| File name: | Clivet.exe |
| Full analysis: | https://app.any.run/tasks/8bcfde7b-1acf-4239-967a-4f744713a080 |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2025, 22:02:29 |
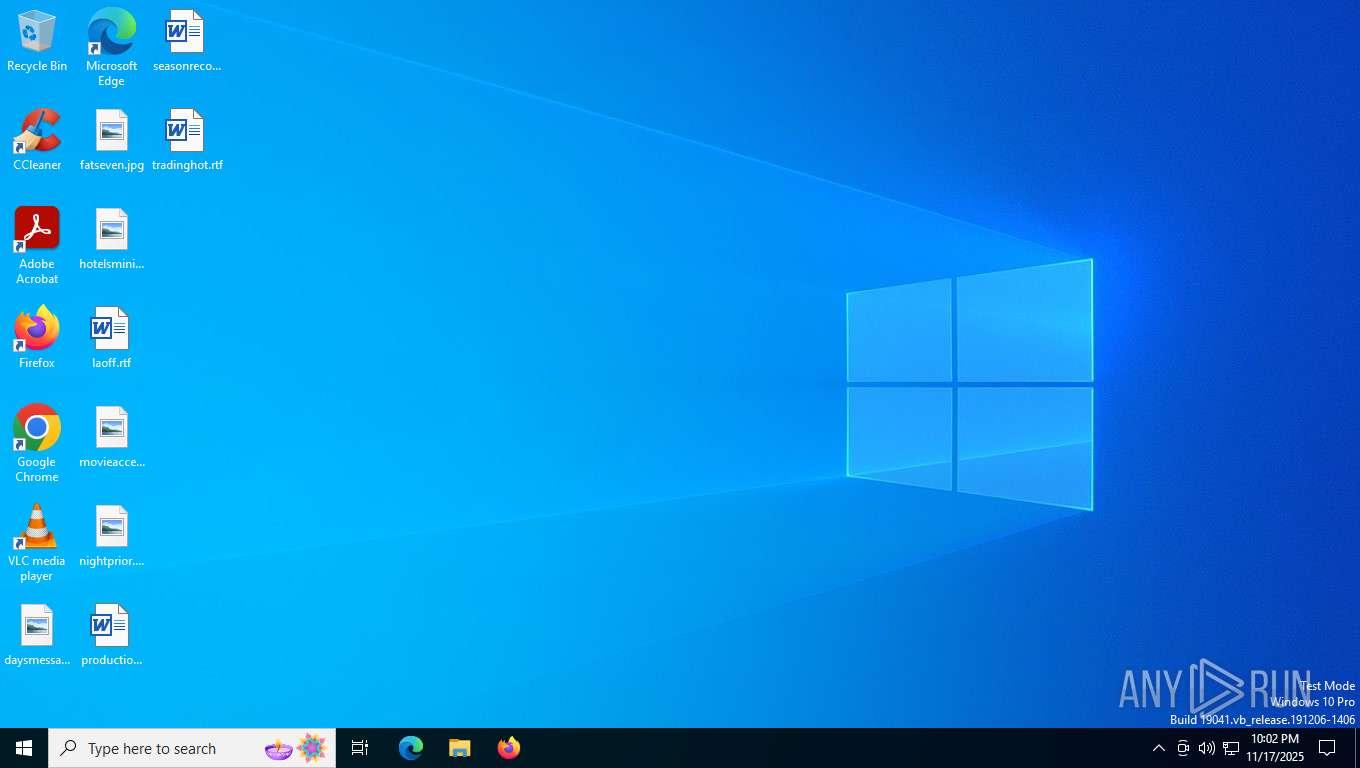
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 12 sections |
| MD5: | 68A263C182F56B186B351E31C98AE328 |
| SHA1: | DE04681E7E018B7079F43F10CCCA68C53F1D504F |
| SHA256: | 6791C14DAC031B23190BBB79281BE8E048F56700EC745BE83AE8D2D3075CC1CA |
| SSDEEP: | 98304:qlnnuR40xOCkQio74V0c5m2AD+vFTFJGtmbkp4G+qGUWdBCy04V2gExDLfjMB6F5:RQc706B0VJtThplJz2nn1/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- Clivet.exe (PID: 7316)
NUITKA compiler has been detected
- Clivet.exe (PID: 7316)
Application launched itself
- Clivet.exe (PID: 7316)
Executable content was dropped or overwritten
- Clivet.exe (PID: 7316)
Loads Python modules
- Clivet.exe (PID: 7412)
The process drops C-runtime libraries
- Clivet.exe (PID: 7316)
Process drops legitimate windows executable
- Clivet.exe (PID: 7316)
Reads security settings of Internet Explorer
- Clivet.exe (PID: 7316)
INFO
Create files in a temporary directory
- Clivet.exe (PID: 7316)
- Clivet.exe (PID: 7412)
Checks supported languages
- Clivet.exe (PID: 7316)
- Clivet.exe (PID: 7412)
The sample compiled with english language support
- Clivet.exe (PID: 7316)
Reads the machine GUID from the registry
- Clivet.exe (PID: 7412)
Reads the computer name
- Clivet.exe (PID: 7412)
- Clivet.exe (PID: 7316)
Checks proxy server information
- slui.exe (PID: 8088)
Reads the software policy settings
- slui.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:11:16 19:08:47+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.43 |
| CodeSize: | 128512 |
| InitializedDataSize: | 15858688 |
| UninitializedDataSize: | 163328 |
| EntryPoint: | 0x10f6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
145
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7316 | "C:\Users\admin\Desktop\Clivet.exe" | C:\Users\admin\Desktop\Clivet.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7412 | C:\Users\admin\Desktop\Clivet.exe | C:\Users\admin\Desktop\Clivet.exe | — | Clivet.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 8088 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 170
Read events
4 170
Write events
0
Delete events
0
Modification events
Executable files
89
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_cffi_backend.pyd | executable | |
MD5:04FD1A452E91605545A267CB04CDD78F | SHA256:C379126647AF2CBFB592D6A921F6218DA59B886E2A56E9B82F8159ACED6F1100 | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\exelbey.dll | executable | |
MD5:34996B56C8C4A72A5D0C8FCBC15755A3 | SHA256:2B921B0C2C88BBA0041A190CB05B5B9B91442C9D06756E400854A1AA8ECC49BF | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_ctypes.pyd | executable | |
MD5:79F339753DC8954B8EB45FE70910937E | SHA256:35CDD122679041EBEF264DE5626B7805F3F66C8AE6CC451B8BC520BE647FA007 | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_bz2.pyd | executable | |
MD5:B45E82A398713163216984F2FEBA88F6 | SHA256:4C2649DC69A8874B91646723AACB84C565EFEAA4277C46392055BCA9A10497A8 | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\mfc140u.dll | executable | |
MD5:03A161718F1D5E41897236D48C91AE3C | SHA256:E06C4BD078F4690AA8874A3DEB38E802B2A16CCB602A7EDC2E077E98C05B5807 | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_sqlite3.pyd | executable | |
MD5:6486E5C8512BDDC5F5606D11FE8F21E0 | SHA256:728D21BE4D47DD664CAF9FA60C1369FE059BC0498EDD383B27491D0DEE23E439 | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_hashlib.pyd | executable | |
MD5:CFB9E0A73A6C9D6D35C2594E52E15234 | SHA256:50DAEB3985302A8D85CE8167B0BF08B9DA43E7D51CEAE50E8E1CDFB0EDF218C6 | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_queue.pyd | executable | |
MD5:C9EE37E9F3BFFD296ADE10A27C7E5B50 | SHA256:9ECEC72C5FE3C83C122043CAD8CEB80D239D99D03B8EA665490BBCED183CE42A | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_elementtree.pyd | executable | |
MD5:1FECAC327FC93FC161833AD709336BBB | SHA256:16480EDE0430BE5249481A9BFB843EB0EF98F93B467A5428352FC23CC8C9051D | |||
| 7316 | Clivet.exe | C:\Users\admin\AppData\Local\Temp\onefile_7316_134078905609083203\_socket.pyd | executable | |
MD5:5DD51579FA9B6A06336854889562BEC0 | SHA256:3669E56E99AE3A944FBE7845F0BE05AEA96A603717E883D56A27DC356F8C2F2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
44
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 20.190.160.65:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | unknown |
— | — | POST | 200 | 20.190.160.66:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 29.1 Kb | unknown |
7872 | SIHClient.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7872 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
6456 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
7872 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 29.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6456 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2408 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6456 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2408 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6776 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |