| File name: | Employee_W2_Form.docx |
| Full analysis: | https://app.any.run/tasks/a23abb0e-5027-4220-826b-e3a420984311 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2024, 17:03:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/octet-stream |
| File info: | Microsoft OOXML |
| MD5: | 45E7D6562BFDDB816D45649DD667ABDE |
| SHA1: | 00087E46EC0EF6225DE59868FD016BD9DD77FA3C |
| SHA256: | 679BBE0C50754853978A3A583505EBB99BCE720CF26A6AAF8BE06CD879701FF1 |
| SSDEEP: | 192:f6ijVmar18H111M05AgPekrFD2h0vsmyVk7PeOJ2wc3rMKkokceeQh:f6ijca6H111/eo1hvsHieIhoseQh |
MALICIOUS
CVE-2022-30190 detected
- WINWORD.EXE (PID: 3744)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- WINWORD.EXE (PID: 3744)
INFO
The process uses the downloaded file
- WINWORD.EXE (PID: 3744)
Drops encrypted VBS script (Microsoft Script Encoder)
- WINWORD.EXE (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:09:11 11:32:36 |
| ZipCRC: | 0x1e3c81b4 |
| ZipCompressedSize: | 358 |
| ZipUncompressedSize: | 1416 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | 34 minutes |
| Pages: | 1 |
| Words: | 206 |
| Characters: | 1176 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 9 |
| Paragraphs: | 2 |
| ScaleCrop: | No |
| Company: | Consumers Association |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1380 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| LastModifiedBy: | user |
| RevisionNumber: | 6 |
| CreateDate: | 2013:10:31 15:25:00Z |
| ModifyDate: | 2021:08:31 16:47:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Microsoft |
| Description: | - |
| Language: | en-US |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
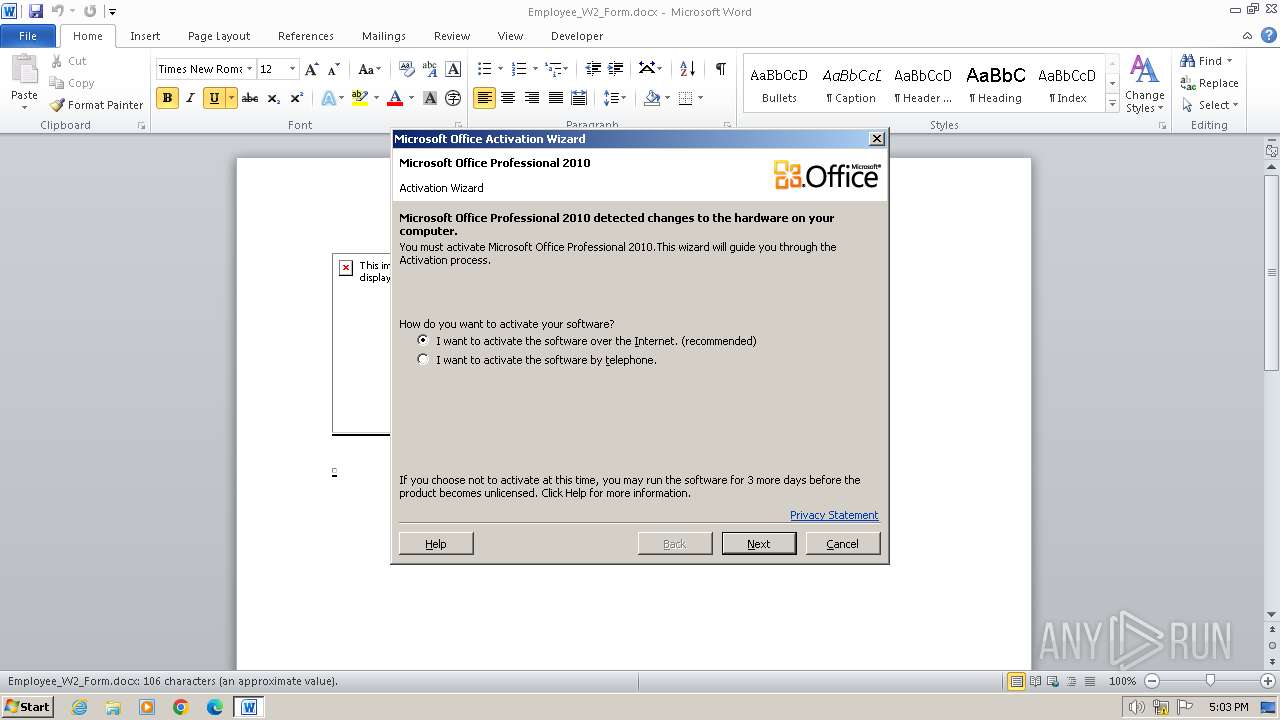
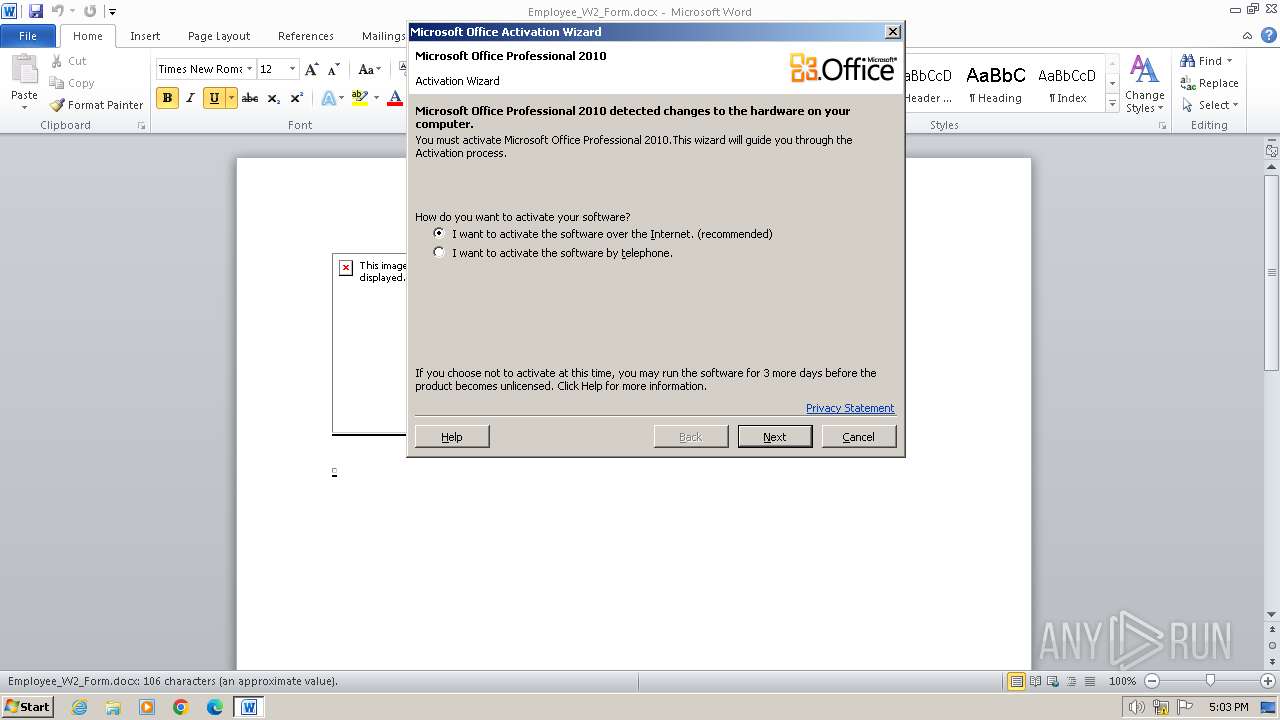
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3744 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\Employee_W2_Form.docx | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 411
Read events
3 616
Write events
548
Delete events
247
Modification events
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /n/ |
Value: 2F6E2F00A00E0000010000000000000000000000 | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC27F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ployee_W2_Form.docx | binary | |
MD5:CFAA0955E52E8ABCEB02D589B096977E | SHA256:B6FFC953E38F762416774815649D95D14D551BB5E57A508BC07A86ABD78B5088 | |||
| 3744 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:4E2FDB6D8B29D038A386ECEABA882E57 | SHA256:40A2ACED0CF44E16365B0D1EFDB979DEE94A533F83EFEF82B6AA1C61E7C478C9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |