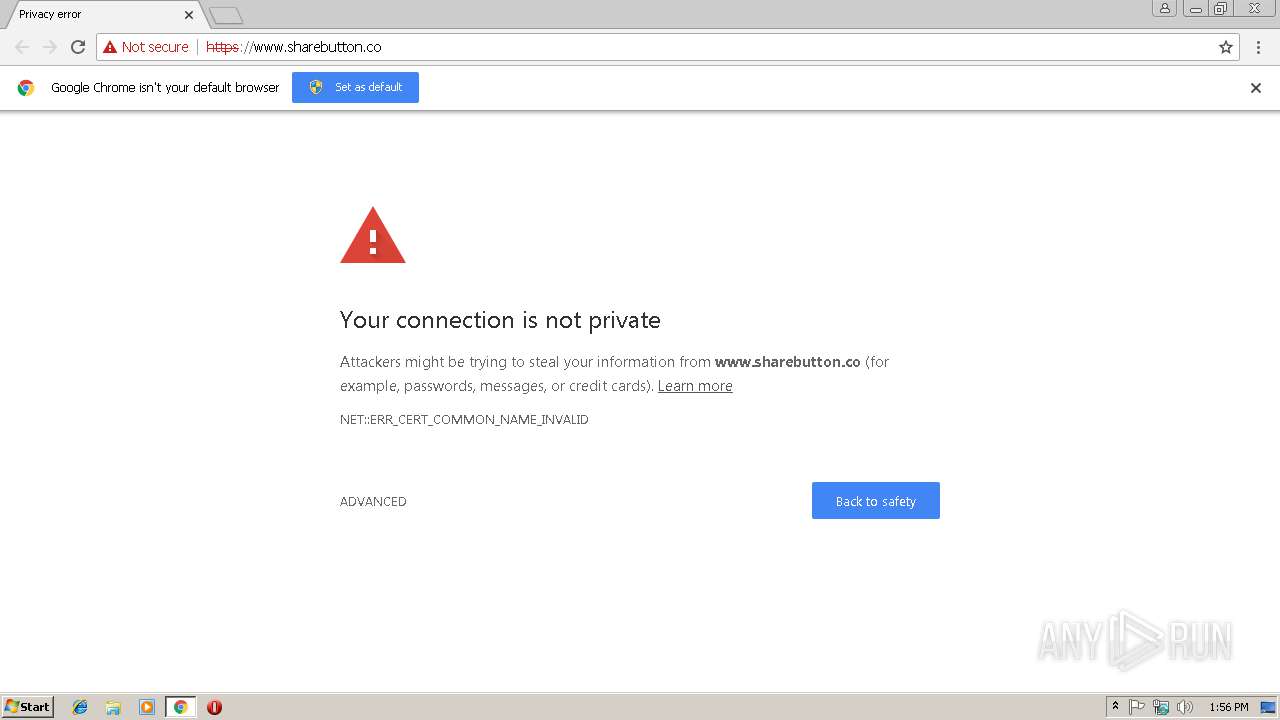
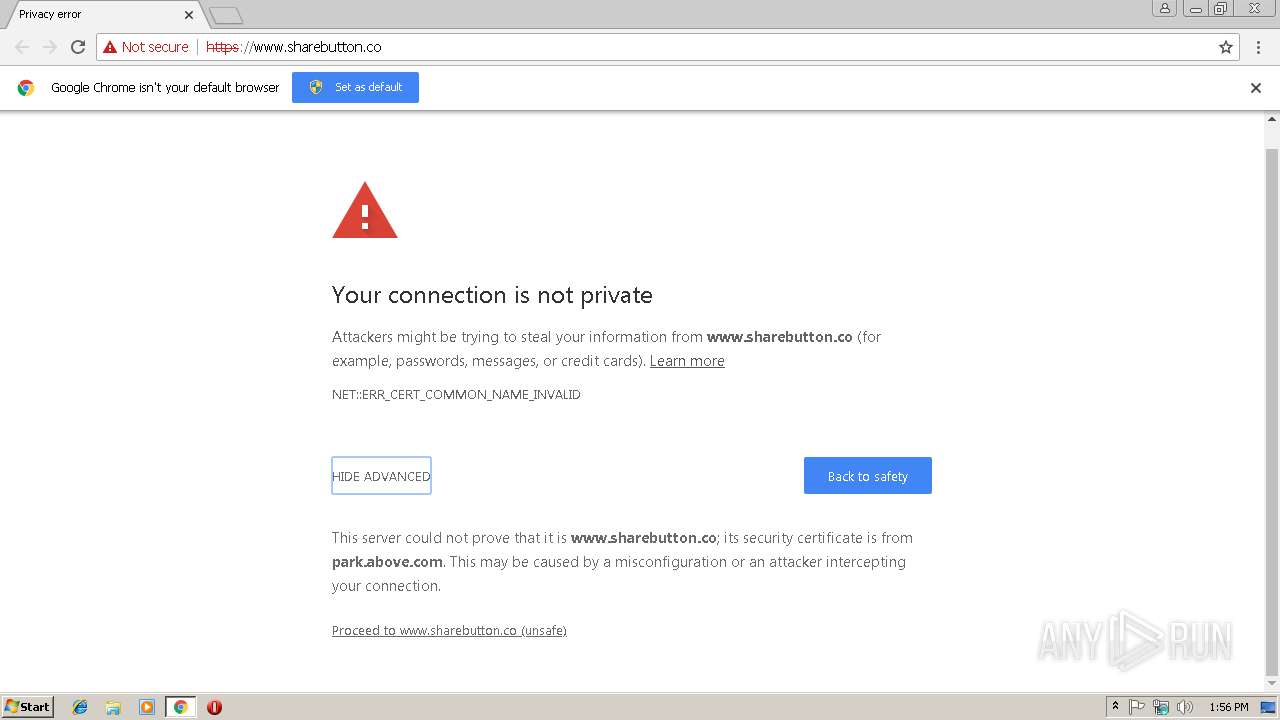
| URL: | https://www.sharebutton.co/ |
| Full analysis: | https://app.any.run/tasks/c11f1fd8-2b8e-4d87-b2f6-70734c12338b |
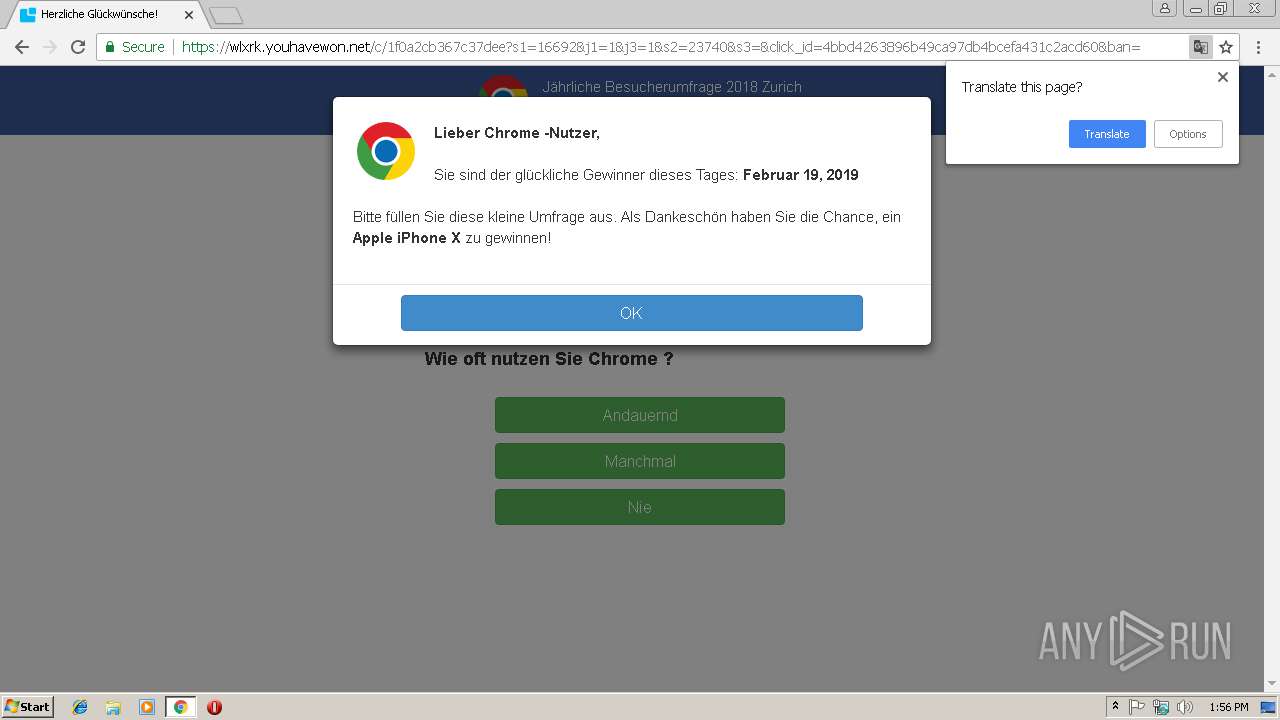
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 13:55:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9324EBFD64AFEA433B4ACD53BFAABEA2 |
| SHA1: | A4ABCC816999FACD2415FD5FF35D1232EFD8BB05 |
| SHA256: | 67B4F820B8C71AAA09FD23D04F8AB0B77569C31A66950F1CE87CAE0E007CFB03 |
| SSDEEP: | 3:N8DSL7RRKQ:2OL7RsQ |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 3416)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6fe300b0,0x6fe300c0,0x6fe300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=1DF6CE24415C0D47DBDC682FF8E09CC1 --mojo-platform-channel-handle=916 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=769498ACA2789E089DCC911BB0ABCA2D --mojo-platform-channel-handle=2468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=35CDE0A8C2947D3014580714B17055D4 --mojo-platform-channel-handle=3876 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --service-pipe-token=2A22F96F3CC9AF46DDE14AD0B9EFBE25 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2A22F96F3CC9AF46DDE14AD0B9EFBE25 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C02C2D5D6EE335062FB276EF292BA217 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C02C2D5D6EE335062FB276EF292BA217 --renderer-client-id=5 --mojo-platform-channel-handle=3376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3420 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.sharebutton.co/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --service-pipe-token=D8958C9B085274783CA3CB440F71F979 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D8958C9B085274783CA3CB440F71F979 --renderer-client-id=3 --mojo-platform-channel-handle=2088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=46689074637CF86CBFEE557D241876D5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=46689074637CF86CBFEE557D241876D5 --renderer-client-id=6 --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
509
Read events
463
Write events
43
Delete events
3
Modification events
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3416-13195058170645250 |
Value: 259 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3416-13195058170645250 |
Value: 259 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
15
Text files
53
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ba617f87-d50b-4ec7-9a48-aa088ce2f8fa.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5a13d73e-a138-4af1-b689-8e130b804c3a.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae475.TMP | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
42
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | chrome.exe | GET | 204 | 172.217.22.35:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
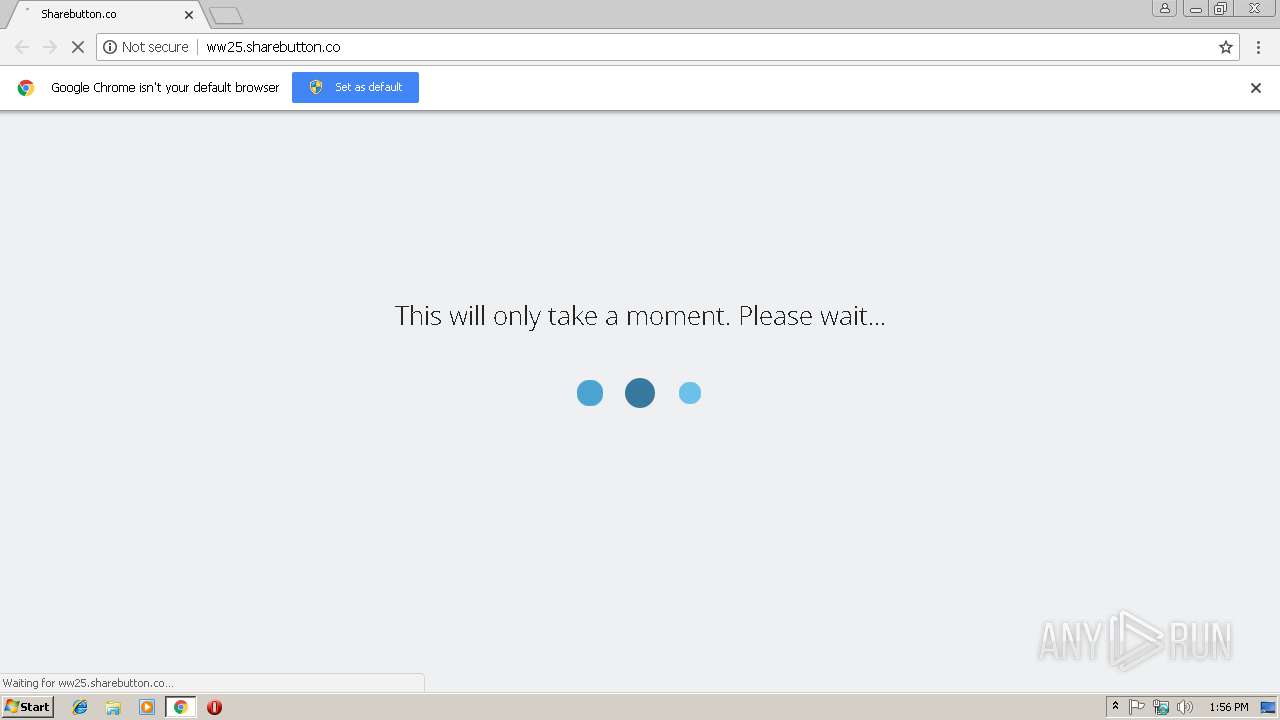
3416 | chrome.exe | GET | 200 | 199.59.242.151:80 | http://ww25.sharebutton.co/ | US | html | 3.93 Kb | malicious |
3416 | chrome.exe | GET | 404 | 199.59.242.151:80 | http://ww25.sharebutton.co/favicon.ico | US | html | 3.93 Kb | malicious |
3416 | chrome.exe | GET | 200 | 199.59.242.151:80 | http://ww25.sharebutton.co/glp?r=&u=http%3A%2F%2Fww25.sharebutton.co%2F&rw=1280&rh=720&ww=1280&wh=582 | US | text | 8.27 Kb | malicious |
3416 | chrome.exe | GET | 302 | 199.59.242.151:80 | http://ww25.sharebutton.co/rz?u=http%3A%2F%2Fusd.photios-raj.com%2Fzcvisitor%2F22700195-344e-11e9-885e-1246884730fe%3Fcampaignid%3D60b91e60-aab4-11e8-a800-0e41d0acbc1a¬adsafe | US | text | 198 b | malicious |
3416 | chrome.exe | POST | 200 | 199.59.242.151:80 | http://ww25.sharebutton.co/gzb | US | text | 198 b | malicious |
3416 | chrome.exe | GET | 200 | 54.172.94.62:80 | http://usd.photios-raj.com/zcvisitor/22700195-344e-11e9-885e-1246884730fe?campaignid=60b91e60-aab4-11e8-a800-0e41d0acbc1a | US | html | 1004 b | malicious |
3416 | chrome.exe | GET | 404 | 54.172.94.62:80 | http://usd.photios-raj.com/favicon.ico | US | html | 940 b | malicious |
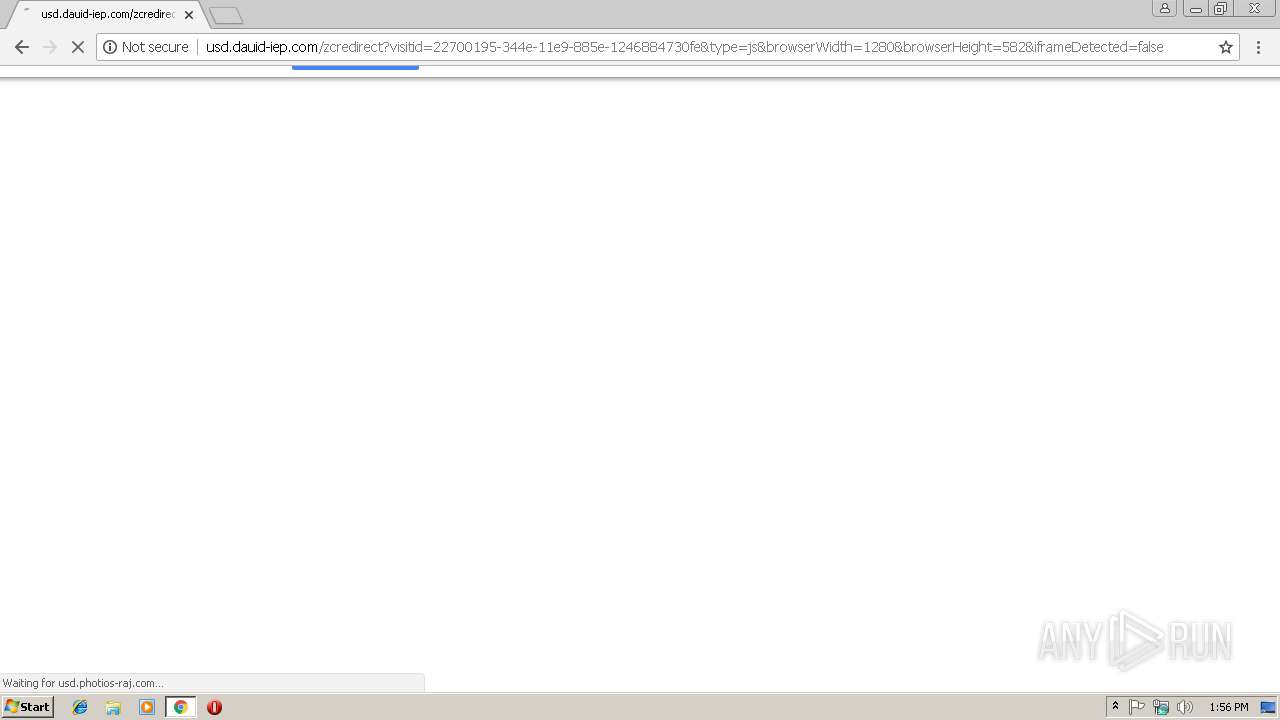
3416 | chrome.exe | GET | 200 | 54.172.94.62:80 | http://usd.dauid-iep.com/zcredirect?visitid=22700195-344e-11e9-885e-1246884730fe&type=js&browserWidth=1280&browserHeight=582&iframeDetected=false | US | html | 882 b | shared |
3416 | chrome.exe | GET | 200 | 172.217.21.196:80 | http://www.google.com/adsense/domains/caf.js | US | text | 55.4 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3416 | chrome.exe | 172.217.22.35:80 | www.gstatic.com | Google Inc. | US | whitelisted |
3416 | chrome.exe | 199.59.242.151:80 | ww25.sharebutton.co | Bodis, LLC | US | malicious |
3416 | chrome.exe | 172.217.21.196:80 | www.google.com | Google Inc. | US | whitelisted |
3416 | chrome.exe | 172.217.18.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3416 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3416 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3416 | chrome.exe | 207.154.224.109:443 | cl-offers.com | Digital Ocean, Inc. | DE | unknown |
3416 | chrome.exe | 54.172.94.62:80 | usd.photios-raj.com | Amazon.com, Inc. | US | unknown |
3416 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.sharebutton.co |
| suspicious |
accounts.google.com |
| shared |
ww25.sharebutton.co |
| malicious |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
usd.photios-raj.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3416 | chrome.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 1 |