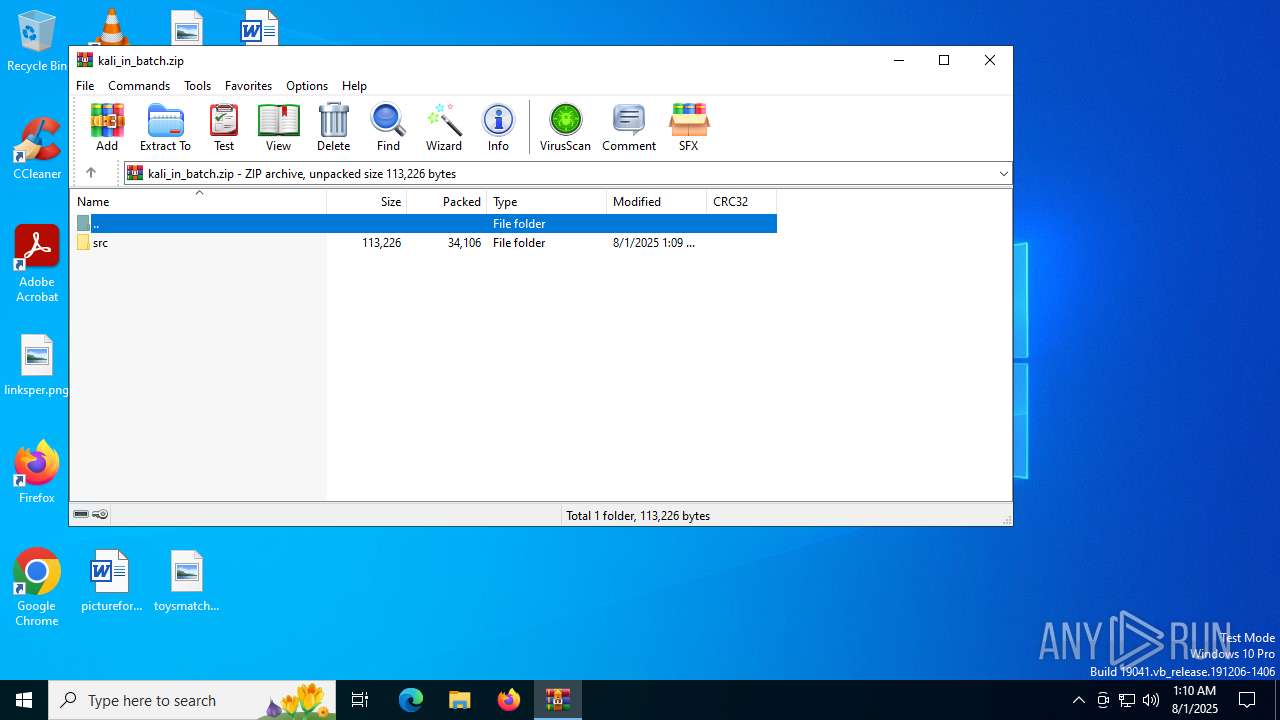
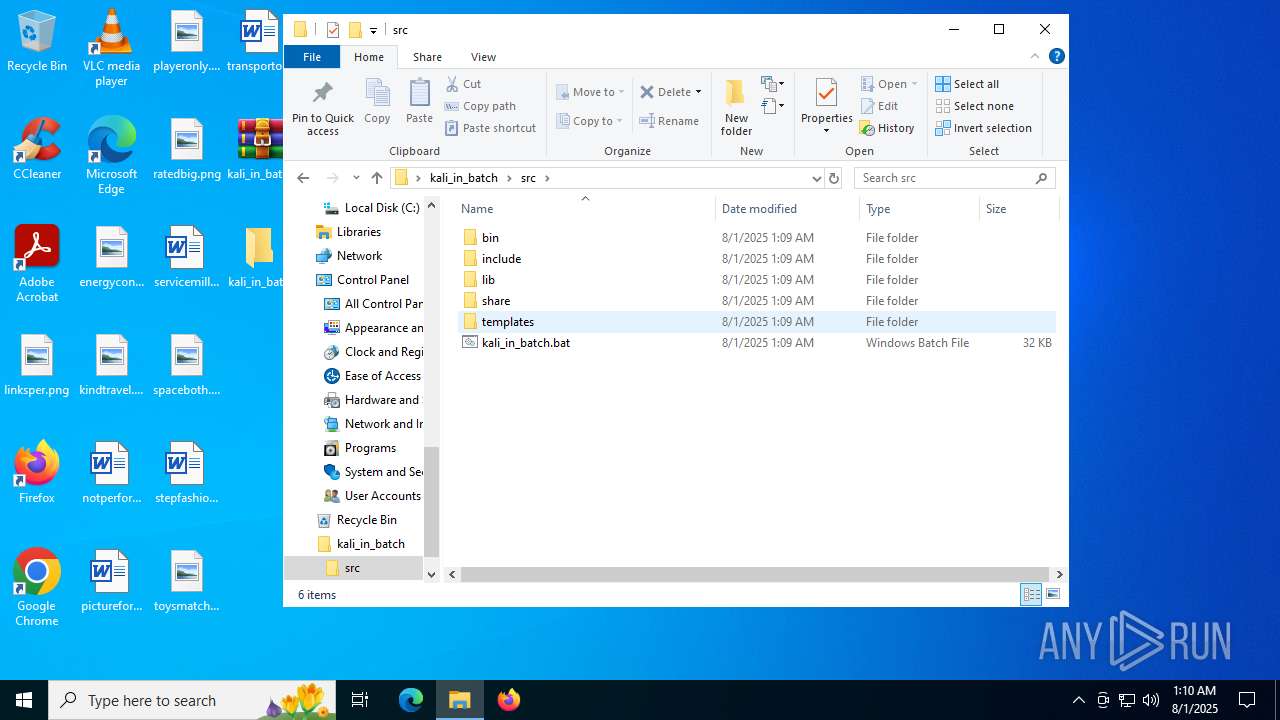
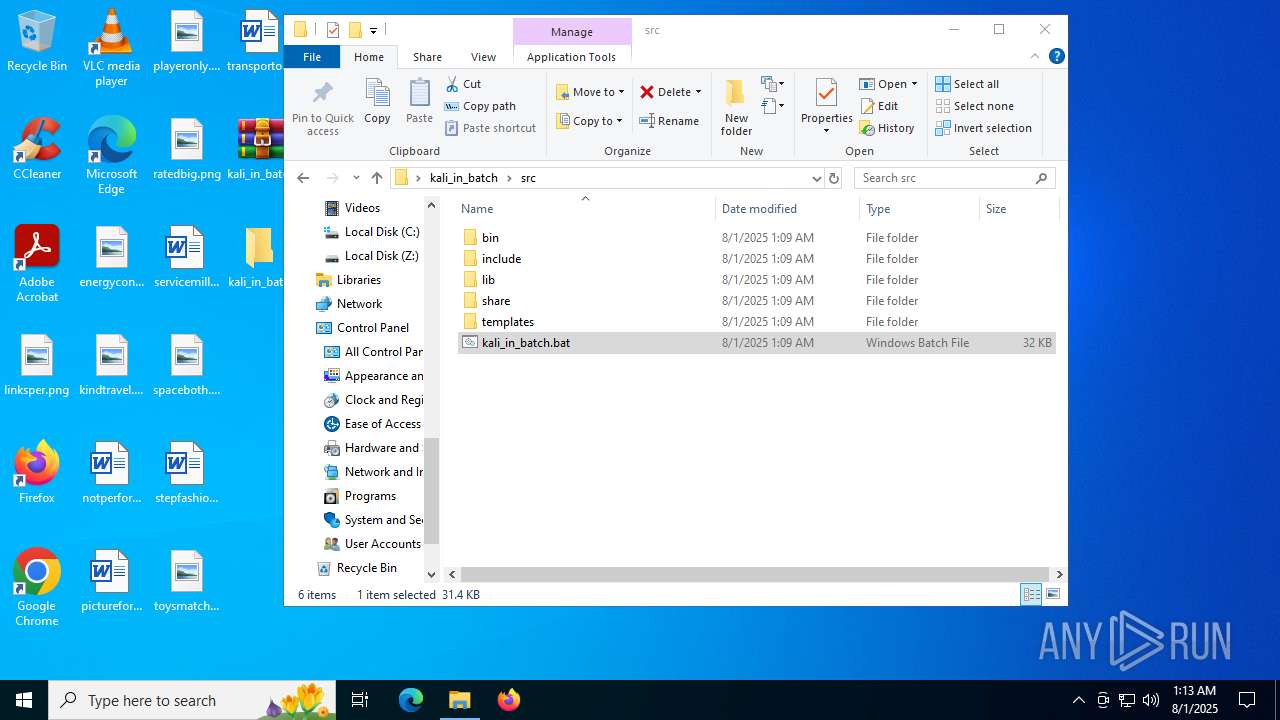
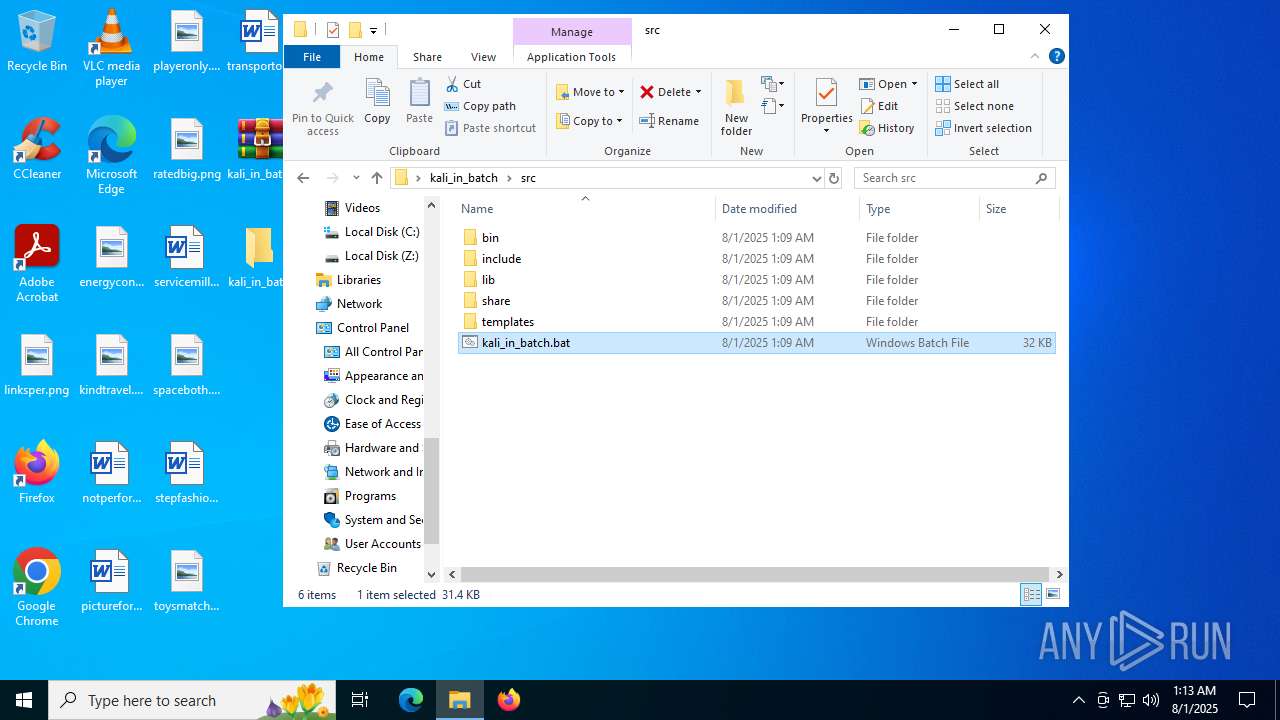
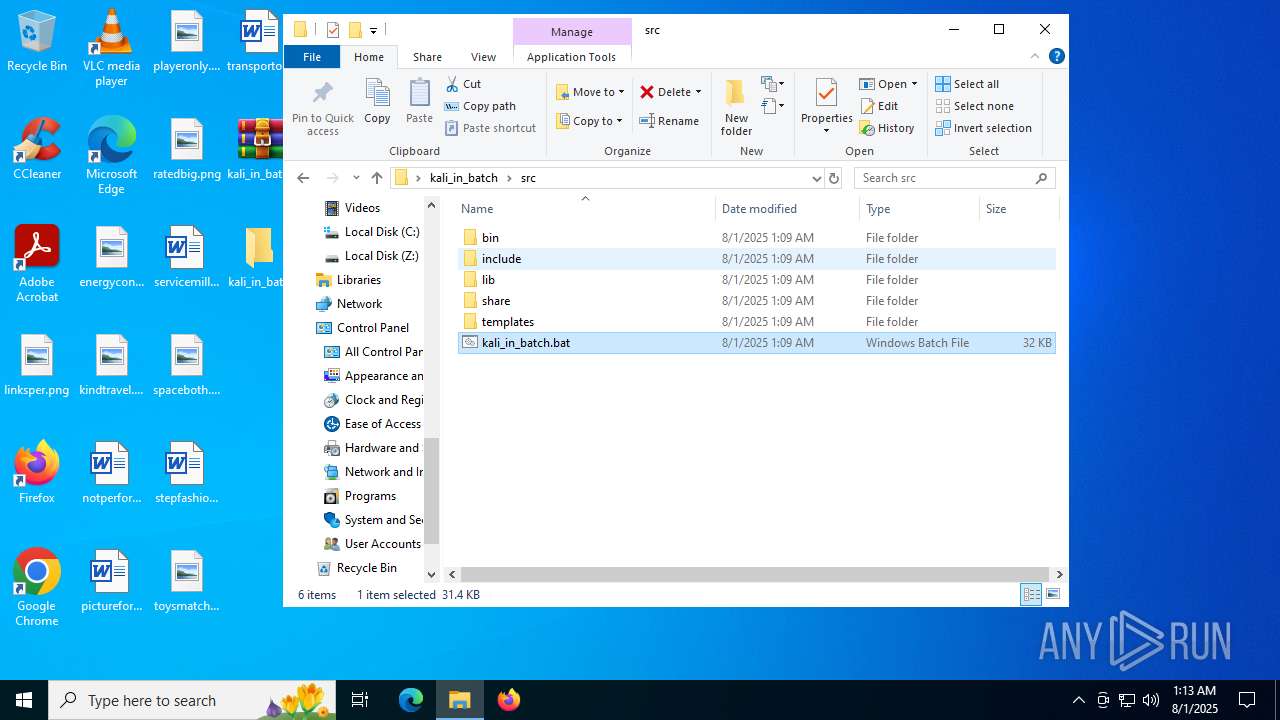
| download: | /Kali-in-Batch/kali-in-batch/releases/download/9.7.1/kali_in_batch.zip |
| Full analysis: | https://app.any.run/tasks/0517fdf0-13e2-40a5-9478-20e7010a2037 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 01:10:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
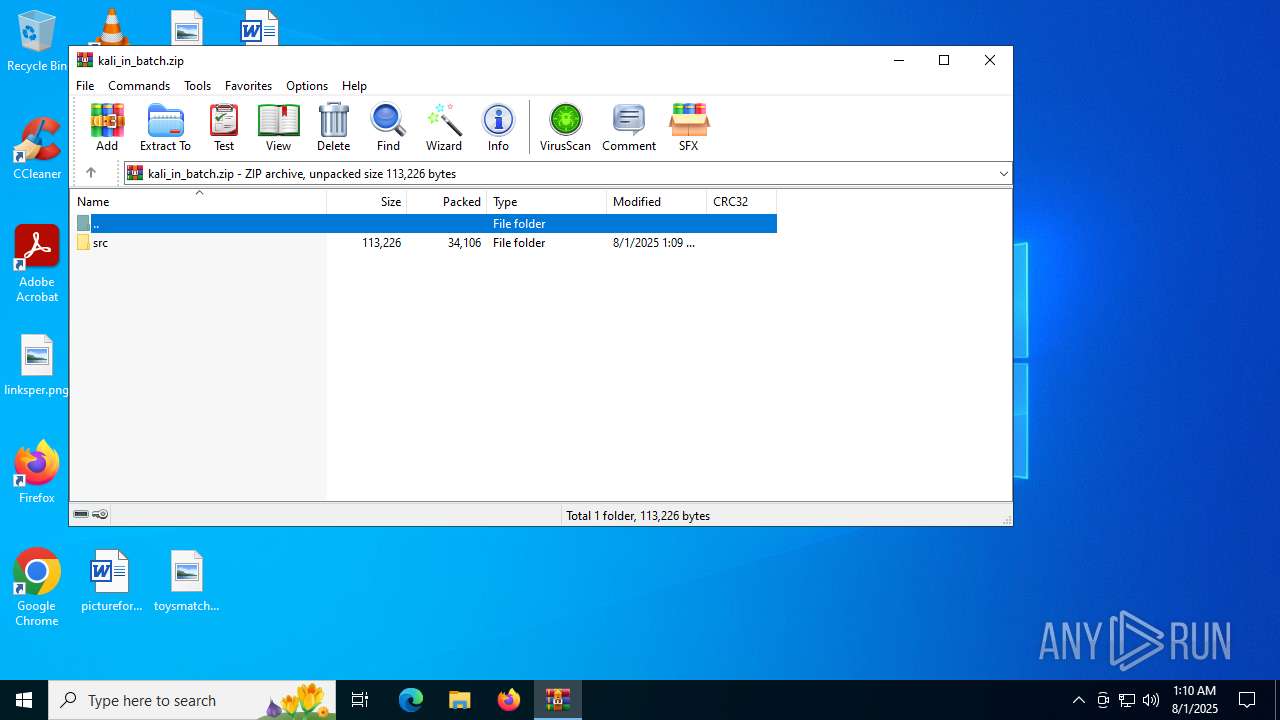
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 4E35E527809A04B8AF950FDE11DA1024 |
| SHA1: | 9E34E6E4083D0BD9F357771C2F11A695FED7AE6D |
| SHA256: | 6778FDD58B4C15D48E9AFF301BDFEB01F388E1BF4179403B5280A45D05C0E04A |
| SSDEEP: | 768:HS0MoUBLDXEIrGY2d+RSF5sOudOefmQ3EV+goCm1e3RV:fMfEIrGToRs51udOCmS16X |
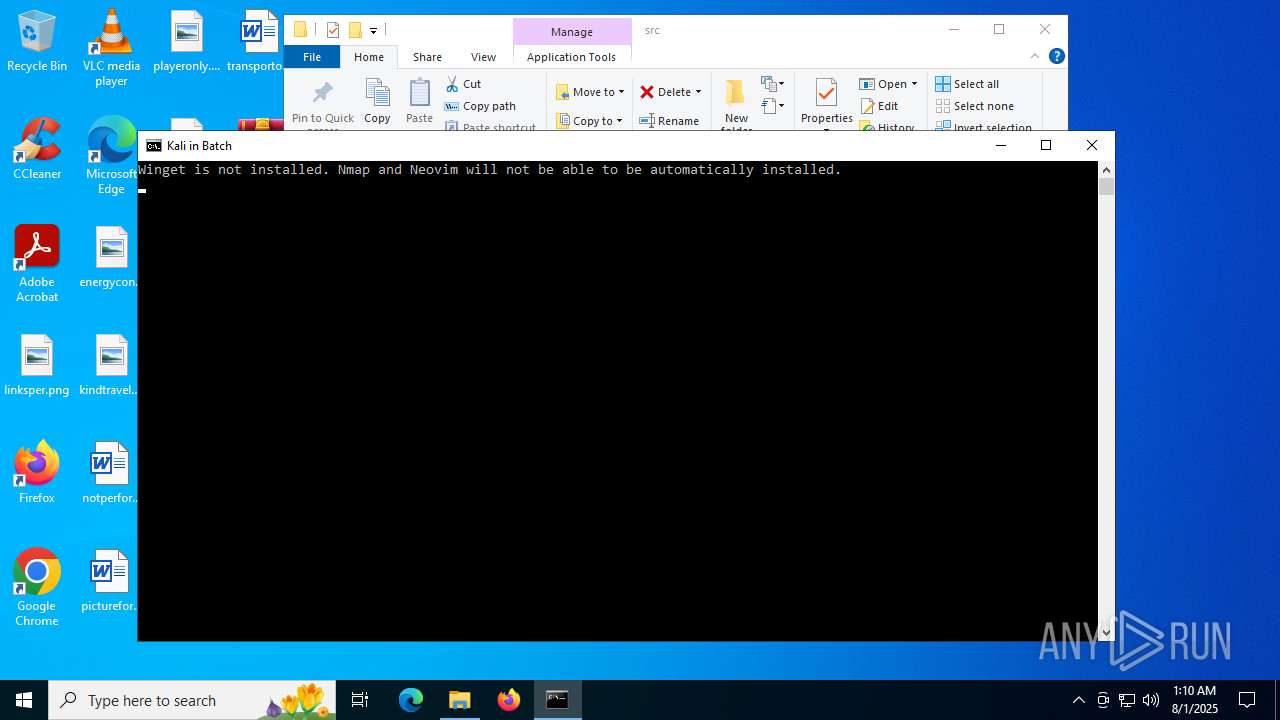
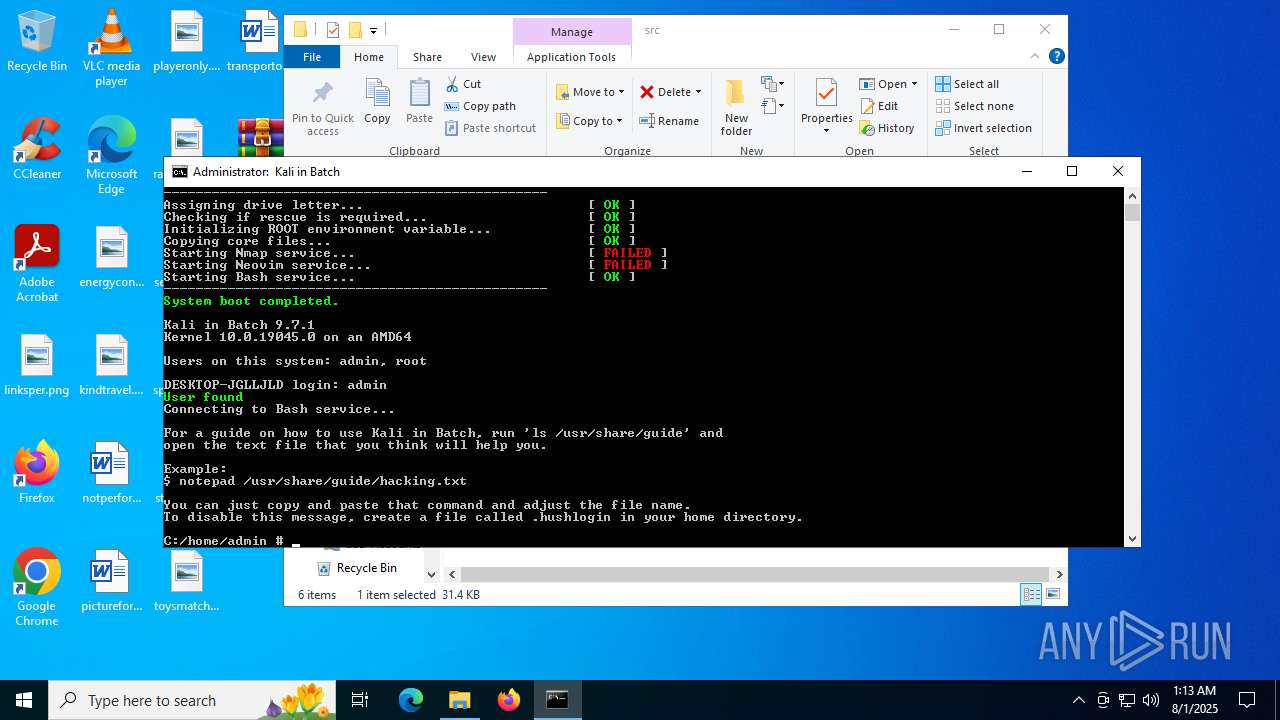
MALICIOUS
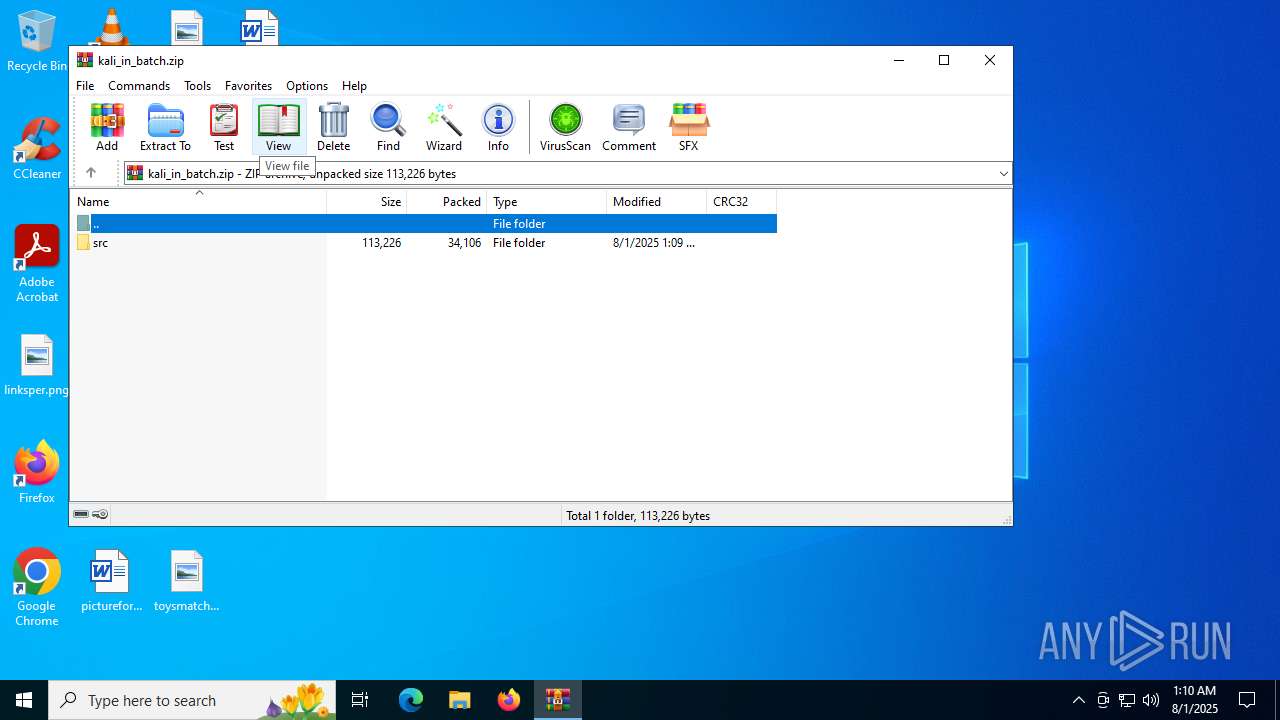
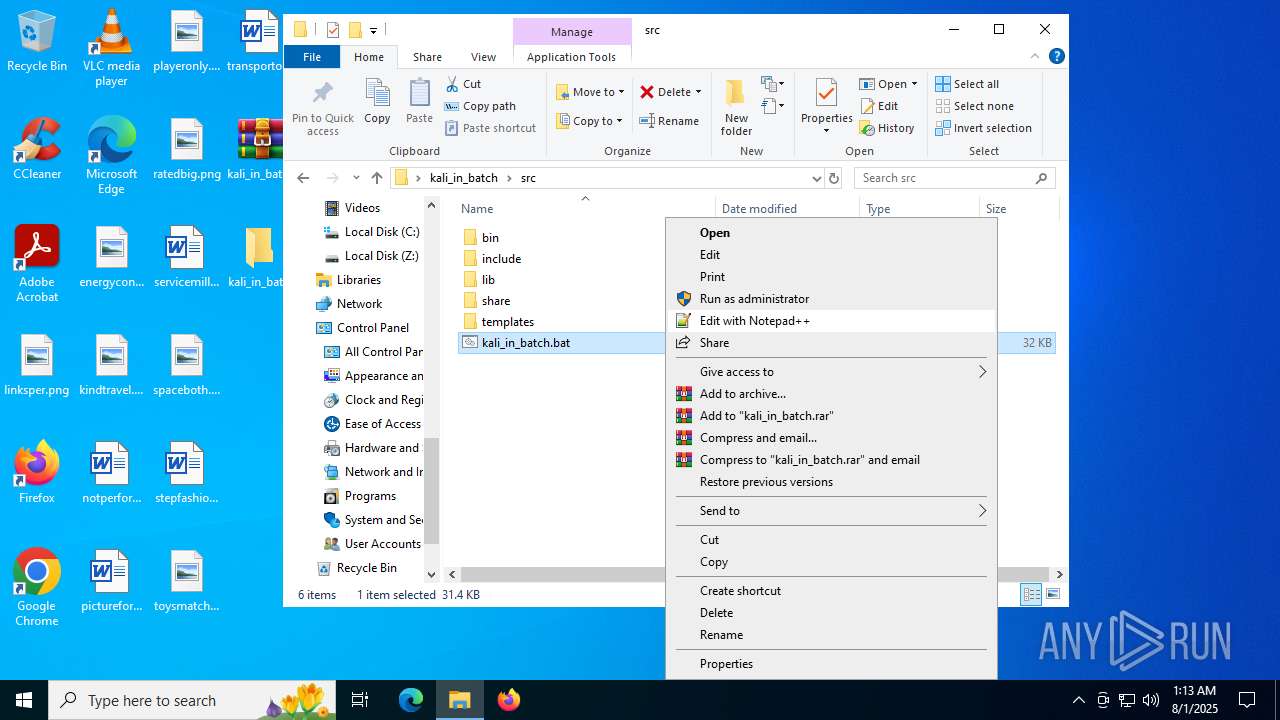
Generic archive extractor
- WinRAR.exe (PID: 304)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 3844)
- cmd.exe (PID: 516)
- cmd.exe (PID: 3968)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3844)
Application launched itself
- cmd.exe (PID: 516)
- cmd.exe (PID: 3968)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4760)
- cmd.exe (PID: 6980)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3968)
- cmd.exe (PID: 516)
Executable content was dropped or overwritten
- curl.exe (PID: 2704)
INFO
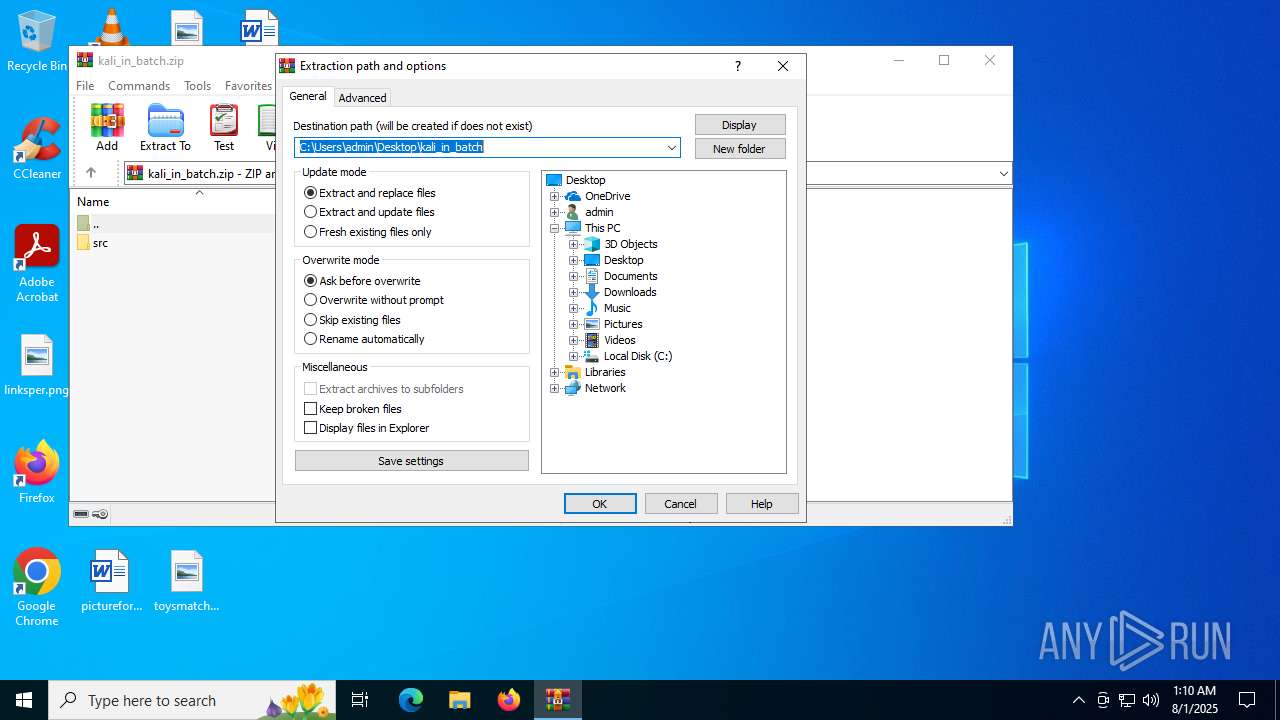
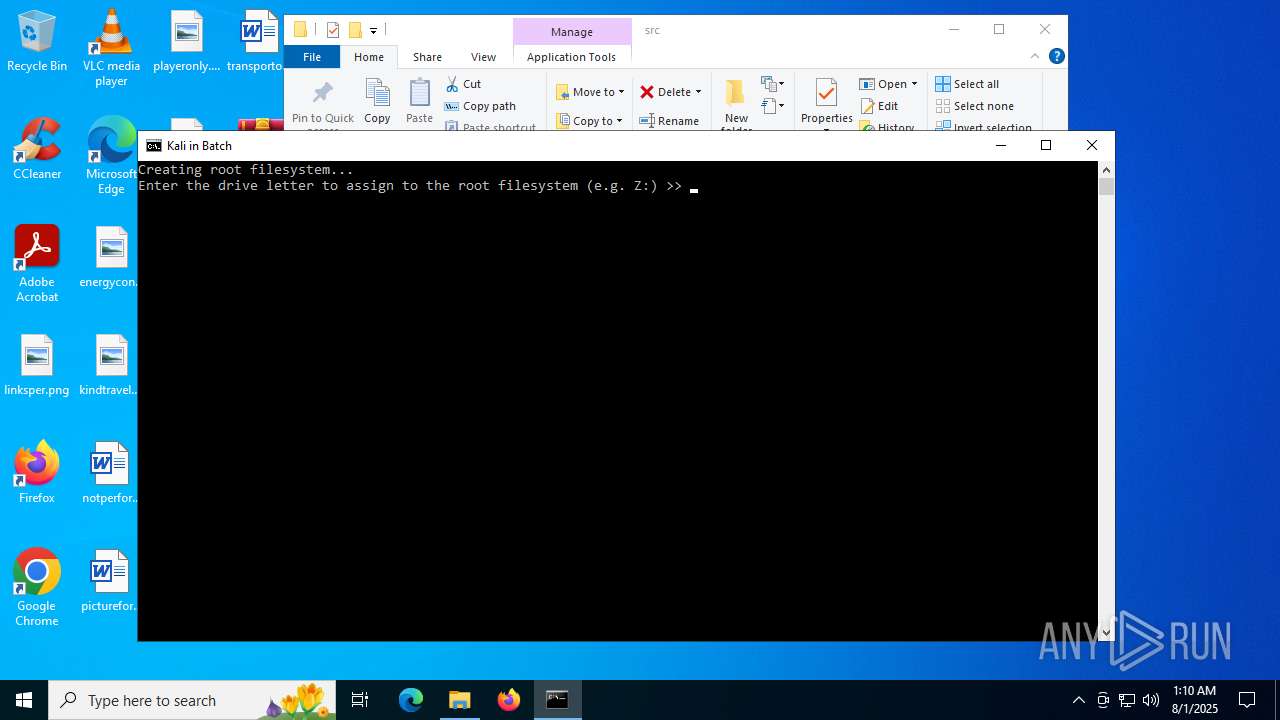
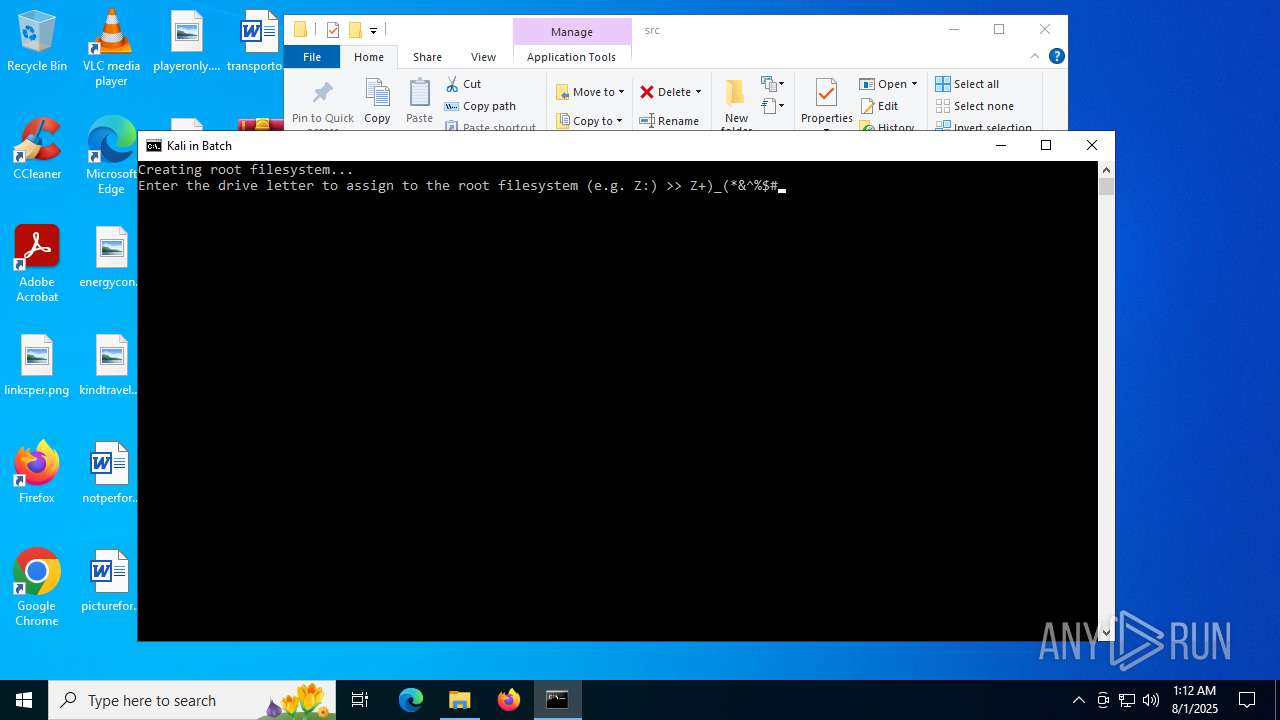
Manual execution by a user
- WinRAR.exe (PID: 892)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 516)
- cmd.exe (PID: 3968)
Checks supported languages
- chcp.com (PID: 1576)
- chcp.com (PID: 828)
- busybox.exe (PID: 4104)
- chcp.com (PID: 1324)
- curl.exe (PID: 2704)
Changes the display of characters in the console
- cmd.exe (PID: 3844)
- cmd.exe (PID: 516)
- cmd.exe (PID: 3968)
Reads the software policy settings
- slui.exe (PID: 984)
Checks proxy server information
- slui.exe (PID: 984)
Execution of CURL command
- cmd.exe (PID: 516)
Reads the computer name
- curl.exe (PID: 2704)
- busybox.exe (PID: 4104)
The sample compiled with english language support
- curl.exe (PID: 2704)
Reads the machine GUID from the registry
- busybox.exe (PID: 4104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:08:01 01:09:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
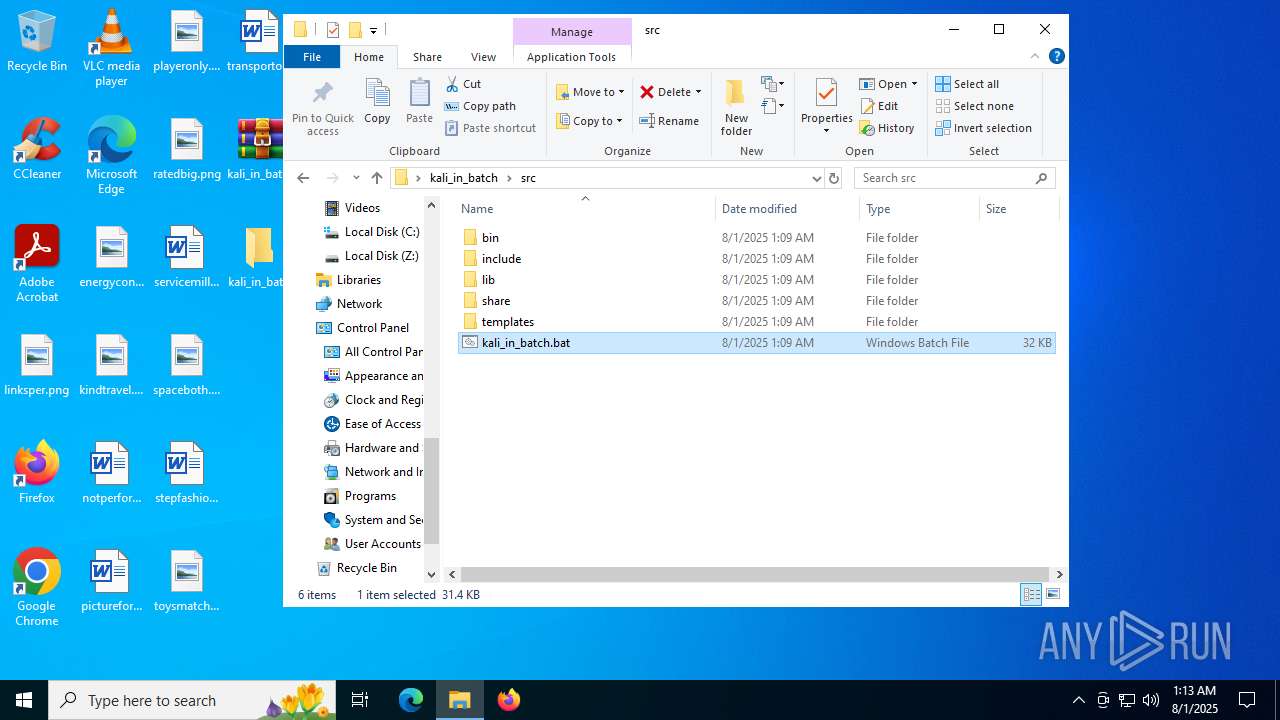
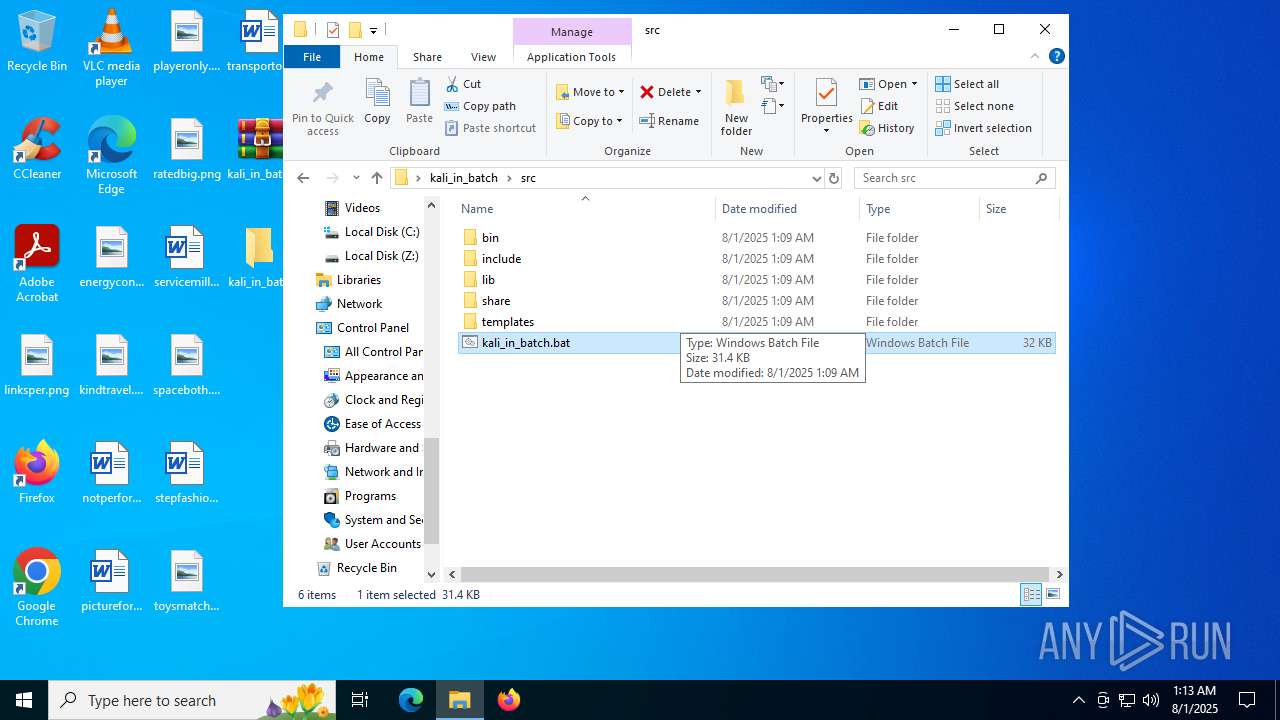
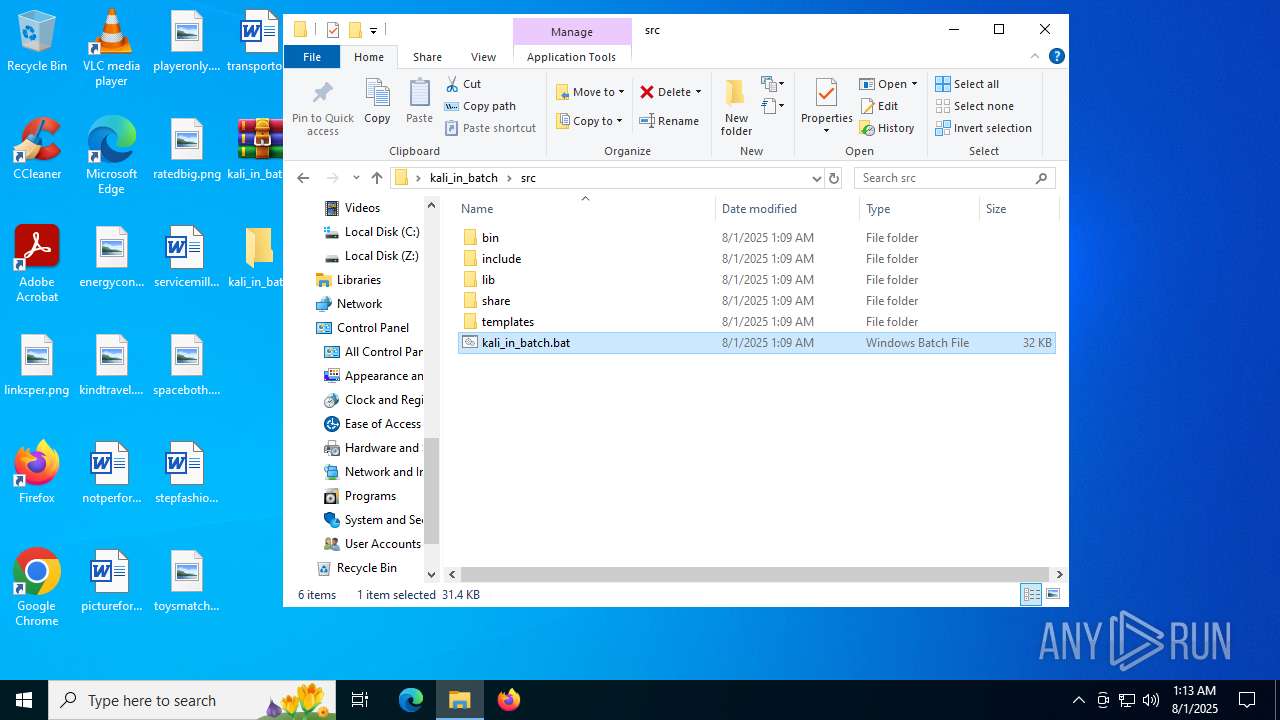
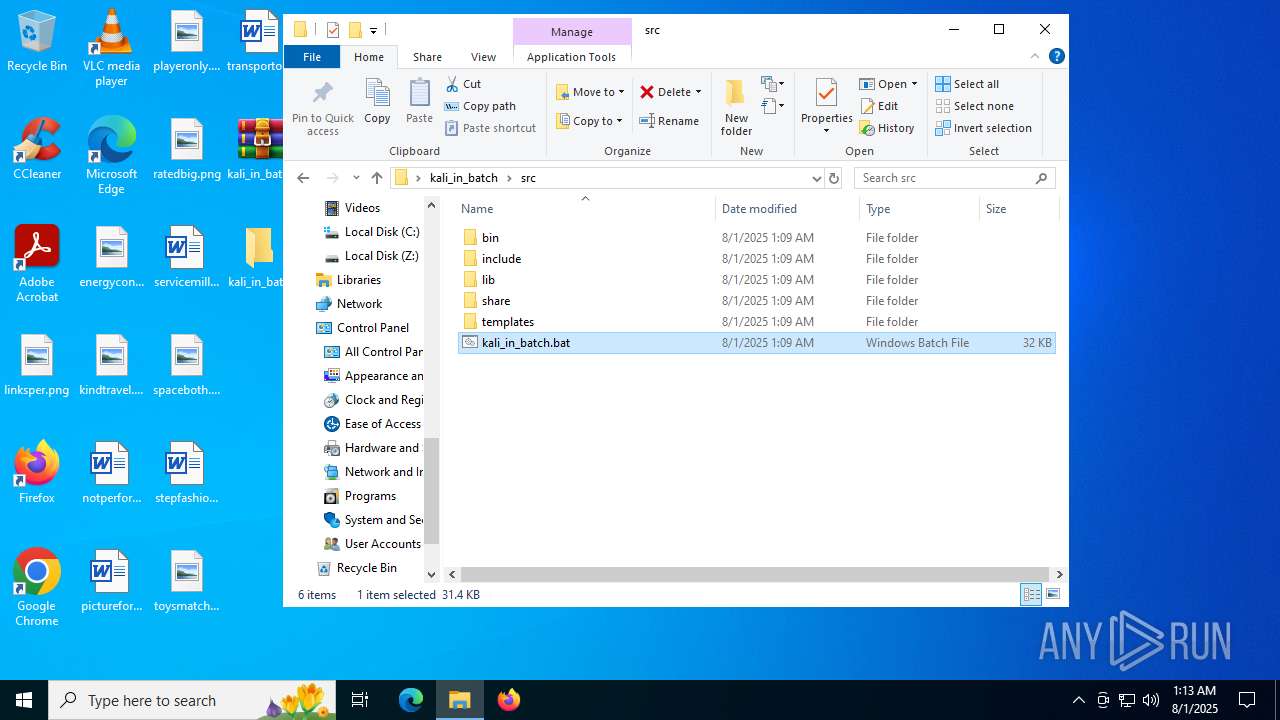
| ZipFileName: | src/ |
Total processes
181
Monitored processes
38
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | xcopy "C:\Users\admin\Desktop\kali_in_batch\src\lib\*" "\usr\lib\" /s /y | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
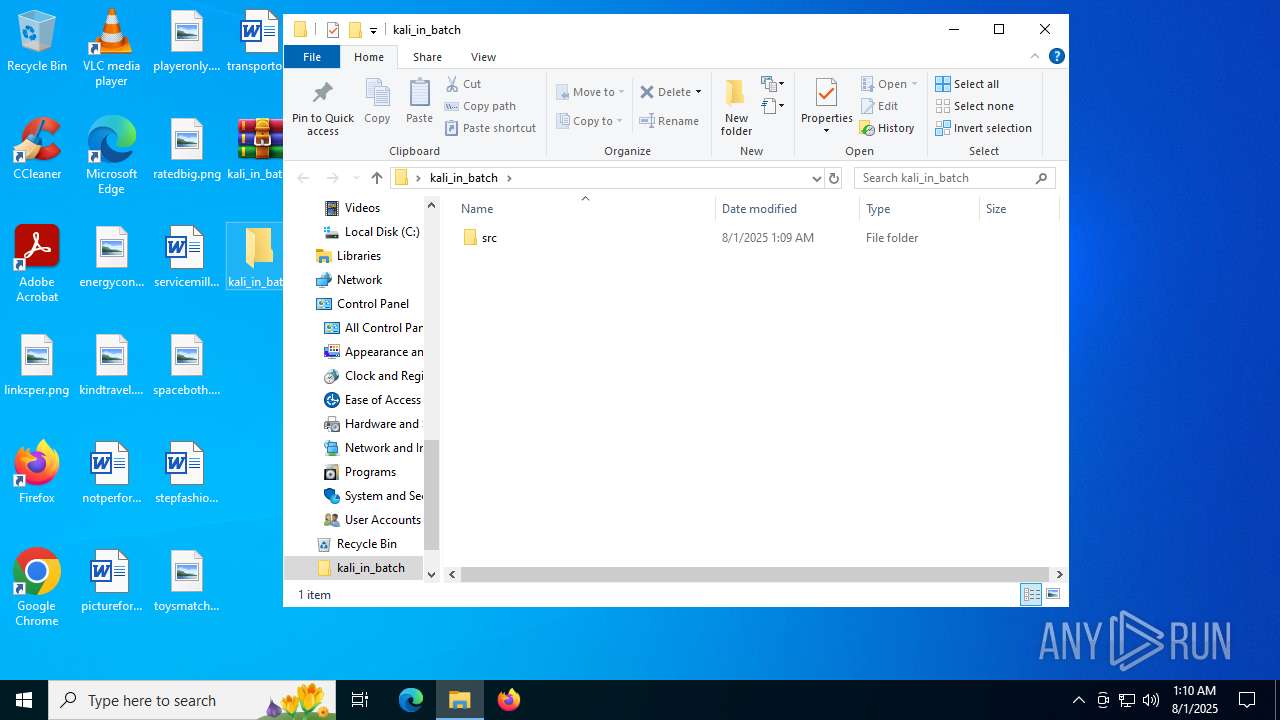
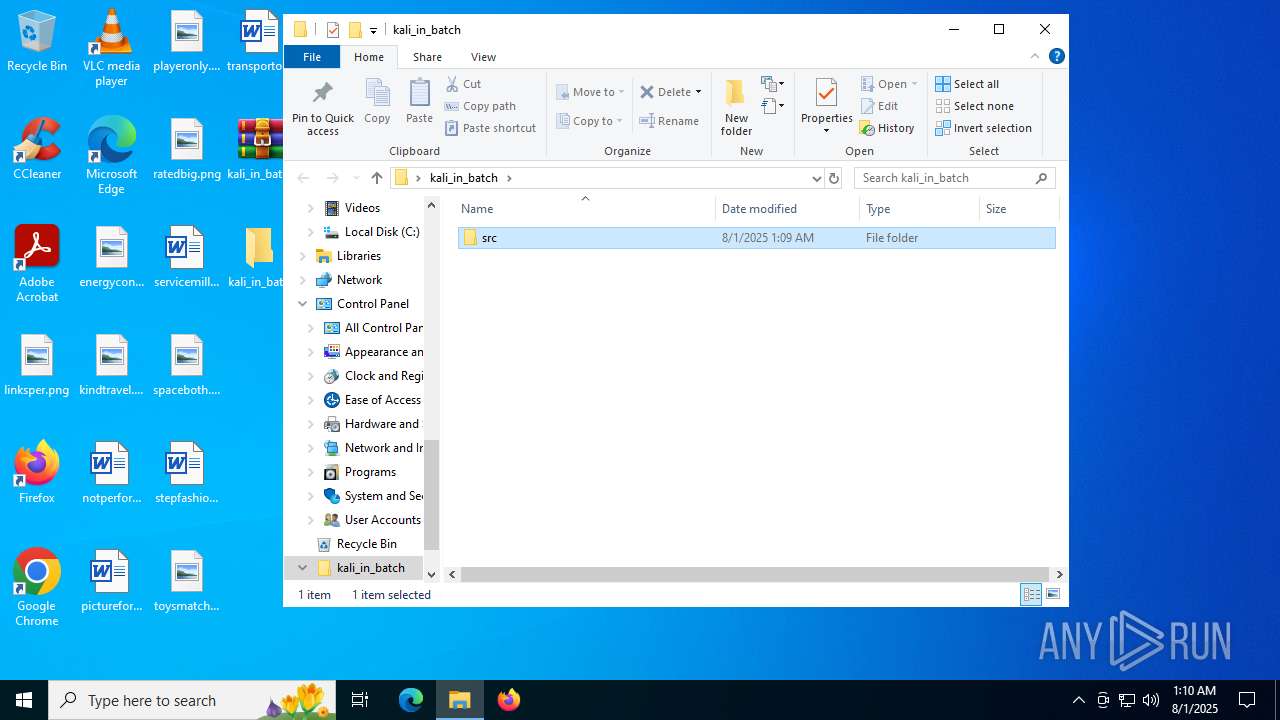
| 304 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\kali_in_batch.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 436 | powershell -command "[System.Environment]::OSVersion.Version.ToString()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
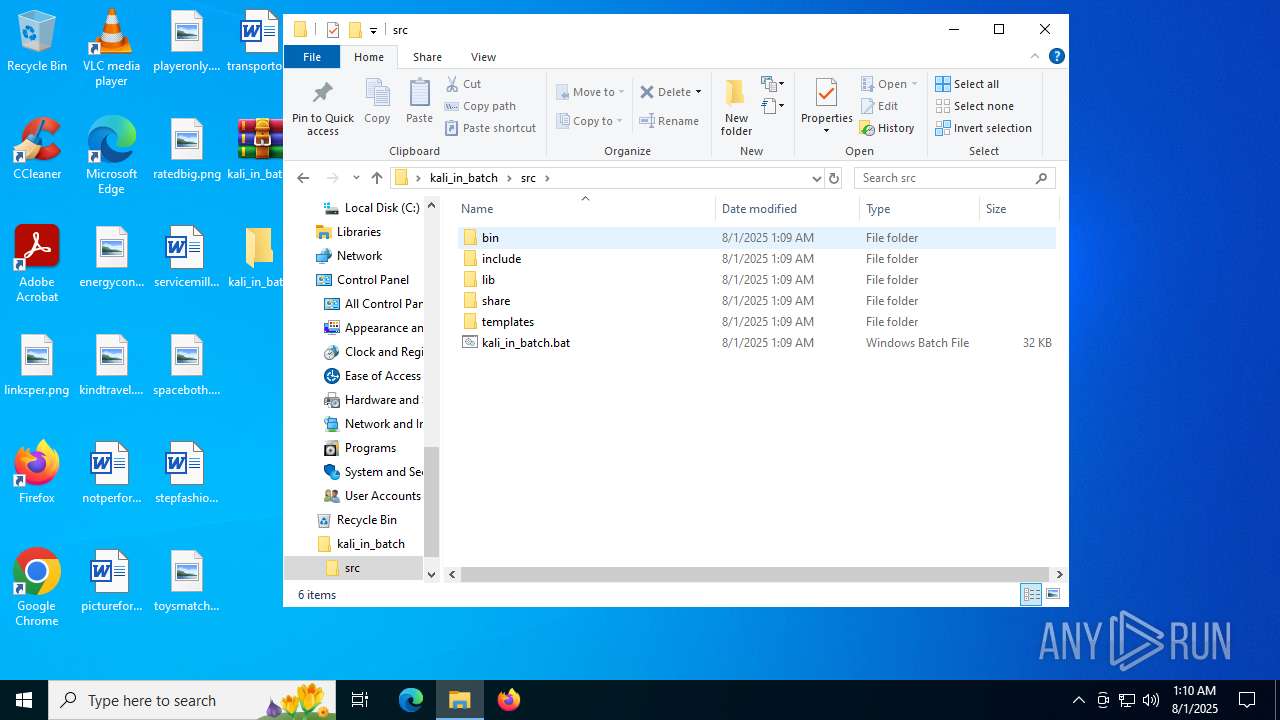
| 516 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\kali_in_batch\src\kali_in_batch.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | powershell -command "[System.Environment]::OSVersion.Version.ToString()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\kali_in_batch.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 984 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | where winget | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | where curl | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Where - Lists location of files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 319
Read events
14 268
Write events
38
Delete events
13
Modification events
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\kali_in_batch.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
1
Text files
58
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\lib\posix\execl.bat | text | |
MD5:2689FE82CB0697F6247EE8878B0CA36C | SHA256:C23B2152A37C93D1897F370AD05A09B86271A004CEB149501454D1099712848A | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\lib\posix\rmdir.bat | text | |
MD5:8034AF01C457D5F41B40ECB326E7873F | SHA256:F6496CEAEEED34462017720EE968D0CCA3FDBB91E92C6D594385D5D33BD6C264 | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\lib\posix\getcwd.bat | text | |
MD5:C494AA45E17AB26904658BA01557E9C8 | SHA256:D9517CCE294682B1EE269F2FDCD7AFA169C11A525099BF0747C6D5F61214AC8C | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\lib\posix\mkdir.bat | text | |
MD5:328EF7B218E8DC695285CAA974CB762F | SHA256:B90D4397F7E905F34DCA883747BDBD9F2AEB7C0B24EB43DBE929F6561CFB2174 | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\include\unistd.h | text | |
MD5:7CB5F504030A0A1FAC832D326A22AE66 | SHA256:49C5A10521786154DBFFE4819FFB0F76EF53090B27C657CB879720DE09ED9C7F | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\bin\uname.bat | text | |
MD5:5AB0E43BA2E24969CAB43974B4F79CF2 | SHA256:084AED3312BABCCCE5A4873FADEBC31B2812E199053C1BF54704AC9795812513 | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\lib\posix\README.md | text | |
MD5:ED8F05D78673A2159B2909D67798ABD0 | SHA256:C7B887A52DA8871CA297CBBDB1842CC3326CD134BADC3A87E36DD15820B5A2D6 | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\bin\pkg.bat | text | |
MD5:587B011C34CC668A835157930D5B1DC6 | SHA256:A0DE1620C82FEC66C385EC59129A54C43951CC3EEA7A63F3E2FCB5AAA904A6AD | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\bin\which.bat | text | |
MD5:55D810DA287F0A503E85E735E9BFEB3F | SHA256:E8910220553C1BE34F6C98CA743C96E52F89CE2FBA1CDE7FCCFE308D3EB66E58 | |||
| 892 | WinRAR.exe | C:\Users\admin\Desktop\kali_in_batch\src\share\guide\usingkiboutsidekib.txt | text | |
MD5:6E3296CBB07964DED1A254DF8799CD50 | SHA256:CB8E0FF30C817D81FCDC06AE2B52B315D9DF451E73B768B101280A1916300A8A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2368 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
3888 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
3888 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2620 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | DE | binary | 471 b | whitelisted |
764 | lsass.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | binary | 2.01 Kb | whitelisted |
764 | lsass.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | binary | 1.98 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1964 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2368 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2368 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |