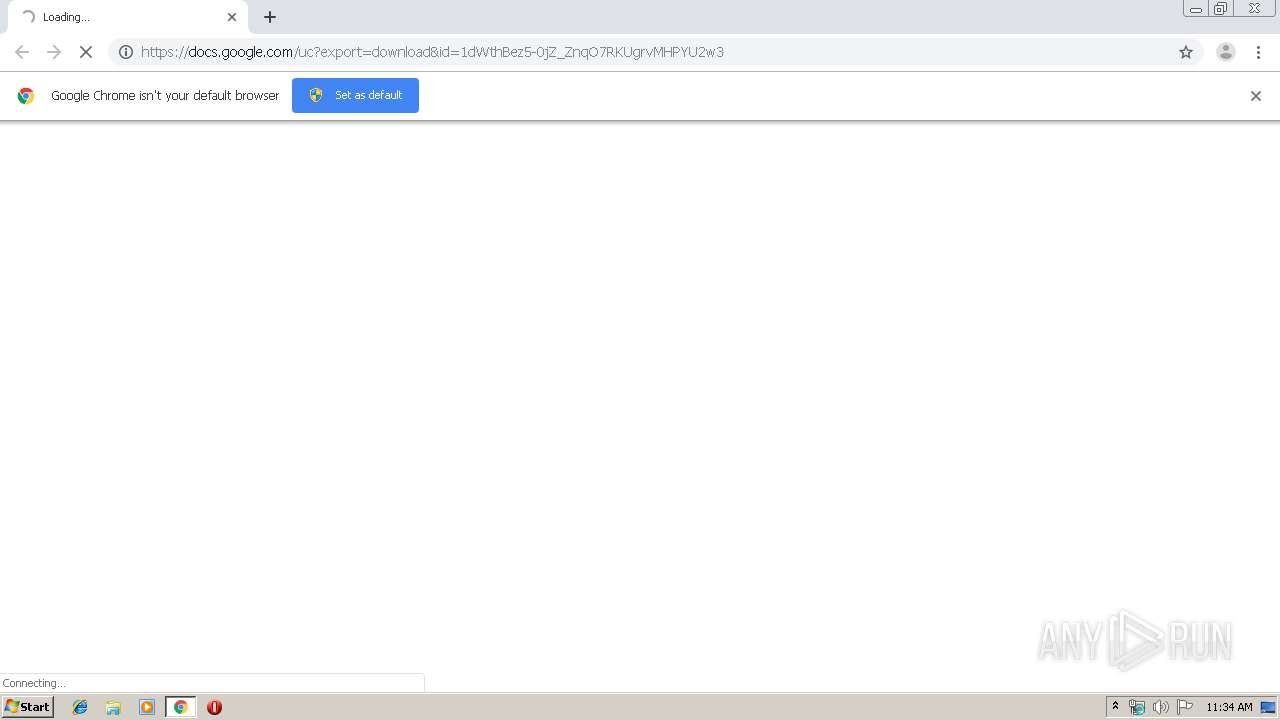
| URL: | https://docs.google.com/uc?export=download&id=1dWthBez5-0jZ_ZnqO7RKUgrvMHPYU2w3 |
| Full analysis: | https://app.any.run/tasks/92ed823e-58bd-4e07-a362-854f79ffd4cb |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 10:34:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 303E98EAC24FC55AB6C8FF157E985B6E |
| SHA1: | B4A83389A27FAA0A1B29E4DBAB9EF4B920246A83 |
| SHA256: | 679DD8090814D1B01FFB7370668D7182BCC0DE3DA777F4E98BE236C3600F7587 |
| SSDEEP: | 3:N8SP3u2NAaBrC2ERKvaIQToEWn:2Sm2BB+2EsvYo/n |
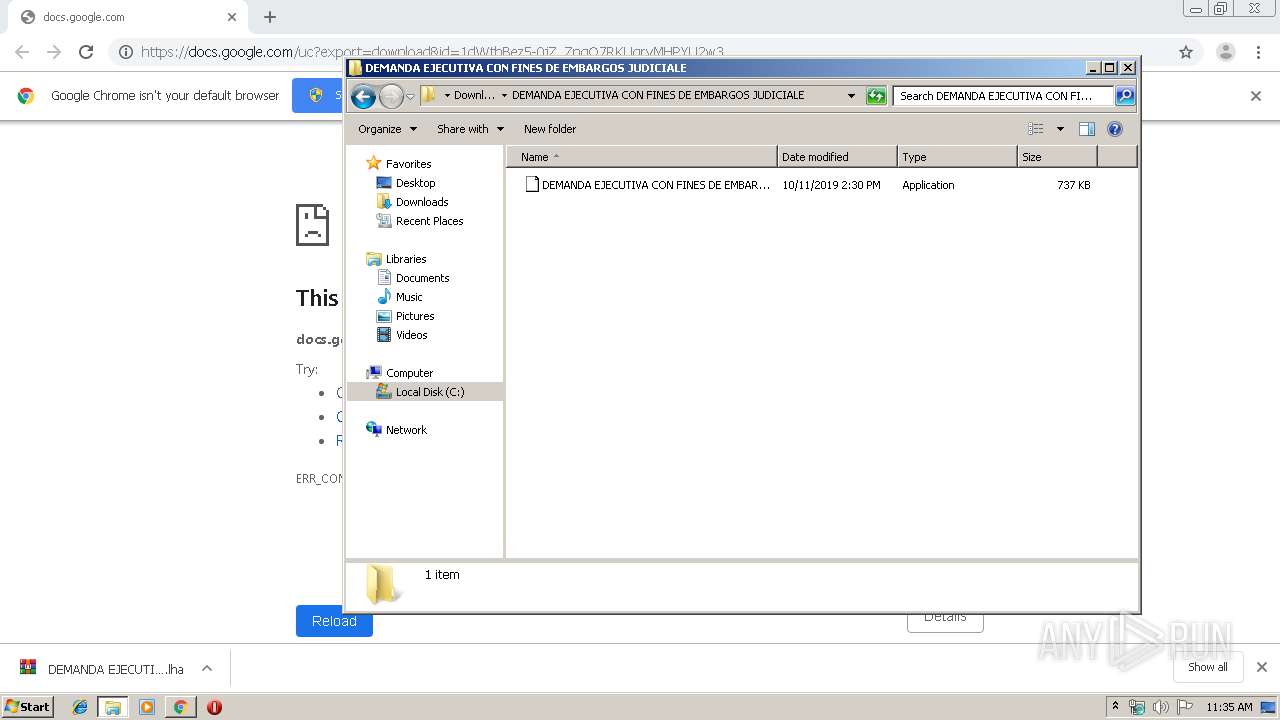
MALICIOUS
Changes the autorun value in the registry
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 1516)
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 3796)
- RegAsm.exe (PID: 1772)
Application was dropped or rewritten from another process
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 1516)
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 3796)
Uses Task Scheduler to run other applications
- RegAsm.exe (PID: 1772)
- RegAsm.exe (PID: 1800)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 4088)
- schtasks.exe (PID: 3028)
- schtasks.exe (PID: 2456)
- schtasks.exe (PID: 1880)
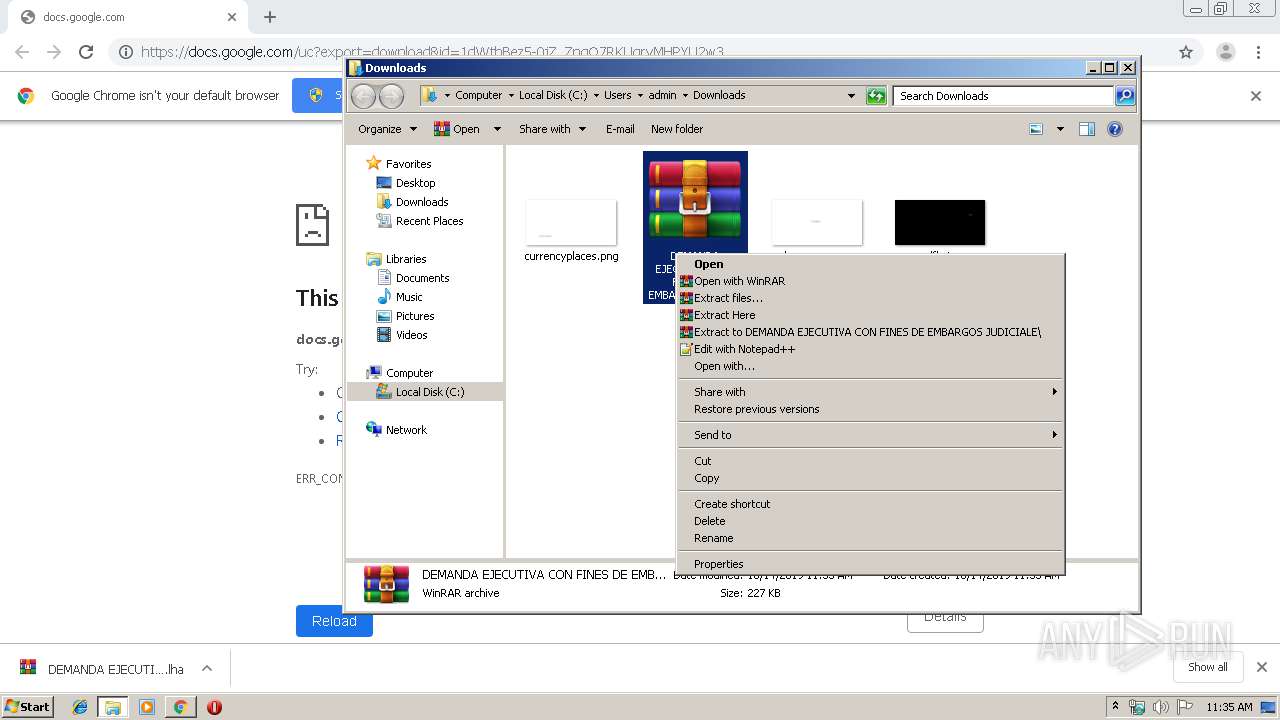
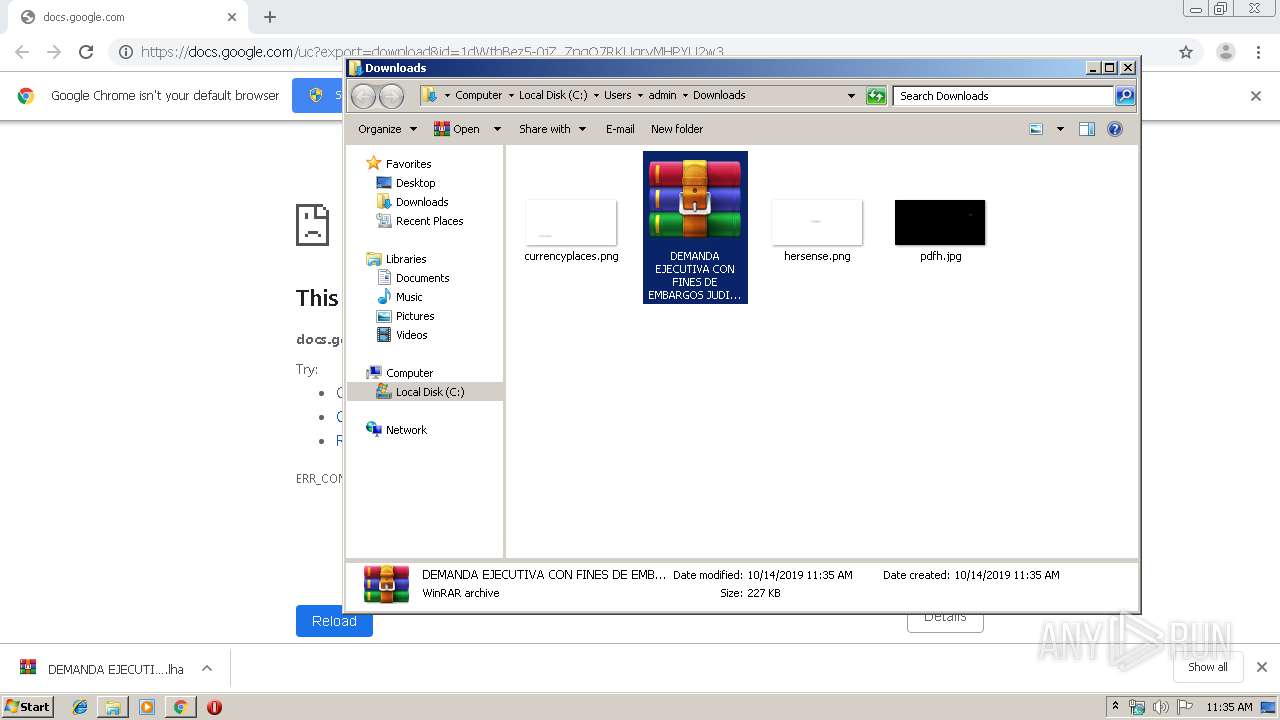
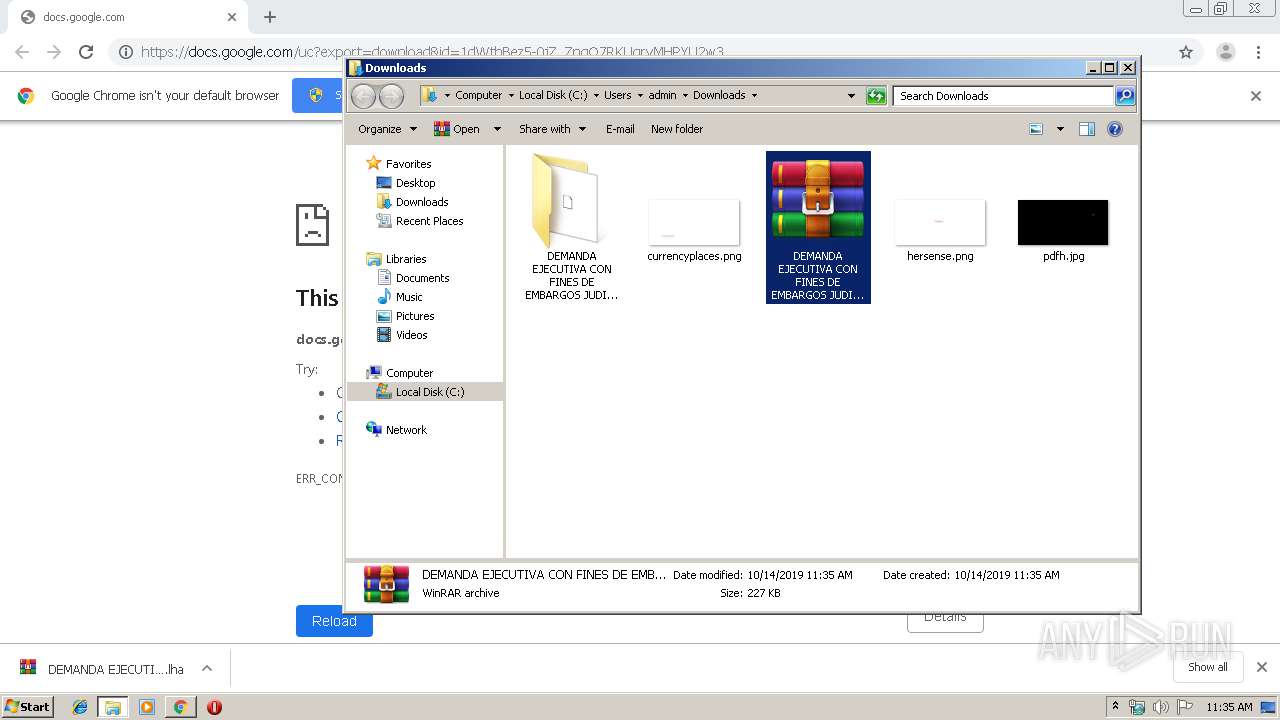
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2580)
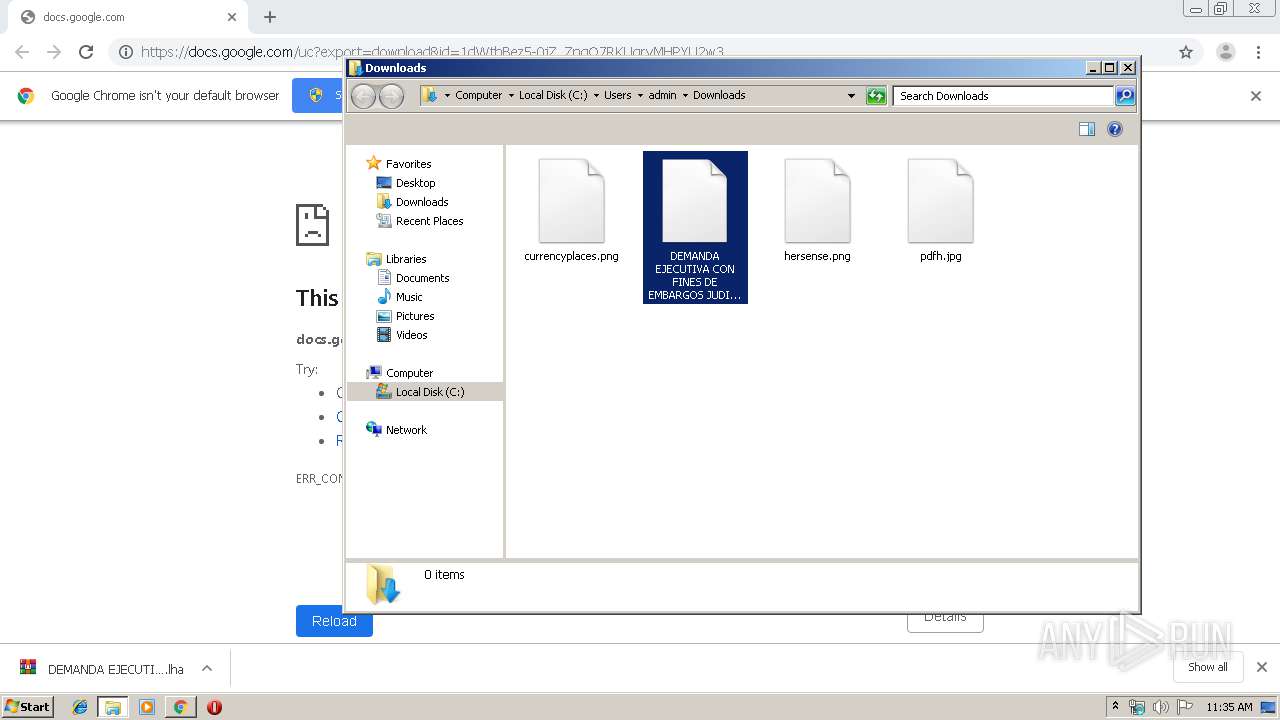
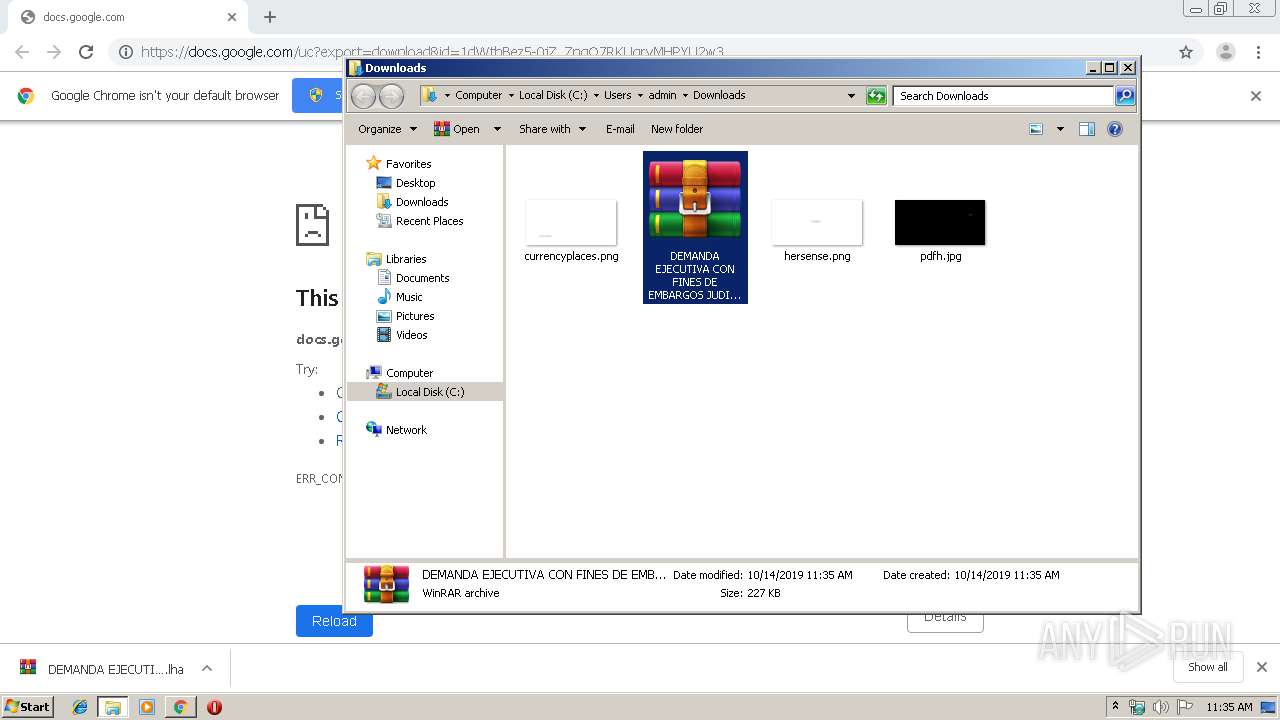
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2088)
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 1516)
Application launched itself
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 1516)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2580)
Reads the hosts file
- chrome.exe (PID: 2580)
- chrome.exe (PID: 600)
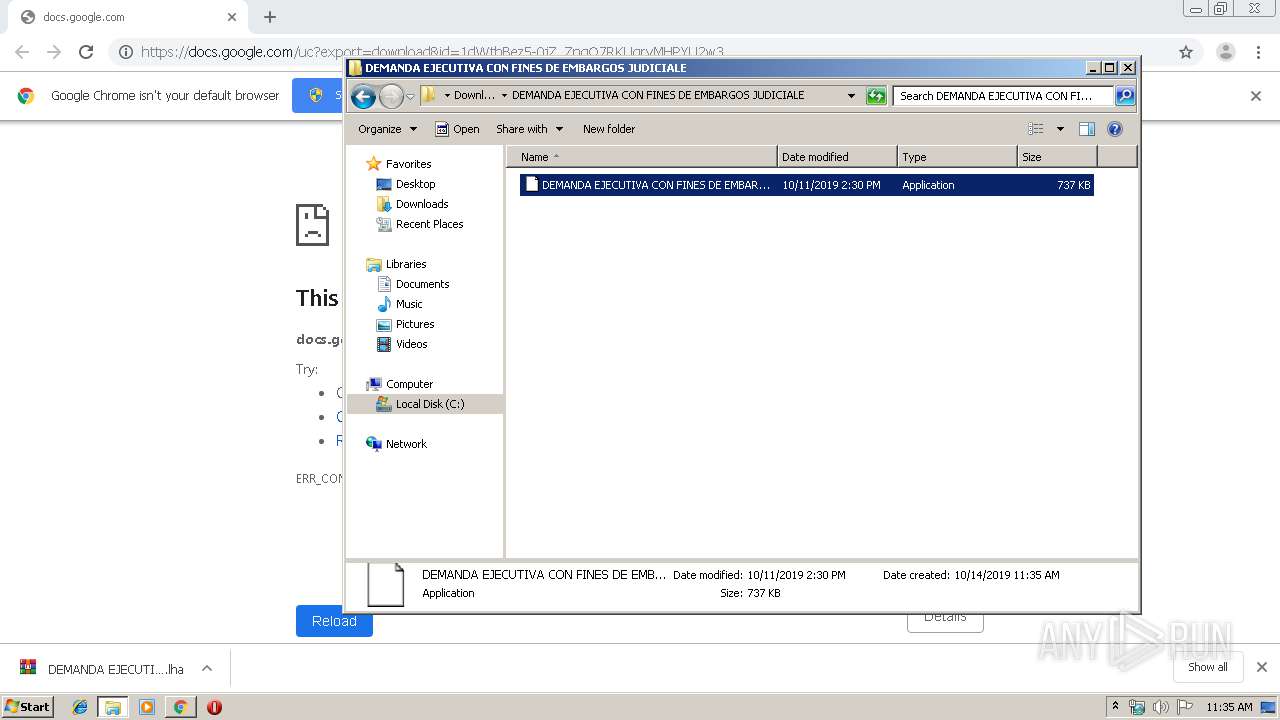
Manual execution by user
- WinRAR.exe (PID: 2088)
- DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe (PID: 1516)
Application launched itself
- chrome.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
36
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1822948215977151314 --mojo-platform-channel-handle=4004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4054252296135548087 --mojo-platform-channel-handle=4388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4714387602834012596 --mojo-platform-channel-handle=3364 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8524033155410690648 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13869773635887391478 --mojo-platform-channel-handle=4860 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=532 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\Downloads\DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALE\DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe" | C:\Users\admin\Downloads\DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALE\DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14035271280628247575 --mojo-platform-channel-handle=3716 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4257627072176797448 --mojo-platform-channel-handle=3952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
1 431
Read events
1 306
Write events
120
Delete events
5
Modification events
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2580-13215522877245500 |
Value: 259 | |||
Executable files
2
Suspicious files
16
Text files
206
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4869ae8c-87df-47d5-8218-f6450a5fba16.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
600 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
600 | chrome.exe | GET | 204 | 216.58.208.35:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
600 | chrome.exe | GET | 200 | 173.194.5.203:80 | http://r5---sn-aigl6n76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.7&mm=28&mn=sn-aigl6n76&ms=nvh&mt=1571049201&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
600 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
600 | chrome.exe | GET | 200 | 173.194.183.168:80 | http://r3---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.7&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1571049201&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
600 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 216.58.208.35:80 | www.gstatic.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 216.58.208.33:443 | doc-0o-70-docs.googleusercontent.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
600 | chrome.exe | 173.194.183.168:80 | r3---sn-aigl6ney.gvt1.com | Google Inc. | US | whitelisted |
— | — | 181.58.132.31:1992 | callejasdns.duckdns.org | Telmex Colombia S.A. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
doc-0o-70-docs.googleusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
Process | Message |
|---|---|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5DEMANDA EJECUTIVA CON FINES DE EMBARGOS JUDICIALES N°46976563-5.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|