| File name: | Victoria 3 Trainer - FLiNG.exe |
| Full analysis: | https://app.any.run/tasks/c3aaf652-1c88-467c-8fba-84fde6813945 |
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2024, 07:49:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C65BD85C8F9108804AE5D9BE7ED688D9 |
| SHA1: | BDCB59978336F4D32611BFFFC62BEF15DF92431B |
| SHA256: | 67C2EE5FB57B0ED7A87457BF94A10B8BECBB95F8235DD091A106ECEB7CCC277C |
| SSDEEP: | 1536:Q668Dtf9nk7RBog5KG6JkOiVPL+09ME5LBtJD64uQgCYO6+YFyHA7OqCkNRBog5m:w8DvE57miVj+J6pHdHg7OA57N/u |
MALICIOUS
Drops the executable file immediately after the start
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Scans artifacts that could help determine the target
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
SUSPICIOUS
Reads security settings of Internet Explorer
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Reads Microsoft Outlook installation path
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Checks Windows Trust Settings
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Reads Internet Explorer settings
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
INFO
Checks proxy server information
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
- slui.exe (PID: 6800)
Reads the computer name
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Checks supported languages
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Reads the machine GUID from the registry
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Reads the software policy settings
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
- slui.exe (PID: 6800)
Process checks Internet Explorer phishing filters
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Creates files or folders in the user directory
- Victoria 3 Trainer - FLiNG.exe (PID: 7460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2076:12:06 19:29:50+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 105984 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1bcfe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.0.0 |
| ProductVersionNumber: | 8.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
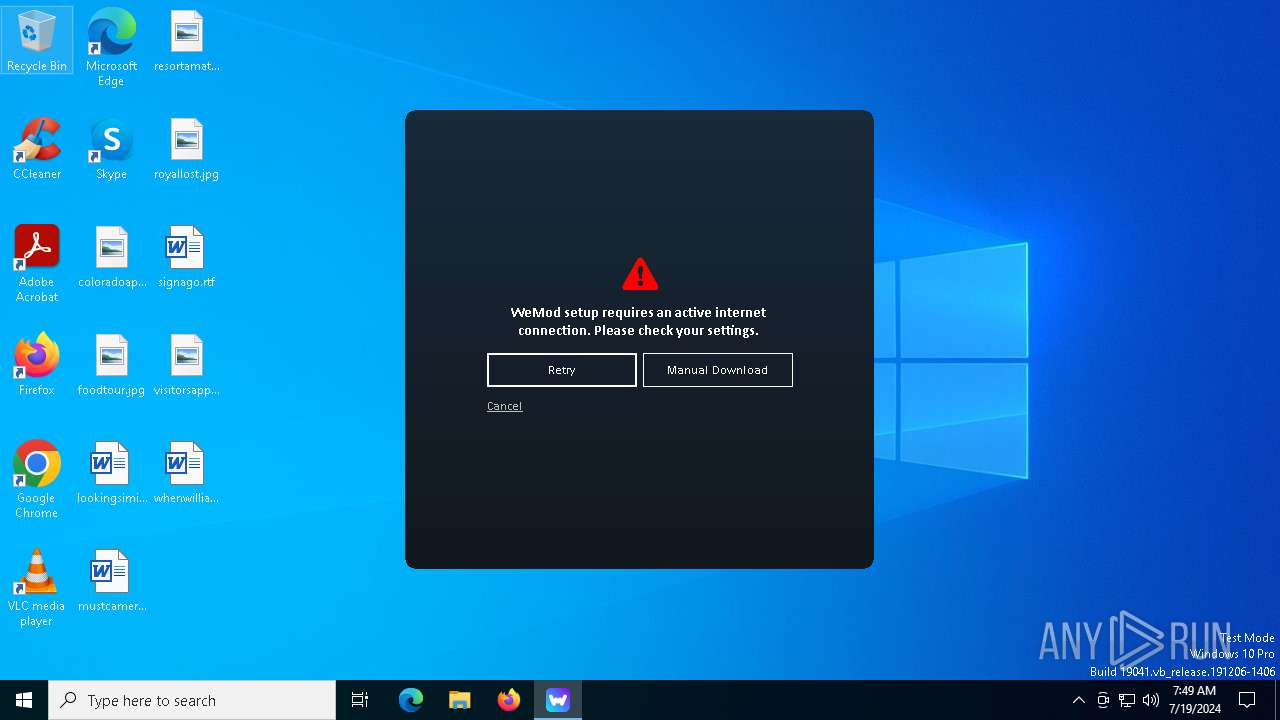
| Comments: | WeMod Setup |
| CompanyName: | WeMod LLC |
| FileDescription: | WeMod Setup |
| FileVersion: | 8.0.0.0 |
| InternalName: | WeMod-Setup.exe |
| LegalCopyright: | Copyright © WeMod LLC 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | WeMod-Setup.exe |
| ProductName: | WeMod |
| ProductVersion: | 8.0.0.0 |
| AssemblyVersion: | 8.0.0.0 |
Total processes
123
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6800 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7460 | "C:\Users\admin\AppData\Local\Temp\Victoria 3 Trainer - FLiNG.exe" | C:\Users\admin\AppData\Local\Temp\Victoria 3 Trainer - FLiNG.exe | explorer.exe | ||||||||||||
User: admin Company: WeMod LLC Integrity Level: MEDIUM Description: WeMod Setup Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
7 040
Read events
7 029
Write events
11
Delete events
0
Modification events
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7460) Victoria 3 Trainer - FLiNG.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5968 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7856 | svchost.exe | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7460 | Victoria 3 Trainer - FLiNG.exe | 172.67.25.118:443 | api.wemod.com | CLOUDFLARENET | US | unknown |
2760 | svchost.exe | 40.113.103.199:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
684 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arc.msn.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
api.wemod.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |