| File name: | presentation16181.jnlp |
| Full analysis: | https://app.any.run/tasks/e5241250-90c9-4173-8566-5b315094b21c |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2021, 13:02:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with CRLF, LF line terminators |
| MD5: | F51380A080032608580D56E9755DEA34 |
| SHA1: | 4BFD4A5DE500500CFC6C4E909B95A4BC5F6898C9 |
| SHA256: | 678355D854068A1430F2FEA87FF1F6FD1BC153874FE67A8B2E1E1C29C166B516 |
| SSDEEP: | 12:TMHdINMd/OdLnx04JodSh8J/umdbbc8POvn:2dkqOdLnx0uzA/umREv |
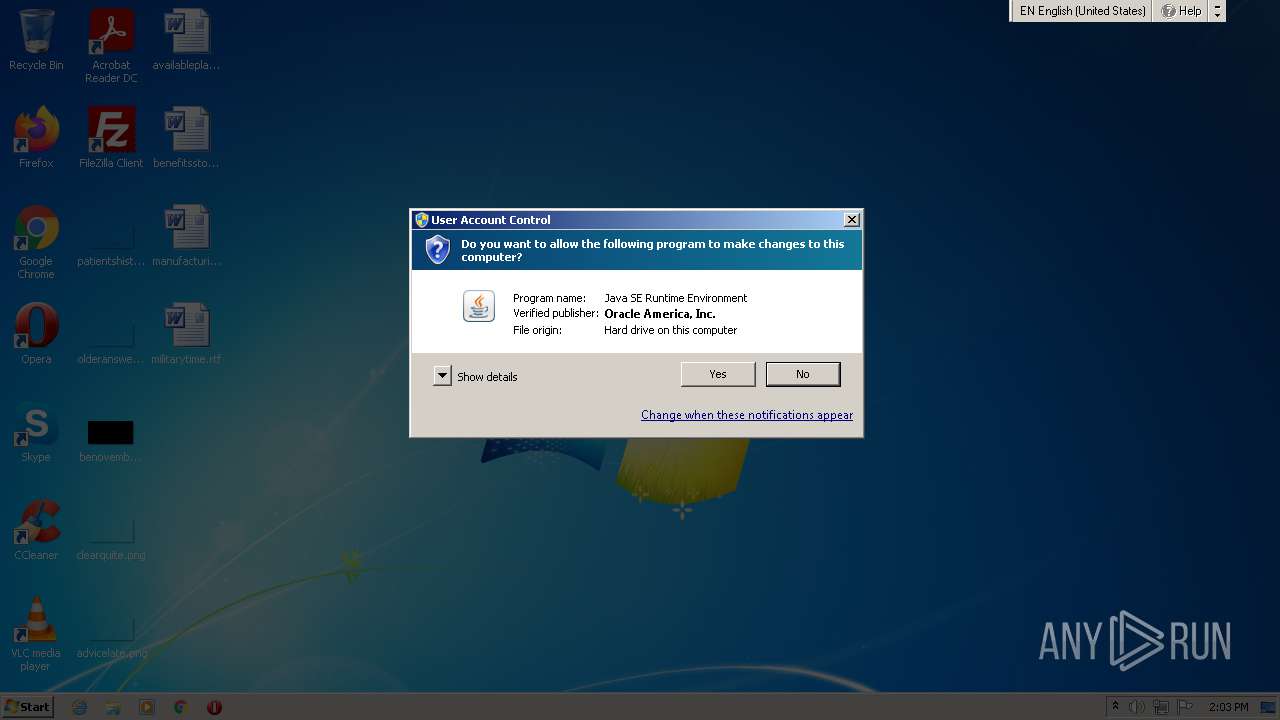
MALICIOUS
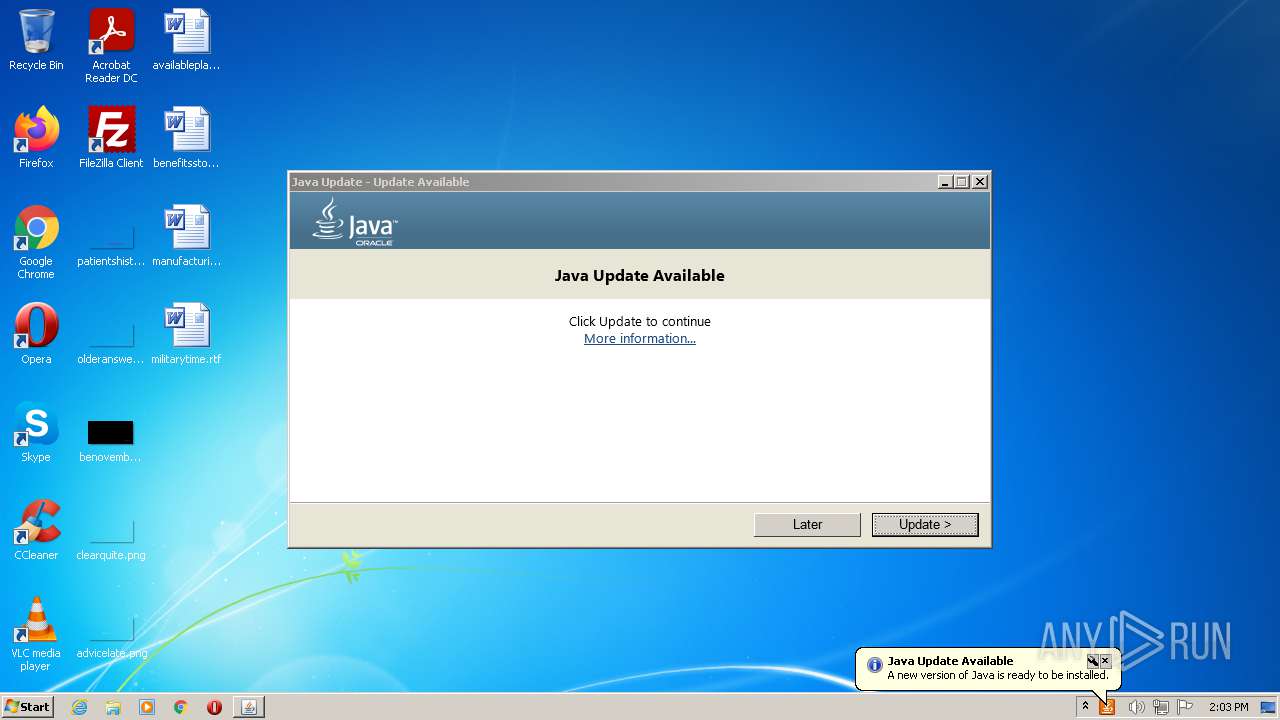
Changes settings of System certificates
- jucheck.exe (PID: 2000)
Application was dropped or rewritten from another process
- jre-8u291-windows-au.exe (PID: 2736)
- jre-8u291-windows-au.exe (PID: 3328)
Drops executable file immediately after starts
- jre-8u291-windows-au.exe (PID: 2736)
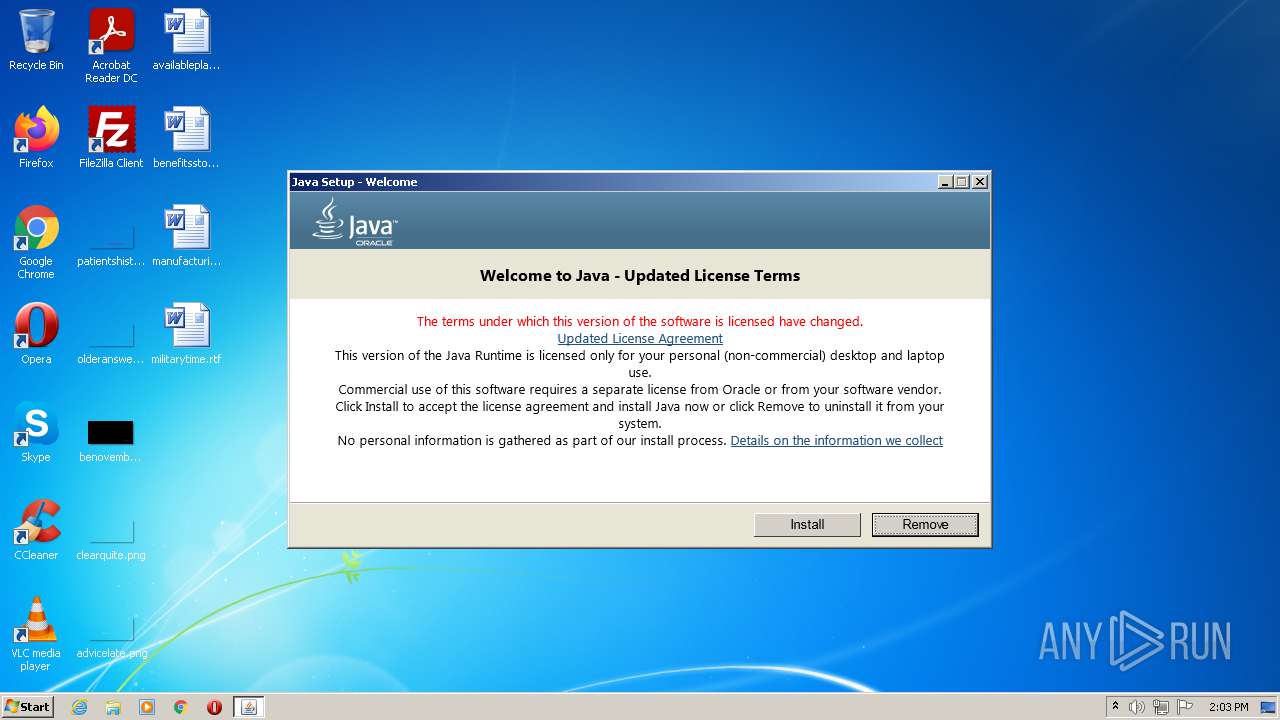
SUSPICIOUS
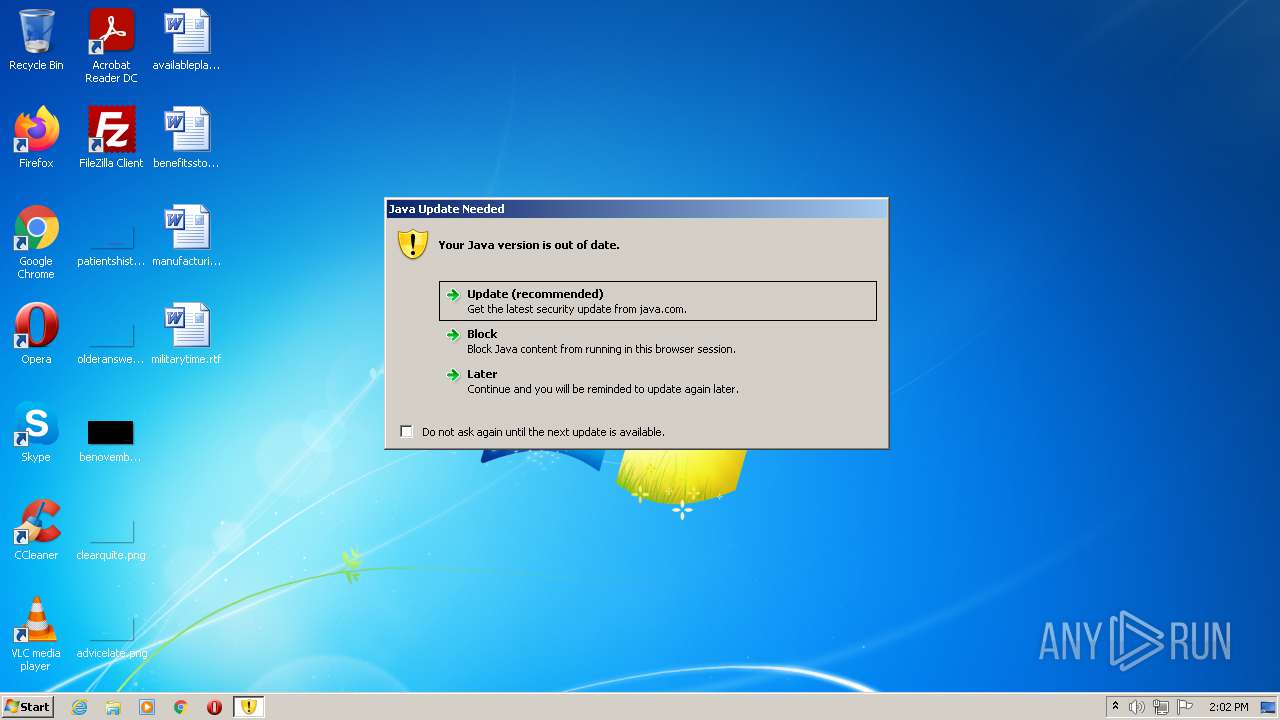
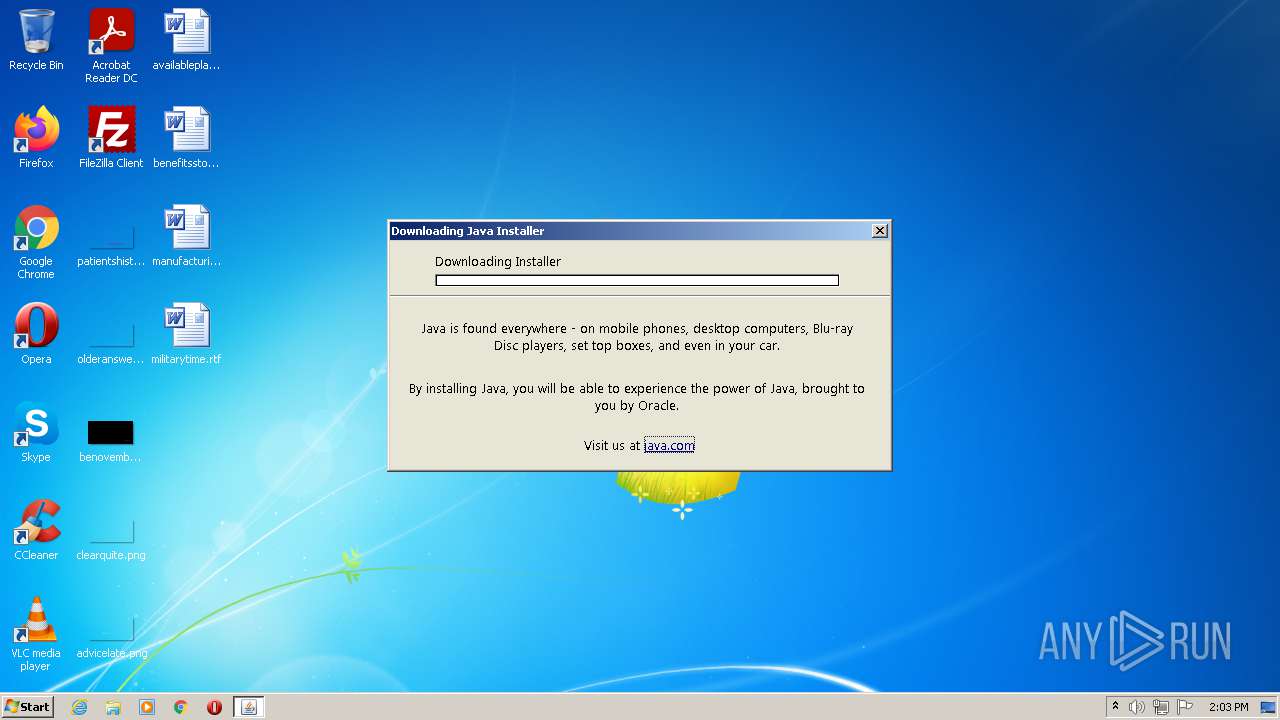
Check for Java to be installed
- javaws.exe (PID: 3912)
- javaw.exe (PID: 3228)
- javaw.exe (PID: 2544)
- javaw.exe (PID: 3388)
- jp2launcher.exe (PID: 2568)
- jucheck.exe (PID: 2000)
Checks supported languages
- javaws.exe (PID: 3912)
- javaw.exe (PID: 3388)
- jucheck.exe (PID: 2000)
- javaw.exe (PID: 3228)
- javaws.exe (PID: 2344)
- jp2launcher.exe (PID: 2568)
- javaw.exe (PID: 2544)
- jre-8u291-windows-au.exe (PID: 2736)
- jre-8u291-windows-au.exe (PID: 3328)
Reads the computer name
- javaw.exe (PID: 2544)
- javaw.exe (PID: 3388)
- javaw.exe (PID: 3228)
- jp2launcher.exe (PID: 2568)
- jucheck.exe (PID: 2000)
- jre-8u291-windows-au.exe (PID: 2736)
- jre-8u291-windows-au.exe (PID: 3328)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 2544)
Creates files in the program directory
- javaw.exe (PID: 2544)
Executes JAVA applets
- javaws.exe (PID: 3912)
Reads Microsoft Outlook installation path
- jucheck.exe (PID: 2000)
- jre-8u291-windows-au.exe (PID: 3328)
Creates files in the user directory
- jucheck.exe (PID: 2000)
Executable content was dropped or overwritten
- jucheck.exe (PID: 2000)
- jre-8u291-windows-au.exe (PID: 2736)
Drops a file with a compile date too recent
- jucheck.exe (PID: 2000)
- jre-8u291-windows-au.exe (PID: 2736)
Reads internet explorer settings
- jucheck.exe (PID: 2000)
- jre-8u291-windows-au.exe (PID: 3328)
INFO
Reads the computer name
- icacls.exe (PID: 1872)
Checks supported languages
- icacls.exe (PID: 1872)
Checks Windows Trust Settings
- jucheck.exe (PID: 2000)
- jre-8u291-windows-au.exe (PID: 3328)
Reads settings of System Certificates
- jucheck.exe (PID: 2000)
- jp2launcher.exe (PID: 2568)
- jre-8u291-windows-au.exe (PID: 3328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jnlp | | | Java Web Start application descriptor (88.3) |
|---|---|---|
| .xml | | | Generic XML (ASCII) (11.6) |
EXIF
XMP
| JnlpApplication-desc: | |
|---|---|
| JnlpApplication-descMain-class: | Secure_Viewer |
| JnlpResourcesJarHref: | presentation.jar |
| JnlpResourcesJ2seVersion: | 1.6+ |
| JnlpSecurityAll-permissions: | - |
| JnlpInformationDescription: | Microsoft secure PowerPoint viewer |
| JnlpInformationHomepageHref: | www.microsoft.com |
| JnlpInformationVendor: | Microsoft |
| JnlpInformationTitle: | PowerPoint Secure Viewer |
| JnlpHref: | presentation.jnlp |
| JnlpCodebase: | https://java.ipq.gnw.mybluehost.me |
| JnlpSpec: | 1.0+ |
Total processes
49
Monitored processes
10
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1872 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Common Files\Java\Java Update\jucheck.exe" | C:\Program Files\Common Files\Java\Java Update\jucheck.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Checker Exit code: 0 Version: 2.8.271.9 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" -J-Djdk.disableLastUsageTracking=true -SSVBaselineUpdate | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | jucheck.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "update" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxwbHVnaW4uamFyAC1EamRrLmRpc2FibGVMYXN0VXNhZ2VUcmFja2luZz10cnVlAC1Eam5scHguanZtPUM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcYmluXGphdmF3LmV4ZQAtRGpubHB4LnZtYXJncz1MVVJxWkdzdVpHbHpZV0pzWlV4aGMzUlZjMkZuWlZSeVlXTnJhVzVuUFhSeWRXVUE= -ma LVNTVkJhc2VsaW5lVXBkYXRlAC1ub3RXZWJKYXZh | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\jre-8u291-windows-au.exe" /installmethod=jau-m FAMILYUPGRADE=1 | C:\Users\admin\AppData\Local\Temp\jre-8u291-windows-au.exe | jucheck.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2910.10 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1619701401" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\Temp\jds1210031.tmp\jre-8u291-windows-au.exe" "/installmethod=jau-m" "FAMILYUPGRADE=1" | C:\Users\admin\AppData\Local\Temp\jds1210031.tmp\jre-8u291-windows-au.exe | jre-8u291-windows-au.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2910.10 Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.271.2" "false" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3912 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" "C:\Users\admin\AppData\Local\Temp\presentation16181.jnlp" | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 1 Version: 11.271.2.09 Modules
| |||||||||||||||
Total events
14 849
Read events
14 490
Write events
336
Delete events
23
Modification events
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1604367352626 | |||
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.271.2 | |||
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\iexplore.exe | |||
| (PID) Process: | (2544) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.271.2 |
Value: update | |||
| (PID) Process: | (3228) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3228) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.271.2 |
Value: update | |||
| (PID) Process: | (3228) javaw.exe | Key: | HKEY_CURRENT_USER\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1619701401153 | |||
Executable files
4
Suspicious files
6
Text files
9
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2000 | jucheck.exe | C:\Users\admin\AppData\Local\Temp\jusched.log | text | |
MD5:— | SHA256:— | |||
| 2544 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 2544 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 2000 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2000 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 2544 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
| 2000 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | der | |
MD5:— | SHA256:— | |||
| 2000 | jucheck.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\TAEW0KYX.txt | text | |
MD5:— | SHA256:— | |||
| 2000 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | binary | |
MD5:— | SHA256:— | |||
| 2000 | jucheck.exe | C:\Users\admin\AppData\Local\Temp\jds1204343.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2000 | jucheck.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2568 | jp2launcher.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2568 | jp2launcher.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2568 | jp2launcher.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2000 | jucheck.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
2000 | jucheck.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a4d6a70d25689ed7 | US | compressed | 4.70 Kb | whitelisted |
2568 | jp2launcher.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2000 | jucheck.exe | 104.109.94.220:443 | javadl-esd-secure.oracle.com | Akamai International B.V. | NL | unknown |
2000 | jucheck.exe | 67.27.234.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2000 | jucheck.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2568 | jp2launcher.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2568 | jp2launcher.exe | 104.109.94.220:443 | javadl-esd-secure.oracle.com | Akamai International B.V. | NL | unknown |
2000 | jucheck.exe | 104.104.182.138:443 | javadl.oracle.com | Akamai International B.V. | NL | unknown |
2000 | jucheck.exe | 2.18.232.55:443 | sdlc-esd.oracle.com | Akamai International B.V. | — | whitelisted |
3328 | jre-8u291-windows-au.exe | 104.109.94.220:443 | javadl-esd-secure.oracle.com | Akamai International B.V. | NL | unknown |
3328 | jre-8u291-windows-au.exe | 104.104.182.138:443 | javadl.oracle.com | Akamai International B.V. | NL | unknown |
3328 | jre-8u291-windows-au.exe | 2.18.232.55:443 | sdlc-esd.oracle.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
javadl-esd-secure.oracle.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |