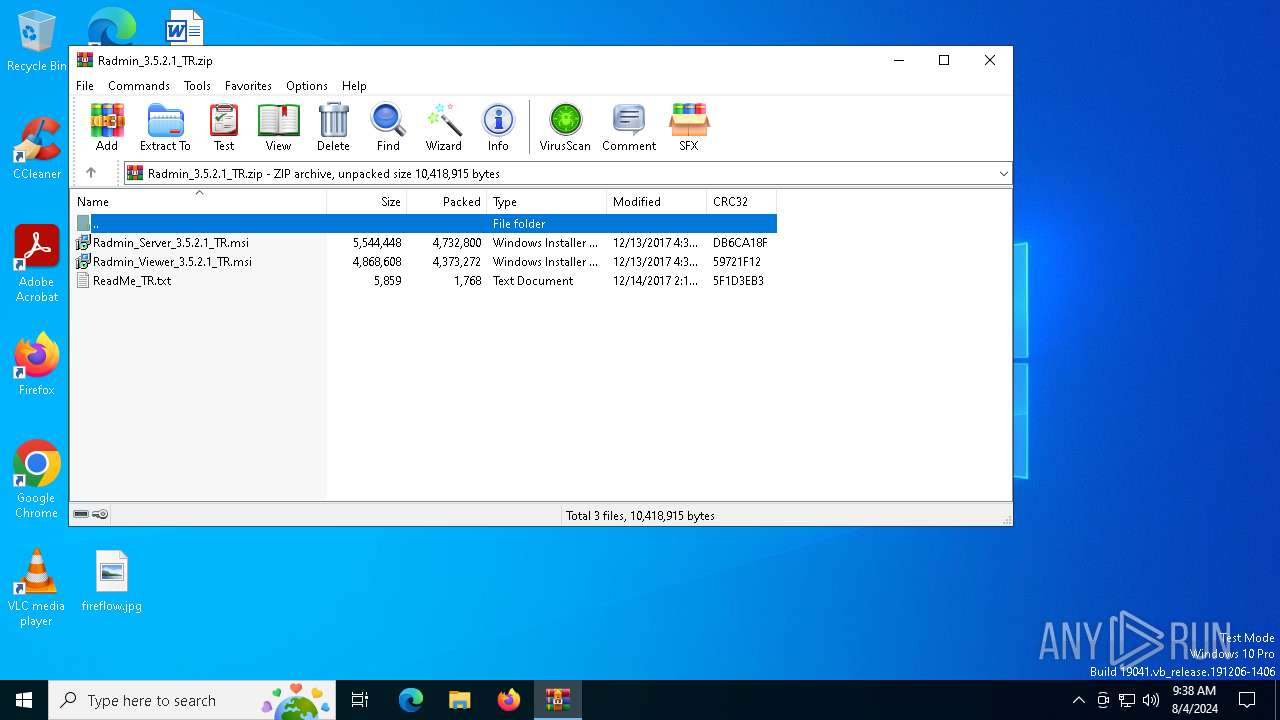
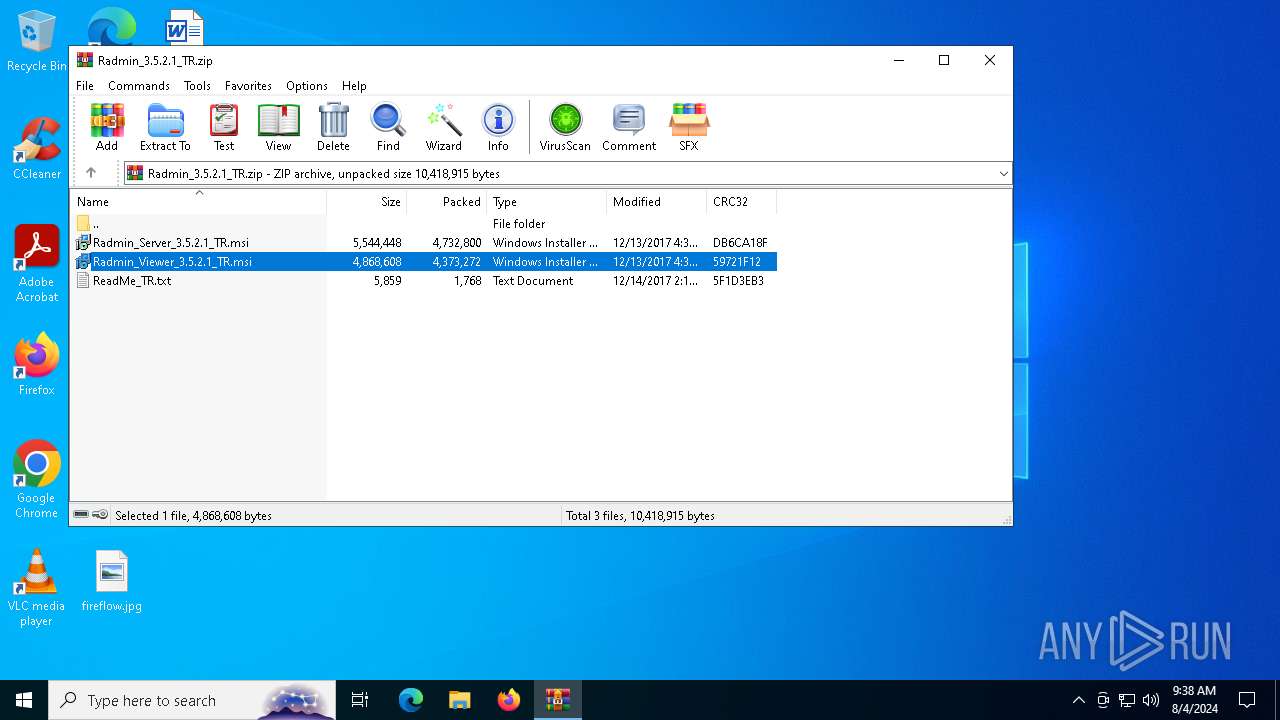
| download: | /download/files/Radmin_3.5.2.1_TR.zip |
| Full analysis: | https://app.any.run/tasks/755b339f-4d39-4f4d-bfa9-8d4407e3d04e |
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2024, 09:37:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | BFC6EEE5148108500E0BEB97227B171B |
| SHA1: | 1382516593E755B9469D49F40324AB50ED385274 |
| SHA256: | 6757A54D56B811F9C8D885697B555FC3E197B5ACB52EF6C15D5F9C44FC13EF35 |
| SSDEEP: | 98304:eoENXVzKyxGMe7b+CSZAU7t7KD02kA2vi2frHqbveVSE4y7LE9bFX3FYvHtxS7Sf:C7lEtPB71qCks6Teb6ueqL/Het |
MALICIOUS
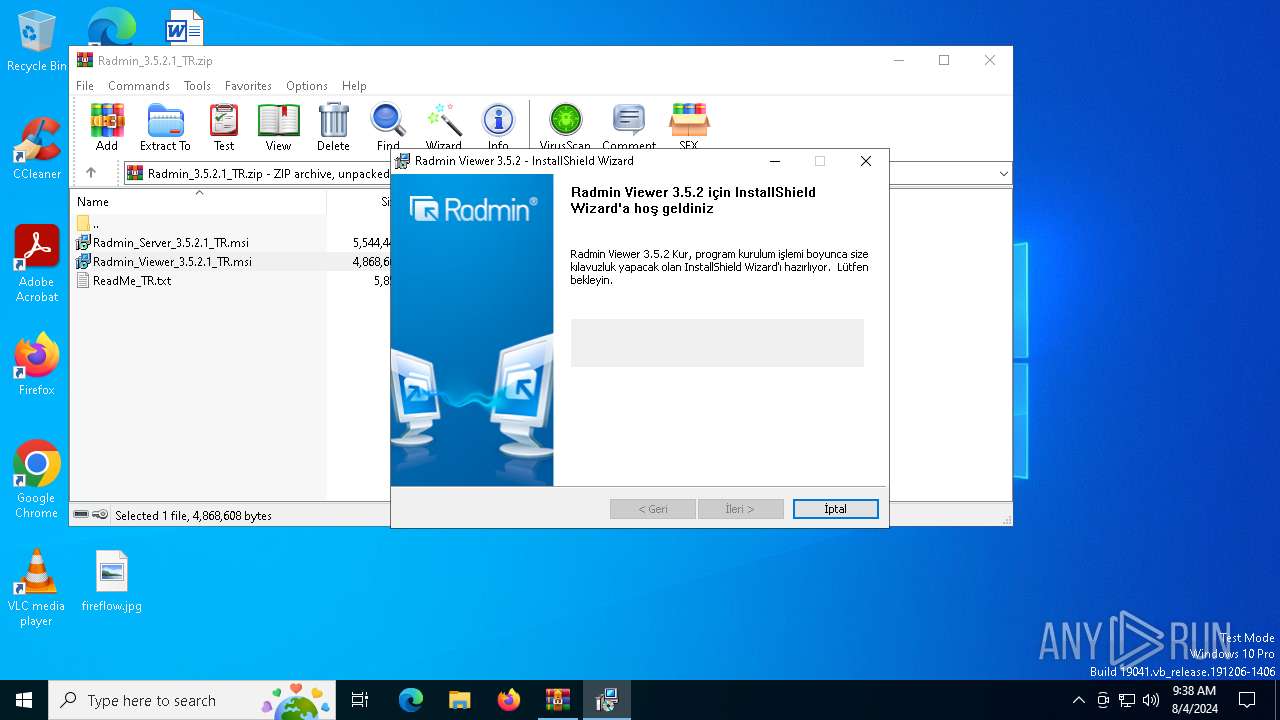
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6356)
- msiexec.exe (PID: 6580)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6356)
Executes as Windows Service
- VSSVC.exe (PID: 6656)
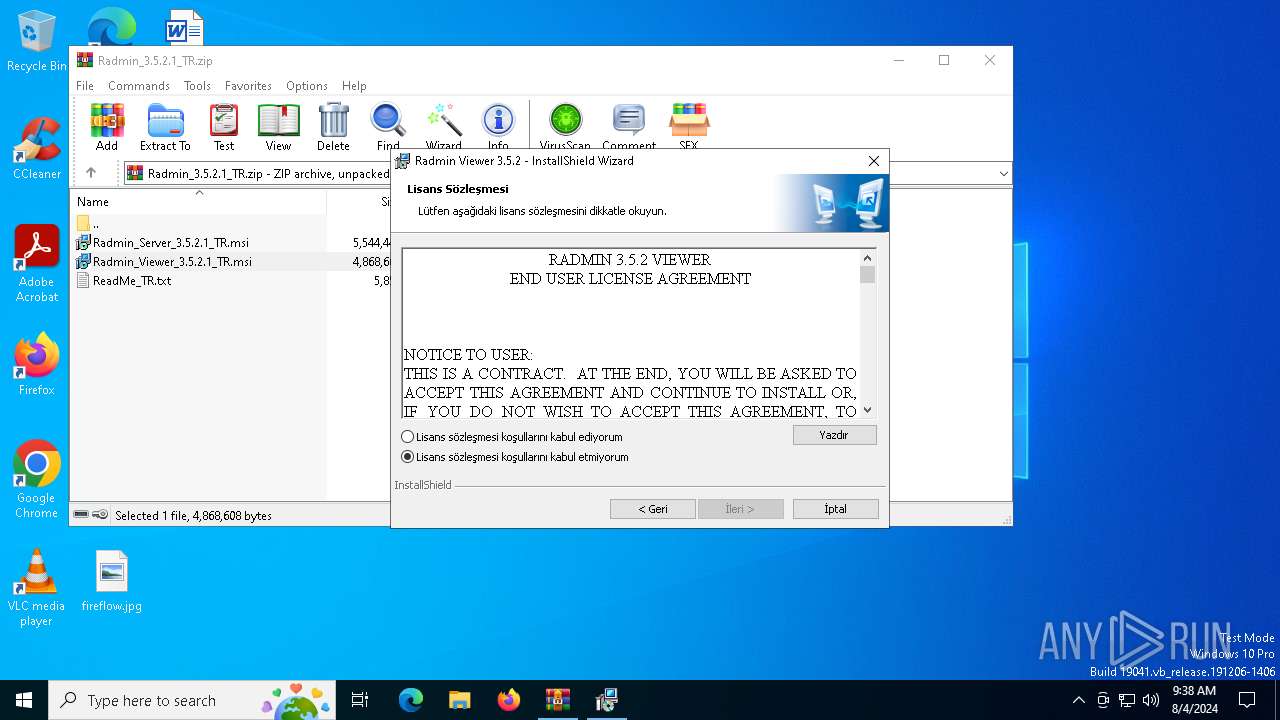
Checks Windows Trust Settings
- msiexec.exe (PID: 6580)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6580)
Process drops legitimate windows executable
- msiexec.exe (PID: 6580)
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6356)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6356)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6492)
Creates files or folders in the user directory
- msiexec.exe (PID: 6492)
Checks proxy server information
- msiexec.exe (PID: 6492)
Create files in a temporary directory
- msiexec.exe (PID: 6624)
Reads the computer name
- msiexec.exe (PID: 6624)
- msiexec.exe (PID: 6580)
- msiexec.exe (PID: 3540)
- msiexec.exe (PID: 888)
Checks supported languages
- msiexec.exe (PID: 6580)
- msiexec.exe (PID: 6624)
- msiexec.exe (PID: 888)
- msiexec.exe (PID: 3540)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6492)
- msiexec.exe (PID: 6580)
Reads the software policy settings
- msiexec.exe (PID: 6492)
- msiexec.exe (PID: 6580)
Drops the executable file immediately after the start
- msiexec.exe (PID: 6492)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6580)
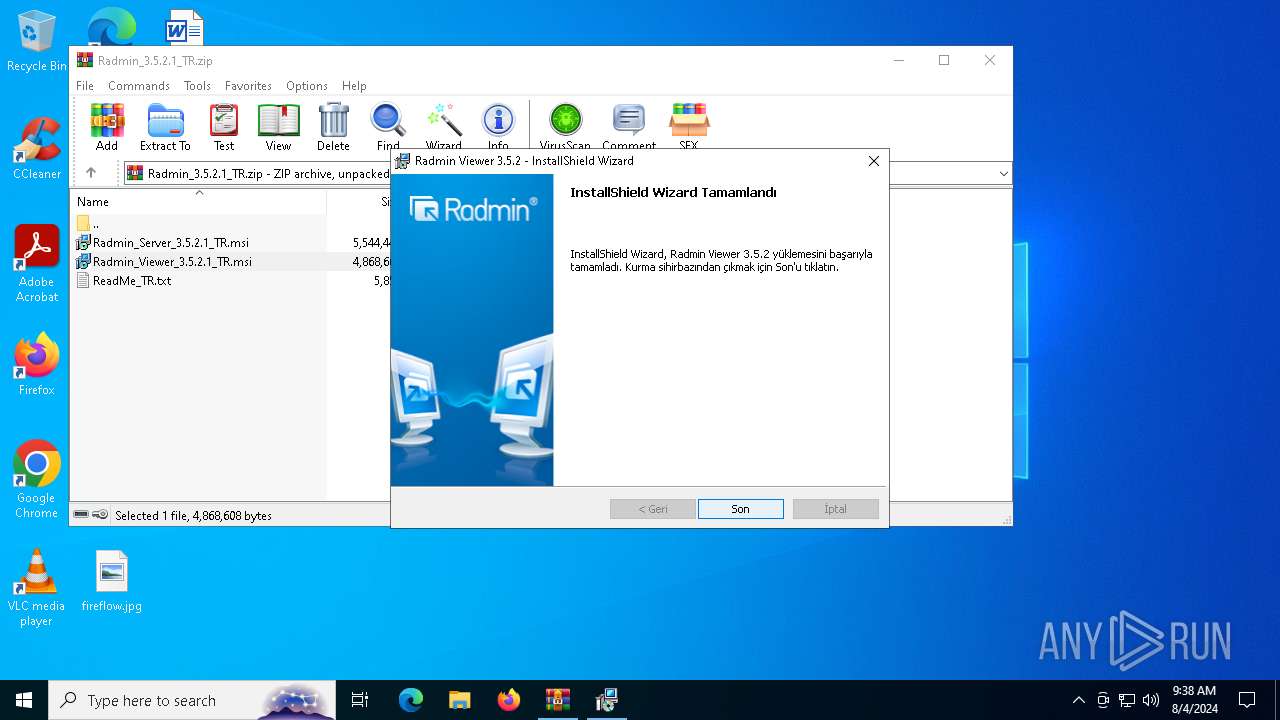
Creates a software uninstall entry
- msiexec.exe (PID: 6580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:12:13 16:32:34 |
| ZipCRC: | 0xdb6ca18f |
| ZipCompressedSize: | 4732800 |
| ZipUncompressedSize: | 5544448 |
| ZipFileName: | Radmin_Server_3.5.2.1_TR.msi |
Total processes
142
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa6356.13086\ReadMe_TR.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 888 | C:\Windows\syswow64\MsiExec.exe -Embedding 014DED7459189CB1CC1EC1BA6D2459AC E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3540 | C:\Windows\syswow64\MsiExec.exe -Embedding 08092C8F375C1FAD93A8797AAA212F5F | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
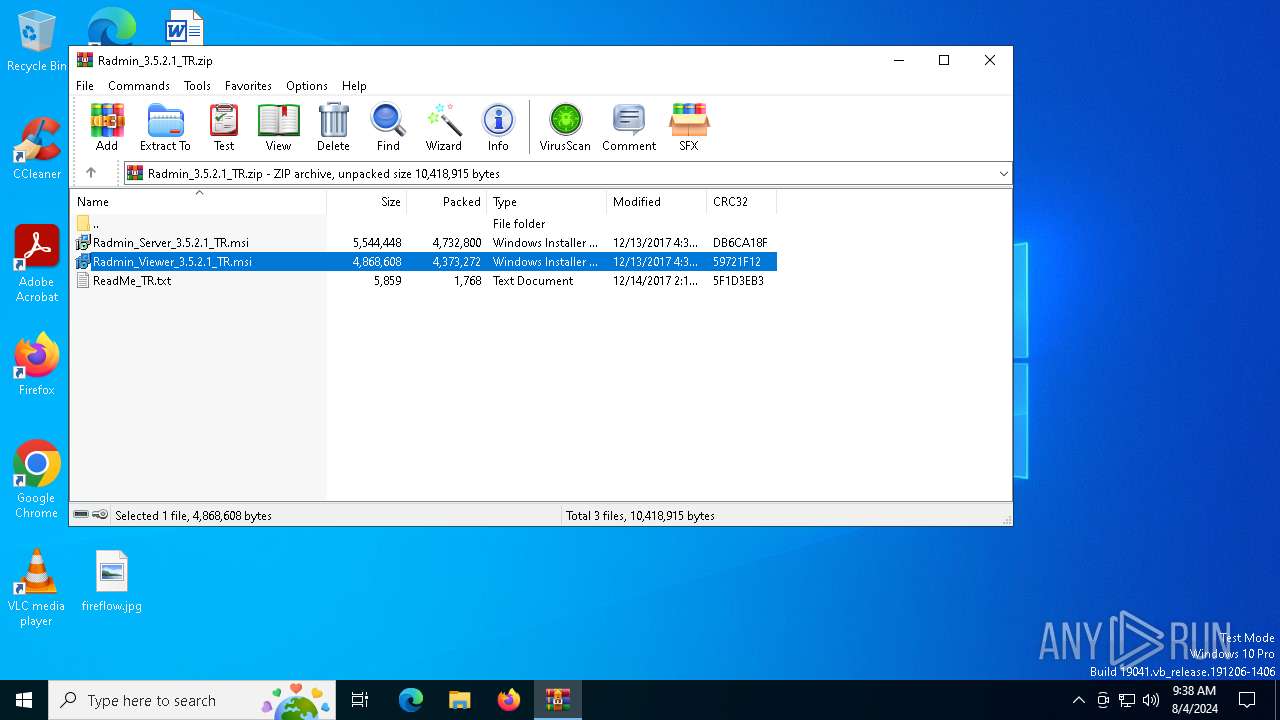
| 6356 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Radmin_3.5.2.1_TR.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
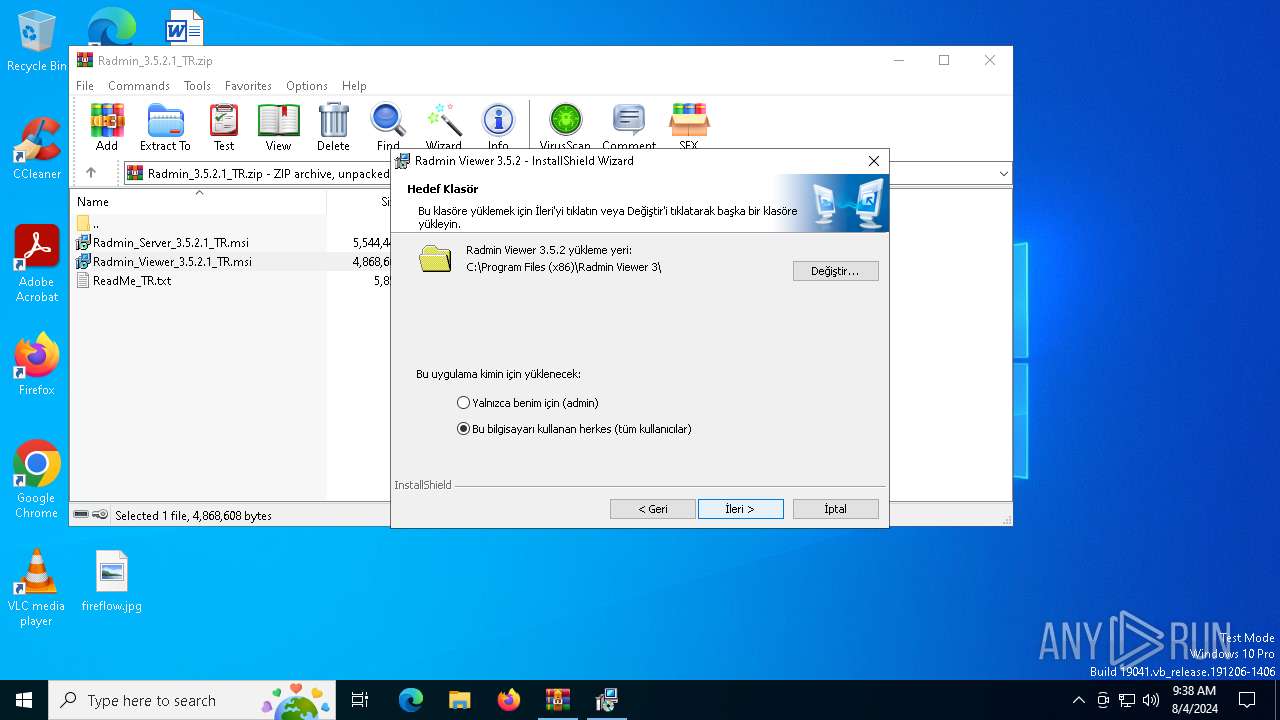
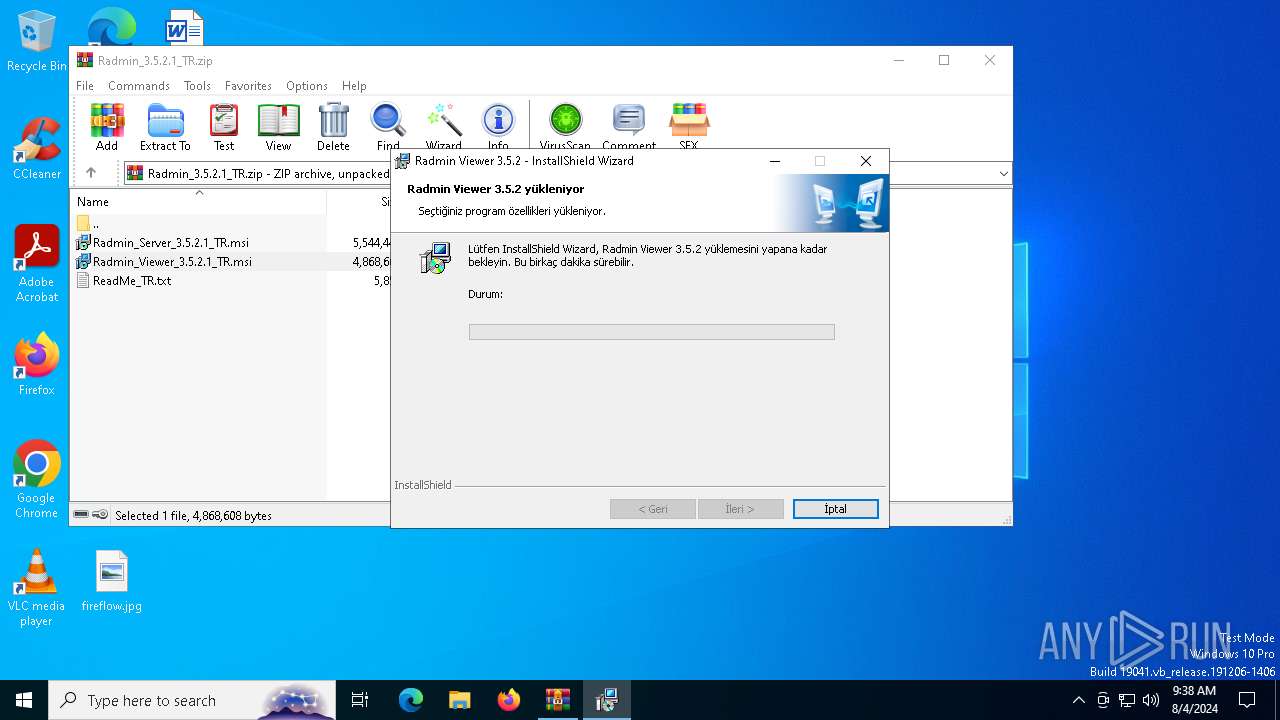
| 6492 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa6356.9731\Radmin_Viewer_3.5.2.1_TR.msi" | C:\Windows\System32\msiexec.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6580 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6624 | C:\Windows\syswow64\MsiExec.exe -Embedding 9666A5015163AD6C4DF7AE4ED8644379 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6656 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 769
Read events
18 395
Write events
355
Delete events
19
Modification events
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Radmin_3.5.2.1_TR.zip | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
| (PID) Process: | (6356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
Executable files
21
Suspicious files
28
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6356.9731\Radmin_Server_3.5.2.1_TR.msi | — | |
MD5:— | SHA256:— | |||
| 6356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6356.9731\Radmin_Viewer_3.5.2.1_TR.msi | — | |
MD5:— | SHA256:— | |||
| 6580 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6580 | msiexec.exe | C:\Windows\Installer\ecf32.msi | — | |
MD5:— | SHA256:— | |||
| 6492 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C46E7B0F942663A1EDC8D9D6D7869173_6043FC604A395E1485AF7AC16D16B7CE | binary | |
MD5:5BCD8EC710183F4D3BCE51E77C9BB914 | SHA256:95812DEDD4921771CC31701958BC7DD4AEBBF0EA8E73FA2964B7FF25BBAC43C9 | |||
| 6356 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6356.9731\ReadMe_TR.txt | text | |
MD5:C243C781CA6DC7F0E28AD6CE79D18072 | SHA256:88DB57A6CEE37BD1545DD47F2D51617FA305CFA162715DF651D4E2C6E609573C | |||
| 6580 | msiexec.exe | C:\Windows\Temp\~DF7D88FB0F186109DB.TMP | binary | |
MD5:235DAF7CF5DAA79FB345C4C979B21609 | SHA256:16A795BE9EB16B062B4B1E95B06BF1018C9E9DF1D3AA999C24853B2A461E052B | |||
| 6580 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:E7A44C0CCD257EA63304FB7F5249EE25 | SHA256:F56EA8F092EE564B27A6EFB9504ADB133B7CFBDB881A479B8E78A04C7B6DE834 | |||
| 6624 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{9F9073EA-5DCE-4B23-8A0C-C7D2C89AEADC}\Support_File.txt | text | |
MD5:308CC0526D58B8D64EA9D638D8E4B430 | SHA256:5584C51AC4D8F5746DEEEF8BCEF05C3229C0BA93F894DCC76E77FBEB6130E25D | |||
| 6580 | msiexec.exe | C:\Windows\Temp\~DFF1701C2239B02820.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
47
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6492 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | US | binary | 5 b | whitelisted |
6492 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | US | binary | 5 b | whitelisted |
6492 | msiexec.exe | GET | 200 | 152.199.19.74:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEGqlk0afvjzQyYSvvrtcLpI%3D | US | binary | 1.47 Kb | whitelisted |
6492 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://s1.symcb.com/pca3-g5.crl | US | binary | 834 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
3900 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6932 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6896 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
3900 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4484 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4060 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6492 | msiexec.exe | 152.199.19.74:80 | s2.symcb.com | EDGECAST | US | unknown |
6492 | msiexec.exe | 192.229.221.95:80 | s1.symcb.com | EDGECAST | US | whitelisted |
4060 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.179:443 | www.bing.com | Akamai International B.V. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
s1.symcb.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
sv.symcd.com |
| shared |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |