| File name: | onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin |
| Full analysis: | https://app.any.run/tasks/f4f5e1c7-f8d8-40ad-9f83-1347bb36cd98 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2026, 19:24:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 5DA5E53C9B251E6F5DC9A2F54D70CFF5 |
| SHA1: | 4BD20EC09DFBBD88B163D1712DFB221B1E2D8622 |
| SHA256: | 6774073E950476DE88902AB098E299D47E4C2E0113730C70B05D30240862BAF9 |
| SSDEEP: | 12288:xhXV1rOck4LbsroP4BMdIVIitfMQeB5z4RYa5sxL:xhl1rHkUbsEO+MIitfLeB58H5iL |
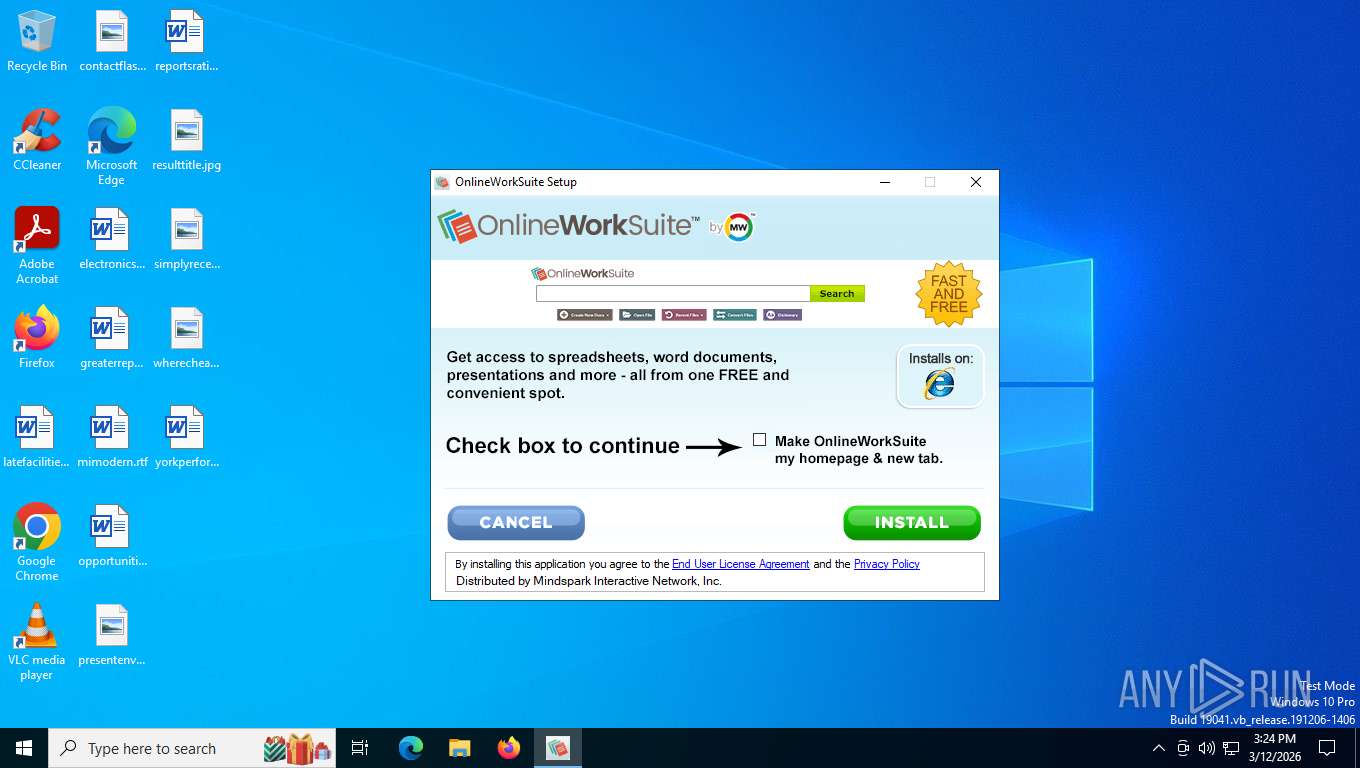
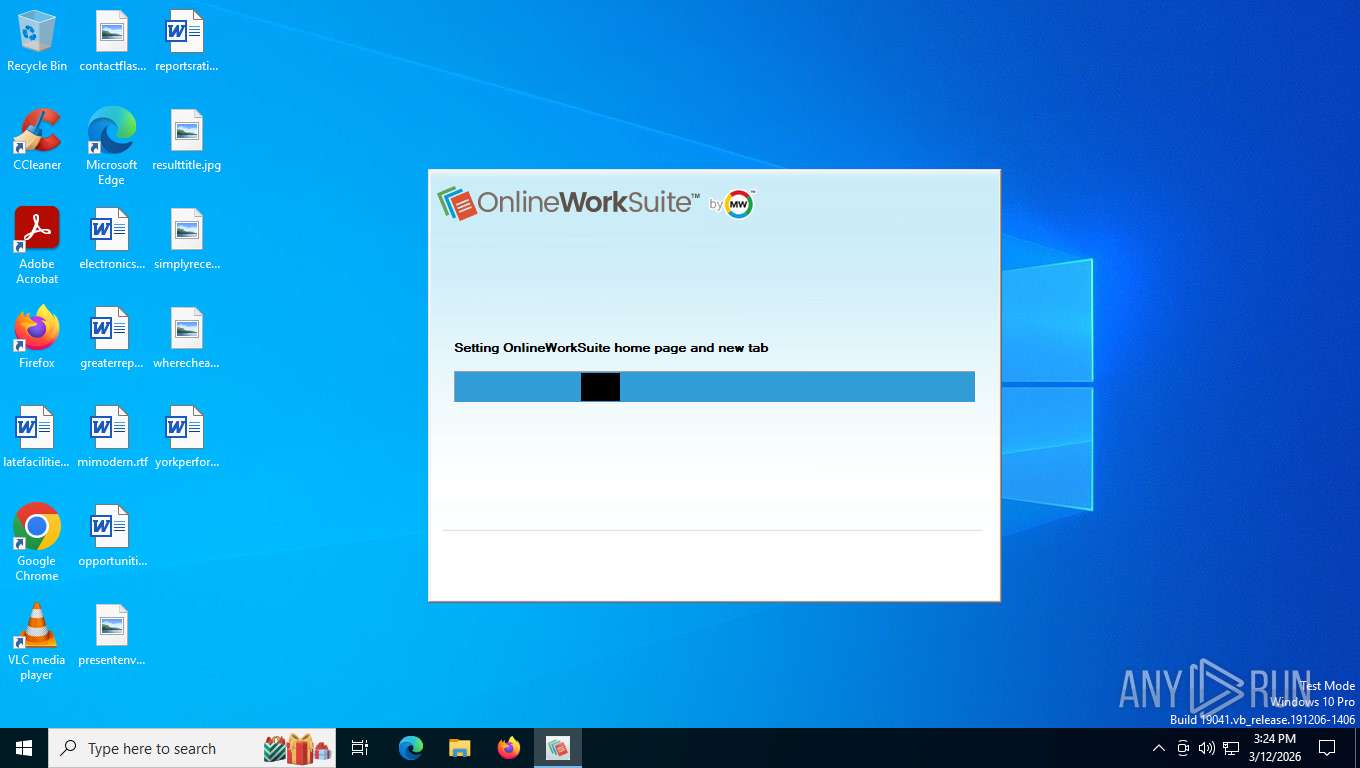
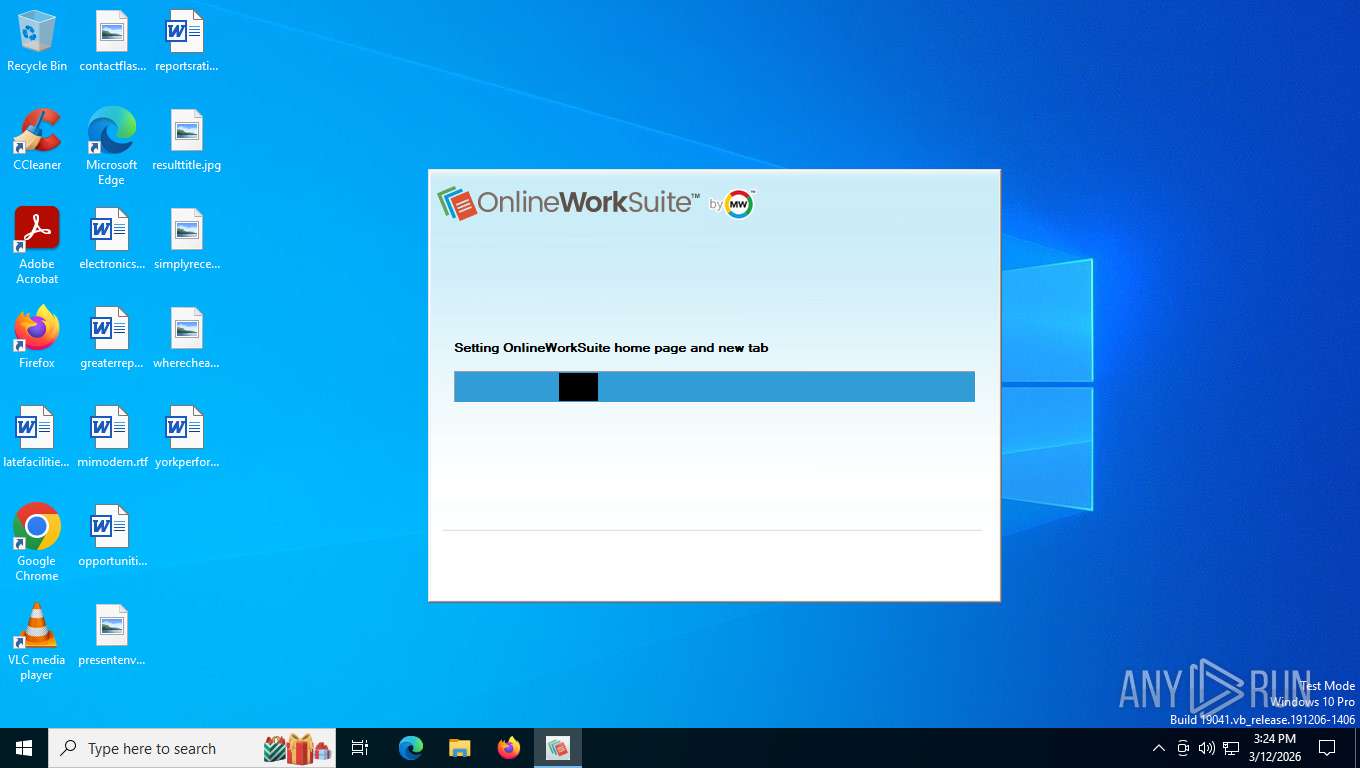
MALICIOUS
Executing a file with an untrusted certificate
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
SUSPICIOUS
The process creates files with name similar to system file names
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Malware-specific behavior (creating "System.dll" in Temp)
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Executable content was dropped or overwritten
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
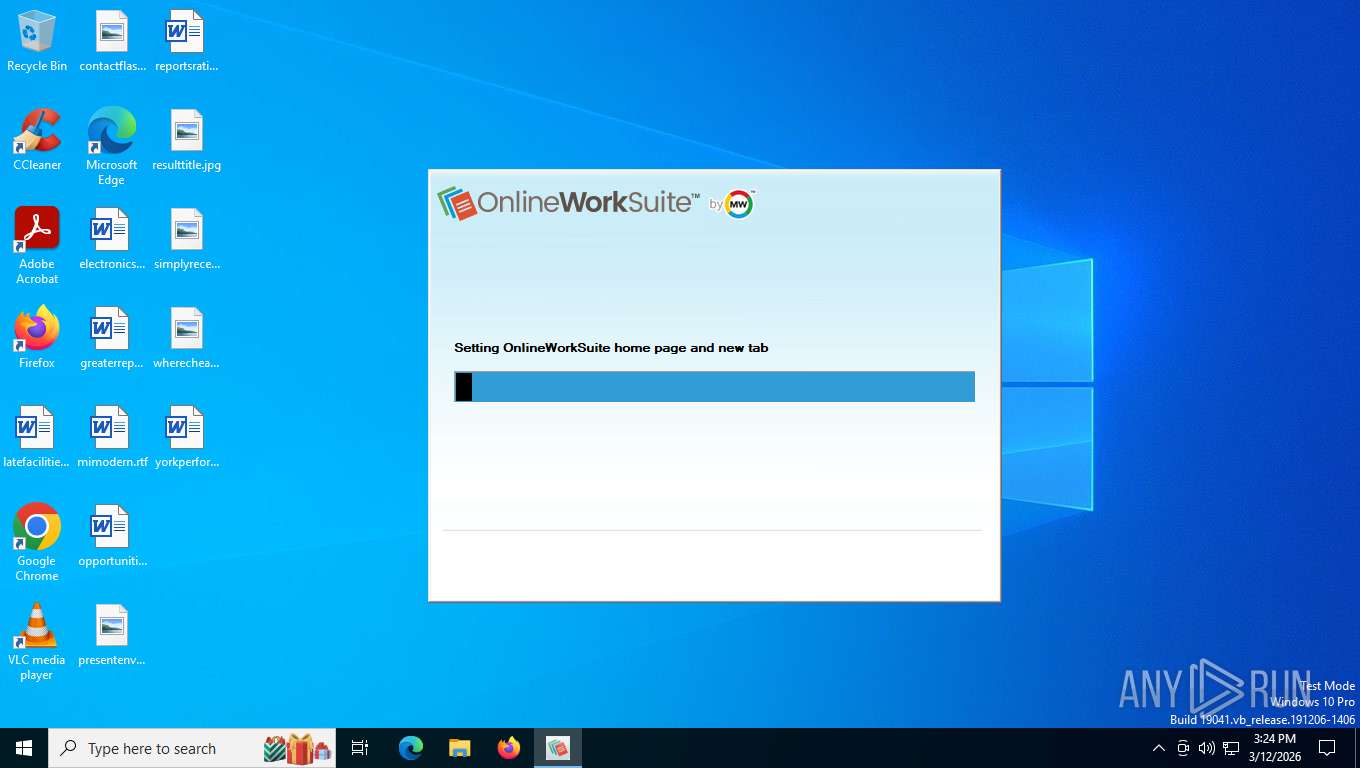
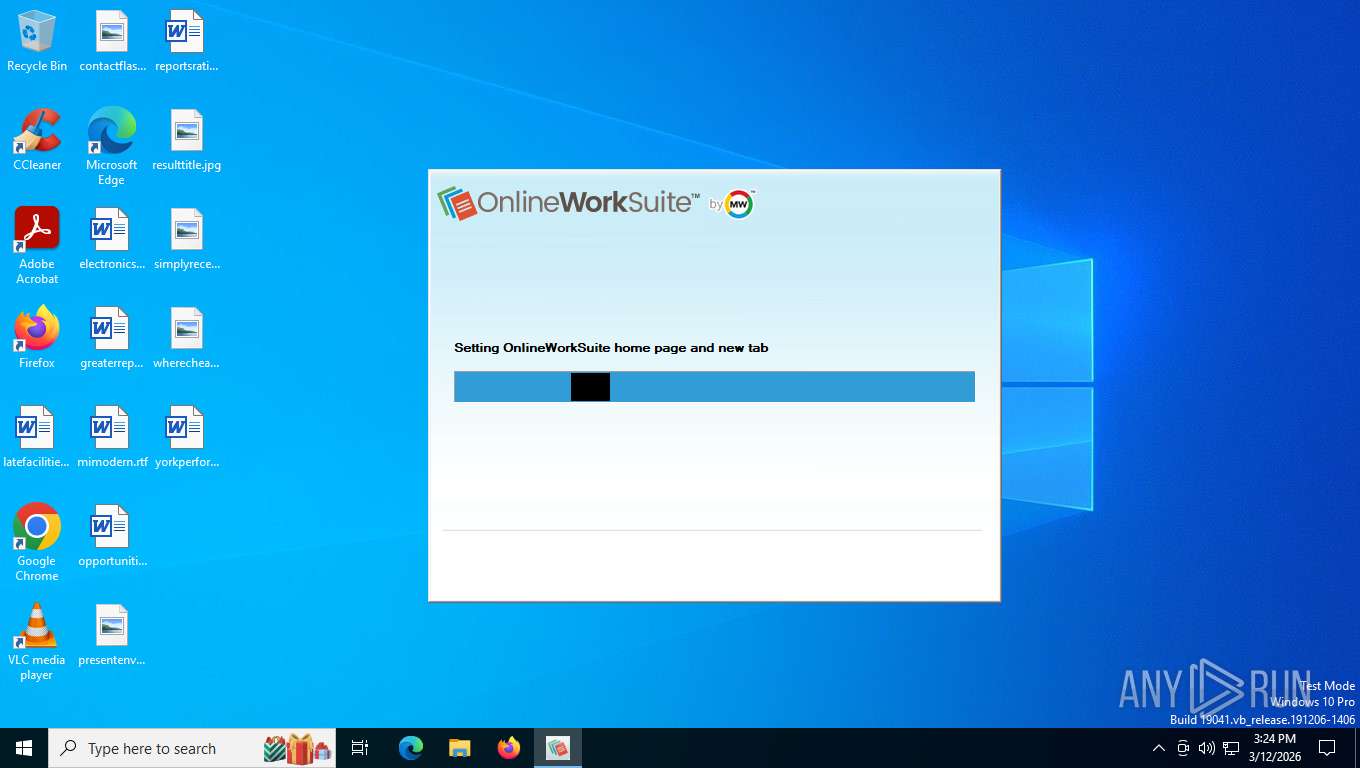
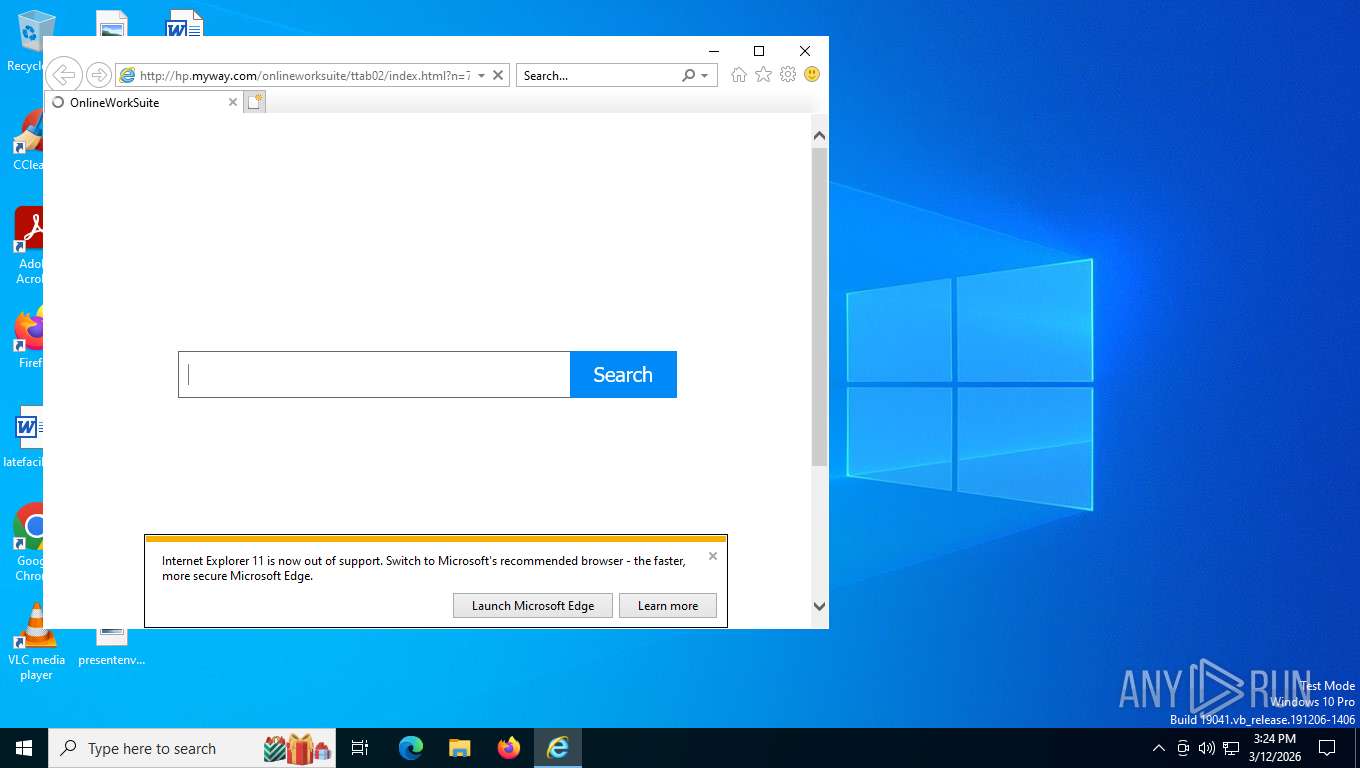
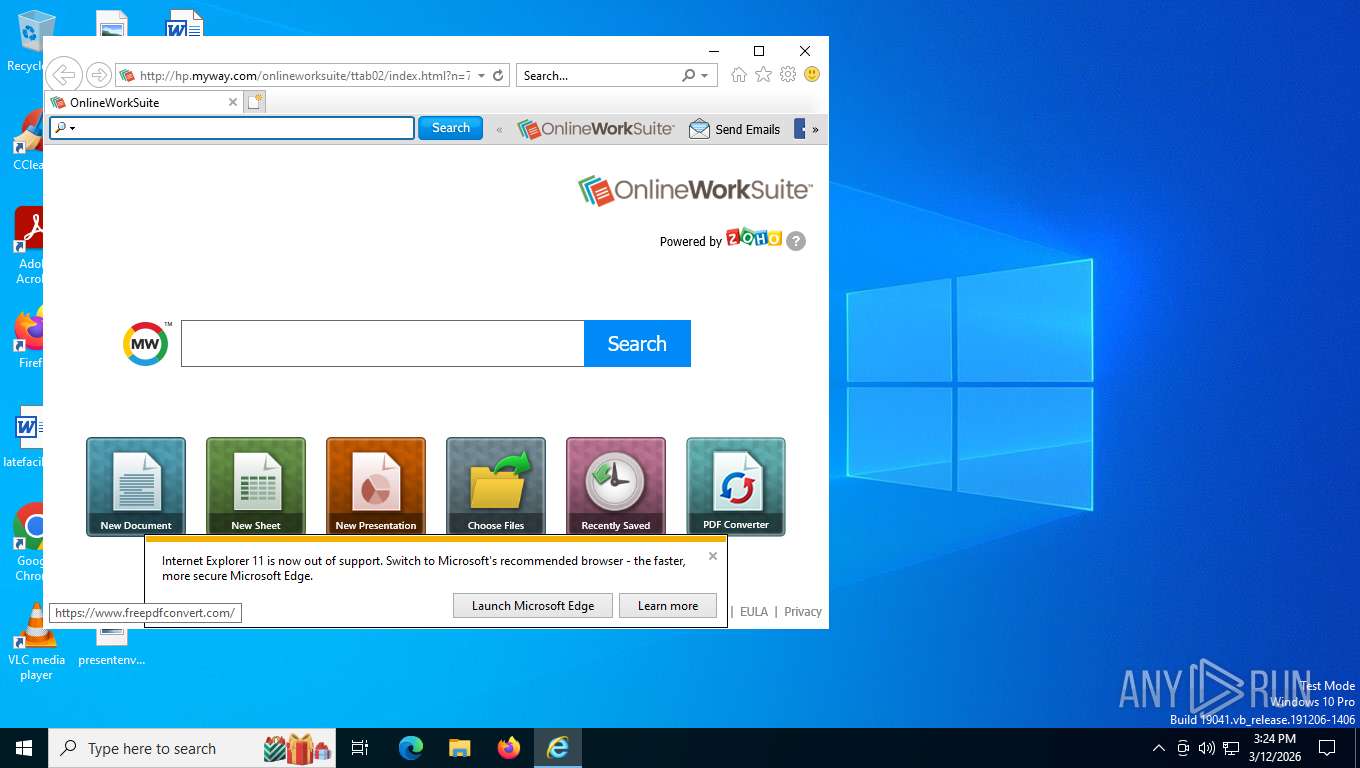
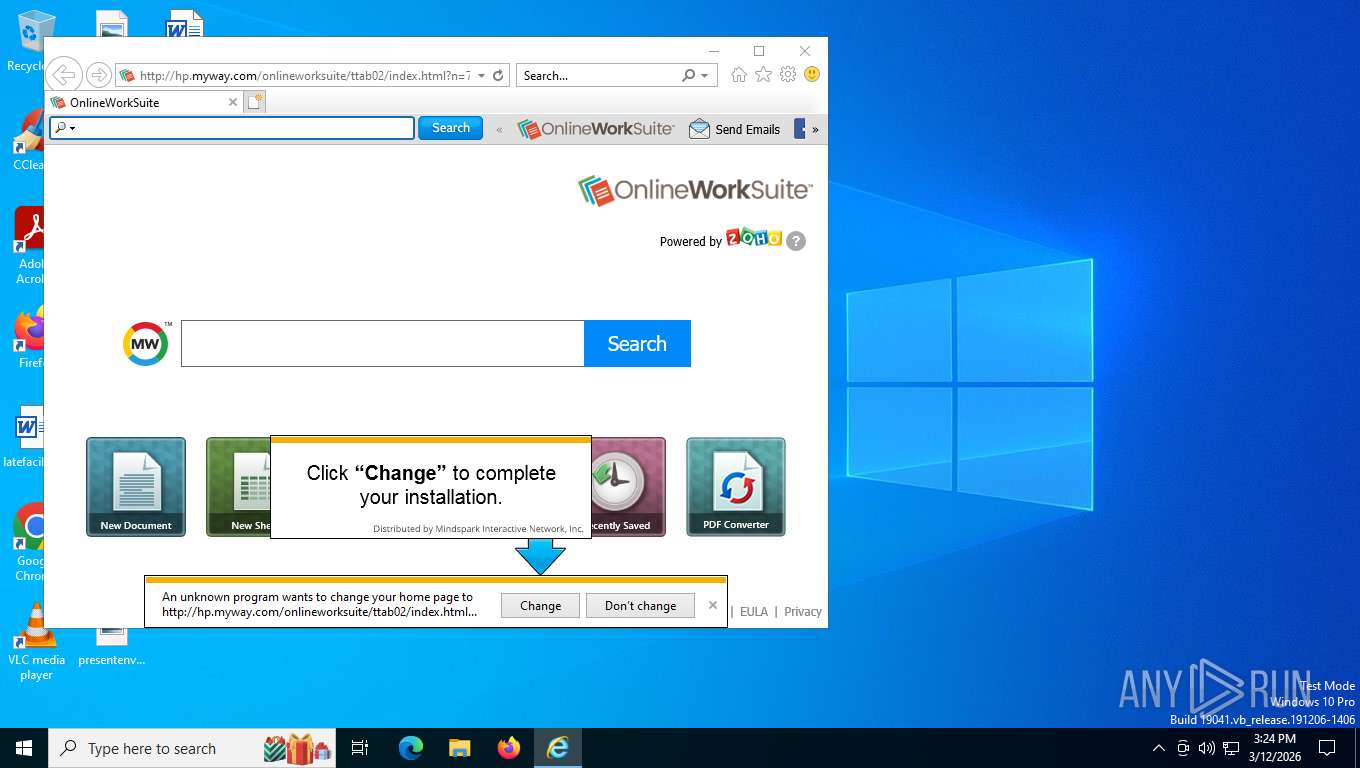
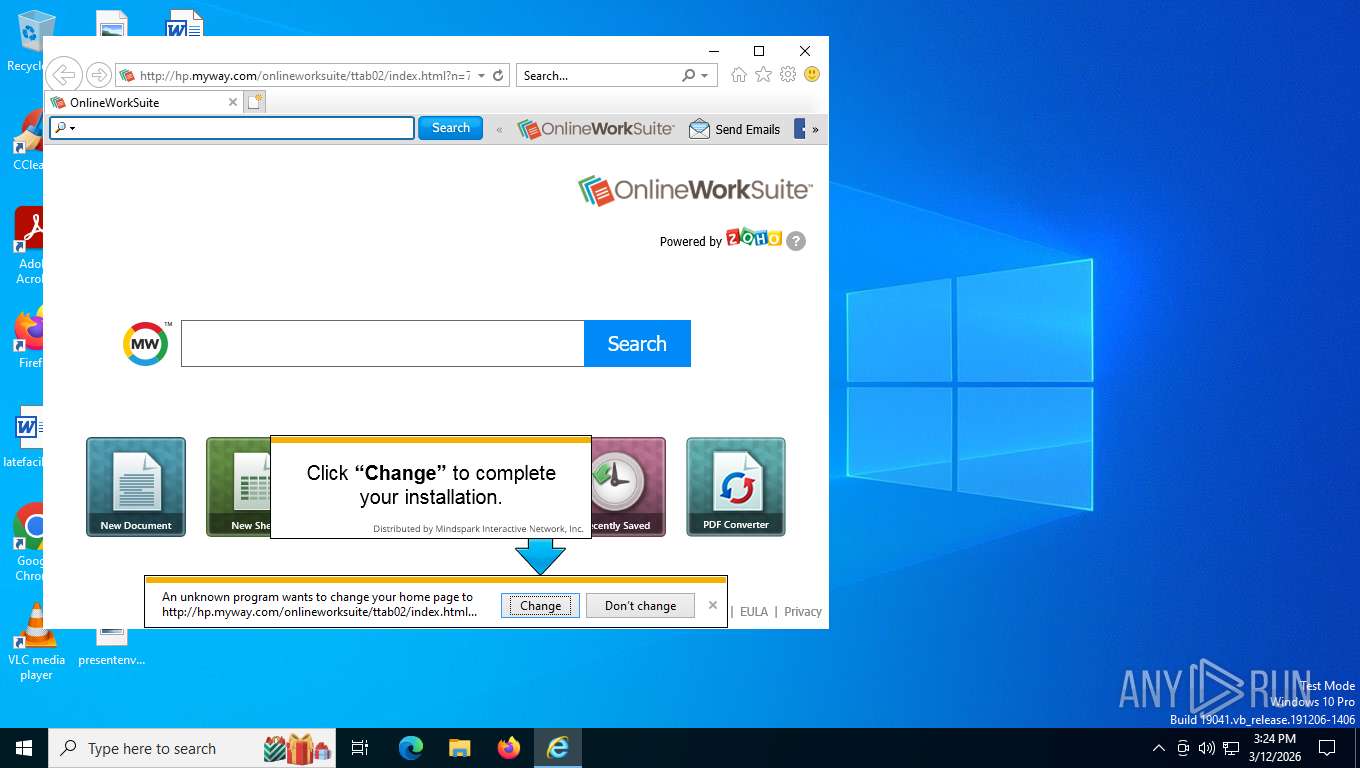
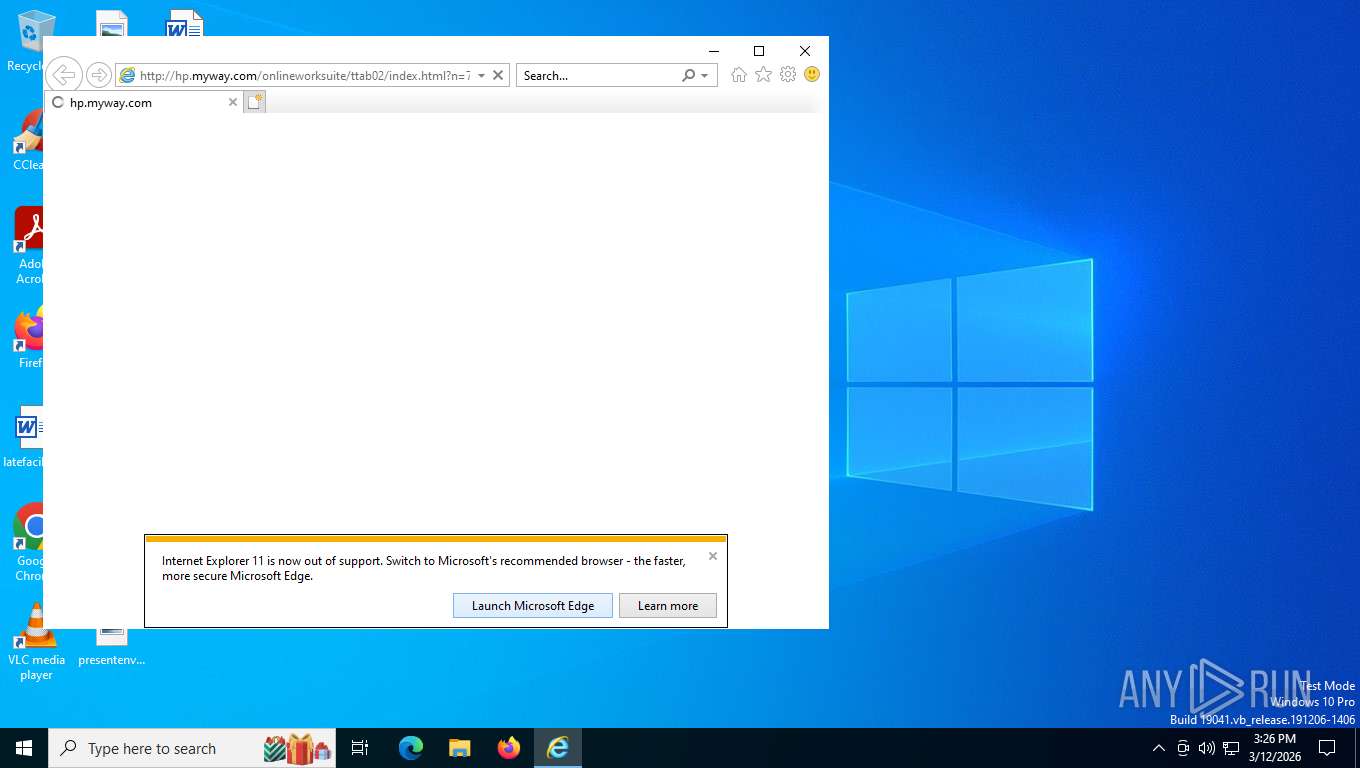
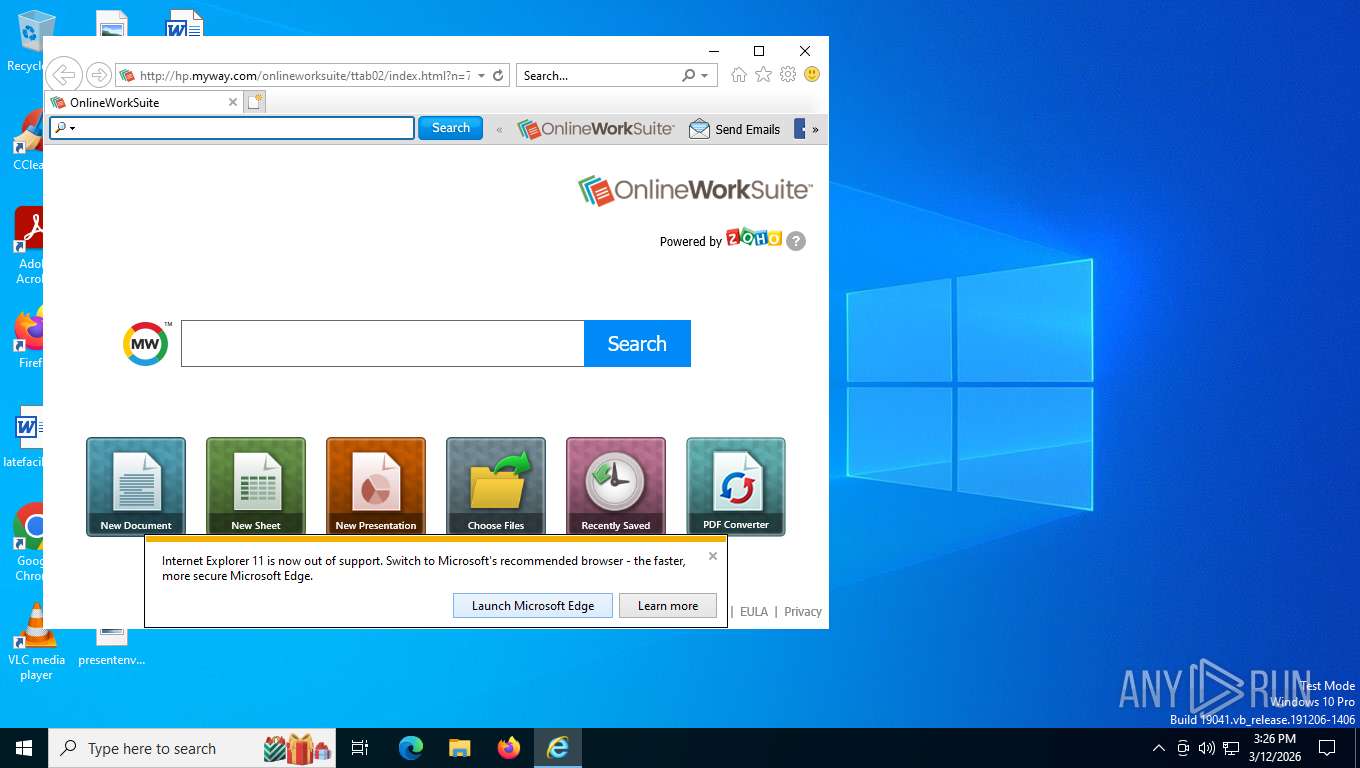
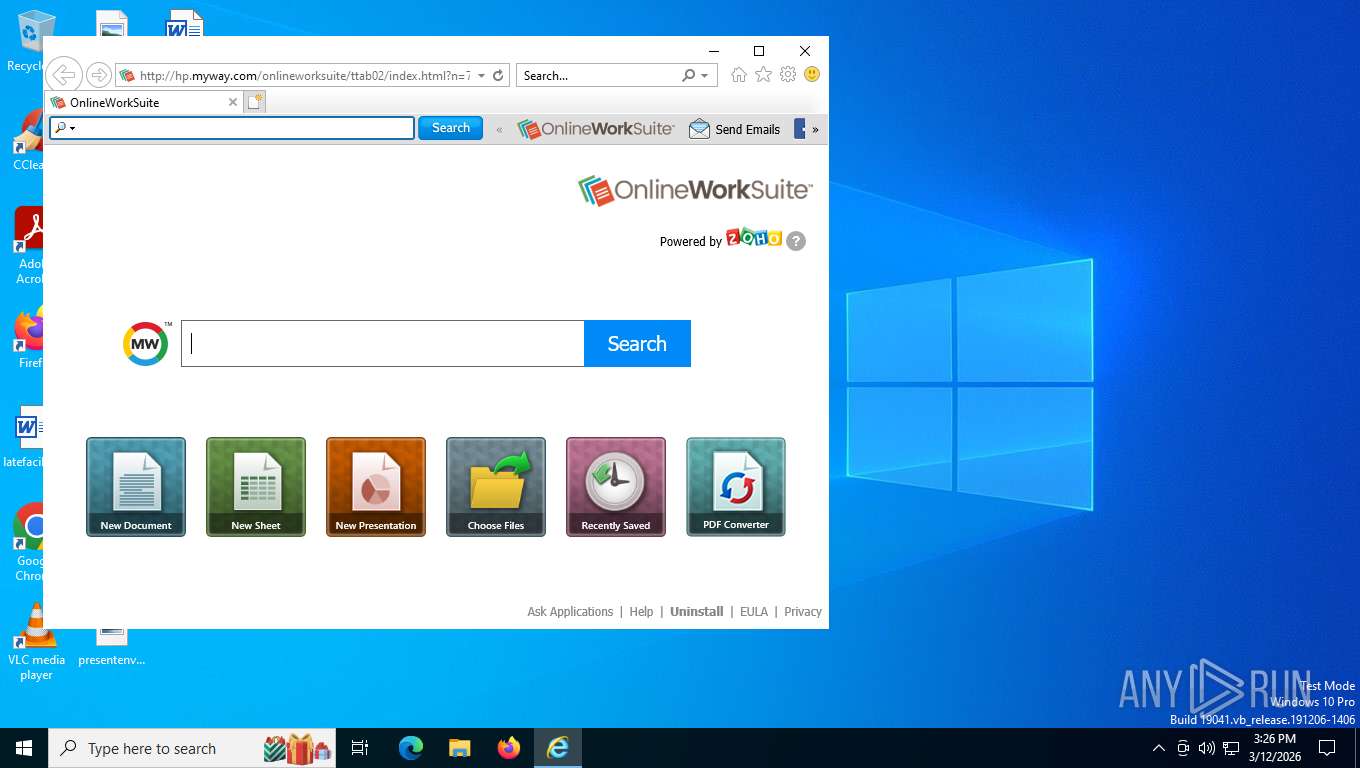
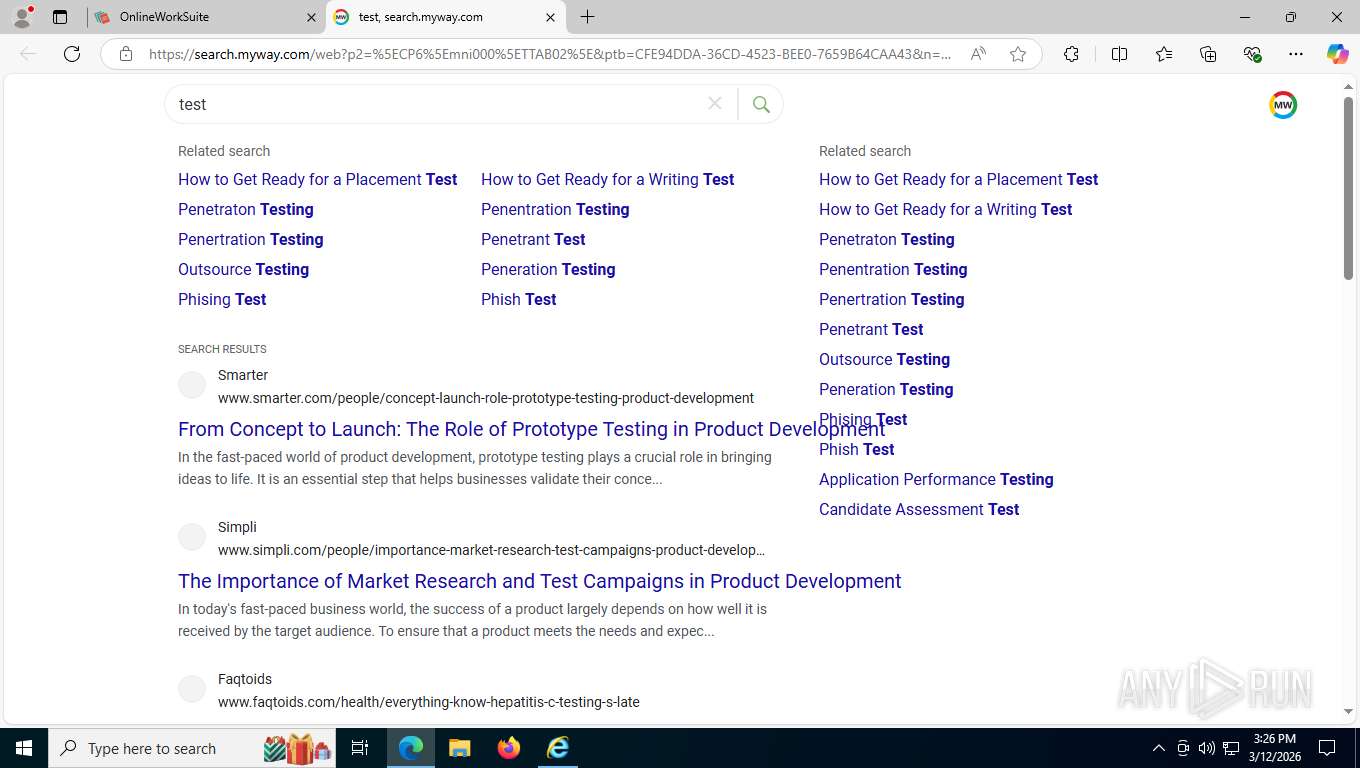
Changes the Home page of Internet Explorer
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Changes the title of the Internet Explorer window
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
INFO
The sample compiled with english language support
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Checks supported languages
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
- ielowutil.exe (PID: 7968)
- identity_helper.exe (PID: 8156)
Creates a software uninstall entry
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Reads the computer name
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
- identity_helper.exe (PID: 8156)
- ielowutil.exe (PID: 7968)
Reads security settings of Internet Explorer
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
- rundll32.exe (PID: 7020)
There is functionality for taking screenshot (YARA)
- rundll32.exe (PID: 7020)
Create files in a temporary directory
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Application launched itself
- msedge.exe (PID: 4364)
- msedge.exe (PID: 6360)
Reads Environment values
- identity_helper.exe (PID: 8156)
Creates files or folders in the user directory
- onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe (PID: 8300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 05:01:44+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.1.3000 |
| ProductVersionNumber: | 2.7.1.3000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | OnlineWorkSuite Setup |
| FileVersion: | 2.7.1.3000 |
| InternalName: | OnlineWorkSuite |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | OnlineWorkSuite |
| ProductVersion: | 2.7.1.3000 |
Total processes
183
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6036,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=6100 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1956 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7152,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=6820 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4256,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=4280 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2620 | C:\WINDOWS\system32\DllHost.exe /Processid:{49F171DD-B51A-40D3-9A6C-52D674CC729D} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=15 --always-read-main-dll --field-trial-handle=6192,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=6836 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6852,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=5244 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4364 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 --edge-skip-compat-layer-relaunch -- http://hp.myway.com/onlineworksuite/ttab02/index.html?n=78C2C86F&p2=%5ECP6%5Emni000%5ETTAB02&ptb=CFE94DDA-36CD-4523-BEE0-7659B64CAA43&coid=5eb9d836784b44c8a10744c5df6e335d | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2256,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=2196 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5528,i,10126025640807071170,8311167339846218442,262144 --variations-seed-version --mojo-platform-channel-handle=5064 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5676 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 524
Read events
5 513
Write events
11
Delete events
0
Modification events
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OnlineWorkSuite |
| Operation: | write | Name: | UnInstallSurveyUrl |
Value: http://@{downloadDomain}.dl.myway.com/uninstall.jhtml?surveyUrl=http%3A%2F%2Fwww.research.net%2Fr%2FHYSCVNM%3Fc%3DCFE94DDA-36CD-4523-BEE0-7659B64CAA43%26ptb%3D^CP6^mni000^TTAB02 | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: http://hp.myway.com/onlineworksuite/ttab02/index.html?n=78C2C86F&p2=^CP6^mni000^TTAB02&ptb=CFE94DDA-36CD-4523-BEE0-7659B64CAA43&coid=5eb9d836784b44c8a10744c5df6e335d | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OnlineWorkSuite |
| Operation: | write | Name: | Start Page |
Value: http://hp.myway.com/onlineworksuite/ttab02/index.html?n=78C2C86F&p2=^CP6^mni000^TTAB02&ptb=CFE94DDA-36CD-4523-BEE0-7659B64CAA43&coid=5eb9d836784b44c8a10744c5df6e335d | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OnlineWorkSuiteTooltab Uninstall Internet Explorer |
| Operation: | write | Name: | DisplayName |
Value: OnlineWorkSuite Internet Explorer Homepage and New Tab | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OnlineWorkSuiteTooltab Uninstall Internet Explorer |
| Operation: | write | Name: | UninstallString |
Value: Rundll32.exe "C:\Users\admin\AppData\Local\OnlineWorkSuiteTooltab\TooltabExtension.dll" U uninstall:OnlineWorkSuite | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OnlineWorkSuiteTooltab Uninstall Internet Explorer |
| Operation: | write | Name: | Publisher |
Value: Mindspark Interactive Network, Inc. | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OnlineWorkSuiteTooltab Uninstall Internet Explorer |
| Operation: | write | Name: | HelpLink |
Value: http://support.mindspark.com/ | |||
| (PID) Process: | (8300) onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OnlineWorkSuiteTooltab Uninstall Internet Explorer |
| Operation: | write | Name: | URLInfoAbout |
Value: http://support.mindspark.com/ | |||
| (PID) Process: | (7020) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7020) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
3
Suspicious files
93
Text files
149
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8300 | onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | C:\Users\admin\AppData\Local\Temp\nsh5226.tmp\nsDialogs.dll | executable | |
MD5:B9A5A272154FC0DD652EF9C59C5D63A0 | SHA256:D84D810B8F8819F4A34D5E033B72951EADDA1BBB5ED0B8C76874B6C25001CAA9 | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\SG5UMOCJ\index[1].htm | html | |
MD5:9C725406CB6ECDB9689EA524D9220763 | SHA256:D60A0FD83768CC8D610462241D93282EAE489F608992422B43B4DBC1B39A0507 | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\MainIcon[1].png | image | |
MD5:CE46F6B3A74B8DF7BE86EA77A5F6D87D | SHA256:E05A14884955EDCFAA6DF1ED91E0ECC32ED98DCA5CA0EB152140E835A997E9AC | |||
| 8300 | onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | C:\Users\admin\AppData\Local\OnlineWorkSuiteTooltab\TooltabExtension.dll | executable | |
MD5:767737F00455032D893A223B78621F2D | SHA256:E71ECA3BA443107880EA99520422489C4EFC238B846681B6E3A5D3C9E61071BF | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\0CBLTDI3\app[1].js | text | |
MD5:F37E8DCA46314BC2821EFACF257E441A | SHA256:0619094F8445C609E80B62EC94662B93F167B3D44FF9540DE498F1F5F1BB4D9E | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:7F924EAEA21BB91214FF7B4525F3BD29 | SHA256:E718475014C8F51A8F2746FBE90A7BFF516B65BEF36EE6340A5FC746BC5DFC32 | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\final_logo_newtab[1].png | image | |
MD5:B8CE9A5CE1FEE01C806AAC4E6C5182B2 | SHA256:A6A62412261BD620D6B34035A3BD2739B8B030907B1A2818C4058EF61578F72F | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\MSIMGSIZ.DAT | binary | |
MD5:0392ADA071EB68355BED625D8F9695F3 | SHA256:B1313DD95EAF63F33F86F72F09E2ECD700D11159A8693210C37470FCB84038F7 | |||
| 8608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:646F35CFECF6737037397A6551D09860 | SHA256:D4D46BD5D15FADFE6F438CAAE26EDFC690040008D8EB88BF8994709D168DD027 | |||
| 8300 | onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | C:\Users\admin\AppData\Local\Temp\nsh5226.tmp\cancel_blue_1473362942233.bmp | image | |
MD5:C20F972BB1E321BCF007A11D1433496C | SHA256:DDEB1A235C5FBB989FADF287A627736894F62406C0258B2A8B73379ADA7A6775 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
258
TCP/UDP connections
200
DNS requests
139
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
8300 | onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | GET | — | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-11&errorType=nsisError&errorDetails=SendRequest+Error&platform=vicinio&anxv=2.7.1.3000&anxd=2018-05-18&coid=5eb9d836784b44c8a10744c5df6e335d&refPartner=^CP6^mni000^TTAB02&refSub=&anxl=en-US&anxr=-2003885429&refCobrand=CP6&refCampaign=mni000&refTrack=TTAB02&refCountry= | unknown | — | — | unknown |
356 | svchost.exe | POST | 200 | 20.190.159.71:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
2600 | svchost.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
356 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.159.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
4144 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.159.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2600 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7368 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8300 | onlineworksuite.5eb9d836784b44c8a10744c5df6e335d.exe.bin.exe | 34.120.232.229:80 | anx.mindspark.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2600 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8608 | iexplore.exe | Misc activity | INSTALLER [ANY.RUN] VCSoapClient Installer HTTP POST Request (UA) |
8608 | iexplore.exe | Misc activity | INSTALLER [ANY.RUN] VCSoapClient Installer HTTP POST Request (UA) |
9052 | iexplore.exe | Misc activity | ET INFO Observed UA-CPU Header |
8608 | iexplore.exe | Misc activity | INSTALLER [ANY.RUN] VCSoapClient Installer HTTP POST Request (UA) |
8608 | iexplore.exe | Misc activity | INSTALLER [ANY.RUN] VCSoapClient Installer HTTP POST Request (UA) |
7864 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7864 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7864 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7864 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |