| File name: | VNC-Viewer-6.20.529-Windows.exe |
| Full analysis: | https://app.any.run/tasks/1e2a38a7-8be1-43e1-8b77-ac132cbdb0bc |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2020, 04:48:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4702659C961EFC0BB3CC8E51F9B0F57C |
| SHA1: | E07351A94CEAEBCB8A9BE7BA951B0023D89CC2EE |
| SHA256: | 6764E39303B4C49E8401E91878B1B26E3706AB5FFB4BAC5F6E6334ECFE3363AE |
| SSDEEP: | 196608:OXvJ9jQrahC3EbfDEUiBu++xImRpcDjvu9Jp:YB9jQWhCCiBF+xImXMLuN |
MALICIOUS
Application was dropped or rewritten from another process
- vncviewer.exe (PID: 3580)
- vncviewer.exe (PID: 3328)
SUSPICIOUS
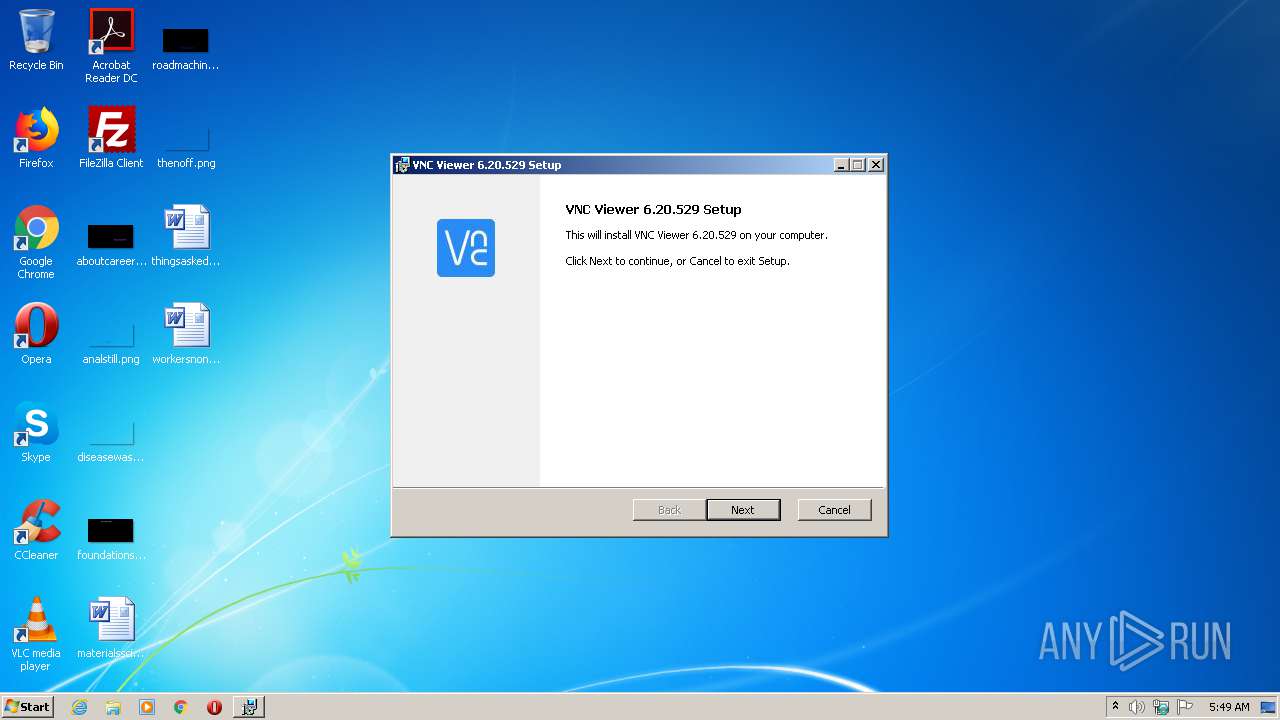
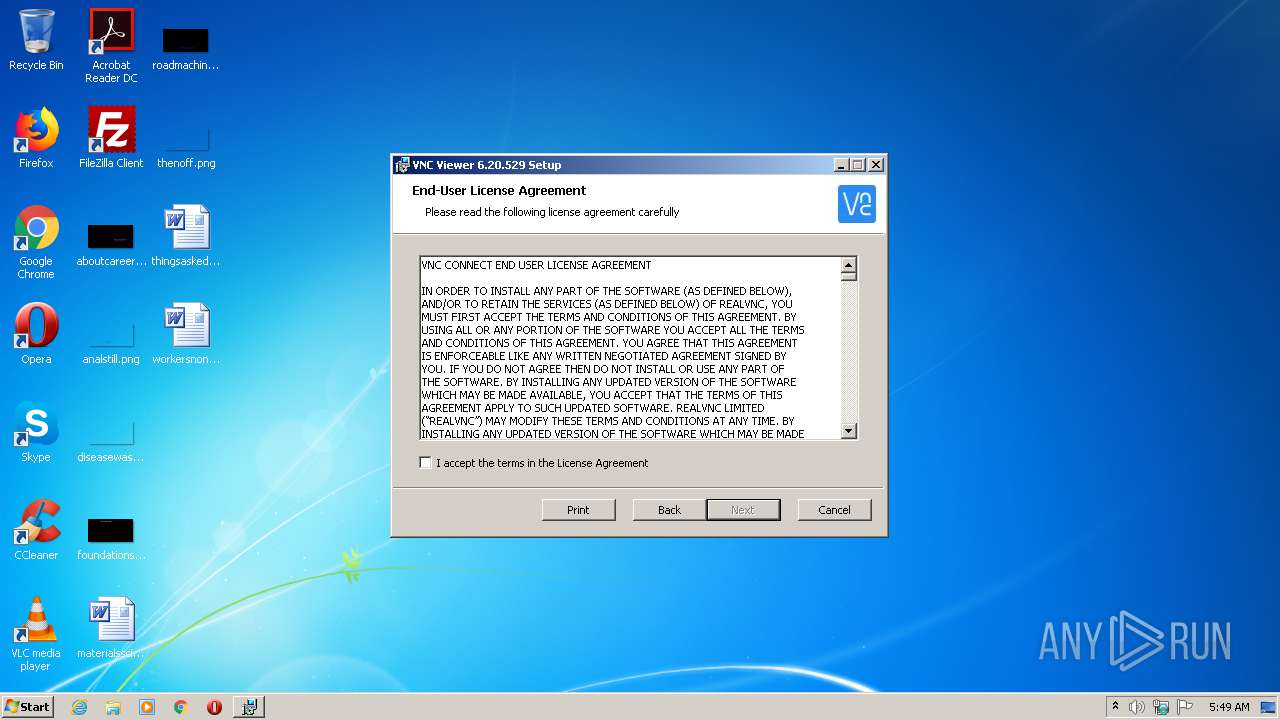
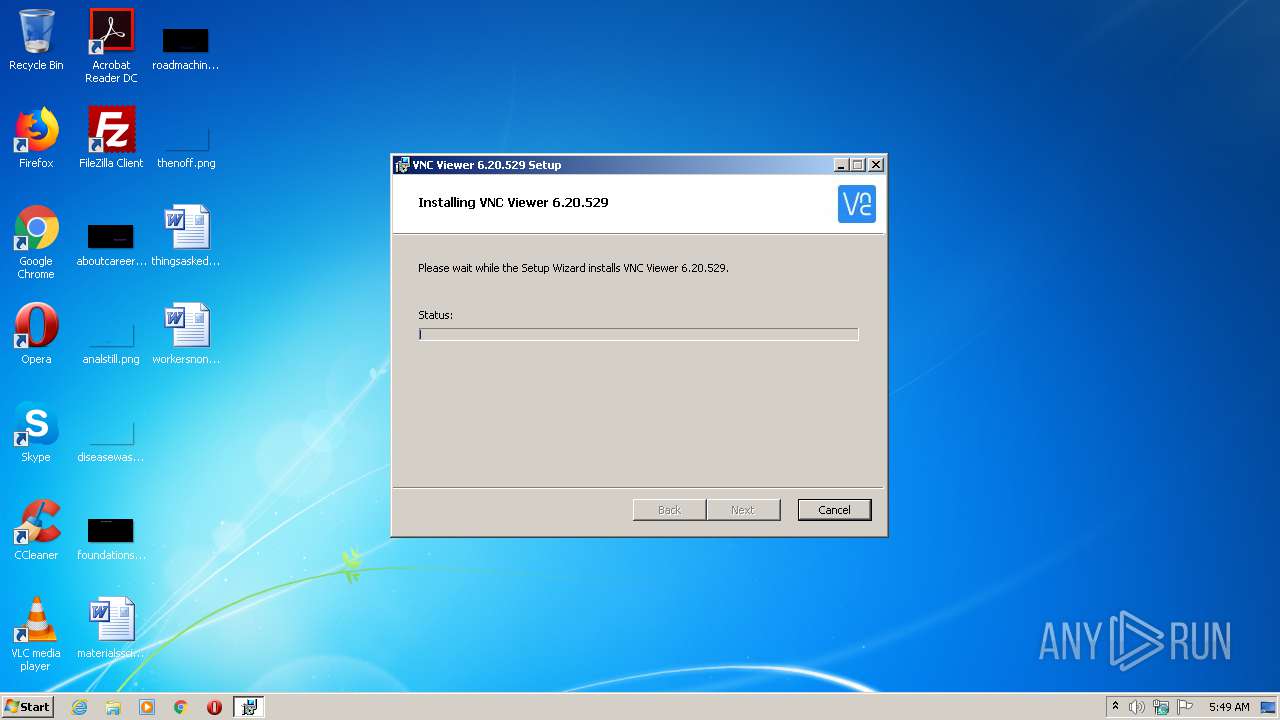
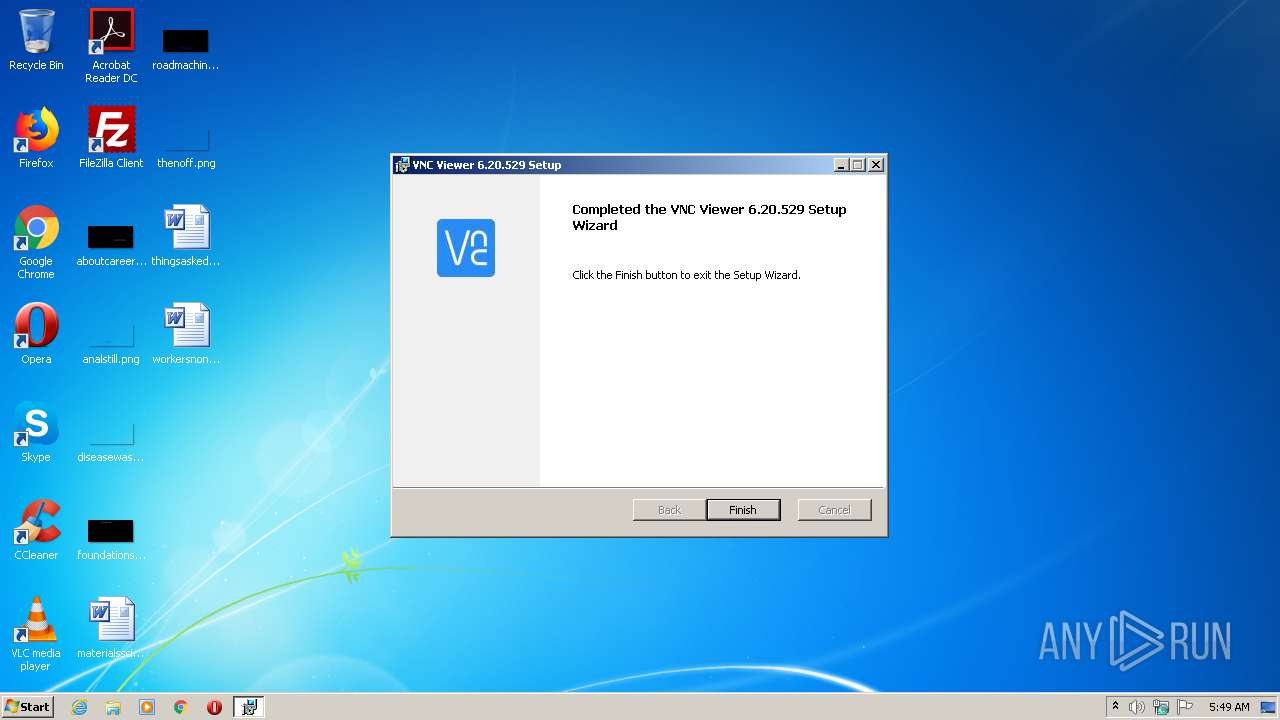
Starts Microsoft Installer
- VNC-Viewer-6.20.529-Windows.exe (PID: 2144)
Modifies the open verb of a shell class
- msiexec.exe (PID: 4032)
Creates files in the user directory
- vncviewer.exe (PID: 3580)
Executed as Windows Service
- vssvc.exe (PID: 2516)
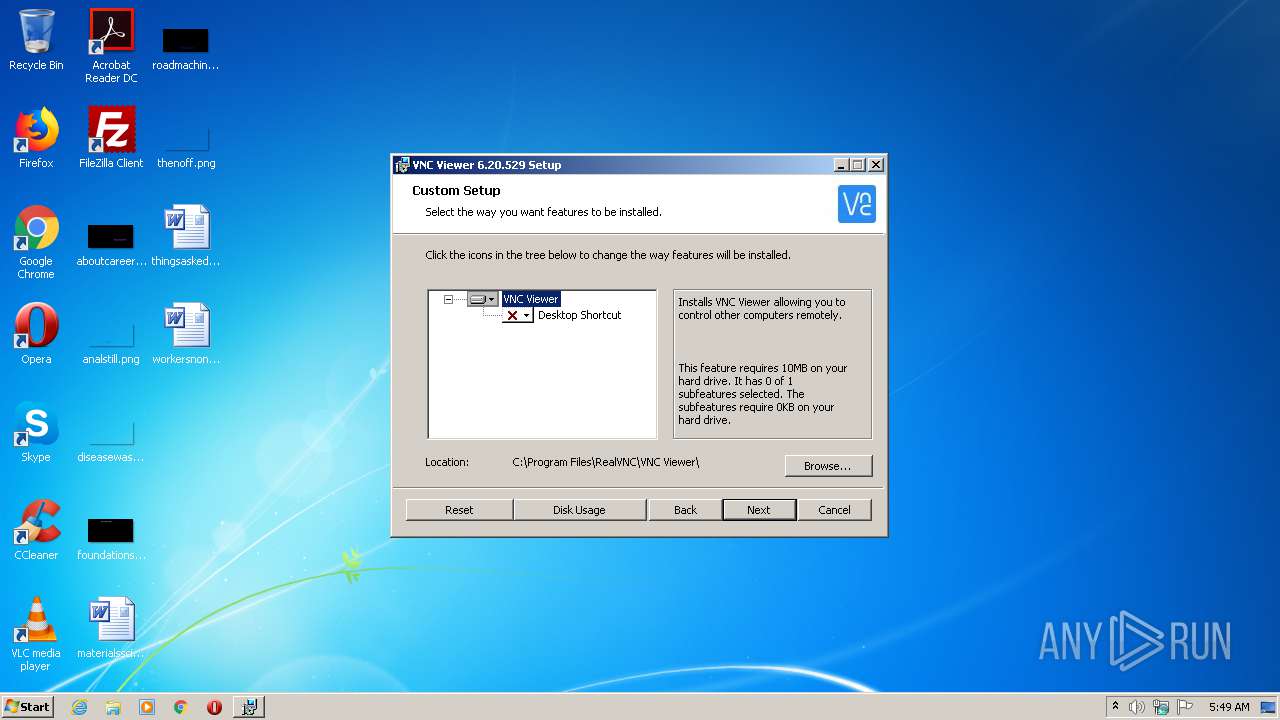
Executable content was dropped or overwritten
- msiexec.exe (PID: 4032)
Application launched itself
- vncviewer.exe (PID: 3580)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2596)
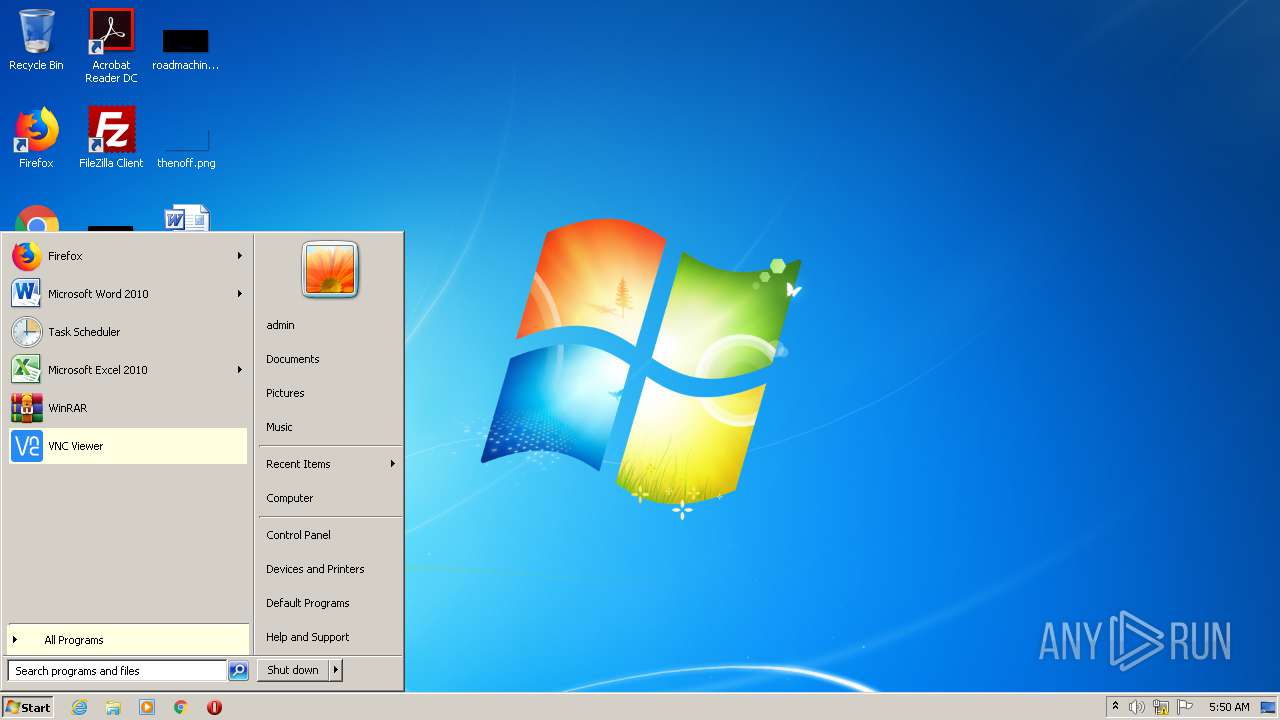
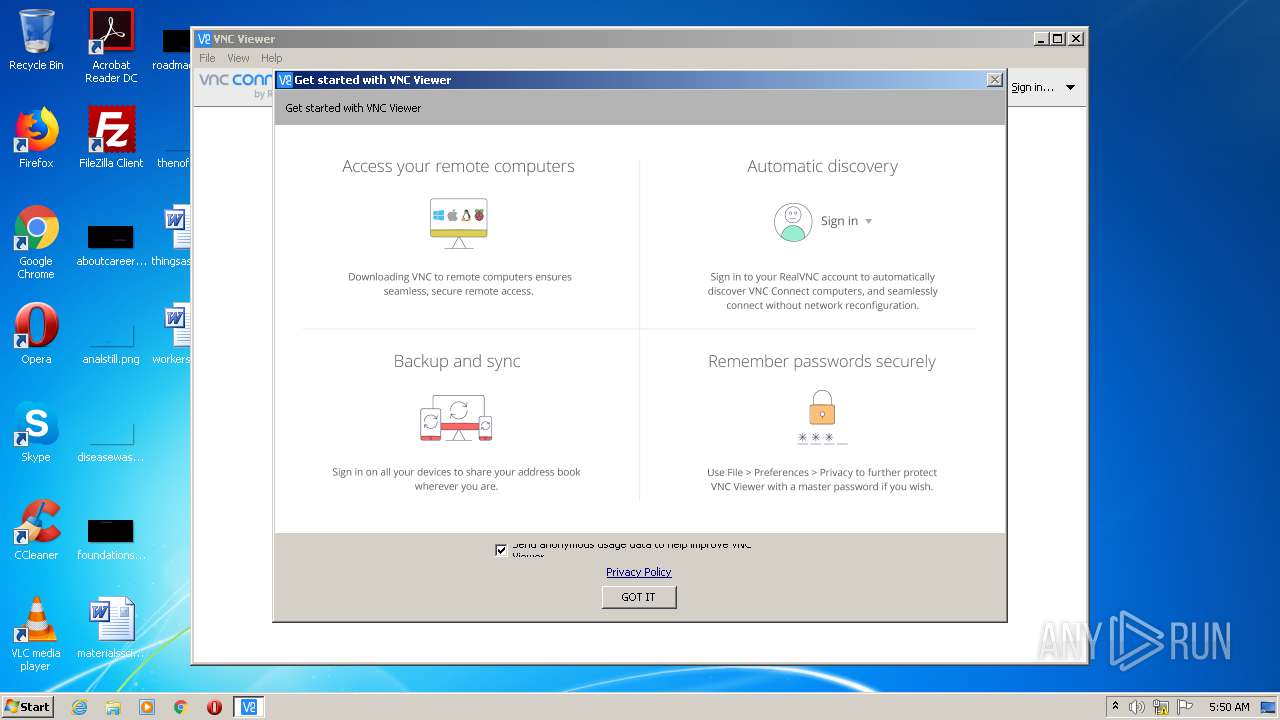
Manual execution by user
- vncviewer.exe (PID: 3580)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2516)
Application launched itself
- msiexec.exe (PID: 4032)
Creates files in the program directory
- msiexec.exe (PID: 4032)
Searches for installed software
- msiexec.exe (PID: 4032)
Creates a software uninstall entry
- msiexec.exe (PID: 4032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:29 13:59:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 1202176 |
| InitializedDataSize: | 9343488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x83a9a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.20.529.42646 |
| ProductVersionNumber: | 6.20.529.42646 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | RealVNC Ltd |
| FileDescription: | VNC® Viewer Installer |
| FileVersion: | 6.20.529 (r42646) |
| InternalName: | vncviewer-installer |
| LegalCopyright: | Copyright © 2002-2020 RealVNC Ltd. |
| LegalTrademarks: | RealVNC and VNC are trademarks of RealVNC Ltd and are protected by trademark registrations and/or pending trademark applications in the European Union, United States of America and other jurisdictions. |
| OriginalFileName: | vncviewer-installer.exe |
| ProductName: | VNC® |
| ProductVersion: | 6.20.529 (r42646) |
| ProgramName: | VNC® Viewer Installer |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-May-2020 11:59:20 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | RealVNC Ltd |
| FileDescription: | VNC® Viewer Installer |
| FileVersion: | 6.20.529 (r42646) |
| InternalName: | vncviewer-installer |
| LegalCopyright: | Copyright © 2002-2020 RealVNC Ltd. |
| LegalTrademarks: | RealVNC and VNC are trademarks of RealVNC Ltd and are protected by trademark registrations and/or pending trademark applications in the European Union, United States of America and other jurisdictions. |
| OriginalFilename: | vncviewer-installer.exe |
| ProductName: | VNC® |
| ProductVersion: | 6.20.529 (r42646) |
| ProgramName: | VNC® Viewer Installer |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-May-2020 11:59:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0012567A | 0x00125800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58994 |
.rdata | 0x00127000 | 0x0003EA34 | 0x0003EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.48746 |
.data | 0x00166000 | 0x00006E3C | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79193 |
.rsrc | 0x0016D000 | 0x00896048 | 0x00896200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.70713 |
.reloc | 0x00A04000 | 0x0000F680 | 0x0000F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67301 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2223 | 1351 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.91708 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.91366 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
LANGDESCS.TXT | 4.49238 | 55 | Latin 1 / Western European | English - United States | BUILTINRESOURCE |
LANGS.TXT | 2.89629 | 14 | Latin 1 / Western European | English - United States | BUILTINRESOURCE |
VNC32.MSI | 7.71525 | 4210688 | Latin 1 / Western European | UNKNOWN | BUILTINRESOURCE |
VNC64.MSI | 7.68882 | 4784128 | Latin 1 / Western European | UNKNOWN | BUILTINRESOURCE |
!APP_ICON | 2.64576 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
ole32.dll |
Total processes
42
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1444 | C:\Windows\system32\msiexec.exe /i C:\Users\admin\AppData\Local\Temp\vnc32.msi ProductLanguage=1033 | C:\Windows\system32\msiexec.exe | — | VNC-Viewer-6.20.529-Windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2144 | "C:\Users\admin\AppData\Local\Temp\VNC-Viewer-6.20.529-Windows.exe" | C:\Users\admin\AppData\Local\Temp\VNC-Viewer-6.20.529-Windows.exe | — | explorer.exe | |||||||||||
User: admin Company: RealVNC Ltd Integrity Level: MEDIUM Description: VNC® Viewer Installer Exit code: 0 Version: 6.20.529 (r42646) Modules
| |||||||||||||||
| 2516 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | C:\Windows\system32\MsiExec.exe -Embedding 5EA409D0BBB68ADB9138C759DCD7DBDE M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
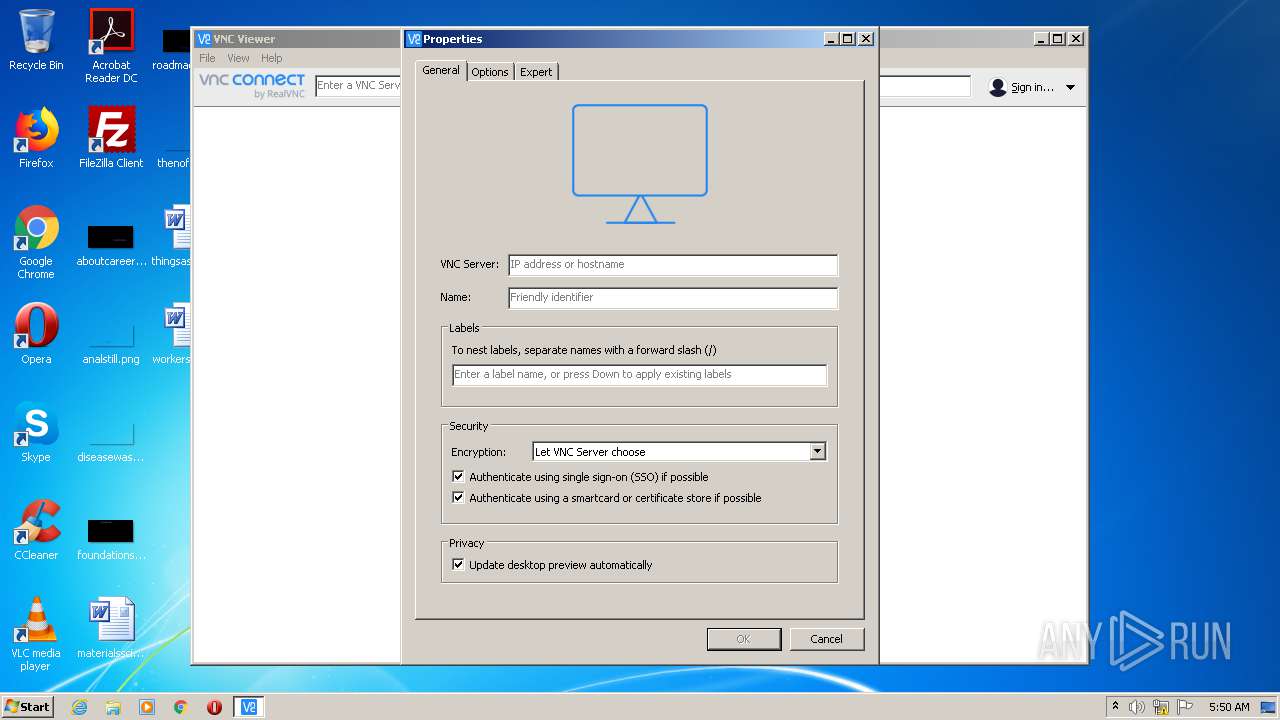
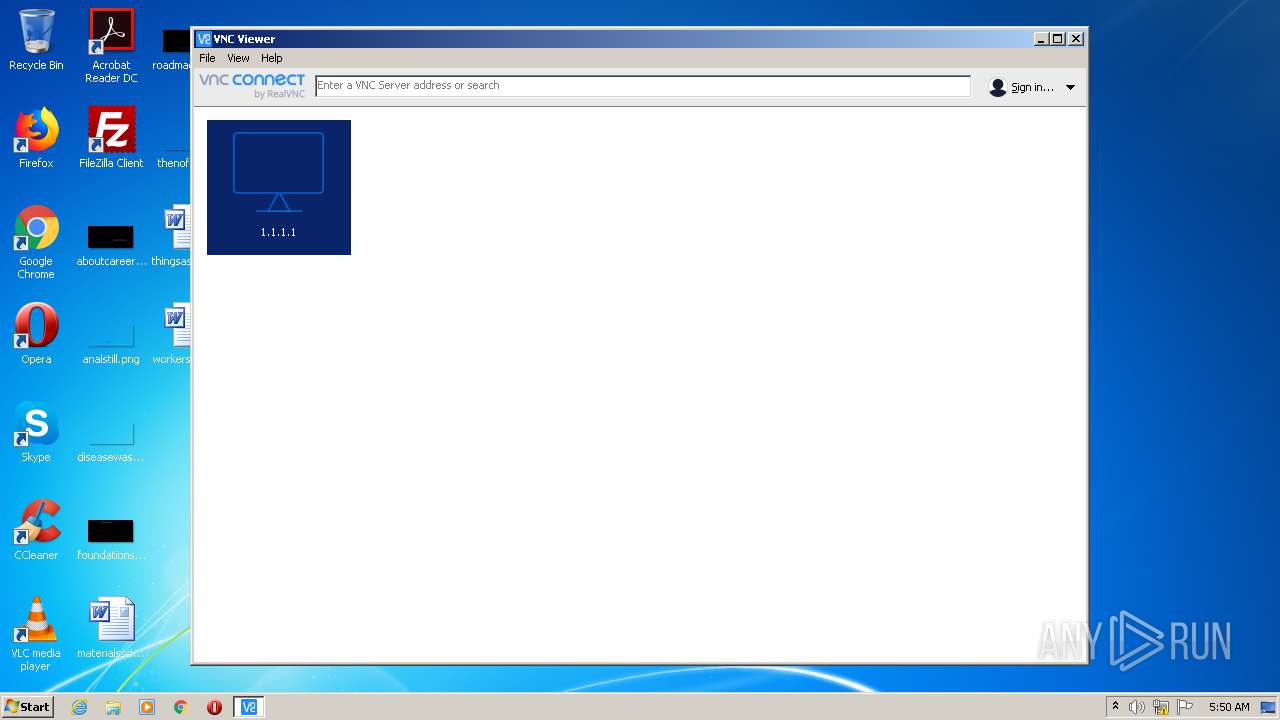
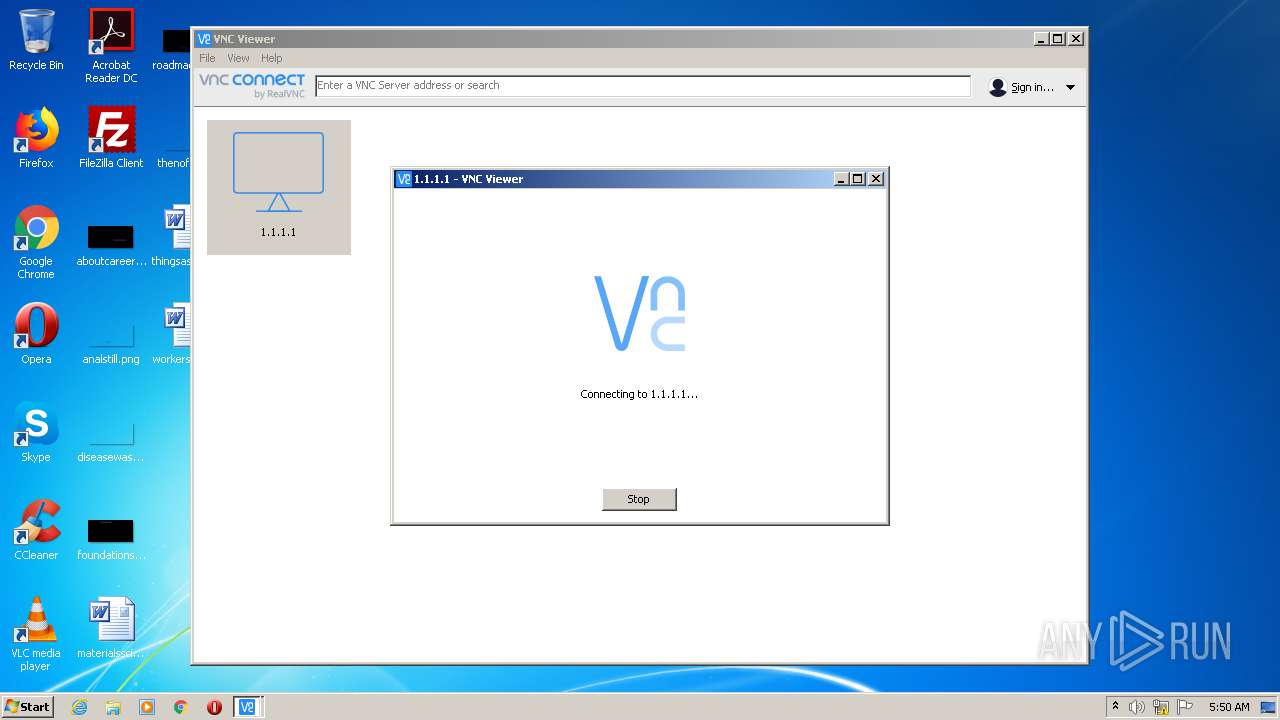
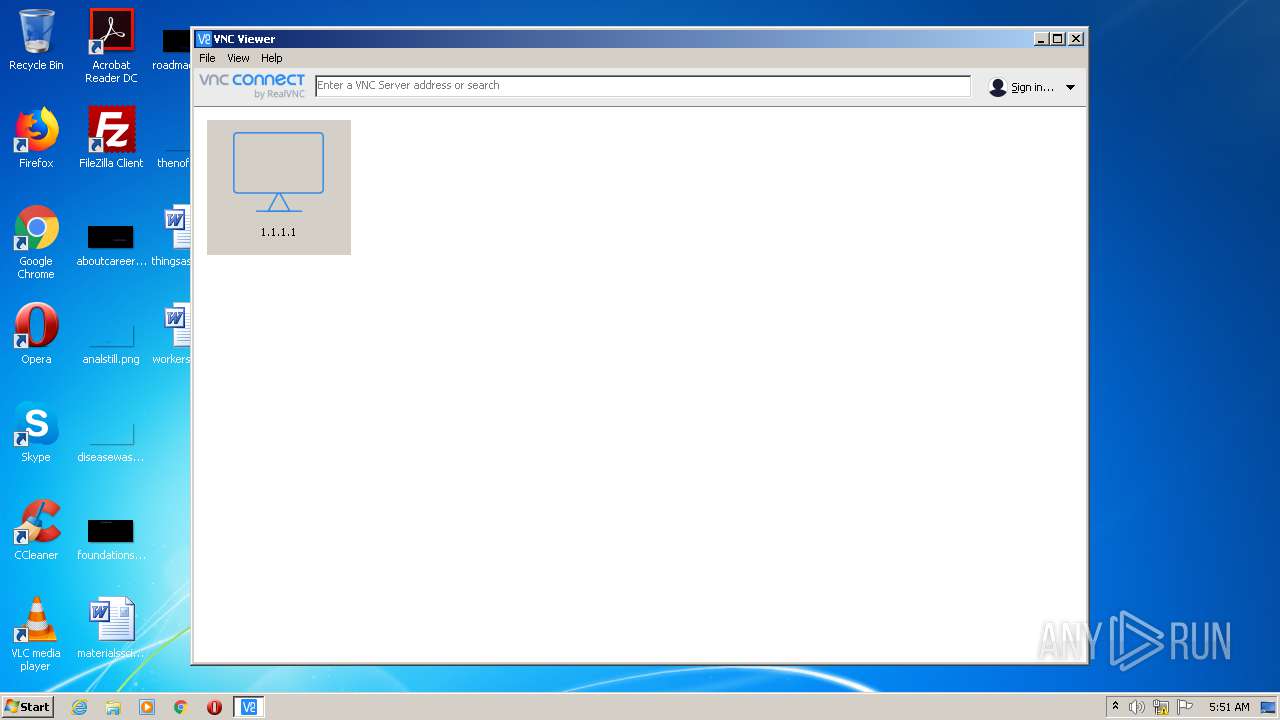
| 3328 | "C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe" -child 1.1.1.1 -hash 0594edf89330105e249867f64bcb15b2deb13a59c45b1ef99ad2871339228585 -sid S-1-5-21-1302019708-1500728564-335382590-1000 RealVNC.admin.vncviewer.vncpipehelper.1511308334 | C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe | vncviewer.exe | ||||||||||||
User: admin Company: RealVNC Ltd Integrity Level: MEDIUM Description: VNC® Viewer Exit code: 0 Version: 6.20.529 (r42646) Modules
| |||||||||||||||
| 3580 | "C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe" | C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe | explorer.exe | ||||||||||||
User: admin Company: RealVNC Ltd Integrity Level: MEDIUM Description: VNC® Viewer Exit code: 0 Version: 6.20.529 (r42646) Modules
| |||||||||||||||
| 4032 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
970
Read events
680
Write events
274
Delete events
16
Modification events
| (PID) Process: | (1444) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000A4036AC7E36AD601C00F0000DC090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000A4036AC7E36AD601C00F0000DC090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 39 | |||
| (PID) Process: | (4032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000A63AC2C7E36AD601C00F0000DC090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000009DC4C7E36AD601C00F00008C080000E80300000100000000000000000000006819B0E60DFDA147AB45896A038F836B0000000000000000 | |||
| (PID) Process: | (2516) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000EC4CBC7E36AD601D4090000480D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000EC4CBC7E36AD601D40900009C020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000EC4CBC7E36AD601D40900003C0D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000EC4CBC7E36AD601D40900006C070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
8
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | VNC-Viewer-6.20.529-Windows.exe | C:\Users\admin\AppData\Local\Temp\vnc32.msi | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Windows\Installer\dee39.msi | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF7C57830452942126.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Program Files\RealVNC\VNC Viewer\SetupCache\VNC-Viewer-6.20.529-Windows-32bit.msi | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Program Files\RealVNC\VNC Viewer\SetupCache\VNC-Viewer-6.20.529-Windows-32bit.msiKey | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Windows\Installer\dee3c.msi | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Windows\Installer\MSIF9A6.tmp | — | |
MD5:— | SHA256:— | |||
| 4032 | msiexec.exe | C:\Windows\Installer\MSIF9F5.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
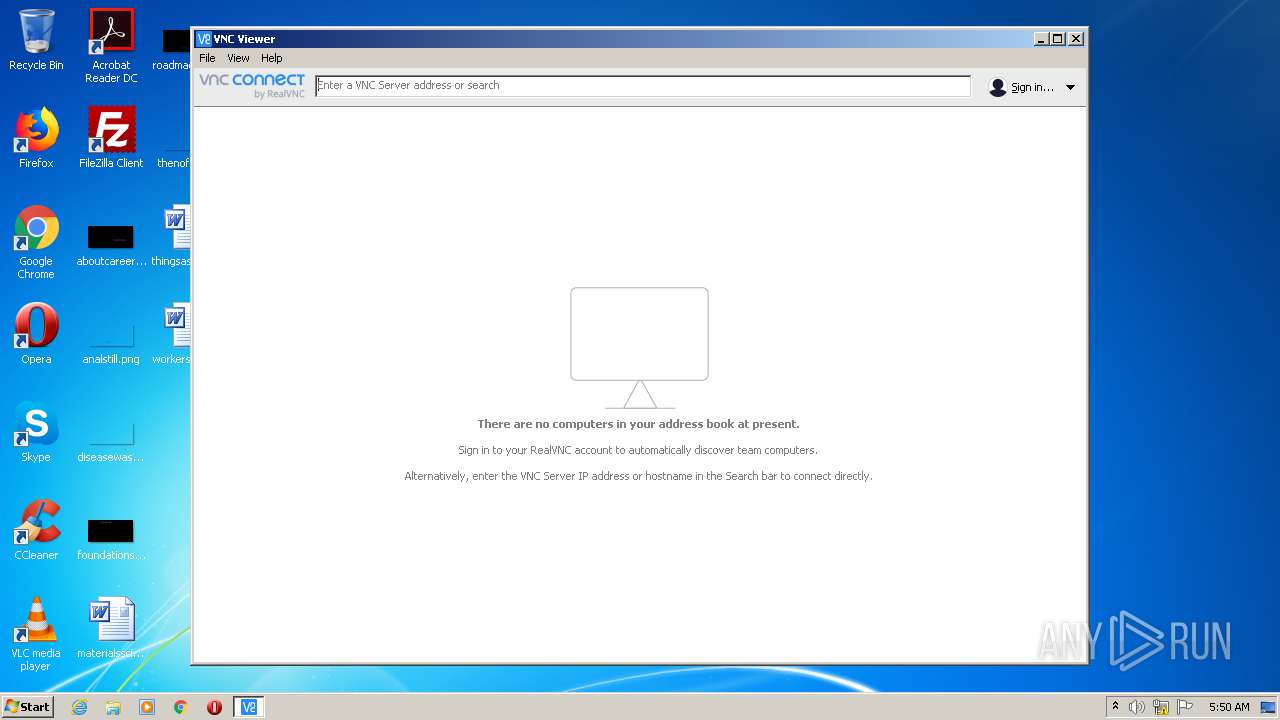
3580 | vncviewer.exe | 165.254.191.229:443 | hb-c.services.vnc.com | NTT America, Inc. | US | unknown |
3328 | vncviewer.exe | 1.1.1.1:5900 | — | — | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hb-c.services.vnc.com |
| unknown |