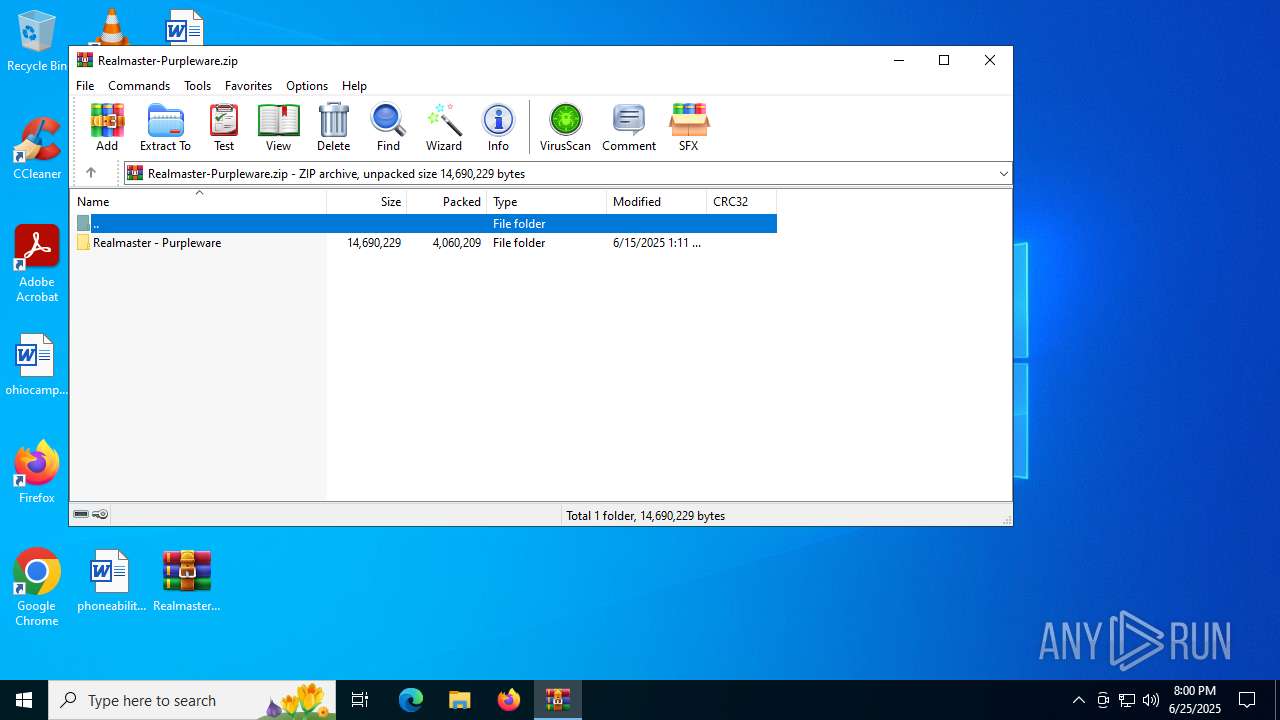
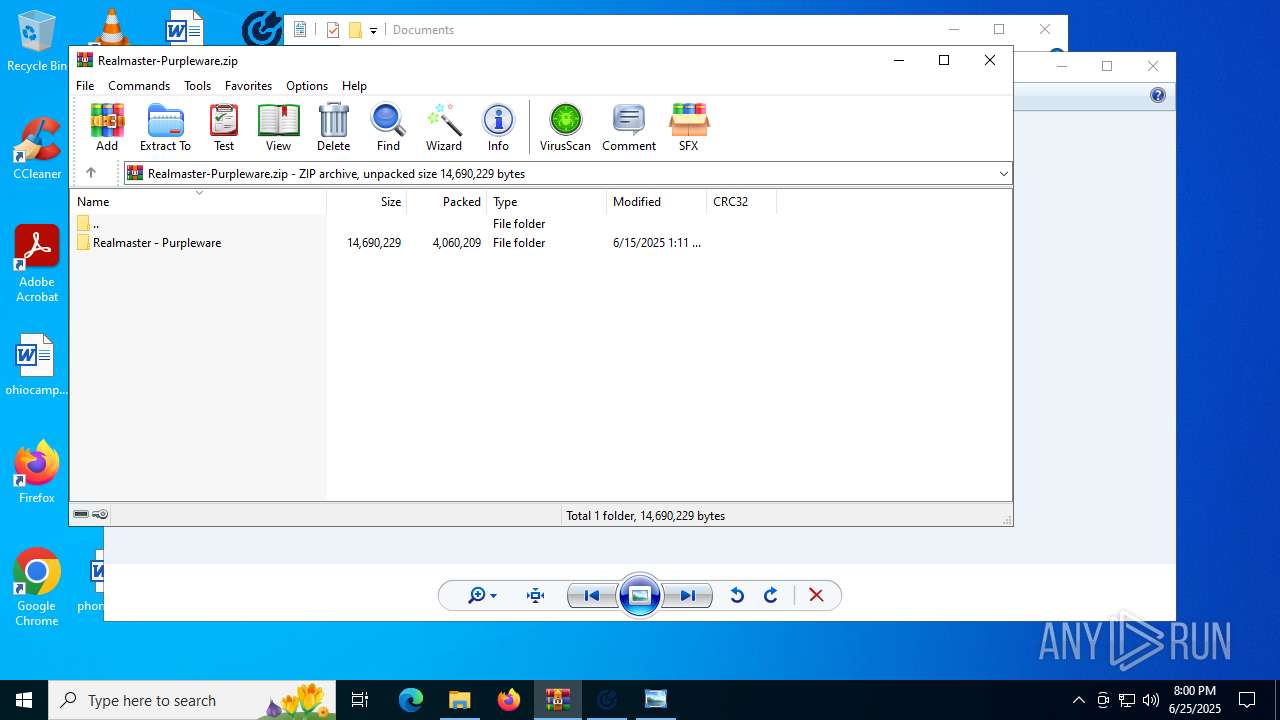
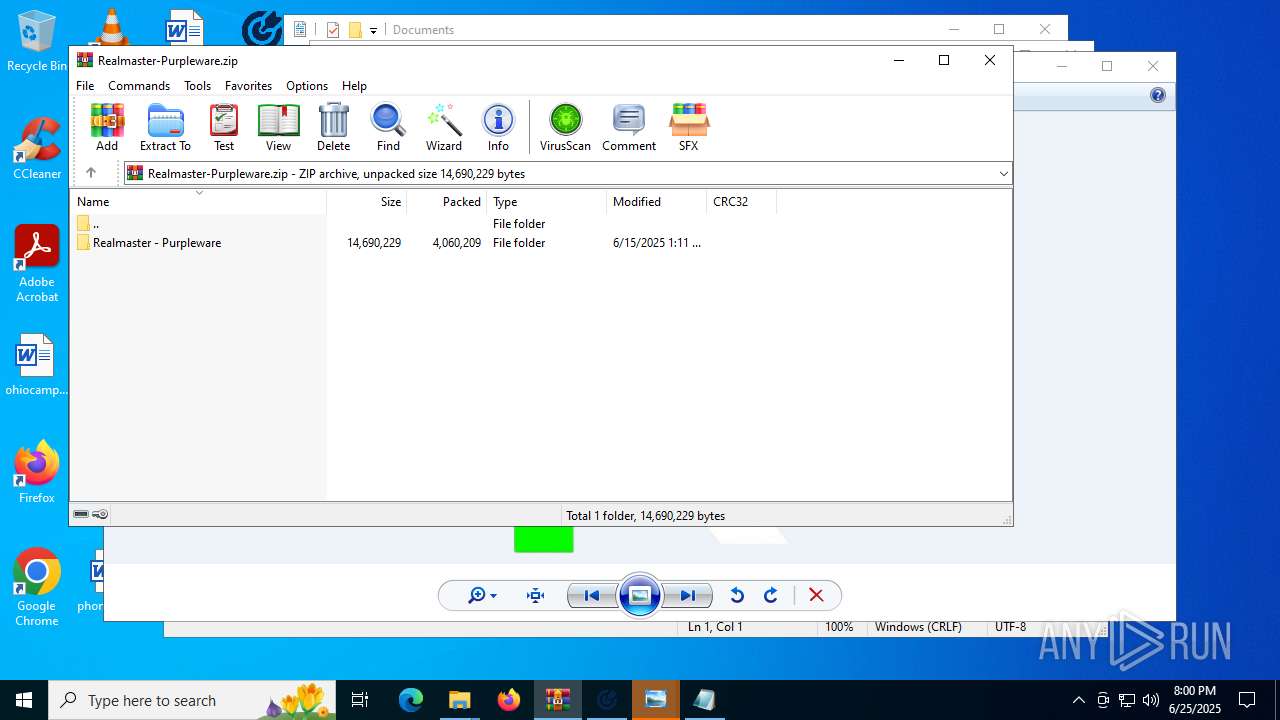
| File name: | Realmaster-Purpleware.zip |
| Full analysis: | https://app.any.run/tasks/dfc0c86c-a0cb-4604-abc2-bce949047e33 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2025, 19:59:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 972077F4A62070F5DB5F2256802546B5 |
| SHA1: | 6F278639CFFCD55256AC0DB39C03BC56576F173F |
| SHA256: | 6786DF618A896966C2443BA4AF8B60543A0F1BE2278D48A2BAADA965272B412D |
| SSDEEP: | 98304:JznpEGaudRX8ezuXSGHd1PMuDClulDOYWtaSWRPoO1HBW2GVp4ZSIhoo9zkWEfH3:c11rar4+BX |
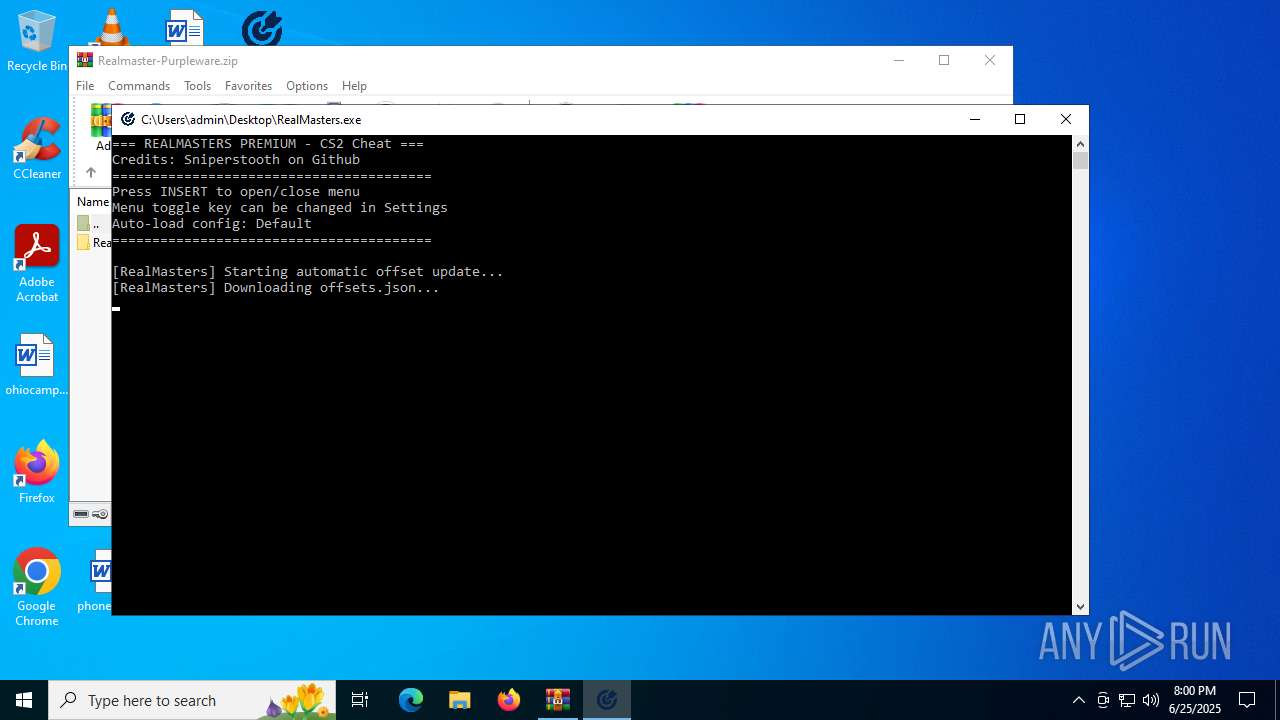
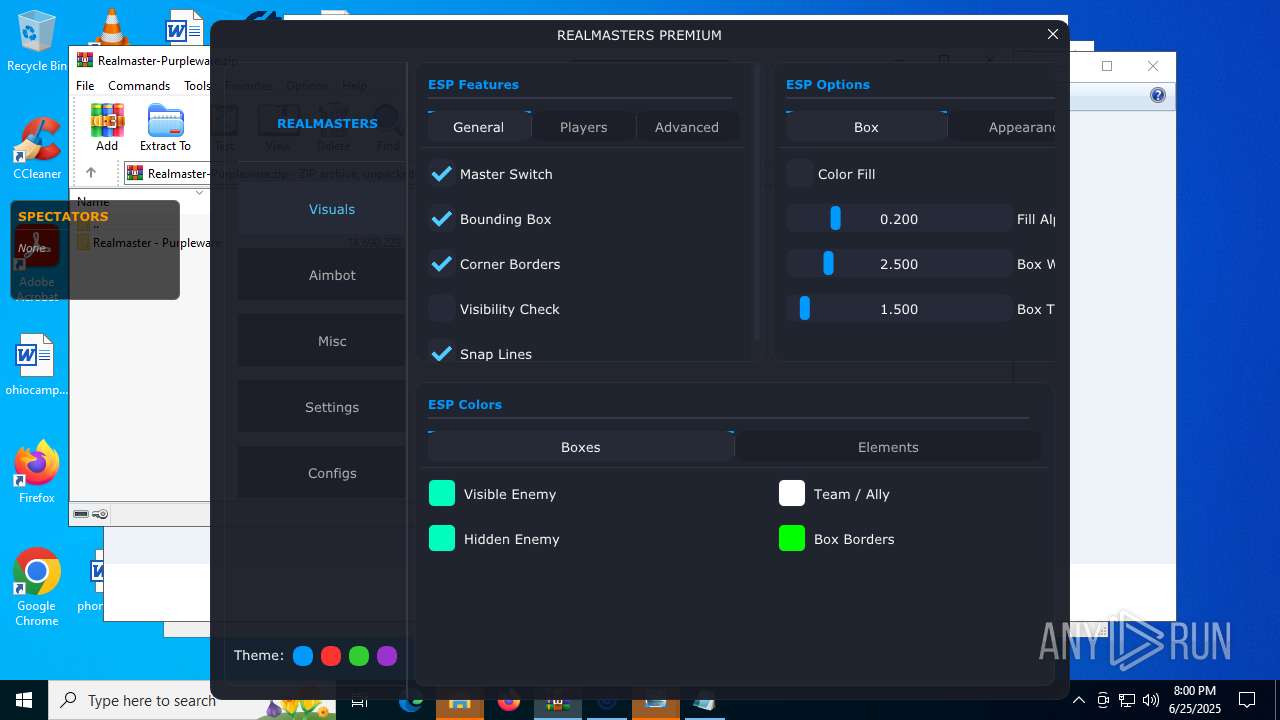
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7100)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3196)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 1180)
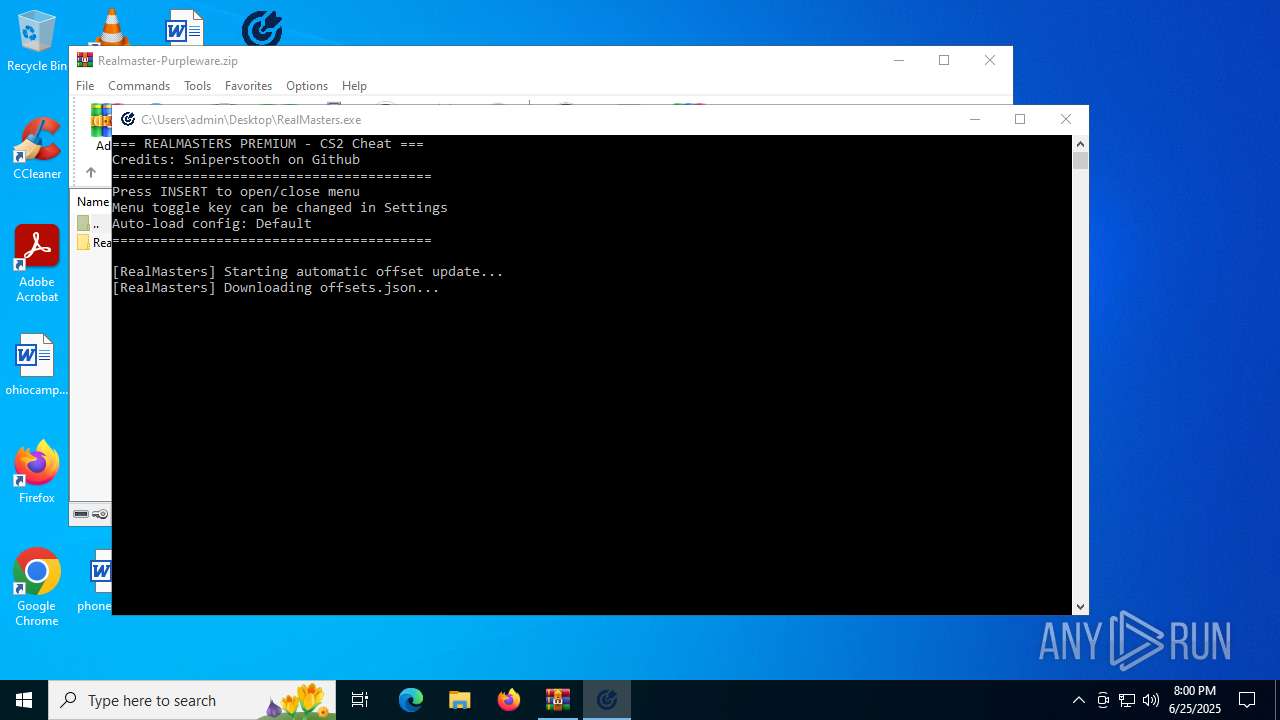
Downloads file from URI via Powershell
- powershell.exe (PID: 2632)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 2704)
Starts CMD.EXE for commands execution
- RealMasters.exe (PID: 5432)
INFO
Checks supported languages
- RealMasters.exe (PID: 5432)
Manual execution by a user
- RealMasters.exe (PID: 5432)
- notepad.exe (PID: 892)
- rundll32.exe (PID: 2648)
- rundll32.exe (PID: 5060)
- rundll32.exe (PID: 7072)
- rundll32.exe (PID: 3460)
- rundll32.exe (PID: 2180)
Reads the machine GUID from the registry
- RealMasters.exe (PID: 5432)
Reads the computer name
- RealMasters.exe (PID: 5432)
Reads the software policy settings
- RealMasters.exe (PID: 5432)
- slui.exe (PID: 6836)
Reads security settings of Internet Explorer
- notepad.exe (PID: 892)
Disables trace logs
- powershell.exe (PID: 2632)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 2704)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 2704)
Checks proxy server information
- powershell.exe (PID: 2632)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 2704)
- slui.exe (PID: 6836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:06:15 13:11:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Realmaster - Purpleware/ |
Total processes
149
Monitored processes
17
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\imgui.ini | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/buttons.json -OutFile buttons.json" | C:\Windows\System32\cmd.exe | — | RealMasters.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/client_dll.json -OutFile client_dll.json" | C:\Windows\System32\cmd.exe | — | RealMasters.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2180 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\aimbot.png | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RealMasters.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/offsets.json -OutFile offsets.json" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\logorm1.png | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2704 | powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/buttons.json -OutFile buttons.json" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3196 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/offsets.json -OutFile offsets.json" | C:\Windows\System32\cmd.exe | — | RealMasters.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3460 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\settings.png | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 172
Read events
27 161
Write events
11
Delete events
0
Modification events
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Realmaster-Purpleware.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
0
Suspicious files
5
Text files
6
Unknown types
0
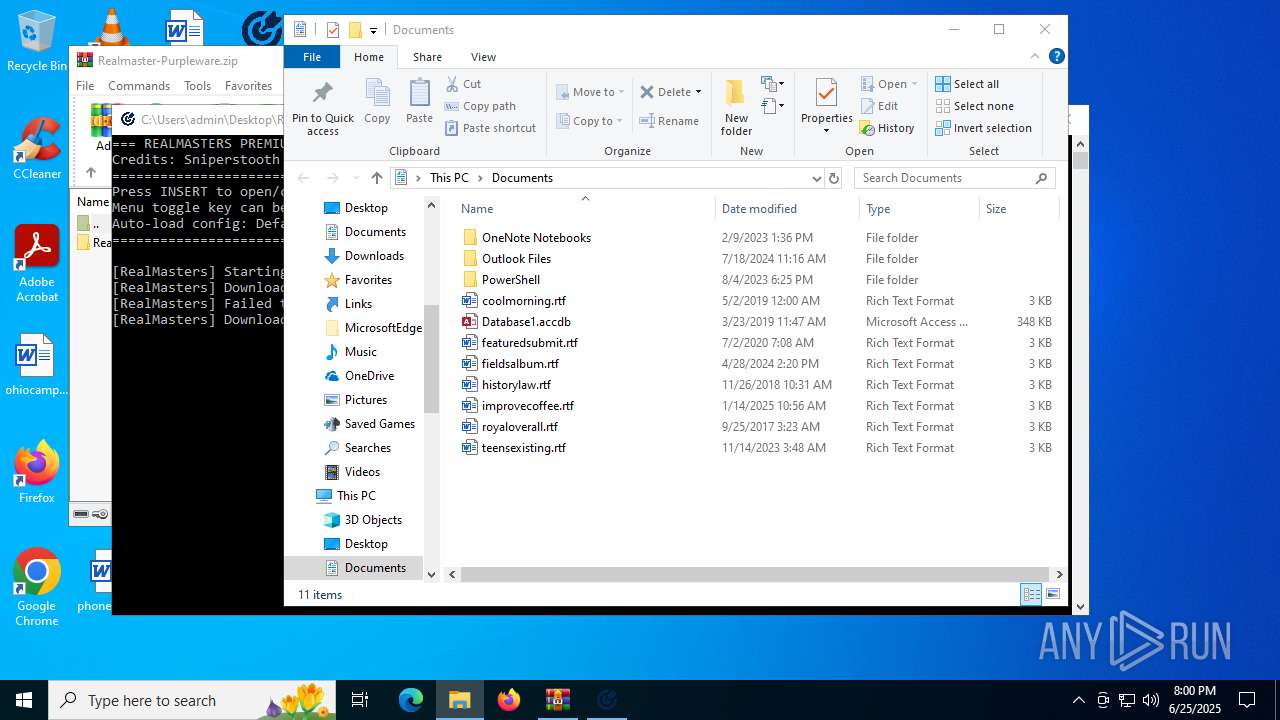
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ywwfdzbr.a4i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
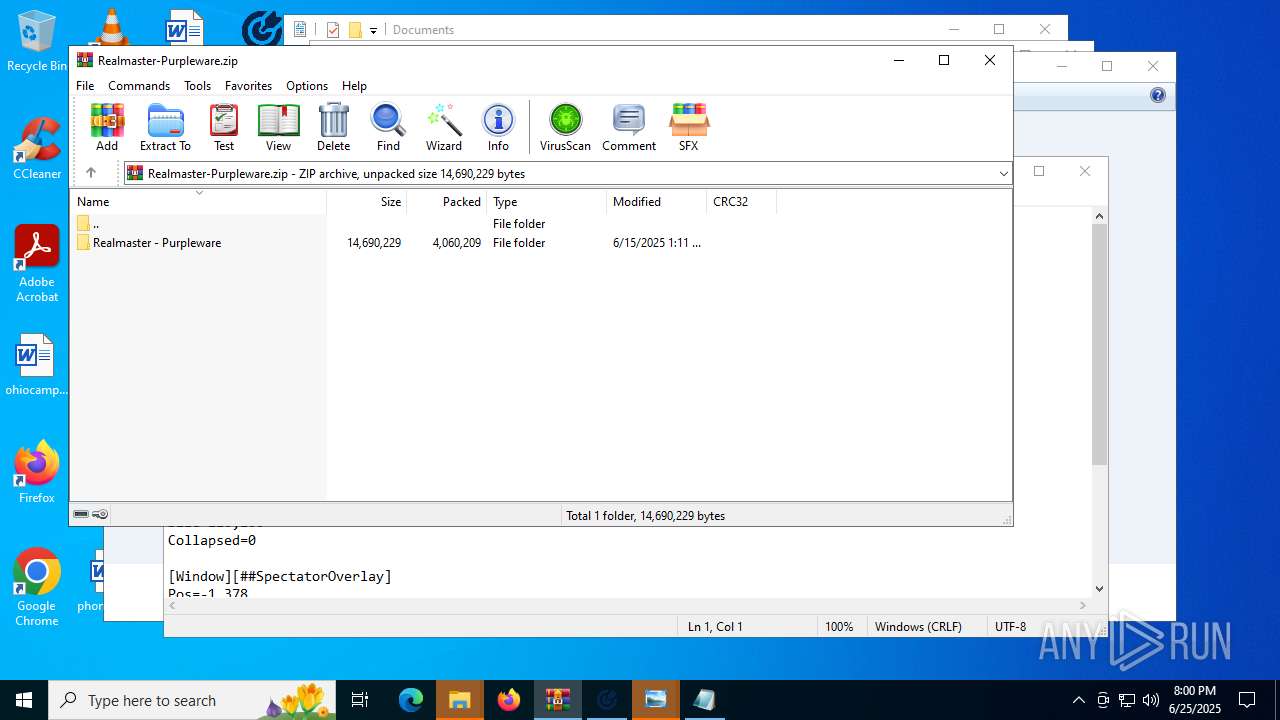
| 5432 | RealMasters.exe | C:\Users\admin\Documents\RealMasters\VisualsOnly.cfg | binary | |
MD5:1D9E0362005A861764DBBF8A6A5534CE | SHA256:CF91AF3E6D1F8F1AA496D43CAC307802D2695944E120389EAF8E21DD0B8B76FF | |||
| 4312 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g1icpm5j.dpk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2704 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hcy2lflb.rn4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4312 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tp0jusk3.jxo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5432 | RealMasters.exe | C:\Users\admin\Documents\RealMasters\Default.cfg | binary | |
MD5:CF9A7C6930A28F2C93FA21A0C4148D7C | SHA256:41552D9BF78FF6D86DC505775A783726658D60F3C2E5065F20A2C06DA4CD0D9C | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:08D2603235407959E233D456C1B11944 | SHA256:A52F3AEABF19A38821BD65D70DF1C9D8F36985E685A85646C9FECF14B75BDD2B | |||
| 5432 | RealMasters.exe | C:\Users\admin\Documents\RealMasters\Legit.cfg | binary | |
MD5:1105A0FF94B3F92626D470F36ED662B0 | SHA256:D9273CC9E93F361BA0D8144459C88C09E80EC2214EB079802F9B7FABCBFBA595 | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c51fkv4q.0mi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5432 | RealMasters.exe | C:\Users\admin\Documents\RealMasters\Rage.cfg | binary | |
MD5:4CED0D40F15F4438D38D4F20AD2FC939 | SHA256:A67896273E11899ED388EAC4BD28667FB1F41E918DF8B720601A37A209B62FAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
31
DNS requests
11
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4372 | RUXIMICS.exe | GET | 200 | 23.48.23.191:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.191:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.191:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/offsets.json | unknown | binary | 1.26 Kb | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4372 | RUXIMICS.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/client_dll.json | unknown | binary | 405 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/buttons.json | unknown | binary | 411 b | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/a2x/cs2-dumper/main/output/offsets.json | unknown | binary | 1.26 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4372 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4372 | RUXIMICS.exe | 23.48.23.191:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.48.23.191:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.48.23.191:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5432 | RealMasters.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
Process | Message |
|---|---|
RealMasters.exe | Logo file not found at: src/ui/icons/logorm1.png
|
RealMasters.exe | Logo file not found at: logorm1.png
|
RealMasters.exe | Logo loading failed for all paths
|
RealMasters.exe | D3D11 device is ready, attempting logo load
|
RealMasters.exe | Logo file not found at: icons/logorm1.png
|
RealMasters.exe | Logo file not found at: ./src/ui/icons/logorm1.png
|
RealMasters.exe | Logo file not found at: icons/logorm1.png
|
RealMasters.exe | Logo file not found at: ./src/ui/icons/logorm1.png
|
RealMasters.exe | Logo loading failed for all paths
|
RealMasters.exe | Logo file not found at: src/ui/icons/logorm1.png
|