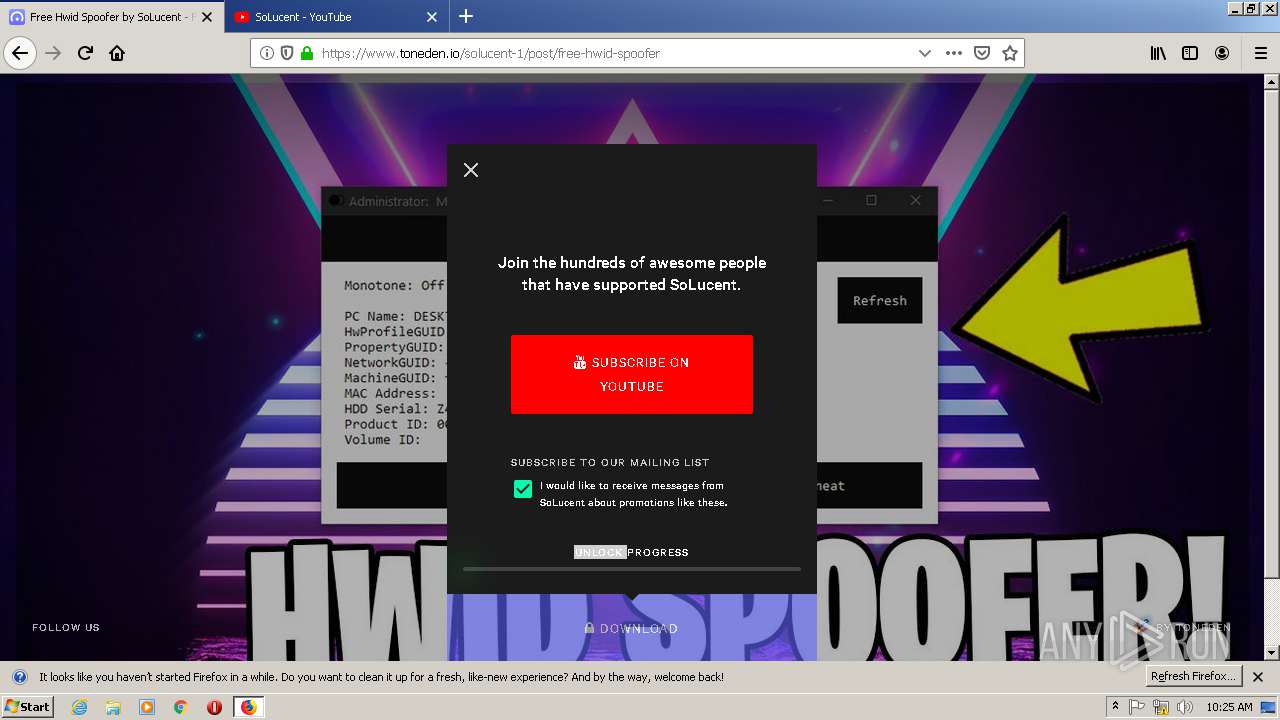
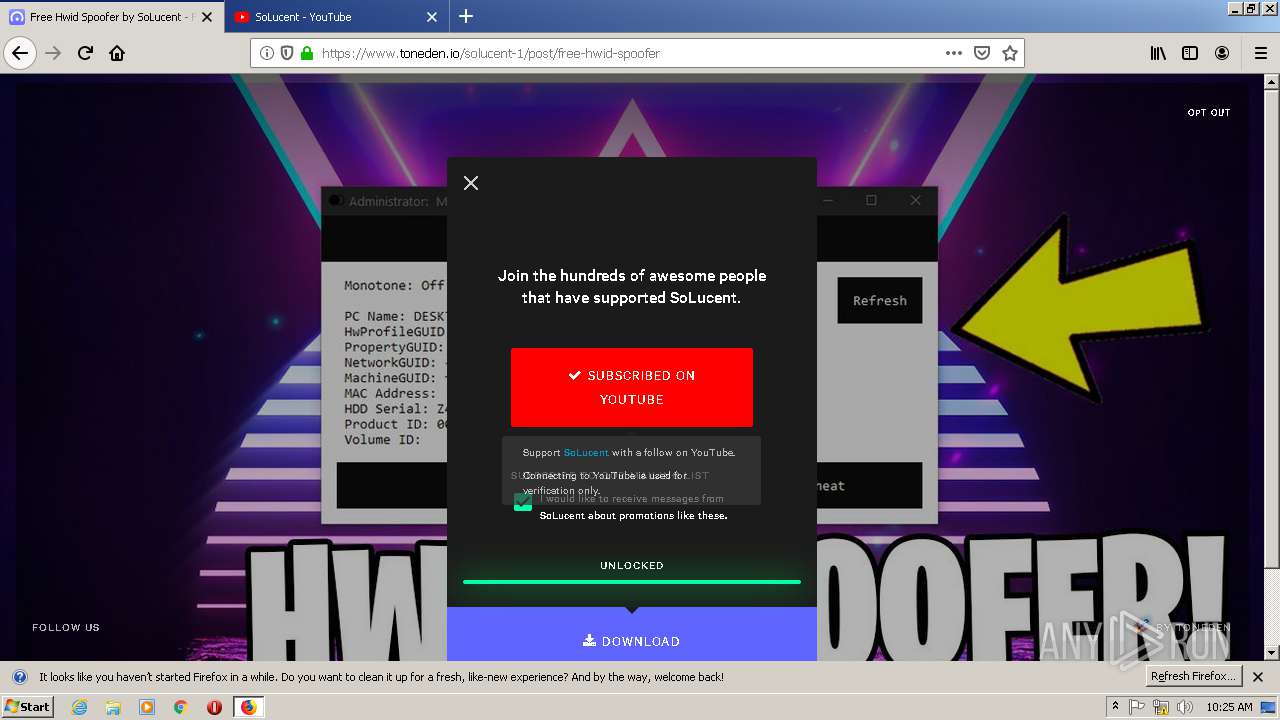
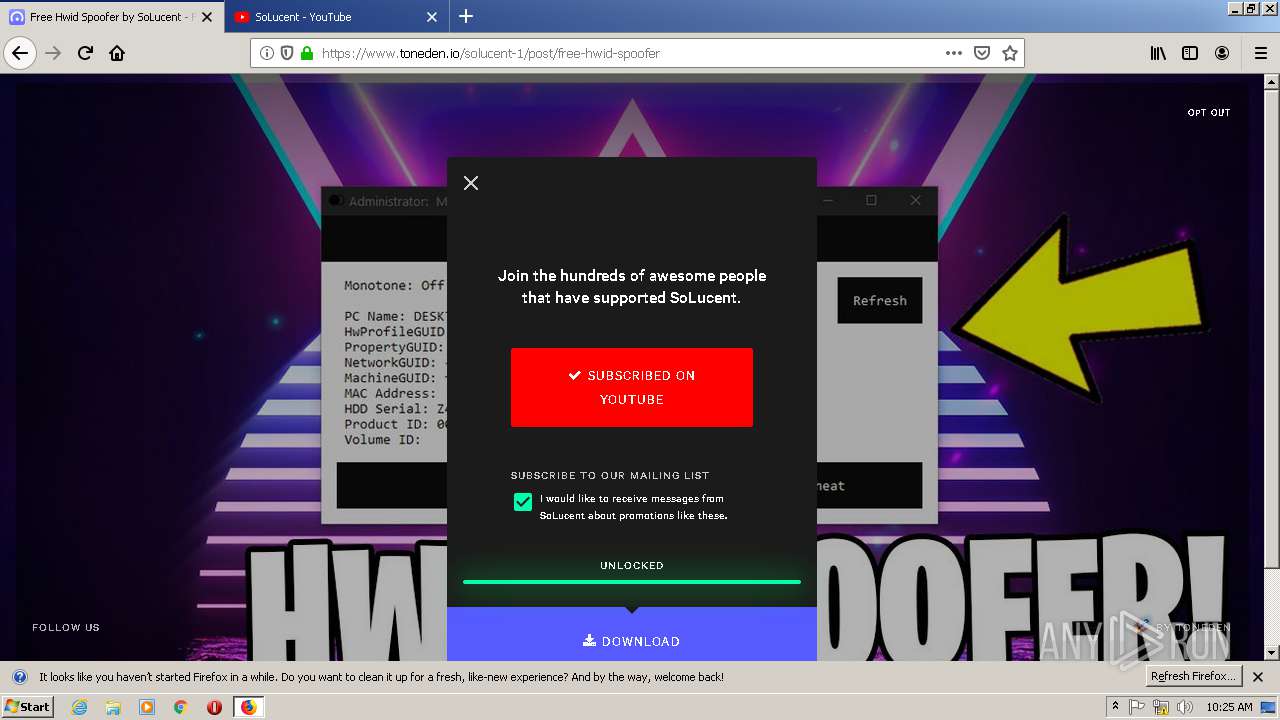
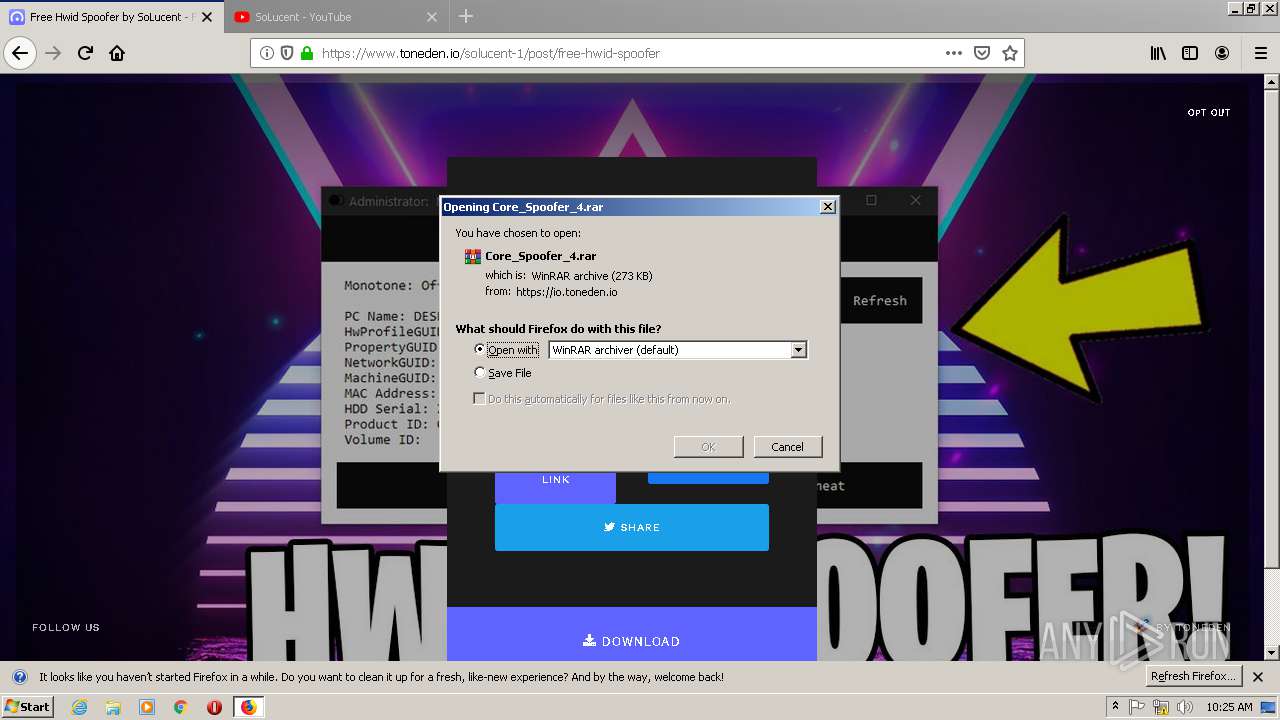
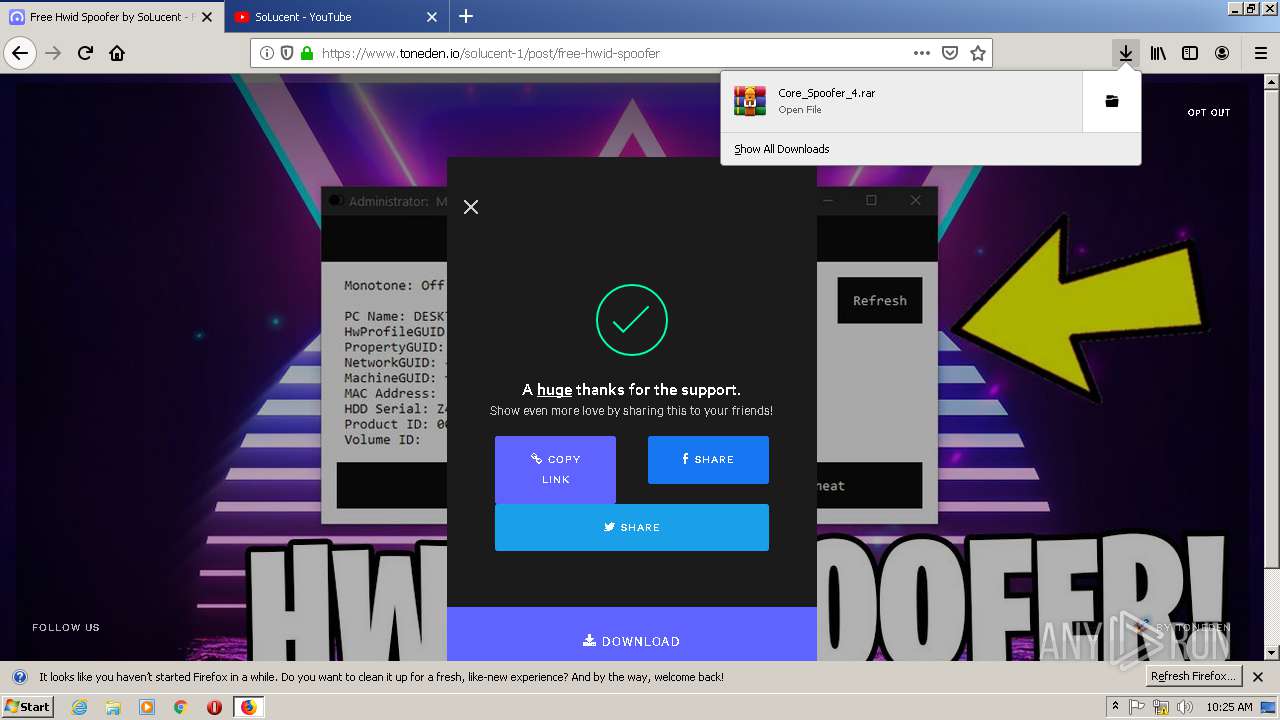
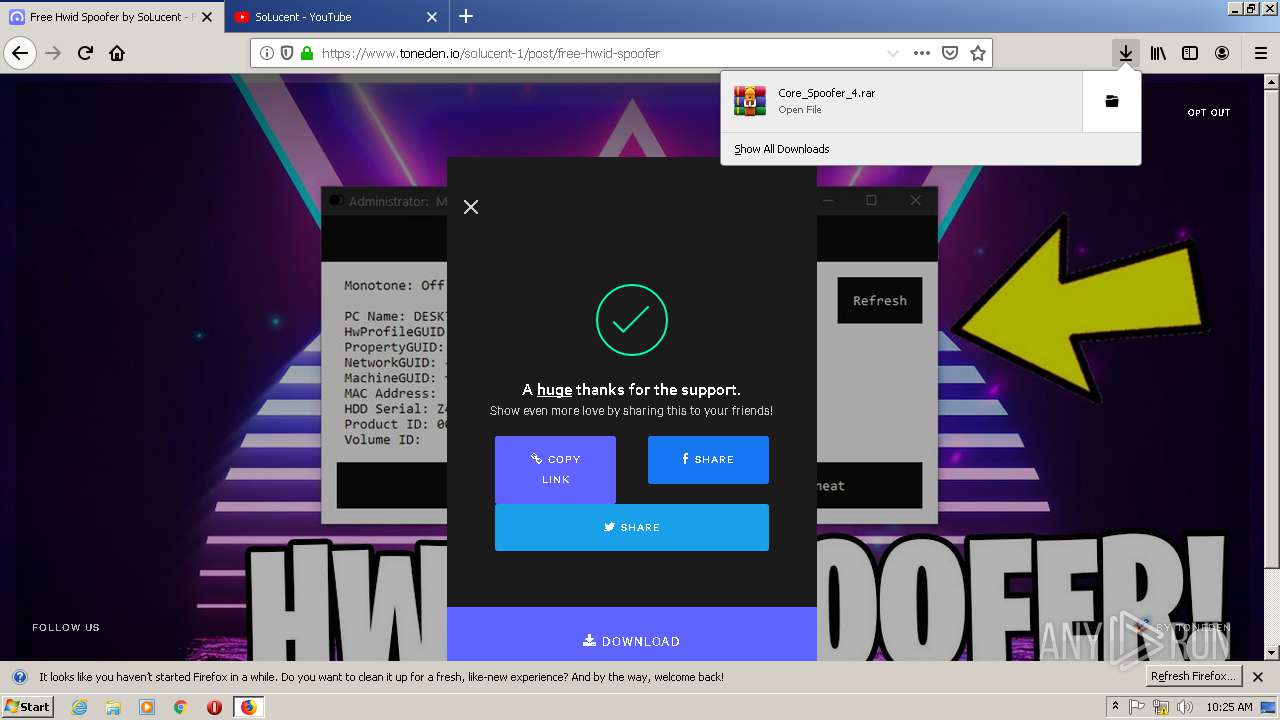
| download: | free-hwid-spoofer |
| Full analysis: | https://app.any.run/tasks/d4b23c00-00ab-487f-b34e-cc4c52b3cfb0 |
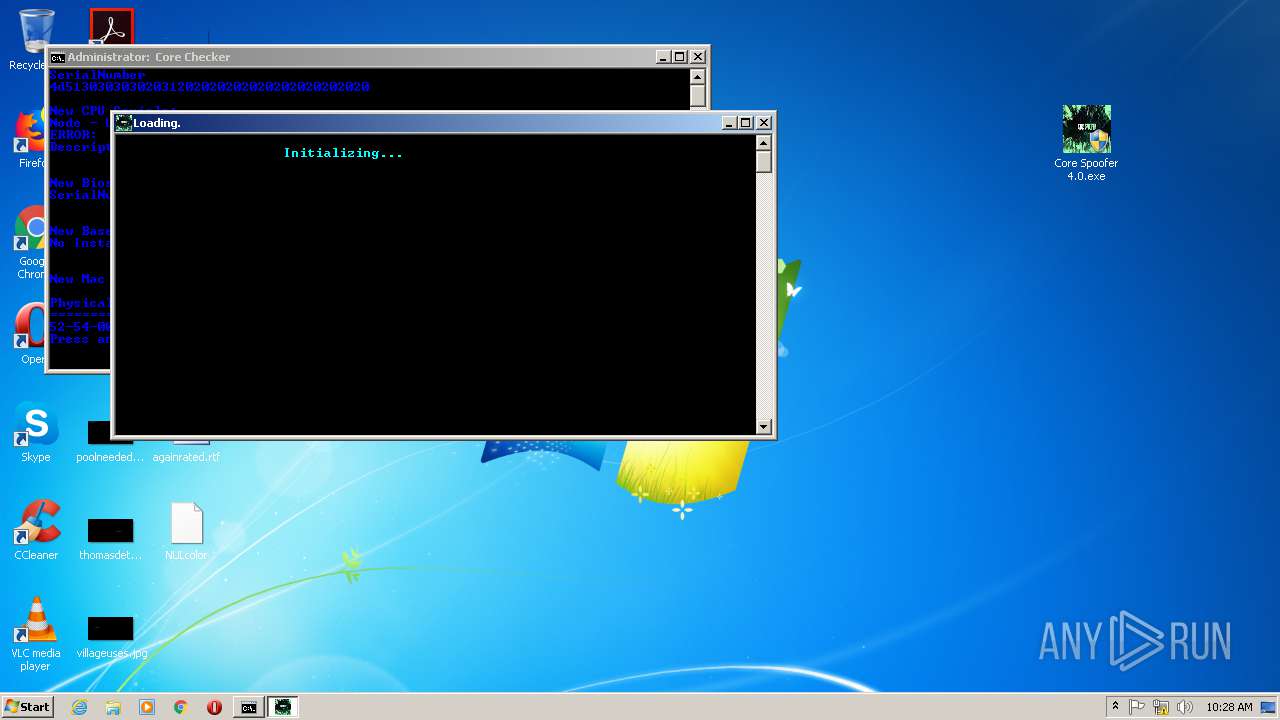
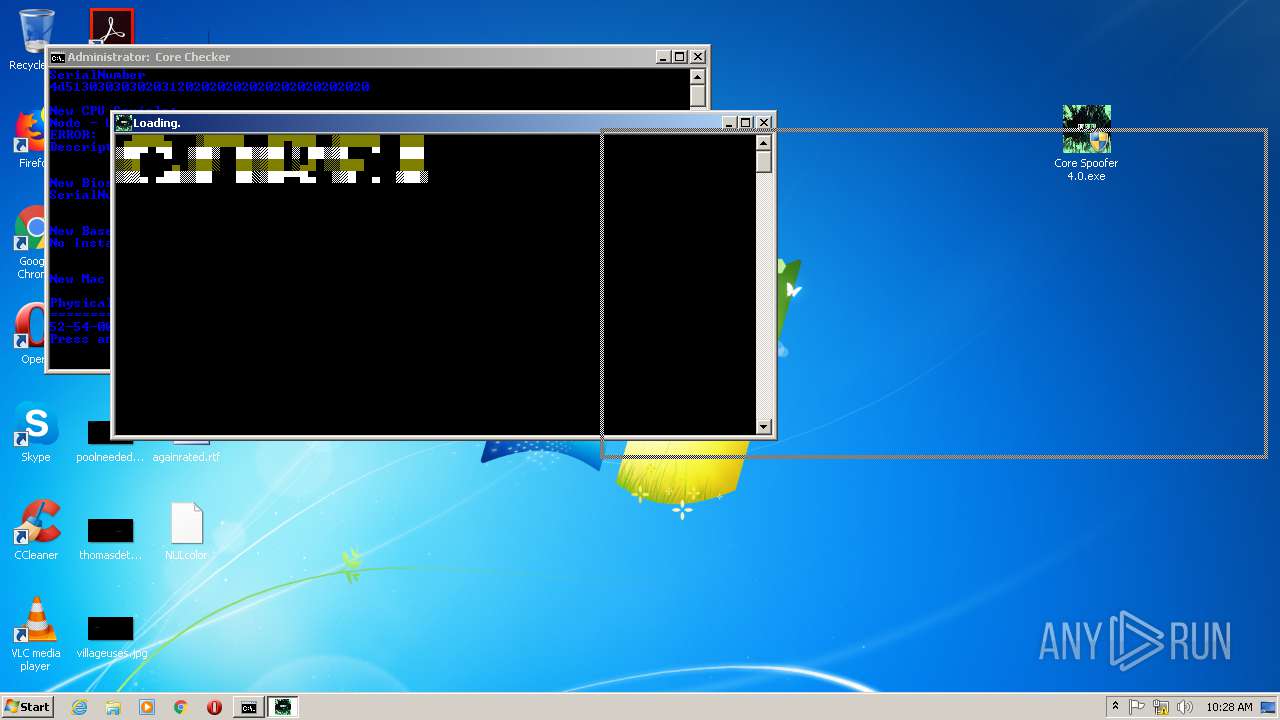
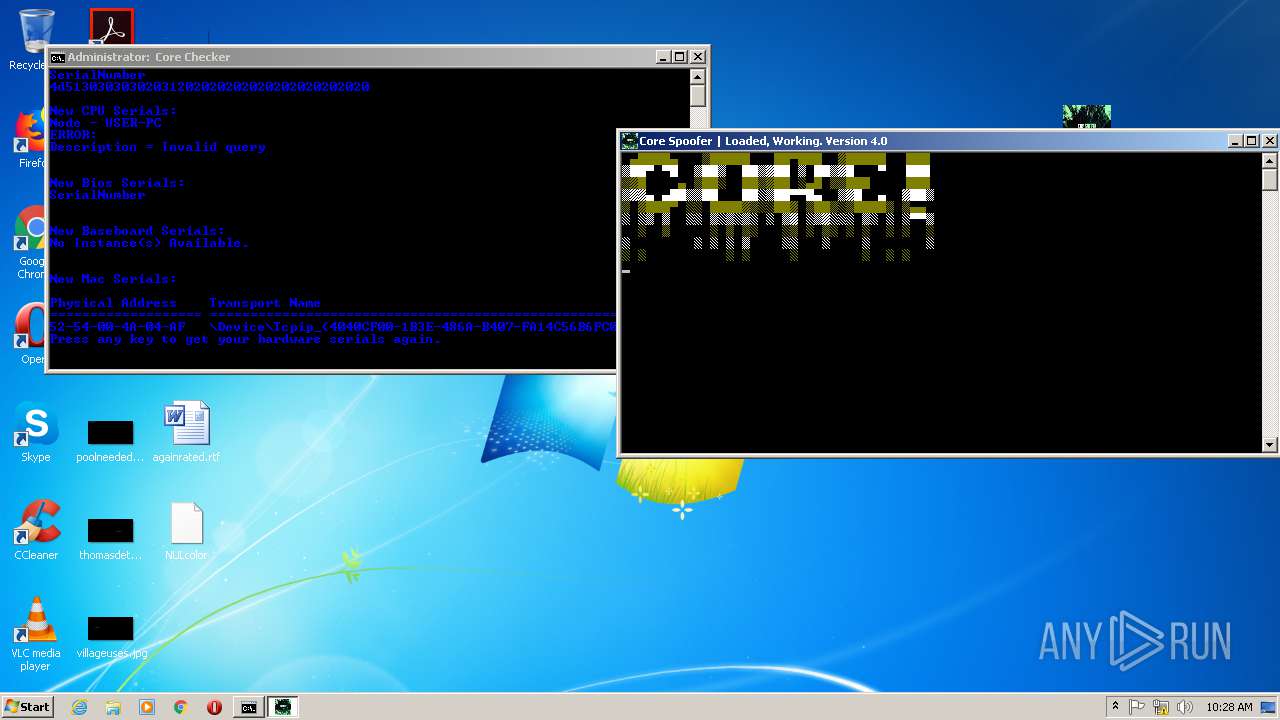
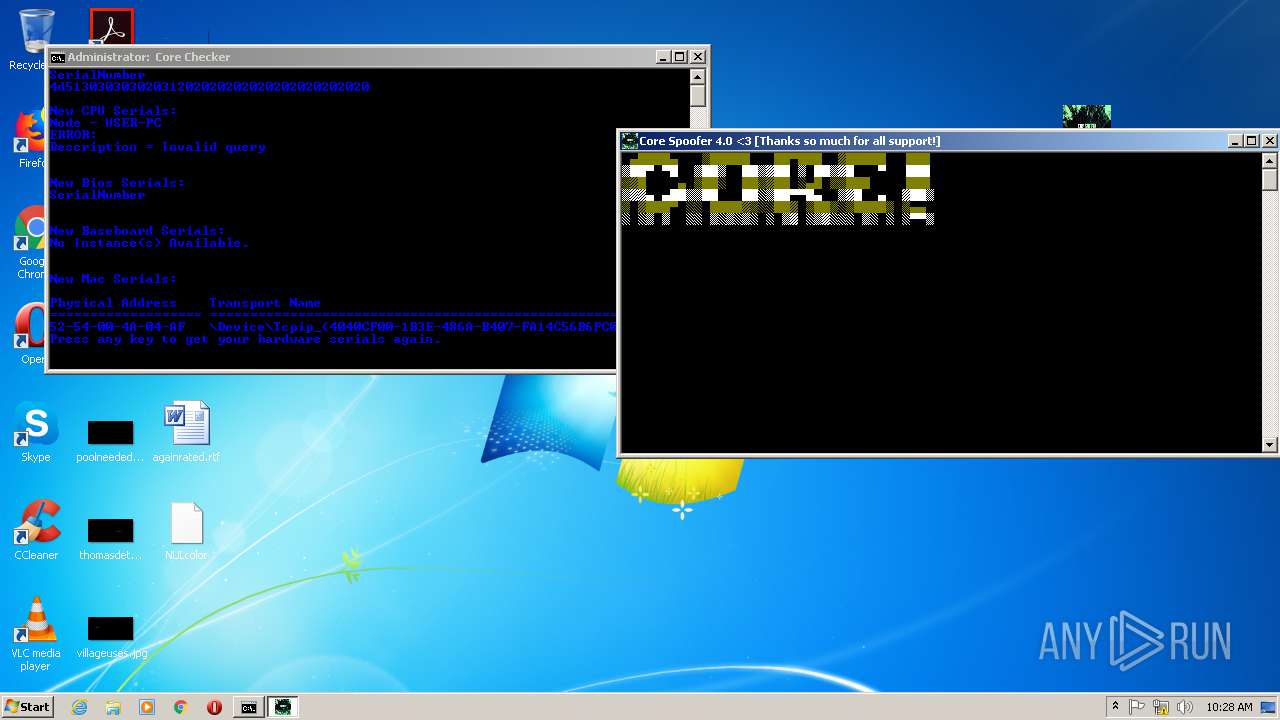
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2020, 09:23:50 |
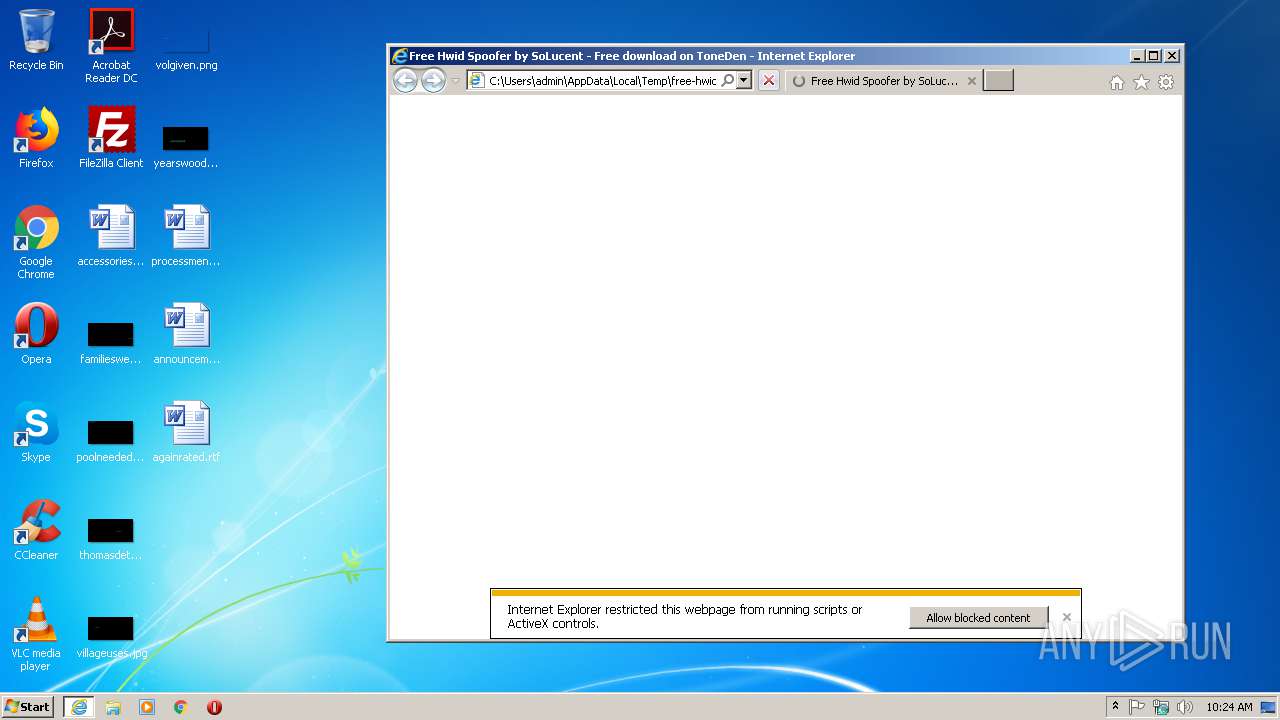
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | DAF94AF77159551D0BE6CECFA2288521 |
| SHA1: | 90719C90DC31C467E13D751F66410ECBDD3AD2DC |
| SHA256: | 67D52AA0C84B84C9D698D27BBEF8EE22AE130179CDD7723BE9555C37284AA747 |
| SSDEEP: | 192:wyDqqW1f+hQl8lo8Vys8hGa7jJE/4RNTn0FVEQBUQEvd6oWlKz19:ELf+/N4D1Xy1vQ6S |
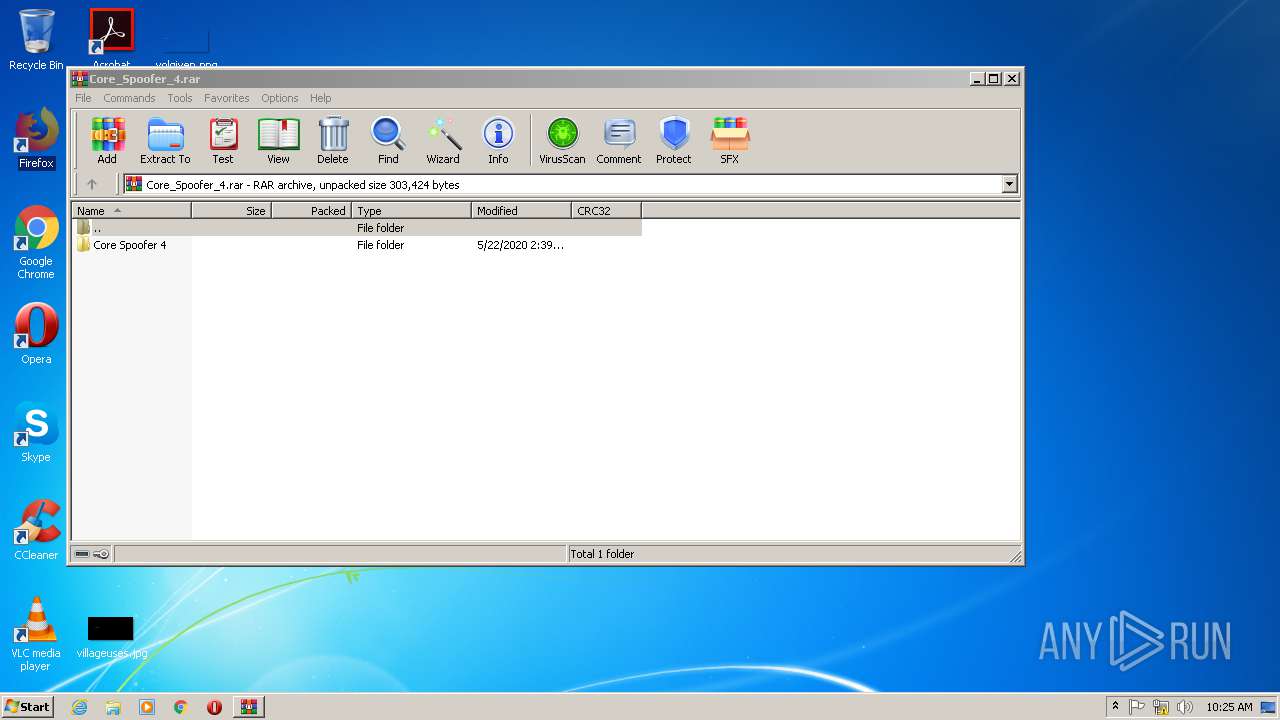
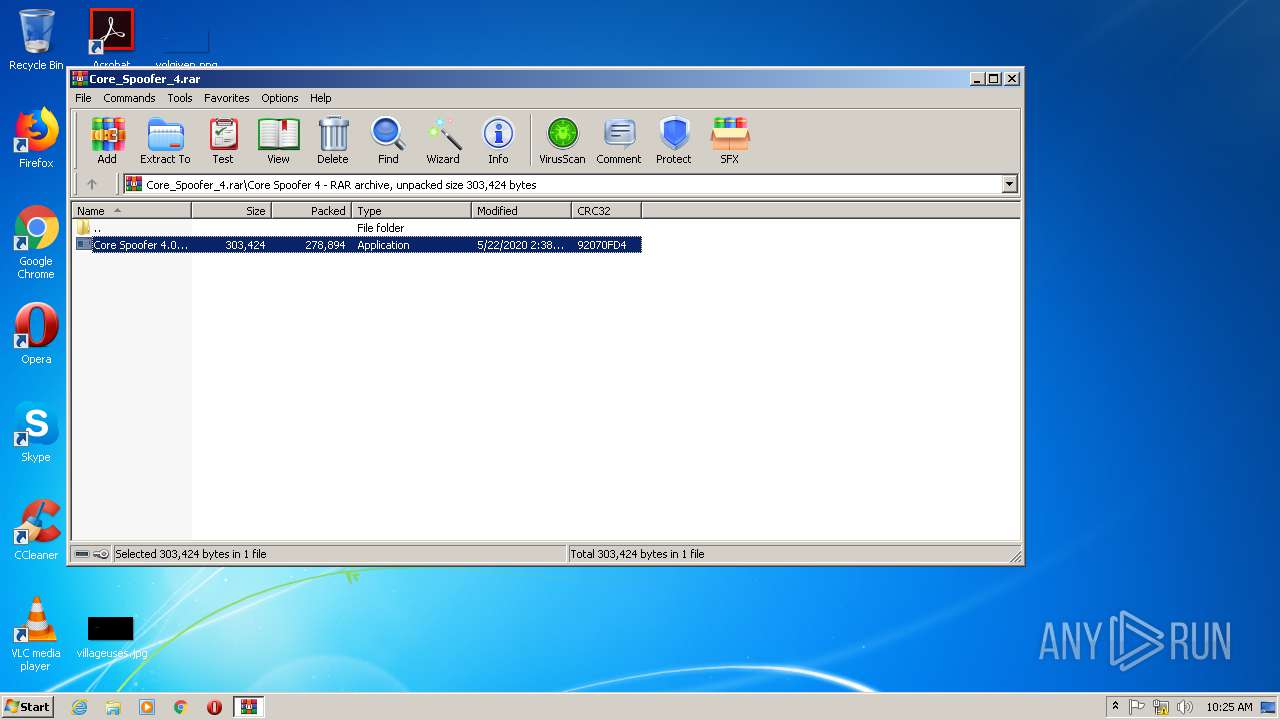
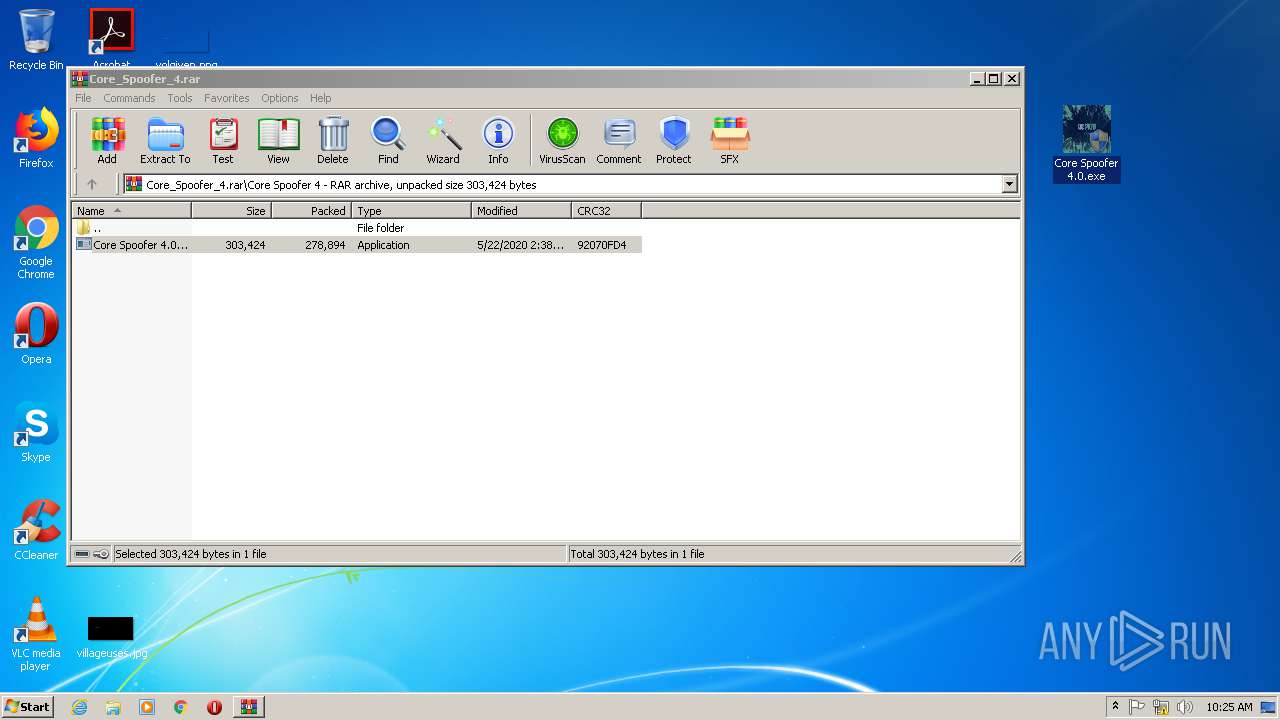
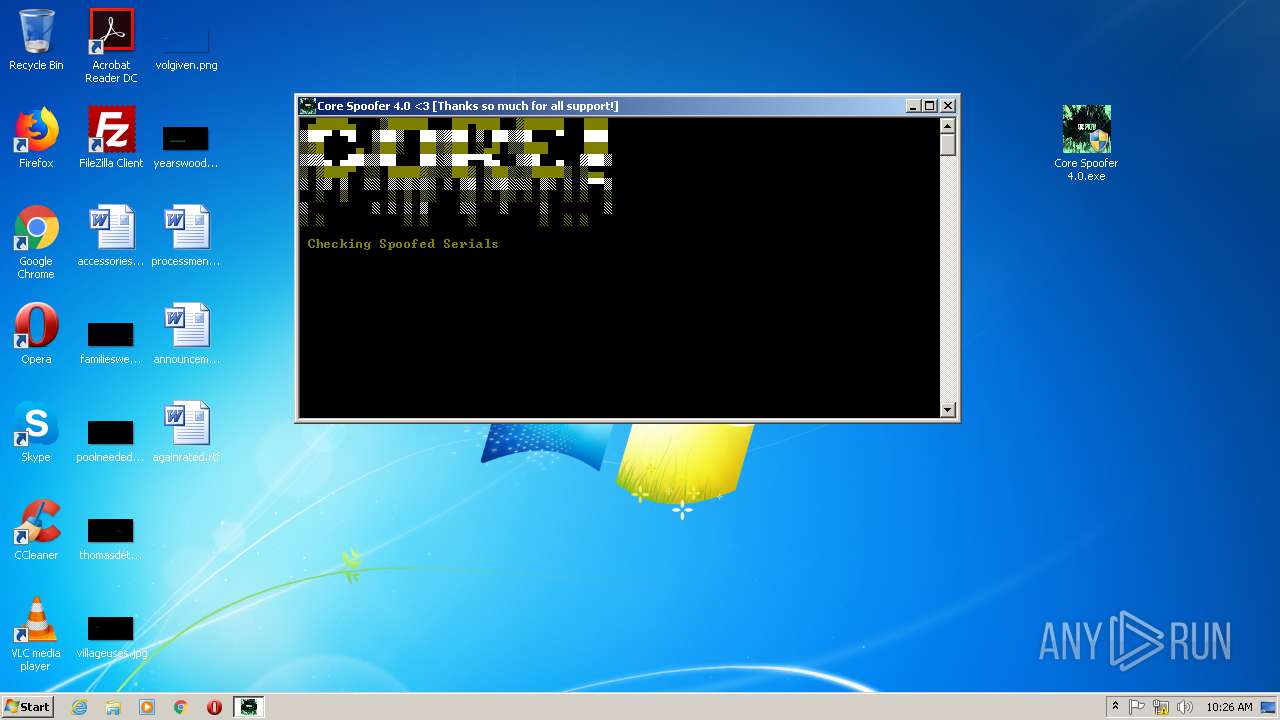
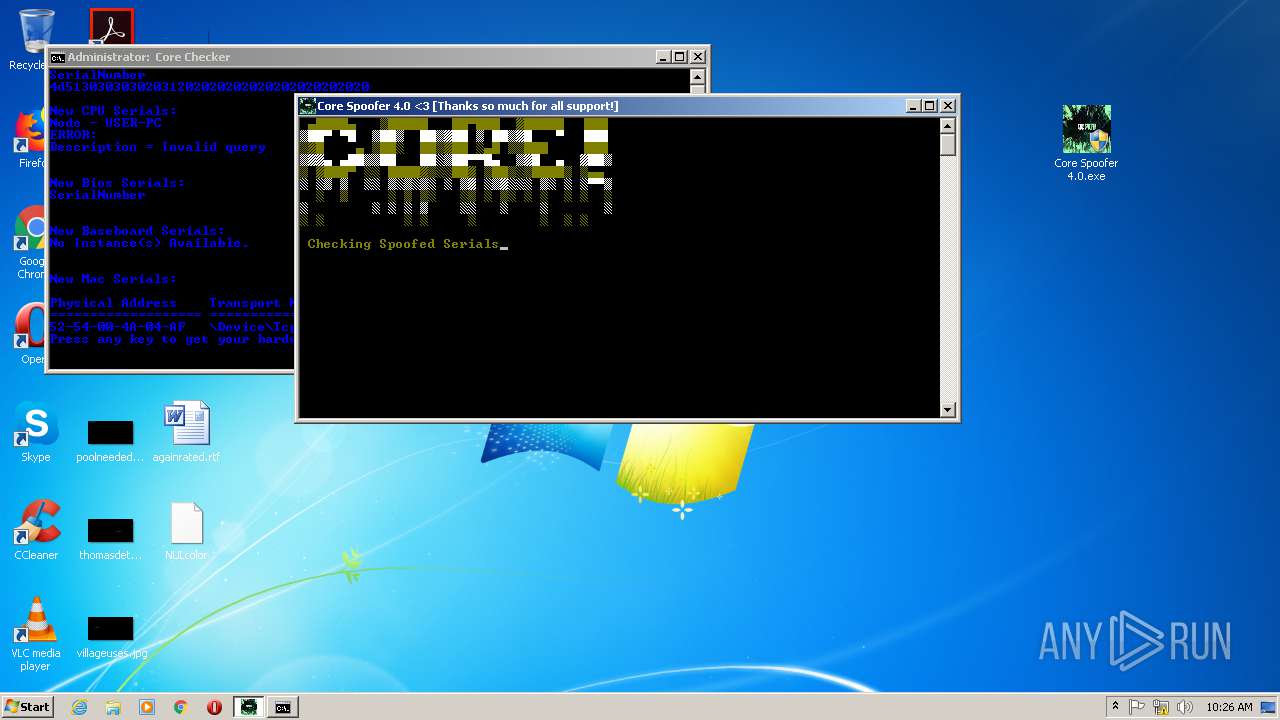
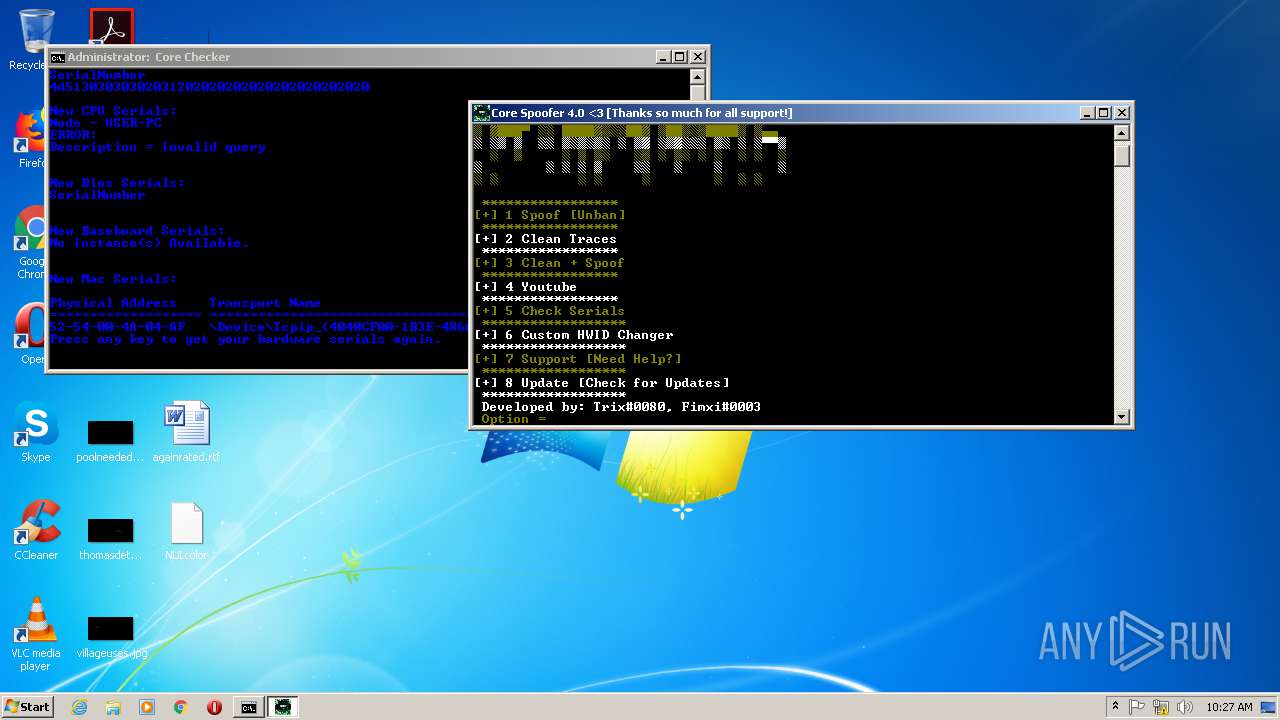
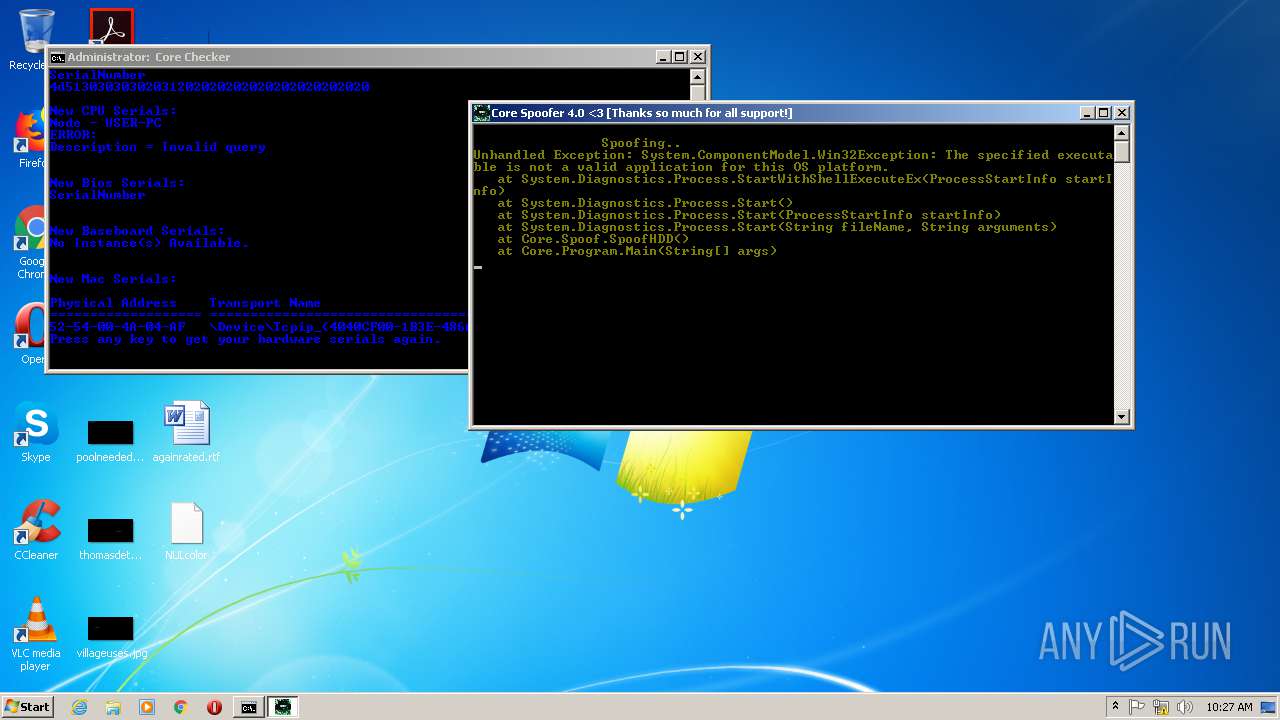
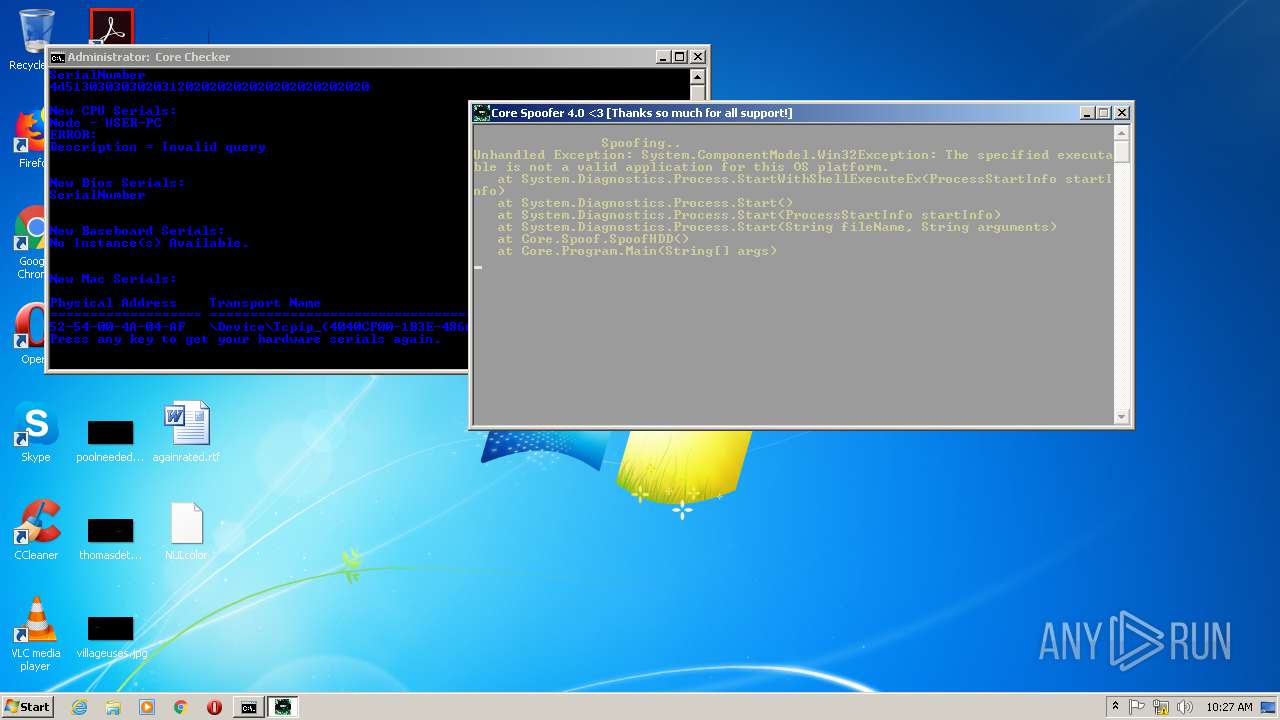
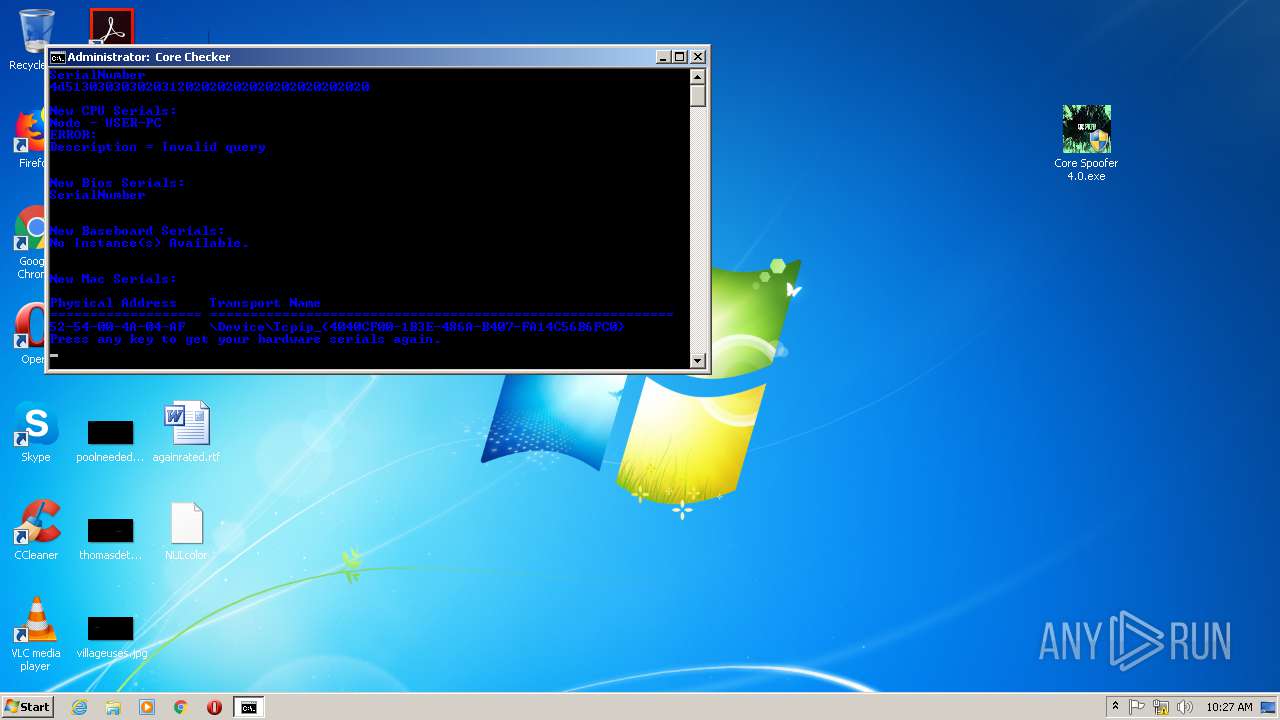
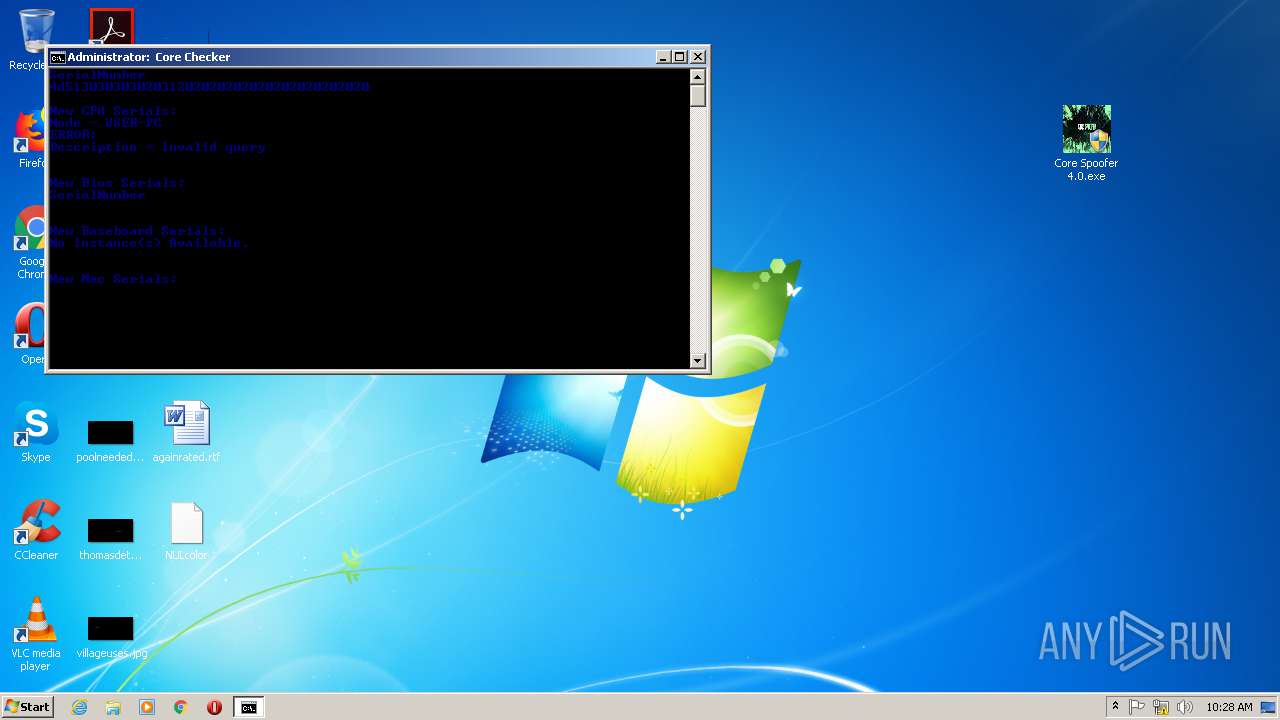
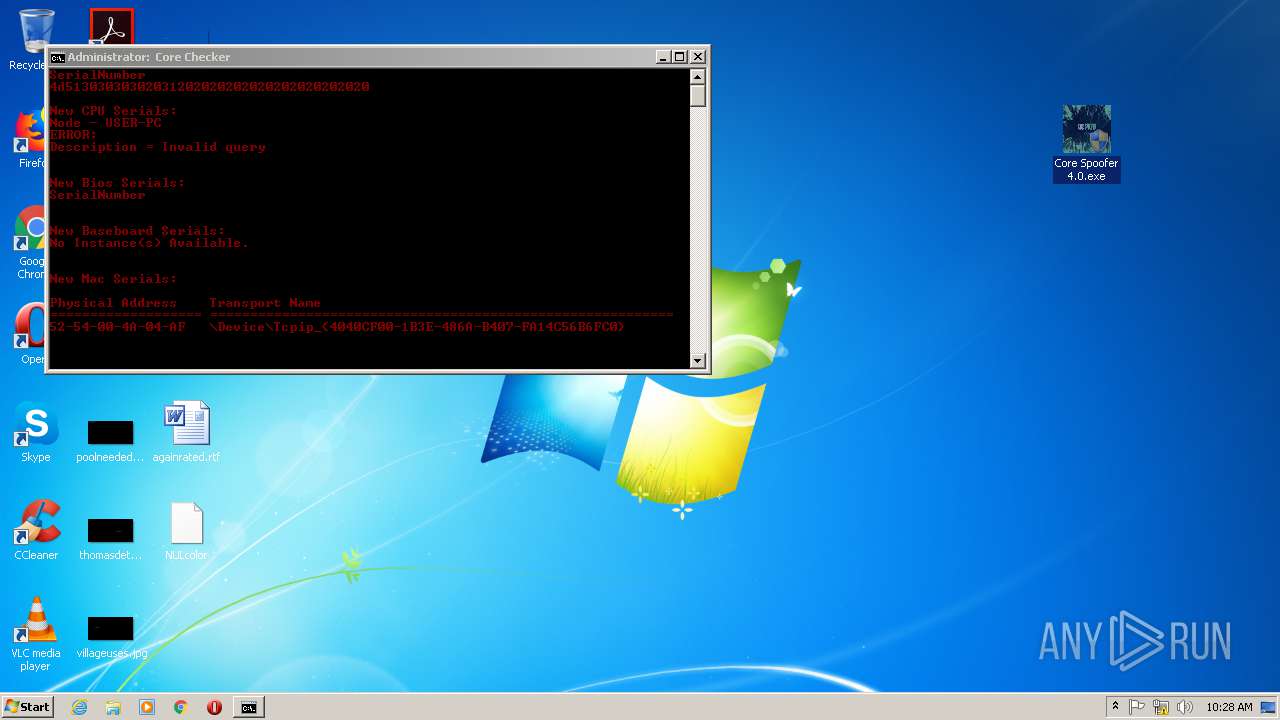
MALICIOUS
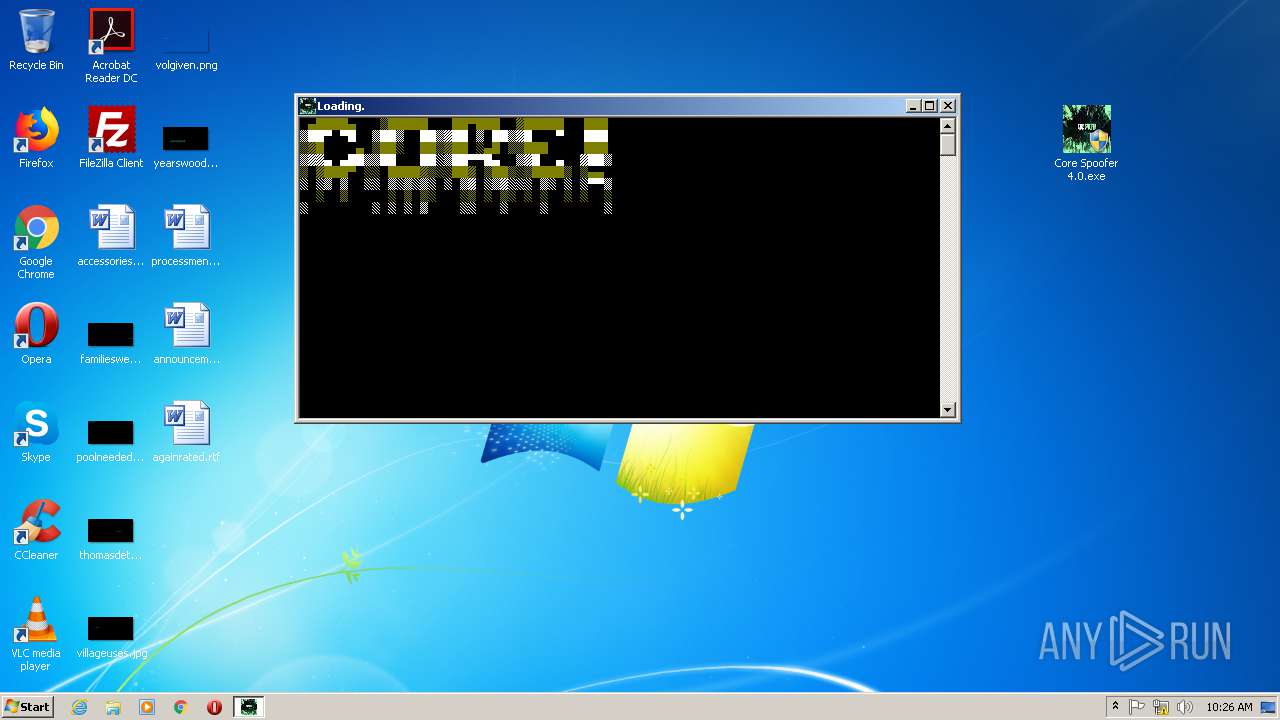
Application was dropped or rewritten from another process
- Core Spoofer 4.0.exe (PID: 492)
- Core Spoofer 4.0.exe (PID: 2804)
- Core Spoofer 4.0.exe (PID: 3924)
- Core Spoofer 4.0.exe (PID: 3312)
- Core Spoofer 4.0.exe (PID: 1920)
- Core Spoofer 4.0.exe (PID: 2300)
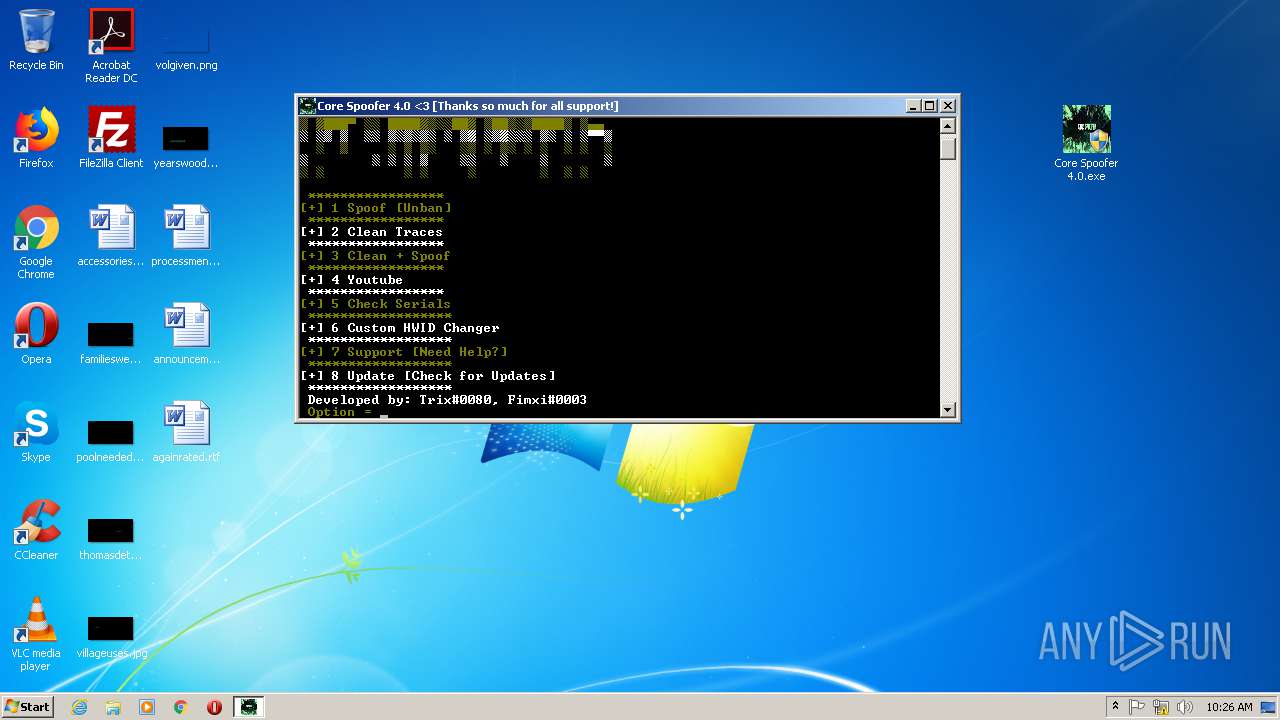
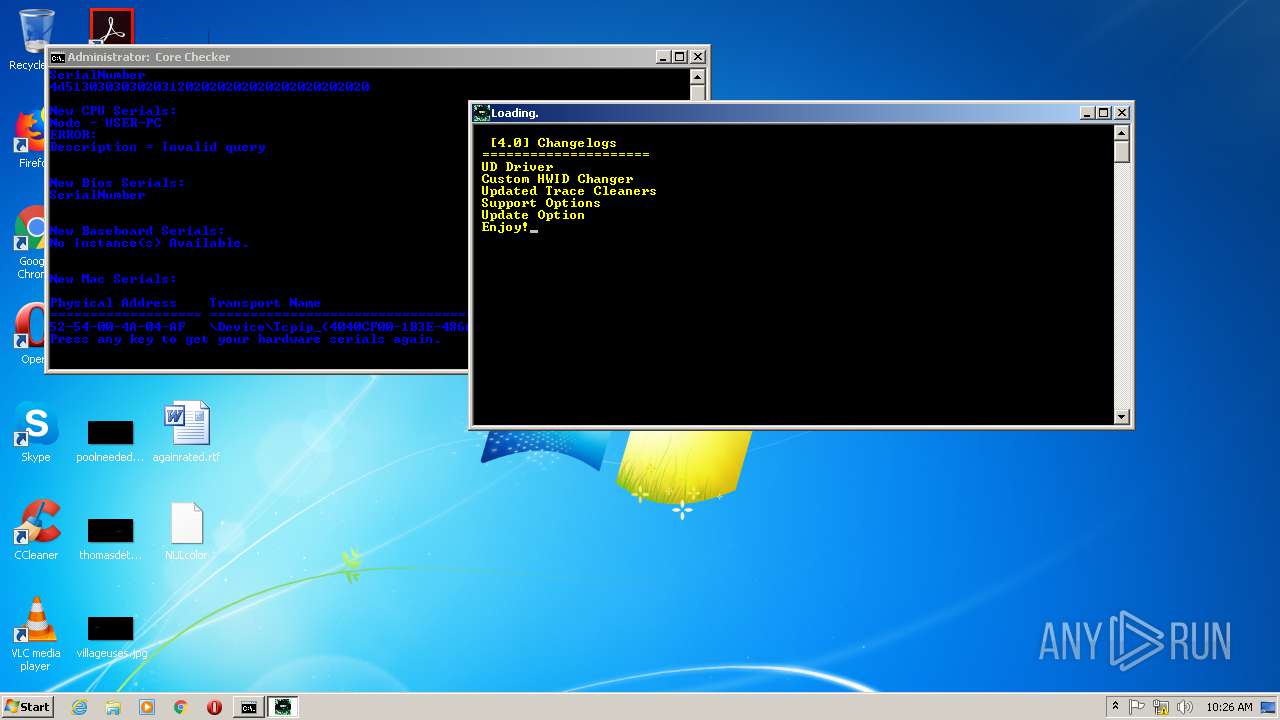
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2460)
Runs app for hidden code execution
- Core Spoofer 4.0.exe (PID: 2300)
Changes settings of System certificates
- Core Spoofer 4.0.exe (PID: 2804)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 1392)
Creates files in the Windows directory
- Core Spoofer 4.0.exe (PID: 2804)
- Core Spoofer 4.0.exe (PID: 1920)
- Core Spoofer 4.0.exe (PID: 2300)
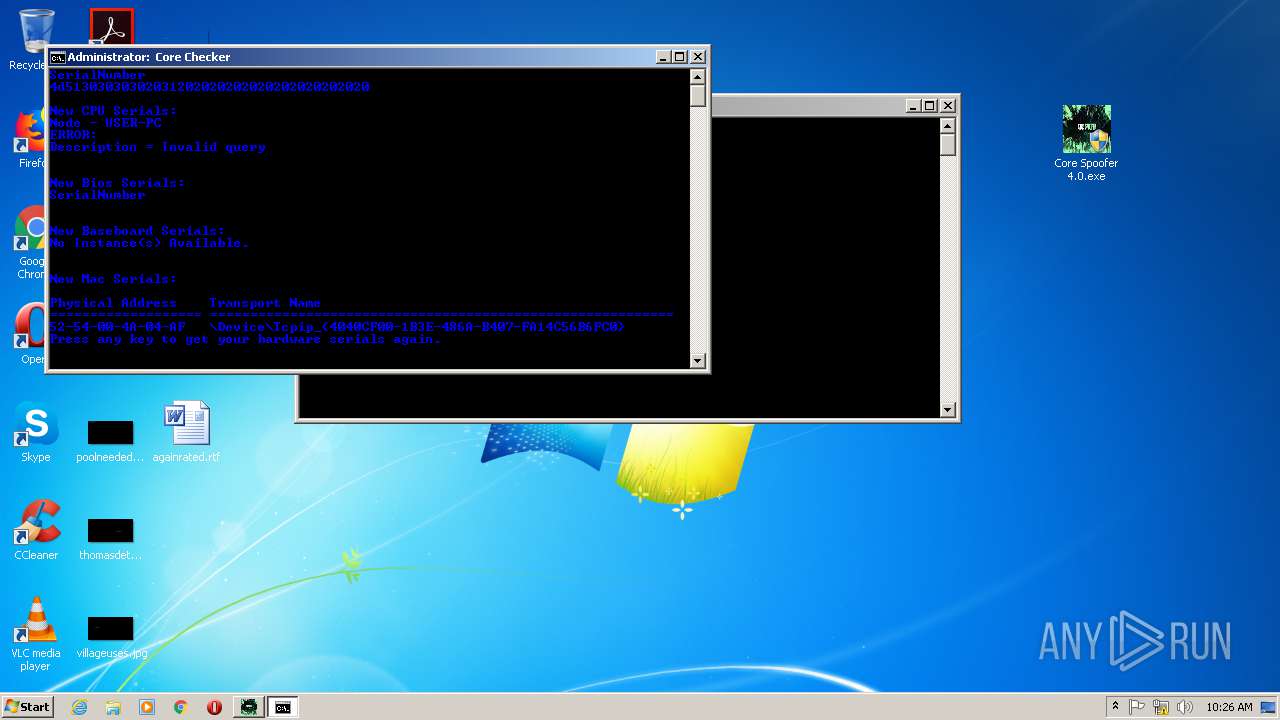
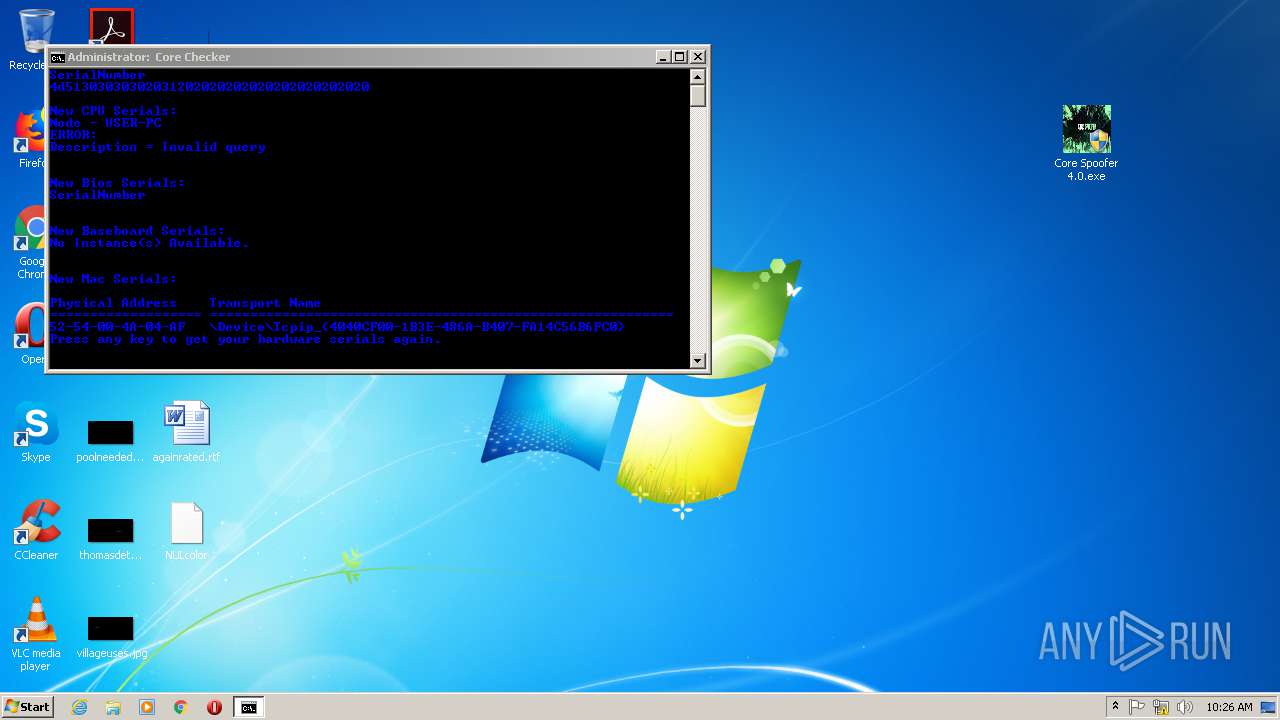
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2460)
Starts CMD.EXE for commands execution
- Core Spoofer 4.0.exe (PID: 2804)
- Core Spoofer 4.0.exe (PID: 2300)
Executable content was dropped or overwritten
- Core Spoofer 4.0.exe (PID: 1920)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2920)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2920)
Adds / modifies Windows certificates
- Core Spoofer 4.0.exe (PID: 2804)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1944)
- firefox.exe (PID: 1392)
- pingsender.exe (PID: 3292)
Changes internet zones settings
- iexplore.exe (PID: 1944)
Reads internet explorer settings
- iexplore.exe (PID: 376)
Application launched itself
- firefox.exe (PID: 2688)
- iexplore.exe (PID: 1944)
- firefox.exe (PID: 1392)
Reads CPU info
- firefox.exe (PID: 1392)
Manual execution by user
- firefox.exe (PID: 2688)
- Core Spoofer 4.0.exe (PID: 492)
- Core Spoofer 4.0.exe (PID: 2804)
- Core Spoofer 4.0.exe (PID: 1920)
- Core Spoofer 4.0.exe (PID: 3924)
- Core Spoofer 4.0.exe (PID: 3312)
- Core Spoofer 4.0.exe (PID: 2300)
Reads settings of System Certificates
- Core Spoofer 4.0.exe (PID: 2804)
- iexplore.exe (PID: 376)
Creates files in the user directory
- firefox.exe (PID: 1392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
134
Monitored processes
71
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1392.0.1617958606\476761983" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1392 "\\.\pipe\gecko-crash-server-pipe.1392" 1180 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 292 | wmic baseboard get serialnumber | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | taskkill /f /im epicgameslauncher.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1944 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 464 | taskkill /f /im FortniteLauncher.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
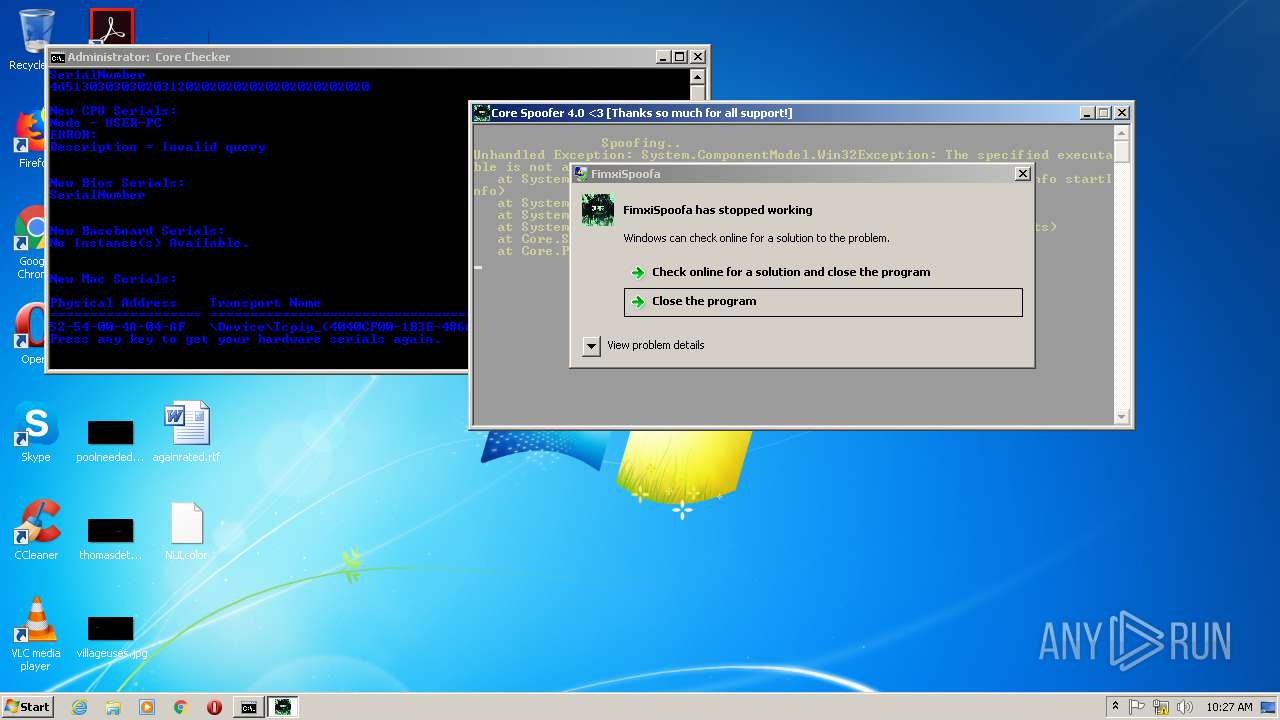
| 492 | "C:\Users\admin\Desktop\Core Spoofer 4.0.exe" | C:\Users\admin\Desktop\Core Spoofer 4.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: FimxiSpoofa Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 584 | wmic bios get serialnumber | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 672 | taskkill /f /im EasyAntiCheat.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 812 | ping -n 1 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 812 | ping -n 1 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 001
Read events
2 674
Write events
1 323
Delete events
4
Modification events
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4171852196 | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30816849 | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
194
Text files
80
Unknown types
123
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1944 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF56AF15891063ADE3.TMP | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3ECAADB426D98133.TMP | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB19635F258E84B9C.TMP | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2F1C613BA8636D22.TMP | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{24660463-A645-11EA-B44D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCFD4D861F2AD4013.TMP | — | |
MD5:— | SHA256:— | |||
| 1392 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
100
DNS requests
198
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1392 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
1392 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 143.204.208.173:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1392 | firefox.exe | POST | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com/ | US | der | 1.80 Kb | whitelisted |
1392 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 104.22.67.194:445 | st.toneden.io | Cloudflare Inc | US | suspicious |
376 | iexplore.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
376 | iexplore.exe | 185.63.144.5:443 | dc.ads.linkedin.com | LinkedIn Corporation | IE | suspicious |
376 | iexplore.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
376 | iexplore.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1392 | firefox.exe | 2.16.107.40:80 | detectportal.firefox.com | Akamai International B.V. | — | malicious |
1392 | firefox.exe | 52.41.191.52:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1392 | firefox.exe | 143.204.201.68:443 | snippets.cdn.mozilla.net | — | US | unknown |
1392 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1392 | firefox.exe | 143.204.201.102:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
st.toneden.io |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
sd.toneden.io |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
www.facebook.com |
| whitelisted |
dc.ads.linkedin.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |