| File name: | 01940258_2 |
| Full analysis: | https://app.any.run/tasks/09d0693c-71bd-4e2f-93e9-2d0f28ca05c5 |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2020, 02:37:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93ECE7B7B405BD9DE21E2092DF658F01 |
| SHA1: | 52E33E018CF42D43D4933BF3775B77911127C400 |
| SHA256: | 674BED3E55C0151A9314960F2C93271F6CE27E1A4EEF71F8C8989595E6647994 |
| SSDEEP: | 98304:DZgrJPMbjEdbWdTSbYtVwrAy8h+rOPNlK0/OwsitPZRFjoWlZCUfF:DZy1ZR8vPNn/5RtNjvZB |
MALICIOUS
Application was dropped or rewritten from another process
- licfldr.exe (PID: 2916)
- Transwiz.exe (PID: 3816)
- Transwiz.exe (PID: 1848)
Loads the Task Scheduler DLL interface
- 01940258_2.exe (PID: 2580)
SUSPICIOUS
Executable content was dropped or overwritten
- 01940258_2.exe (PID: 2580)
- msiexec.exe (PID: 1084)
- msiexec.exe (PID: 3824)
Creates files in the user directory
- 01940258_2.exe (PID: 2580)
Executed as Windows Service
- vssvc.exe (PID: 3188)
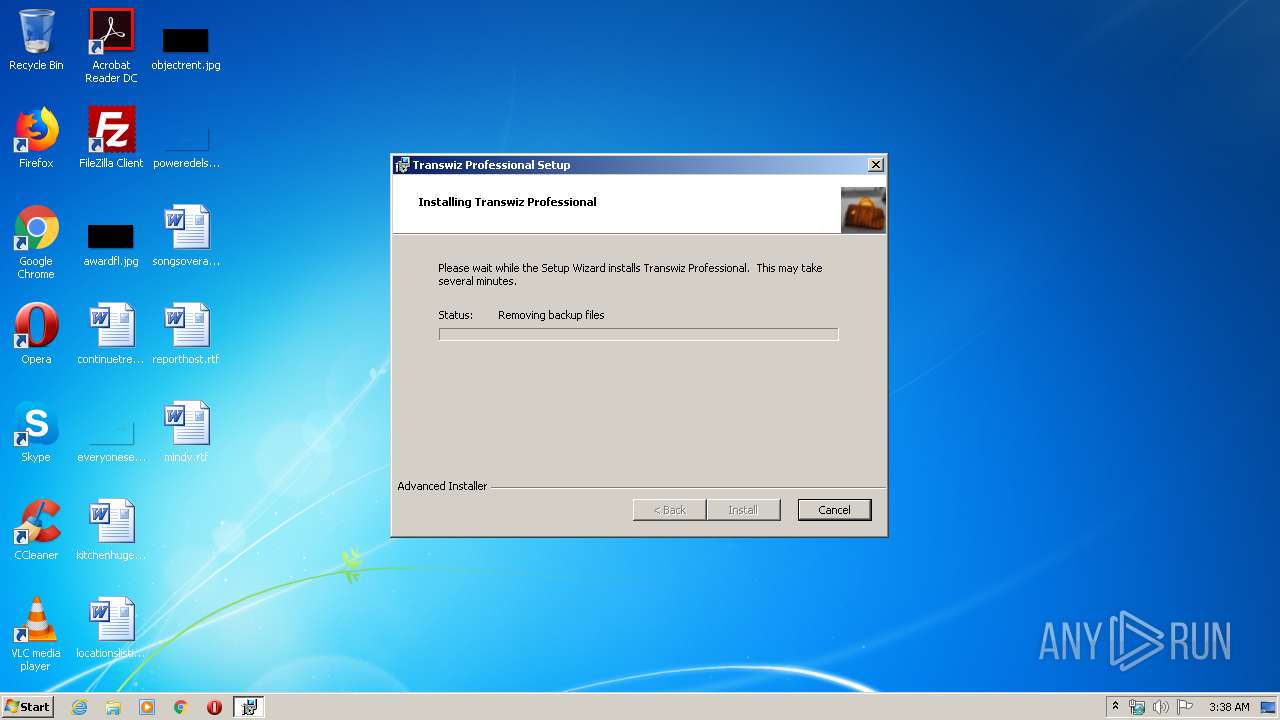
Starts Microsoft Installer
- 01940258_2.exe (PID: 2580)
INFO
Searches for installed software
- msiexec.exe (PID: 1084)
Application launched itself
- msiexec.exe (PID: 1084)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1916)
- MsiExec.exe (PID: 1692)
- MsiExec.exe (PID: 988)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3188)
Creates a software uninstall entry
- msiexec.exe (PID: 1084)
Creates files in the program directory
- msiexec.exe (PID: 1084)
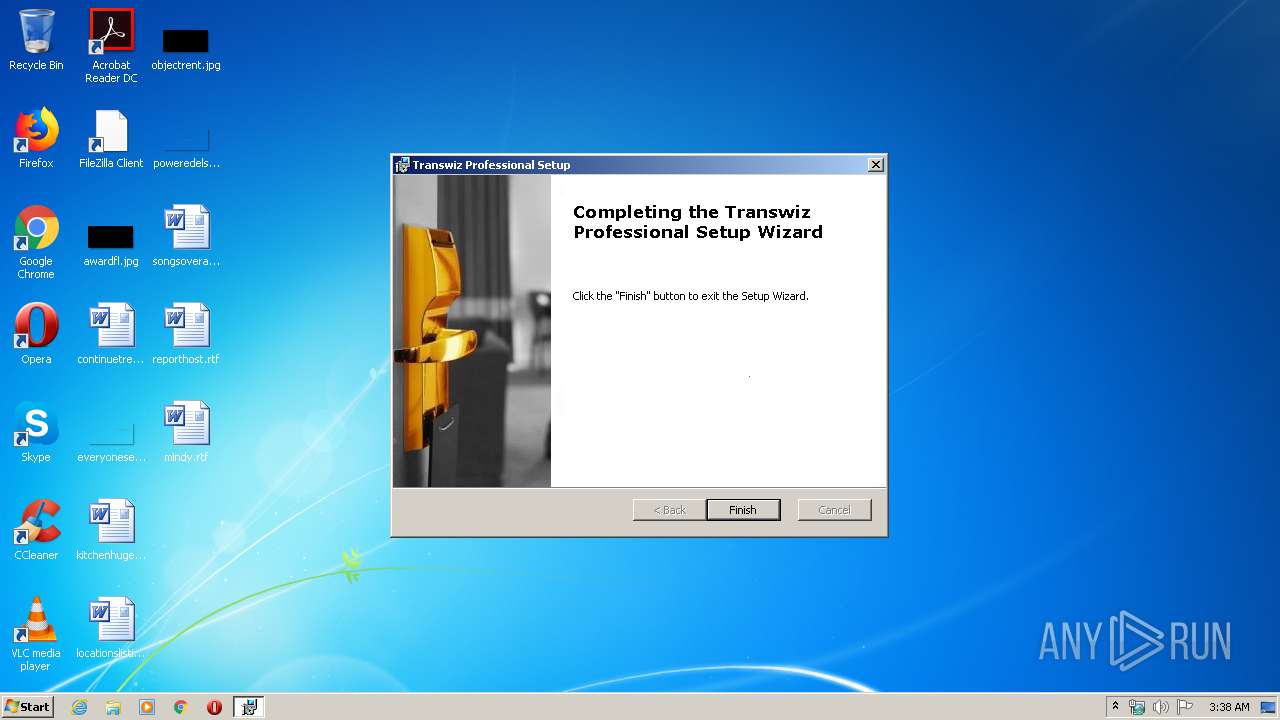
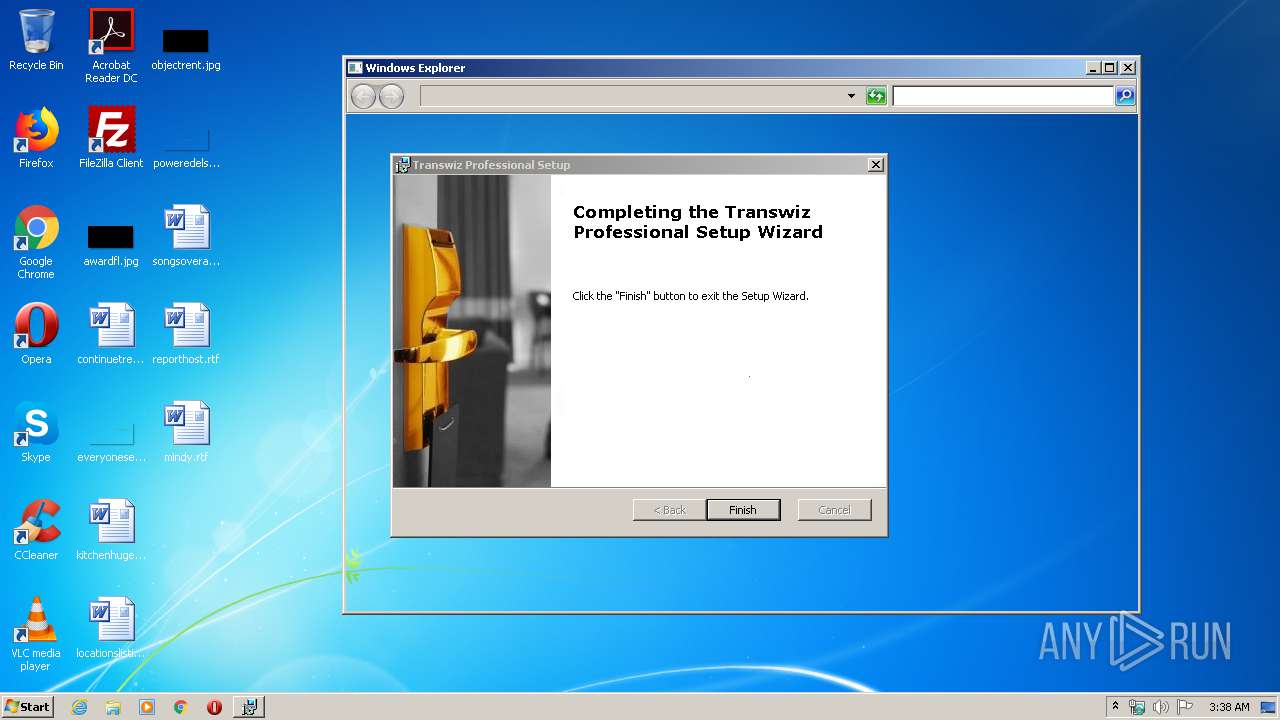
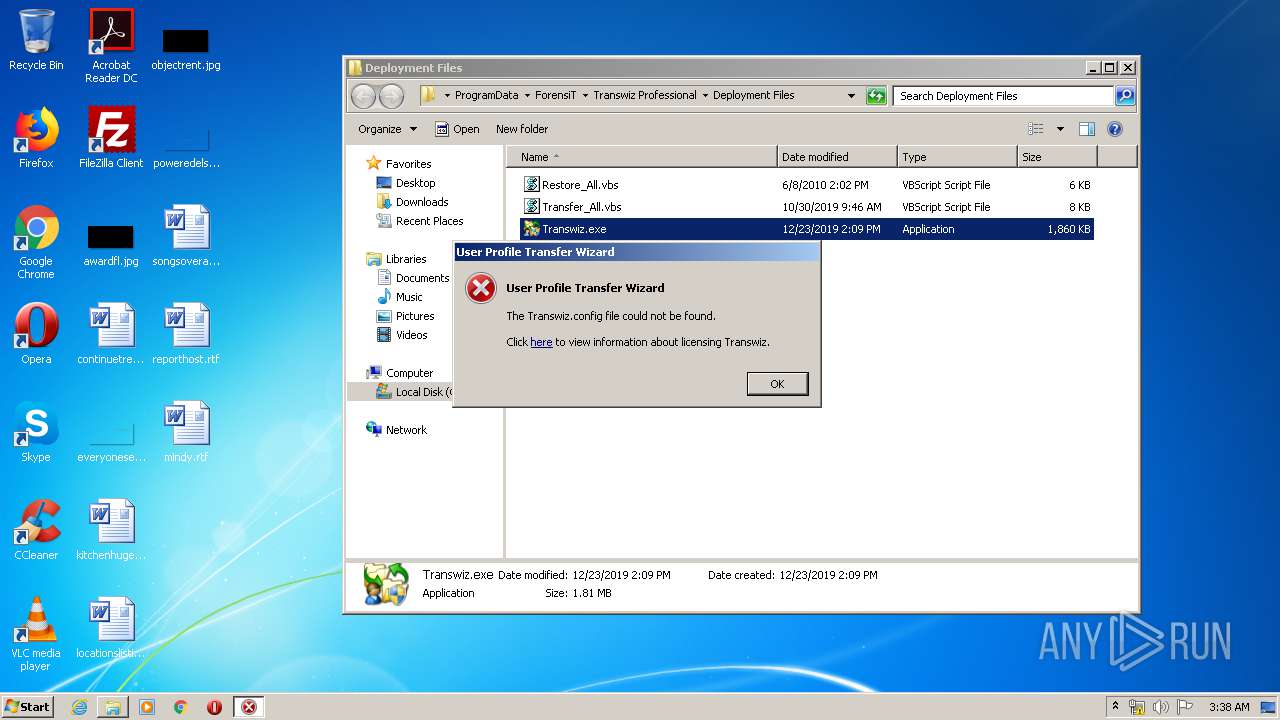
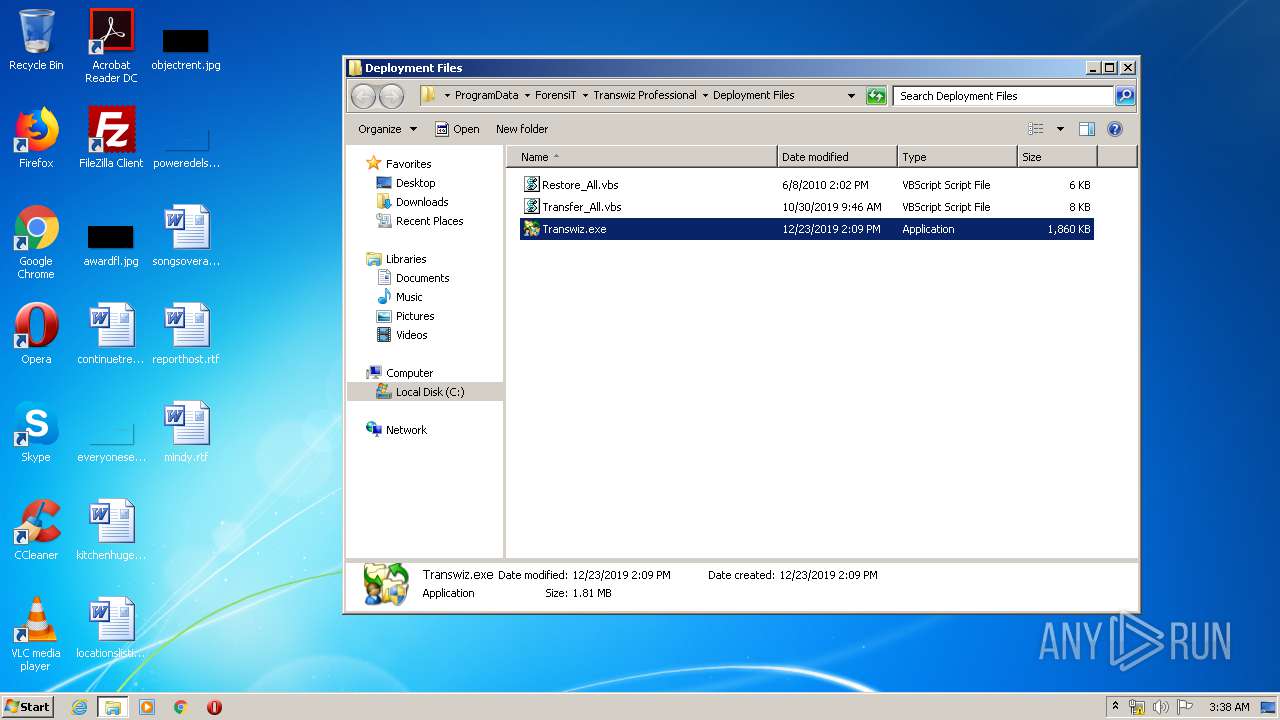
Manual execution by user
- Transwiz.exe (PID: 1848)
- Transwiz.exe (PID: 3816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:17 10:36:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.23 |
| CodeSize: | 1493504 |
| InitializedDataSize: | 628736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11952f |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.17.1094.0 |
| ProductVersionNumber: | 1.17.1094.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
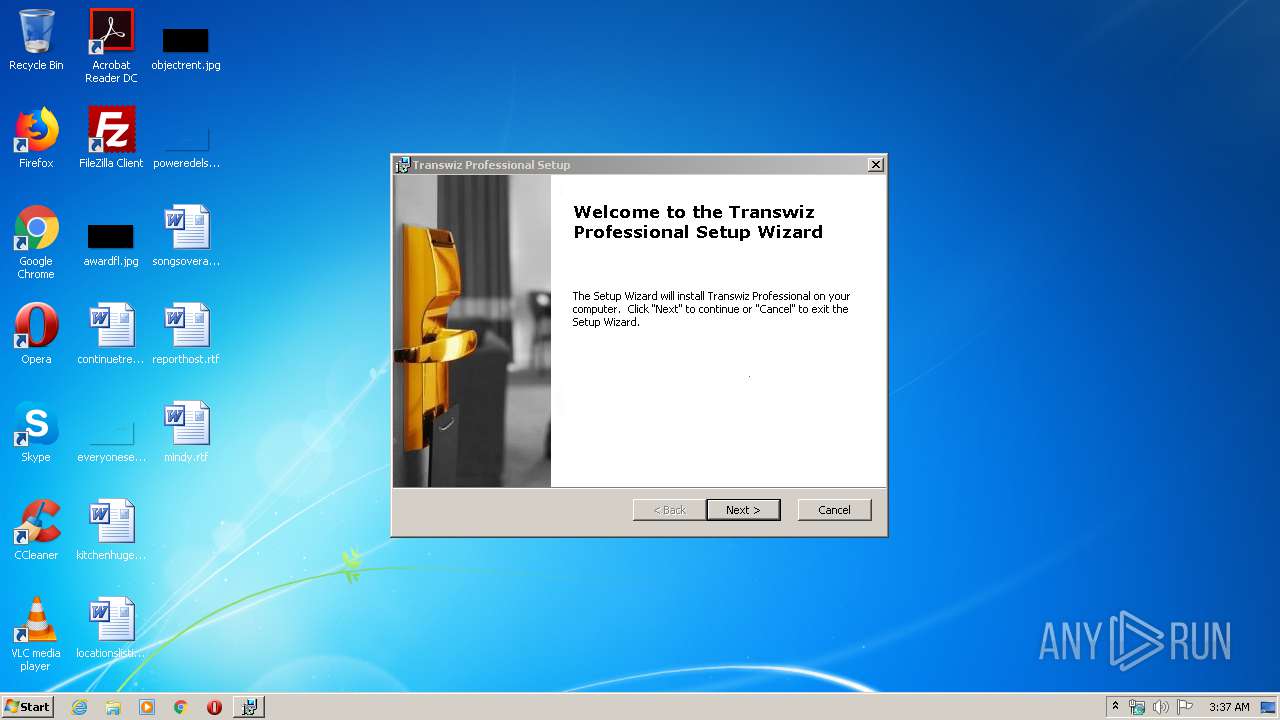
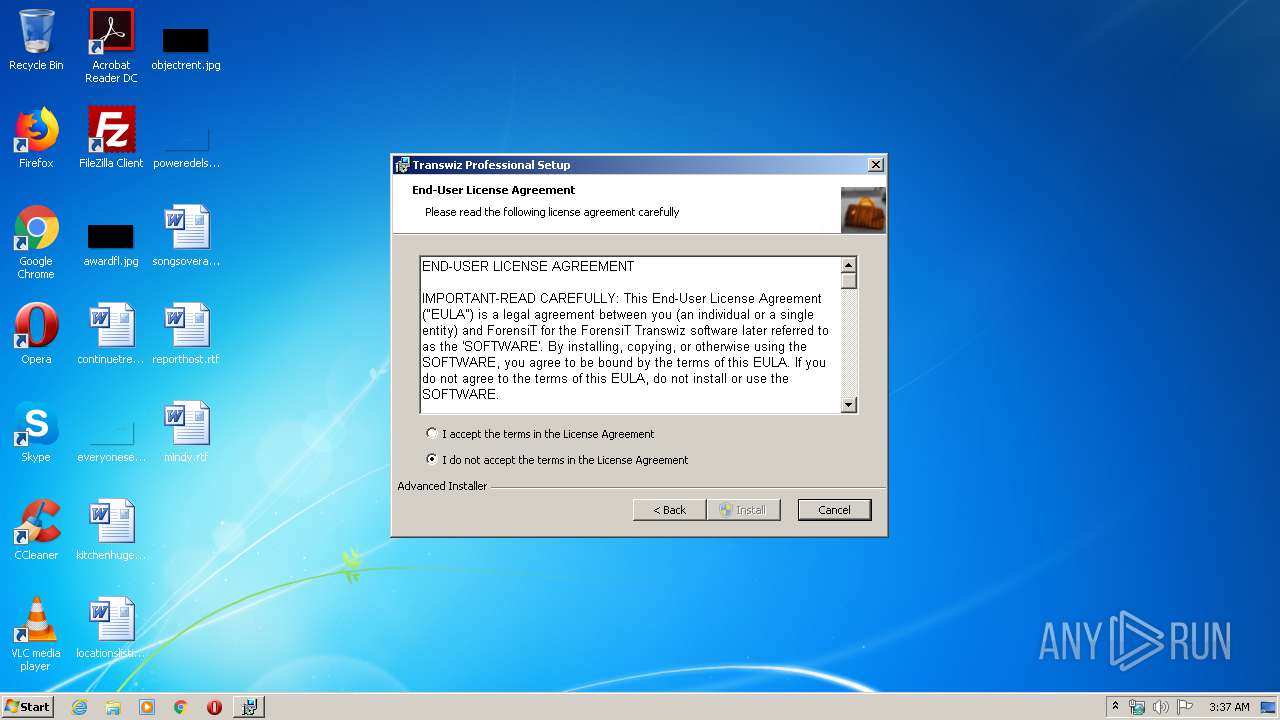
| CompanyName: | ForensiT |
| FileDescription: | Transwiz Professional Installer |
| FileVersion: | 1.17.1094 |
| InternalName: | Transwiz_Pro_1.17.1094_setup |
| LegalCopyright: | Copyright (C) 2019 ForensiT |
| OriginalFileName: | Transwiz_Pro_1.17.1094_setup.exe |
| ProductName: | Transwiz Professional |
| ProductVersion: | 1.17.1094 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Dec-2019 09:36:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ForensiT |
| FileDescription: | Transwiz Professional Installer |
| FileVersion: | 1.17.1094 |
| InternalName: | Transwiz_Pro_1.17.1094_setup |
| LegalCopyright: | Copyright (C) 2019 ForensiT |
| OriginalFileName: | Transwiz_Pro_1.17.1094_setup.exe |
| ProductName: | Transwiz Professional |
| ProductVersion: | 1.17.1094 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Dec-2019 09:36:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0016C84F | 0x0016CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45811 |
.rdata | 0x0016E000 | 0x0005E254 | 0x0005E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59891 |
.data | 0x001CD000 | 0x00006D78 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.04023 |
.rsrc | 0x001D4000 | 0x0001CAA8 | 0x0001CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.38509 |
.reloc | 0x001F1000 | 0x00019240 | 0x00019400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55545 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.20194 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.33479 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.97702 | 42475 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.28257 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.6552 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.1558 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
50
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 988 | C:\Windows\system32\MsiExec.exe -Embedding BF9F8C9124806307857B9799E9555434 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | C:\Windows\system32\MsiExec.exe -Embedding 5F38572046A4B1098EDC3127DFFC7D38 C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
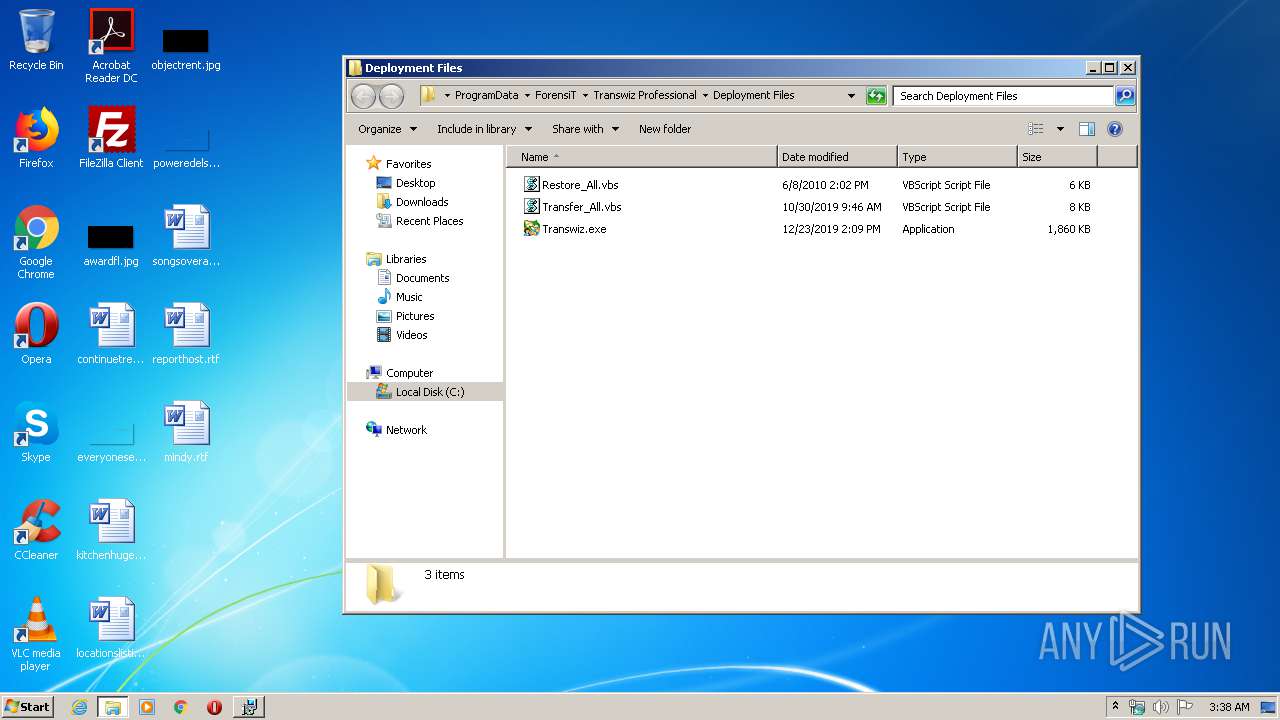
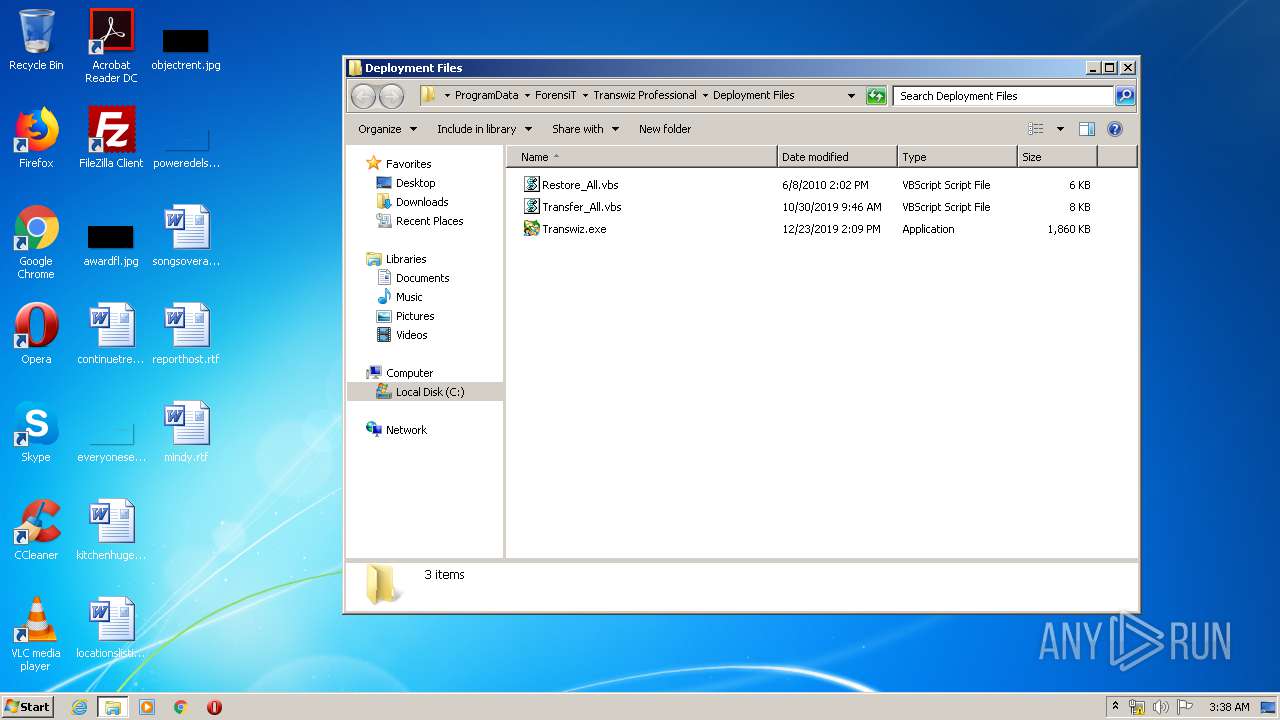
| 1848 | "C:\ProgramData\ForensiT\Transwiz Professional\Deployment Files\Transwiz.exe" | C:\ProgramData\ForensiT\Transwiz Professional\Deployment Files\Transwiz.exe | explorer.exe | ||||||||||||
User: admin Company: ForensiT Limited Integrity Level: HIGH Description: ForensiT Transwiz Exit code: 1 Version: 1.17.1094.0 Modules
| |||||||||||||||
| 1916 | C:\Windows\system32\MsiExec.exe -Embedding F1DE8EDC89B7A0F5321747A8C400290E C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\01940258_2.exe" | C:\Users\admin\AppData\Local\Temp\01940258_2.exe | explorer.exe | ||||||||||||
User: admin Company: ForensiT Integrity Level: MEDIUM Description: Transwiz Professional Installer Exit code: 0 Version: 1.17.1094 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\ForensiT\Transwiz Professional\licfldr.exe" -t | C:\Program Files\ForensiT\Transwiz Professional\licfldr.exe | — | MsiExec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3188 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | "C:\ProgramData\ForensiT\Transwiz Professional\Deployment Files\Transwiz.exe" | C:\ProgramData\ForensiT\Transwiz Professional\Deployment Files\Transwiz.exe | — | explorer.exe | |||||||||||
User: admin Company: ForensiT Limited Integrity Level: MEDIUM Description: ForensiT Transwiz Exit code: 3221226540 Version: 1.17.1094.0 Modules
| |||||||||||||||
| 3824 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\ForensiT\Transwiz Professional 1.17.1094\install\Transwiz Professional.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\01940258_2.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1586388925 " | C:\Windows\system32\msiexec.exe | 01940258_2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 139
Read events
848
Write events
279
Delete events
12
Modification events
| (PID) Process: | (2580) 01940258_2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3824) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000004864DBDE170ED6013C040000640A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000004864DBDE170ED6013C040000640A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (1084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000066E941DF170ED6013C040000640A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1084) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C04B44DF170ED6013C040000A00A0000E8030000010000000000000000000000B072ECFA6414834C91A57368DDA7AF6A0000000000000000 | |||
| (PID) Process: | (3188) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F8E760DF170ED601740C00002C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3188) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F8E760DF170ED601740C0000D40B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3188) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F8E760DF170ED601740C000010010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
6
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | 01940258_2.exe | C:\Users\admin\AppData\Local\Temp\MSIEF4A.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF2C5.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF352.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF372.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF3C2.tmp | — | |
MD5:— | SHA256:— | |||
| 1084 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1084 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFBD40180E49FDEFCE.TMP | — | |
MD5:— | SHA256:— | |||
| 1084 | msiexec.exe | C:\Windows\Installer\MSI51FE.tmp | — | |
MD5:— | SHA256:— | |||
| 1084 | msiexec.exe | C:\Windows\Installer\MSI52BB.tmp | — | |
MD5:— | SHA256:— | |||
| 3188 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
01940258_2.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\01940258_2.exe] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIEF4A.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIF2C5.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIF352.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIF372.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIF3C2.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSI4FE8.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSI51FE.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSI52BB.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIC03A.tmp] CPU: __isa_available = 5
|