| File name: | http://getapp.mennythanks.com/up/dl/1576740781970921/CEUpdater.exe?e=BFEBFBFF000806E9%20%20%20%20%20%20JR1000D31EDJEE0205857FEB8 |
| Full analysis: | https://app.any.run/tasks/bc57476c-1c9e-4a44-ae65-23e7ed66549c |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 03:07:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B36A396DD00DC57C472475165F742C63 |
| SHA1: | 80D3E36E51A32501DEB73E1ECB8A34877228A828 |
| SHA256: | 67ACDDDA7726183DB30AD749CBC2A8AC1929D9C50BC3D1EF7F60852F57B879A9 |
| SSDEEP: | 98304:sK3/z0hcZ7AF05U4usM+Ldi5e/w9KB72j:sKPYhwA52M8diYw9KBS |
MALICIOUS
Loads dropped or rewritten executable
- 383e456d-8493-467a-88ce-6903715ba486.exe (PID: 2452)
Loads the Task Scheduler COM API
- 383e456d-8493-467a-88ce-6903715ba486.exe (PID: 2452)
SUSPICIOUS
Executable content was dropped or overwritten
- 383e456d-8493-467a-88ce-6903715ba486.exe (PID: 2452)
Creates files in the user directory
- 383e456d-8493-467a-88ce-6903715ba486.exe (PID: 2452)
Starts CMD.EXE for commands execution
- 383e456d-8493-467a-88ce-6903715ba486.exe (PID: 2452)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 2856)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3468)
INFO
Application launched itself
- chrome.exe (PID: 3468)
Reads the hosts file
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2392)
Manual execution by user
- chrome.exe (PID: 3468)
Reads settings of System Certificates
- chrome.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2083:03:10 21:17:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5437440 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5317ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | EdgeChromeUpdater |
| FileVersion: | 1.0.0.0 |
| InternalName: | CEUpdater.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | CEUpdater.exe |
| ProductName: | EdgeChromeUpdater |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Feb-1947 13:48:45 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | EdgeChromeUpdater |
| FileVersion: | 1.0.0.0 |
| InternalName: | CEUpdater.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | CEUpdater.exe |
| ProductName: | EdgeChromeUpdater |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Feb-1947 13:48:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0052F7F4 | 0x0052F800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.53684 |
.rsrc | 0x00532000 | 0x000005CC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13573 |
.reloc | 0x00534000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
77
Monitored processes
38
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17428859094987945598 --mojo-platform-channel-handle=4224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 616 | choice /C Y /N /D Y /T 3 | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17533387258315858049 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2596 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10168725443554618349 --mojo-platform-channel-handle=4540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17929861946179282680 --mojo-platform-channel-handle=4008 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16496626720002722236 --mojo-platform-channel-handle=4336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6195268616397089355 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16156319446330296304 --mojo-platform-channel-handle=3328 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f70a9d0,0x6f70a9e0,0x6f70a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13805595883272856296,17361582349075467642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15073193075073671387 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
940
Read events
827
Write events
108
Delete events
5
Modification events
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2452) 383e456d-8493-467a-88ce-6903715ba486.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\383e456d-8493-467a-88ce-6903715ba486_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
88
Text files
181
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BD08E-D8C.pma | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\404a34da-4fdf-4b25-bb82-f1d29f905aa2.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2452 | 383e456d-8493-467a-88ce-6903715ba486.exe | C:\Users\admin\AppData\Roaming\CEUpdater\383e456d-8493-467a-88ce-6903715ba486.exe | executable | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18d03b.TMP | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18d04b.TMP | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF18d06a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
75
DNS requests
86
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
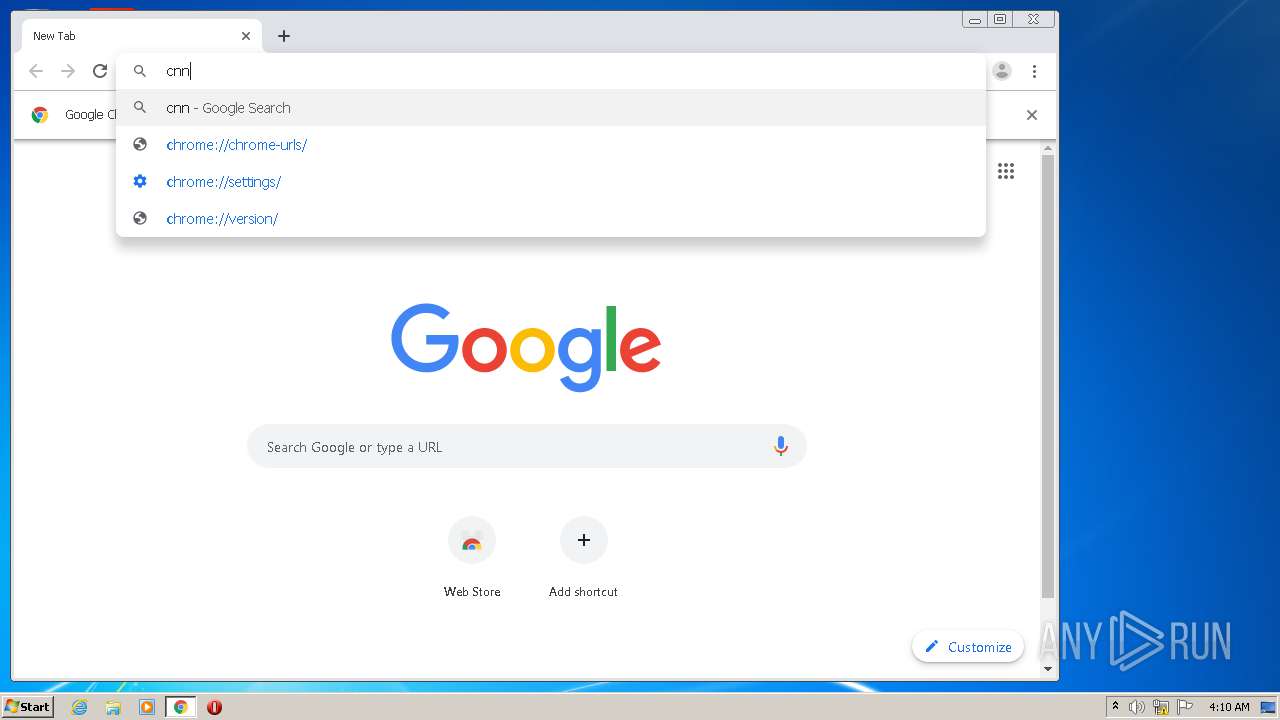
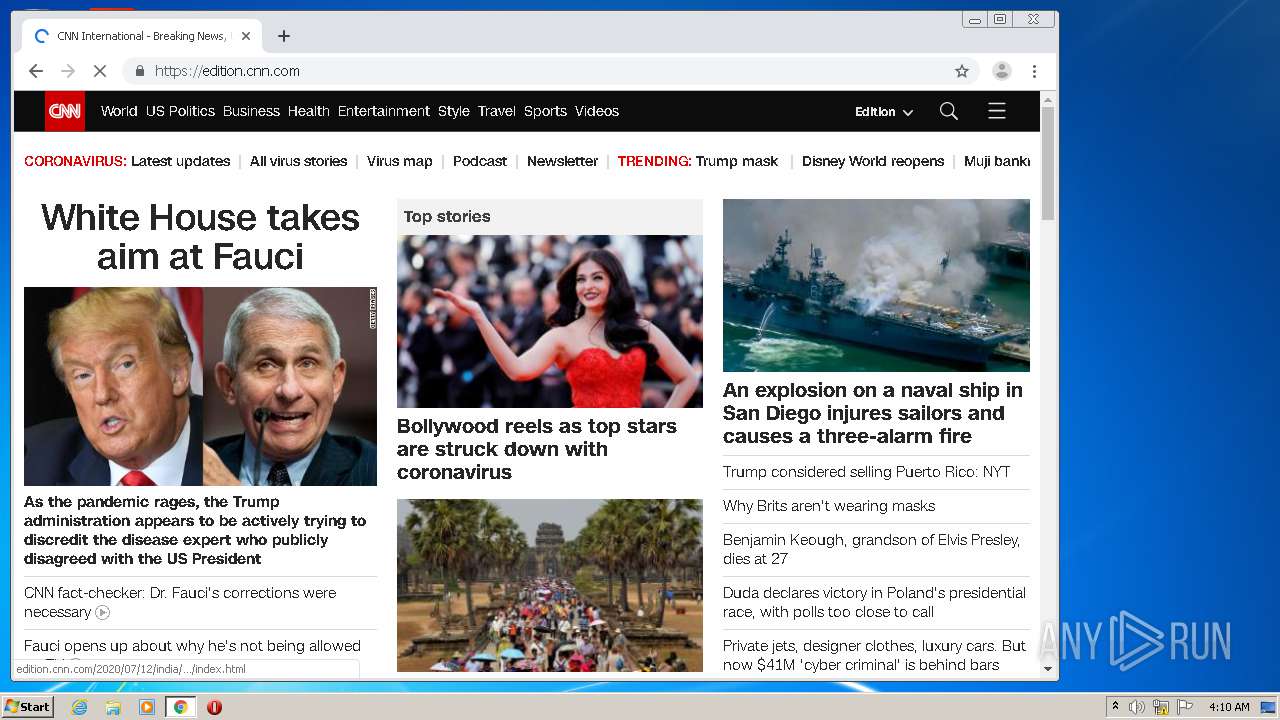
2392 | chrome.exe | GET | 301 | 151.101.1.67:80 | http://www.cnn.com/ | US | — | — | whitelisted |
2392 | chrome.exe | GET | 301 | 151.101.1.67:80 | http://cnn.com/ | US | — | — | whitelisted |
2452 | 383e456d-8493-467a-88ce-6903715ba486.exe | POST | 200 | 45.67.228.180:80 | http://inf.rapsee.com/api/report/install?event_name=edge_chromium_report&infoJson=D2xhVE9MBxQCEE1UVENaMlcsMiMtMl9eRFRbQipdQAVeRVxeR1FYRFxeRlFYRV1eRlFZRF1eRlFZRF1eRlFZRF1eRlFZRFpcQVVbRFsvRFUqMk1CeWtLVE0PBA00HQtMTkFJRVpZQlZfRFhWRVhcRFZcRUNHeWVOVEMEBAocFRUCGggxBxgYKwQHGgVJTk9MOQgIBgAdGwcfVDgHGgUEAxxOQ0E7BgAIERIYHQAAFQ1LVkNjfkFLVgAeERMKAAYAEz4YDRwxAgQZBwYBGkNRVE1YWlBFQ1leRU9dQVpdQkNHeWVOVEMCEAoAAENRVE0cFREYEQpMWGxhVE9MAgQZBwYBGj4CGhwaVltLVl5dVk1mfk9OVhUZHQgJERNJTk9MHQ8YAA4CGENHeWVOVEMKFxsHGw9JTk9MJxUKBhtOHQ8YAA4CGEEbBgANERIYWk1jfhw%3d | unknown | — | — | malicious |
2452 | 383e456d-8493-467a-88ce-6903715ba486.exe | POST | 200 | 45.67.228.180:80 | http://inf.rapsee.com/api/report/install?event_name=edge_chromium_report&infoJson=D2xhVE9MBxQCEE1UVENaMlcsMiMtMl9eRFRbQipdQAVeRVxeR1FYRFxeRlFYRV1eRlFZRF1eRlFZRF1eRlFZRF1eRlFZRFpcQVVbRFsvRFUqMk1CeWtLVE0PBA00HQtMTkFJRVpZQlZfRFhWRVhcRFZcRUNHeWVOVEMEBAocFRUCGggxBxgYKwQHGgVJTk9MOQgIBgAdGwcfVDgHGgUEAxxOQ0E7BgAIERIYHQAAFQ1LVkNjfkFLVgAeERMKAAYAEz4YDRwxAgQZBwYBGkNRVE1YWlBFQ1leRU9dQVpdQkNHeWVOVEMCEAoAAENRVE0cFREYEQpMWGxhVE9MAgQZBwYBGj4CGhwaVltLVl5dVk1mfk9OVhUZHQgJERNJTk9MHQ8YAA4CGENHeWVOVEMKFxsHGw9JTk9MIAAYHxxOFxMOFRsLEEEYAQwNERINAQMCDUNmfhI%3d | unknown | — | — | malicious |
2392 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
2392 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
2392 | chrome.exe | GET | 200 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594609569&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 823 Kb | whitelisted |
2392 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594609569&mv=u&mvi=4&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | 383e456d-8493-467a-88ce-6903715ba486.exe | 45.67.228.180:80 | inf.rapsee.com | — | — | malicious |
2392 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 216.58.206.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
— | — | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.22.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2392 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.18.163:443 | www.google.lv | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
inf.rapsee.com |
| malicious |
imp.rapsee.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |