| download: | invce2139 |
| Full analysis: | https://app.any.run/tasks/438a8baf-d7cb-4377-9b4f-80b55dc119ff |
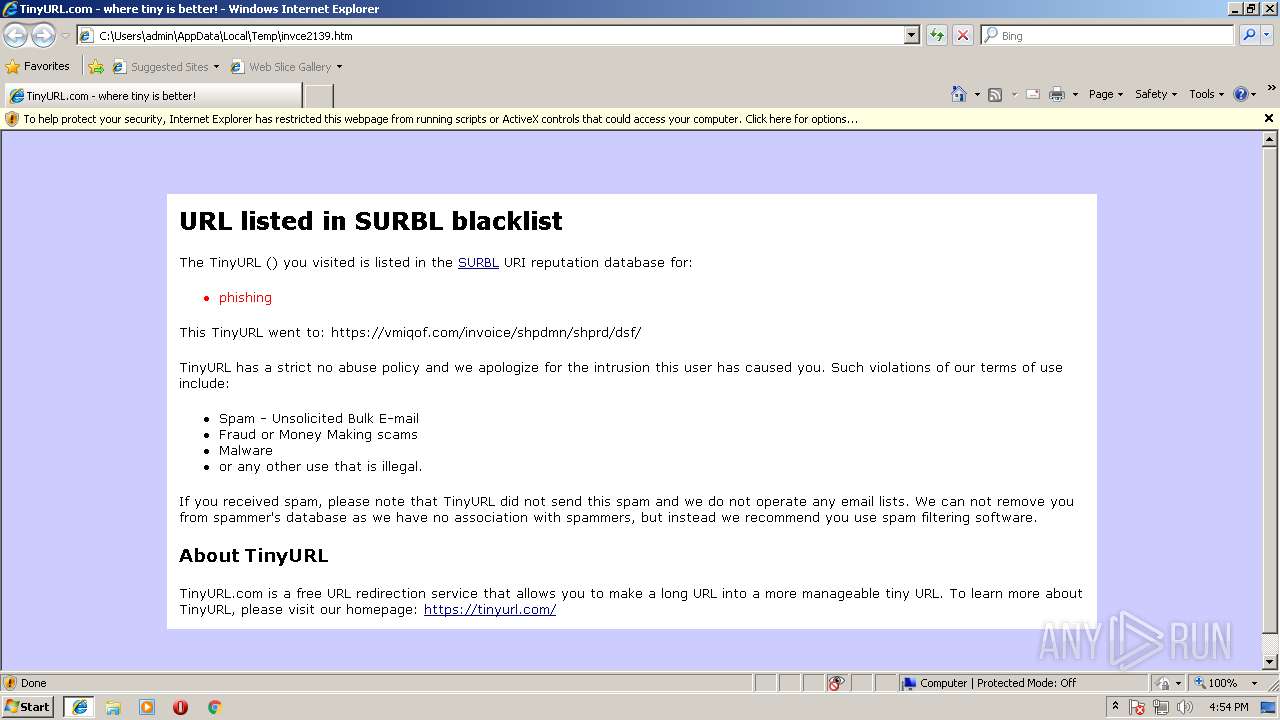
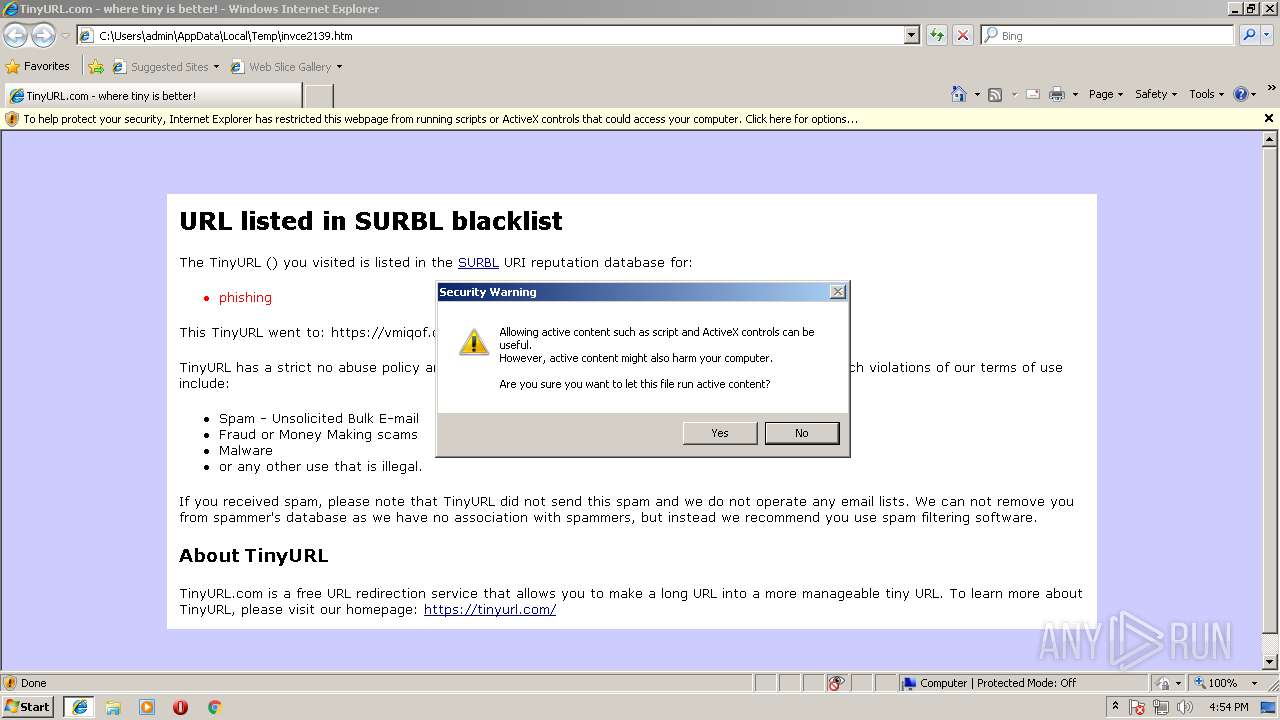
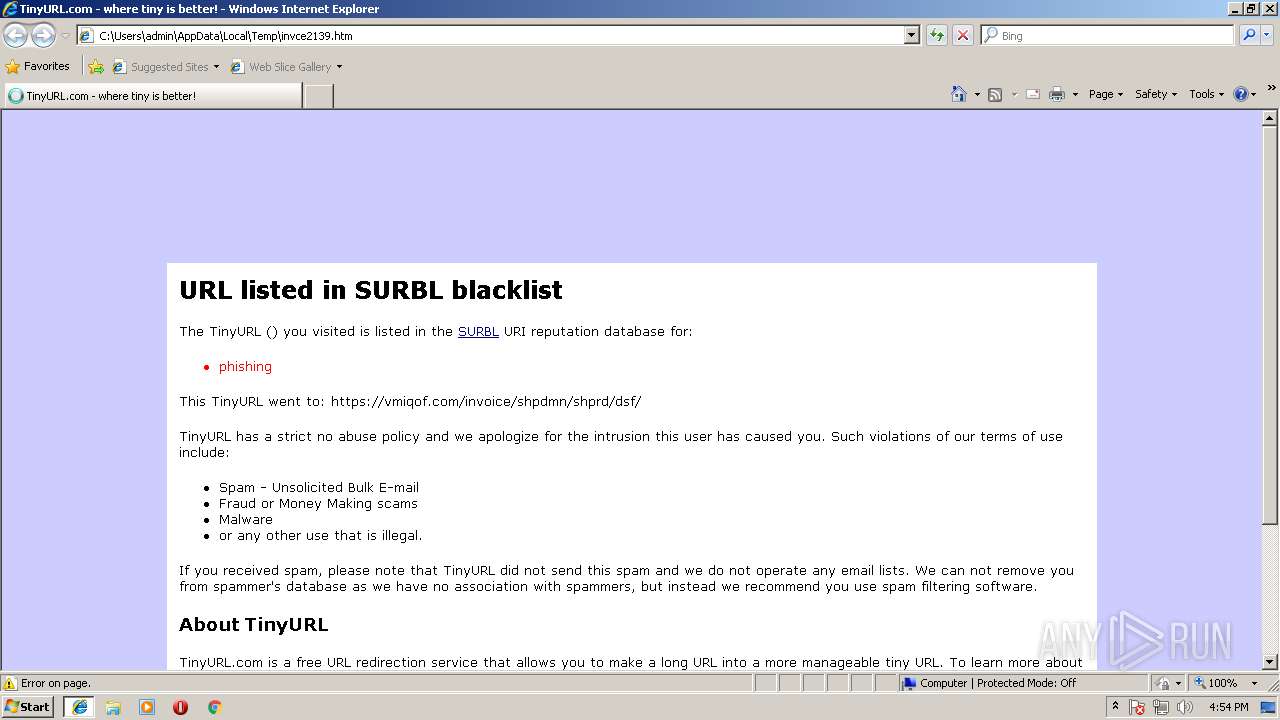
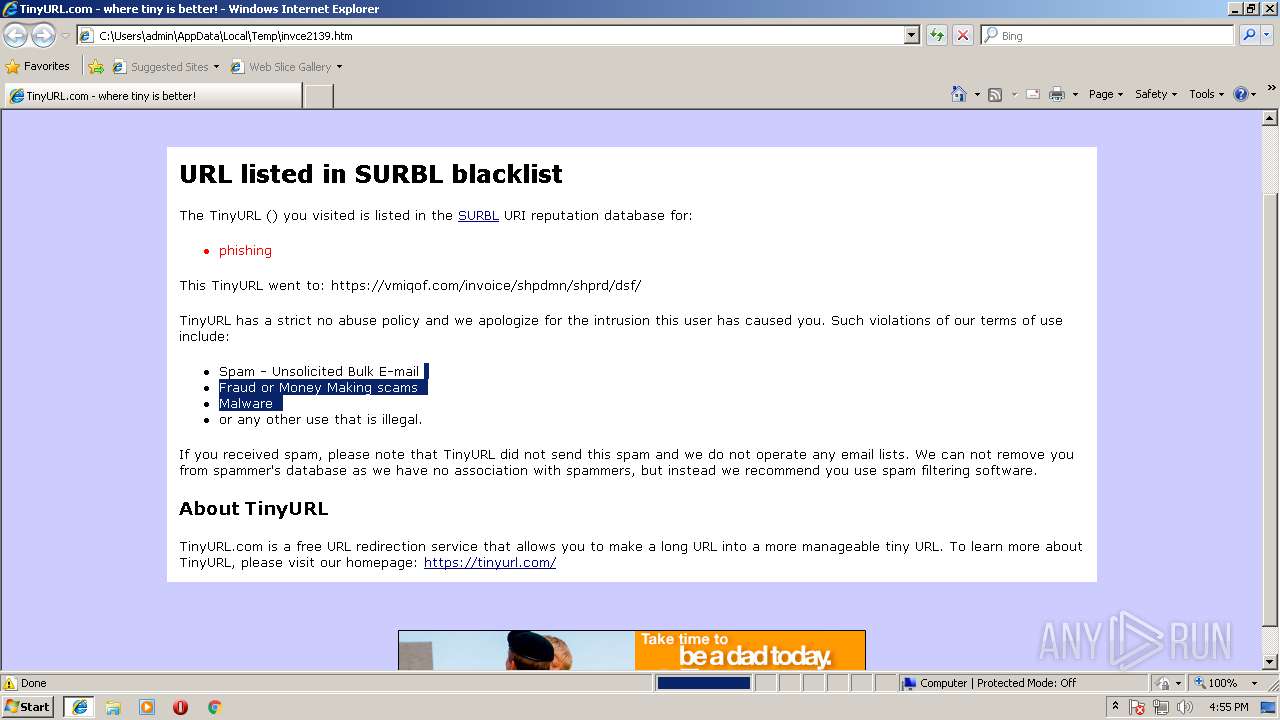
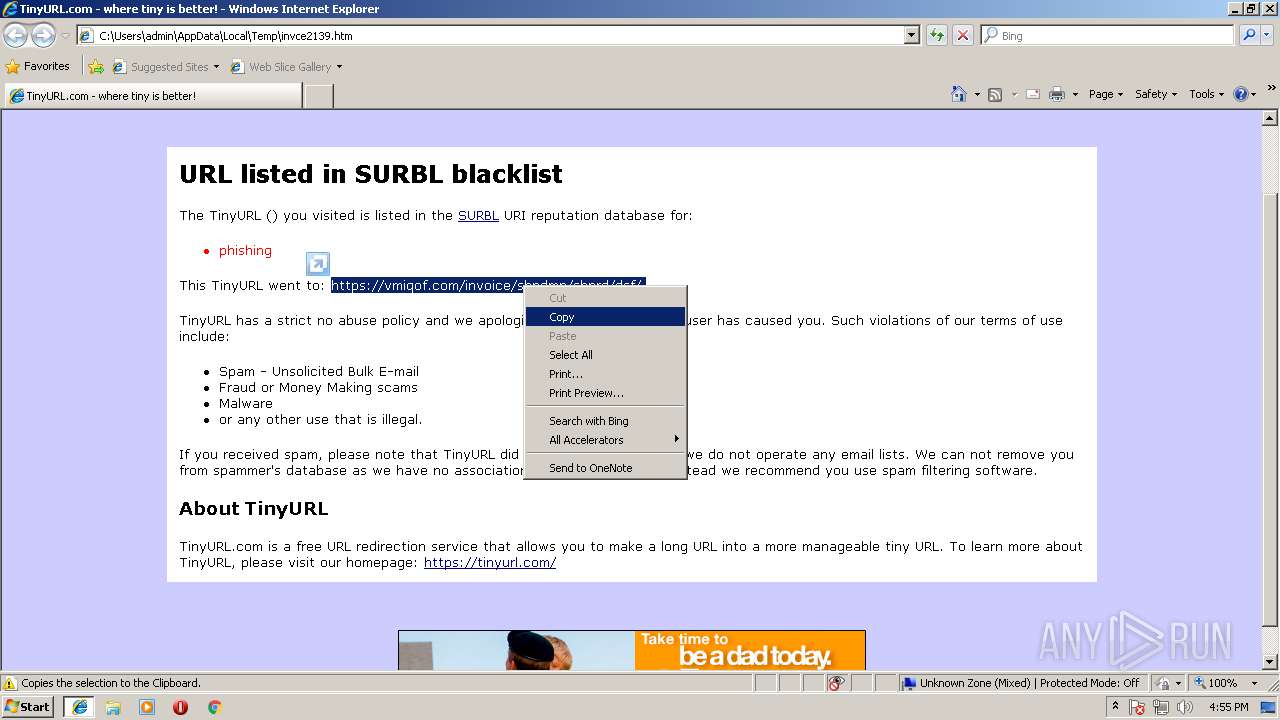
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2018, 15:54:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | D9AD7B8D96224A2A470714DC65064EE7 |
| SHA1: | 8A16DB442899FE7508663E5F01045CCE3C927467 |
| SHA256: | 672638F137E81FBBD82B93FE71FC875ED5EF7A0FBCDD513BEAC78CF0F626F641 |
| SSDEEP: | 96:t+J3JFDjLhx5u8Veqzcm8uFFZKbJcSBcQufaAKb6QuAzaYI:t255jLhxg8Vemcm8uFnYJhBcfaAYjuyI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1224)
Reads internet explorer settings
- iexplore.exe (PID: 1272)
Reads settings of System Certificates
- iexplore.exe (PID: 1272)
Changes internet zones settings
- iexplore.exe (PID: 1224)
Reads Internet Cache Settings
- iexplore.exe (PID: 1224)
- iexplore.exe (PID: 1272)
Dropped object may contain URL's
- iexplore.exe (PID: 1272)
Creates files in the user directory
- iexplore.exe (PID: 1272)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1272)
Changes settings of System certificates
- iexplore.exe (PID: 1272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| Title: | TinyURL.com - where tiny is better! |
|---|
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1224 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\invce2139.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1224 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
434
Read events
343
Write events
88
Delete events
3
Modification events
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {2D44B77F-AD36-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (1224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207080005001F000F0036002C00A502 | |||
Executable files
0
Suspicious files
4
Text files
56
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1224 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab6475.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar6476.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab6486.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar6487.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab64E6.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar64F7.tmp | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[2].txt | — | |
MD5:— | SHA256:— | |||
| 1272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\displayAd[1].js | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
43
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1272 | iexplore.exe | GET | 200 | 18.197.5.180:80 | http://edge.quantserve.com/quant.js | DE | text | 5.33 Kb | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/displayAd.js?dver=0.8&th=6263147382 | US | text | 331 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/p.media?clickID=a0mQ8ypdeo3mQV5VQdTGJ9VV7fSPJyWdZb5WFj15bExVE3xVEJ9Pa3IQcjBRrixPWvcWVbV2UenmtaOXqmN3WvESsZbG2mBImdayUtfhXrfcXFj7XaZanRFnGWU3SVWrYobBmPbrmXann4EBh4TYRmEMC1rZbfUtM1oAQInsQooW3J3aZbf2dAm3PjJmFQZb0sr01bYjueXoAP&mediaDataID=5207316&mediaName=frame.html | US | html | 443 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/real/tags/TinyURLcom/ROS/tags.js | US | text | 13.5 Kb | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/p.media?clickID=aPmQ8y0q2p4tUAPG7A4PJJpdaOTdfb0b7i1bJeXaiNSUvZdUFB5WHU0oFjuRU7y1T3s5TUj2qfXmEjIYrZbaTt7SomMZapGfrmHUJ2ar73dms4PZbEpr3IXcQQ1cYV0cFOpEfU3bFRWbFDVPr1Pq3QQsZbtStZbr1HvxT63M3sZb3YbvDTPio5AMcRmfF3dvsXd3ApaAJMjvhWe&mediaDataID=5578346&mediaName=frame.html | US | html | 229 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/p.media?clickID=aTmQgM4WvO0H3CnHim3PUY4VYeTsM7VsM6PAJwUWFWWFB25rEuVqQoWqF6SEBZaQGYIPbevRdfkWGMW2FmnnHIqXEax4WbZbPsrD2mMJmdAyTWfc0rf6XUZbj0TqsPb3CTFJ1VHUWnbbsQrZbtXqYo3TZba4q7XoT7I1FUaTWBUnP7ZapGrwoHQF2TFe2HZap56rZbprbOp5IRVc&mediaDataID=6546596&mediaName=frame.html | US | html | 288 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 2.18.234.175:80 | http://cdnx.tribalfusion.com/media/5268466/468.jpeg | unknown | image | 18.0 Kb | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/p.media?clickID=aRmQgMmH3J3TYh5HuM4mjGmrUGYcQPXsFTXVrvnavT5bvPTUfZcVA35Qaf4SVZbqSd3O1dfuVAjn2cY30U3JUPPn46B6QmMI3dZbmXWrZcpdEo56vT3cjaUc39WVMfPPQMTtZbUUF7P2rerVTUmWaU7STYFSGQIRravPt76VsQQ5resod6OXqPO3tjGPsJB4PFZamdXHquZdbE4&mediaDataID=7665496&mediaName=frame.html | US | html | 178 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/j.ad?flashVer=9&ver=1.28&th=6263147382&tagKey=2439653603&loaderVer=0.1&site=tinyurlcom&adSpace=ros¢er=1&json=1&callback=e9Manager.setSingleAdResponse&env=display&size=728x90,468x60&busted=1&url=file%3A%2F%2F%2FC%3A%2FUsers%2Fadmin%2FAppData%2FLocal%2FTemp%2Finvce2139.htm&f=0&p=10841000&tKey=a4mneMnr3IYV7SXVv10croMdbbVtZbrk6&a=3&adContainerId=richmedia_4&rnd=10850672 | US | html | 3.51 Kb | whitelisted |
1272 | iexplore.exe | GET | 200 | 204.11.109.65:80 | http://a.tribalfusion.com/p.media?clickID=aVmQgMSGBZa46QZbpHZanUdFhYFb9Yrbi1qqOPrFFUbBYTHr1obJxQUJrXaJp3EUj2qfXmEjIYU3hUWbPoAvLmc3notbG3aZb92Hmn3AZbIprMEXGQW1sFX1GjOnavU5UQSWUvGWmMTQTQ2PGrqPHJxYt7uVmbv4s3U0bZbZcUmqu5PnbR6fK2Wrp1HJJmW6O5AZbR3sjQsK6CJf&mediaDataID=6719746&mediaName=frame.html | US | html | 319 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1272 | iexplore.exe | 157.240.20.38:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
1272 | iexplore.exe | 18.184.254.112:443 | pixel.quantserve.com | — | US | unknown |
1272 | iexplore.exe | 204.11.109.75:80 | tags.expo9.exponential.com | Exponential Interactive, Inc. | US | unknown |
1272 | iexplore.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1272 | iexplore.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
1272 | iexplore.exe | 108.177.126.157:80 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
1272 | iexplore.exe | 18.197.5.180:80 | edge.quantserve.com | Amazon.com, Inc. | DE | unknown |
1272 | iexplore.exe | 204.11.109.65:80 | a.tribalfusion.com | Exponential Interactive, Inc. | US | unknown |
4 | System | 54.230.93.252:445 | rules.quantcount.com | Amazon.com, Inc. | US | unknown |
4 | System | 54.230.93.131:445 | rules.quantcount.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tags.expo9.exponential.com |
| whitelisted |
www.facebook.com |
| whitelisted |
pixel.quantserve.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
a.tribalfusion.com |
| whitelisted |
edge.quantserve.com |
| whitelisted |
rules.quantcount.com |
| whitelisted |