| URL: | https://2z3c99ry.r.us-east-1.awstrack.me/L0/https:%2F%2Fmy.engage.bz%2Flogin%2F%3FcustomerId=novonor/1/0100018d3c17ecea-61c90f7e-12ae-444e-9a0c-d7087545a205-000000/YjE_7rA91obSkf8y1TUP6kKjaIA=358 |
| Full analysis: | https://app.any.run/tasks/987fdcdc-831a-4a94-989a-da1b662a3e78 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2024, 18:58:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 284DDDCCA7DAD9A5FCACEFFBE3E1C668 |
| SHA1: | 44810097A92F979F3D957AE56F68CE8271C3039E |
| SHA256: | 6731C253ABD86BFF0CB6A3F2AD27DFE407434DBBD79D116A0F5347A542850E6F |
| SSDEEP: | 6:2DtMjfoHTdhljvWu0ThcWgdUjR/TaJgfgnwI:2DGT2ZPjvL0ThcWgdUjR7fgH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msdt.exe (PID: 3400)
Reads settings of System Certificates
- msdt.exe (PID: 3400)
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 2248)
Reads the Internet Settings
- sdiagnhost.exe (PID: 2248)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 2248)
INFO
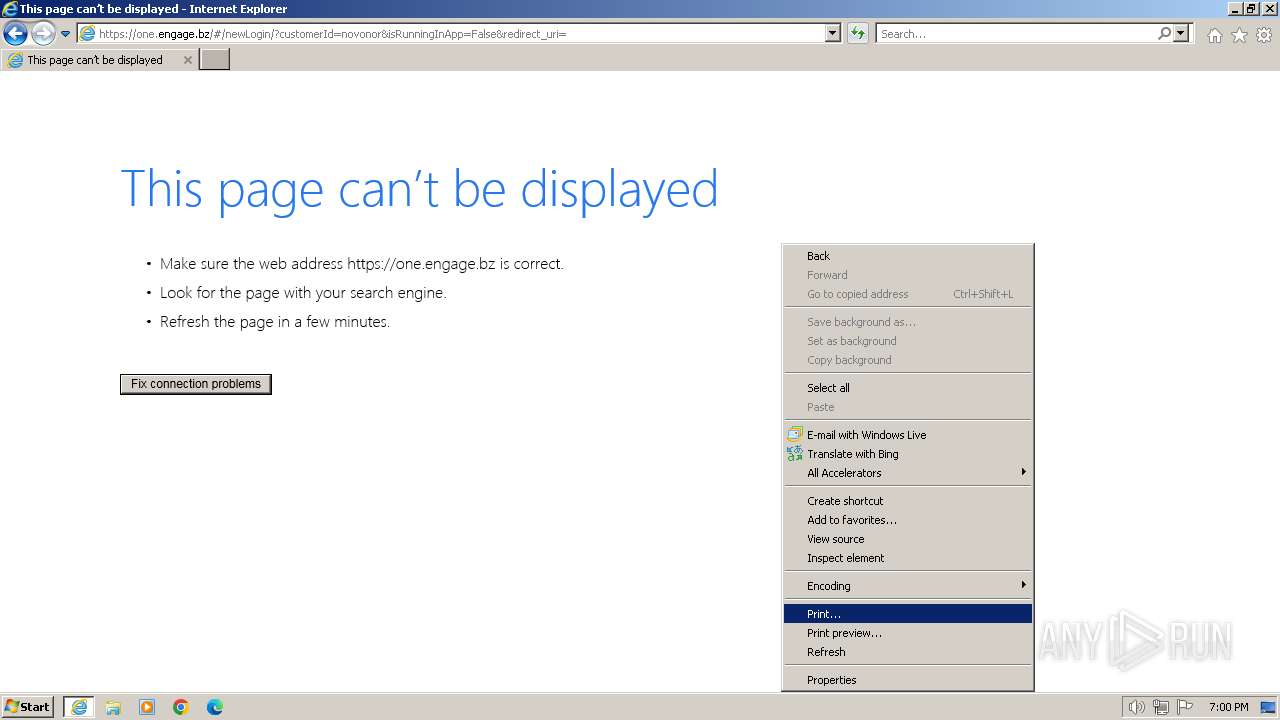
Application launched itself
- iexplore.exe (PID: 2640)
Drops the executable file immediately after the start
- msdt.exe (PID: 3400)
Create files in a temporary directory
- msdt.exe (PID: 3400)
- sdiagnhost.exe (PID: 2248)
- makecab.exe (PID: 3112)
Reads security settings of Internet Explorer
- msdt.exe (PID: 3400)
- sdiagnhost.exe (PID: 2248)
Creates files or folders in the user directory
- msdt.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2248 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2640 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://2z3c99ry.r.us-east-1.awstrack.me/L0/https:%2F%2Fmy.engage.bz%2Flogin%2F%3FcustomerId=novonor/1/0100018d3c17ecea-61c90f7e-12ae-444e-9a0c-d7087545a205-000000/YjE_7rA91obSkf8y1TUP6kKjaIA=358" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3032 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3400 | -modal 852342 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDFC765.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 741
Read events
20 639
Write events
96
Delete events
6
Modification events
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
47
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2640 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2640 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:5798C2D5EA672F9AEC56E698ADABAB84 | SHA256:7BB19AC76B290549B13FA934AC44357C0383EEBA049E3627F196E45F5BBE8952 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:EA34894ED94D8B2D21E813B0AEEA1F85 | SHA256:073287D8CB7593DC16CACF592CE7F0A5C802E46513A7622C6FF3664220C6949B | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:4BBA5BE95F567C442A7AB471F3AF4A1B | SHA256:0BF0B4497895AFA405D6F4266FF2F88F055754E4BFF469C56754766E507E2FD1 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:DC5997A0ED29BFD58FA354A377166681 | SHA256:F237DBE872B6613FFA00EDD0B84B1CA8FC4C5CC563B52131C047B359E5C070F9 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F53EB4E574DE32C870452087D92DBEBB_5AD7BA168583E2EA5A5F741E887096C2 | binary | |
MD5:3A7463D7B04D928056EB69213E57AAF5 | SHA256:A905AD1C1925D1A1A1C68FFA28059944BE95A8FB0F4EEE1700F5300E15F55B12 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:D2C2F112DF6FF6AC06399F72EC0F52D9 | SHA256:3CA485AF8E7AB81435D347F713E53FECAC3C879402134B278106FBCF1A9EEB4C | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F53EB4E574DE32C870452087D92DBEBB_5AD7BA168583E2EA5A5F741E887096C2 | binary | |
MD5:ADD0CB07A7C68645669A7615AAAF8DC2 | SHA256:2F08E6524B547C82678B99B043DFA501EB32135EF0C79B1D3875F296CCC4CCC5 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D03E46CD585BBE111C712E6577BC5F07_432CB52BF49B6B0106A45314A7E9FD8E | binary | |
MD5:FDF5B5A674F34E2D472BA0FE03A9D7ED | SHA256:72DC44EFCFCD12C6688D766120D453C725E4C0AA74E87E4656DE6B5A904182C5 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | der | |
MD5:2BC82B85886840089D2162D6742F73C1 | SHA256:49E439CD5870128ACF77D1017F748AEA8FF88A48278682E1F78D5FA871A92154 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
37
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | iexplore.exe | GET | 304 | 23.48.23.7:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1012f9097c4a32e9 | unknown | — | — | unknown |
2640 | iexplore.exe | GET | 304 | 23.48.23.7:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a071a3cff9a7a2a1 | unknown | — | — | unknown |
2588 | iexplore.exe | GET | 200 | 18.165.185.4:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
2640 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
2588 | iexplore.exe | GET | 200 | 18.165.184.219:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | binary | 1.37 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 18.165.184.219:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.49 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 18.165.184.219:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | binary | 1.37 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 18.165.189.160:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAsyeFobanz%2BMyE76aDoppc%3D | unknown | binary | 471 b | unknown |
2588 | iexplore.exe | GET | 200 | 13.32.26.76:80 | http://ocsp.r2m01.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBShdVEFnSEQ0gG5CBtzM48cPMe9XwQUgbgOY4qJEhjl%2Bjs7UJWf5uWQE4UCEA0j6ZLc75YOYfL1s112jco%3D | unknown | binary | 471 b | unknown |
2640 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | iexplore.exe | 52.44.155.103:443 | 2z3c99ry.r.us-east-1.awstrack.me | AMAZON-AES | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2640 | iexplore.exe | 104.126.37.179:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2640 | iexplore.exe | 23.48.23.7:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2640 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2588 | iexplore.exe | 18.165.185.4:80 | o.ss2.us | — | US | unknown |
2588 | iexplore.exe | 18.165.184.219:80 | ocsp.rootg2.amazontrust.com | — | US | unknown |
2588 | iexplore.exe | 18.165.189.160:80 | ocsp.r2m02.amazontrust.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2z3c99ry.r.us-east-1.awstrack.me |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m02.amazontrust.com |
| whitelisted |
my.engage.bz |
| unknown |