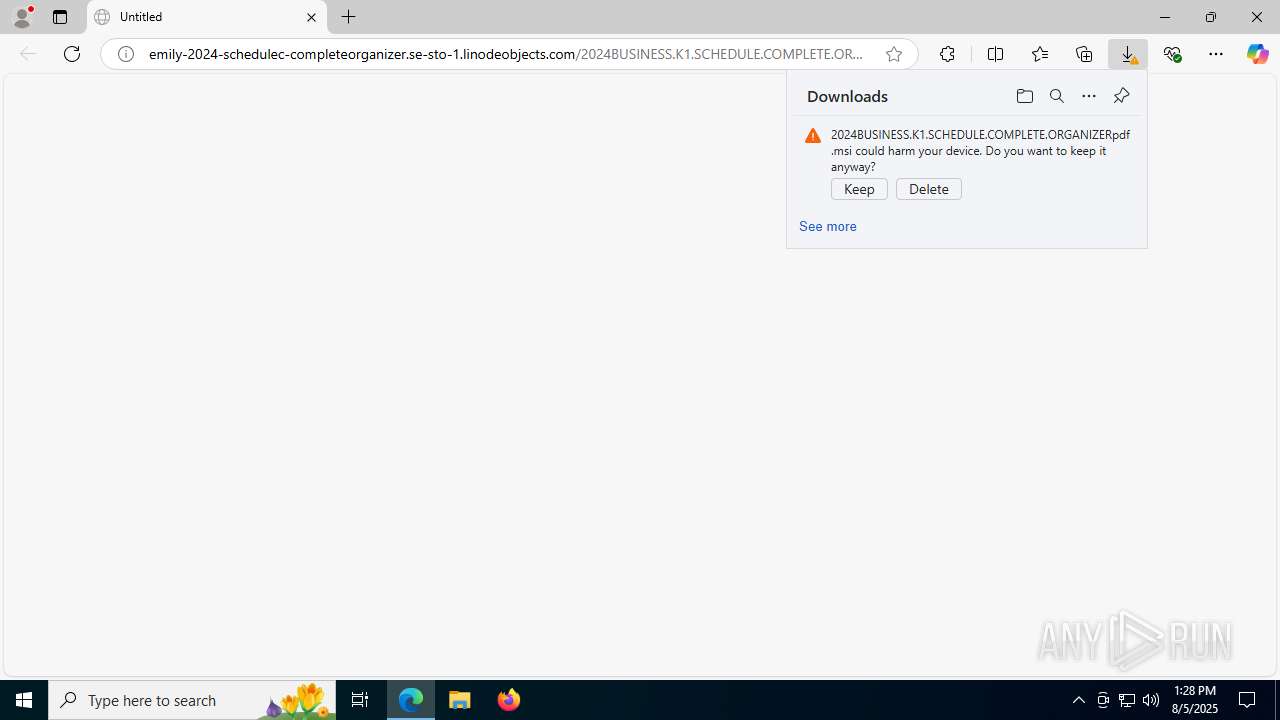
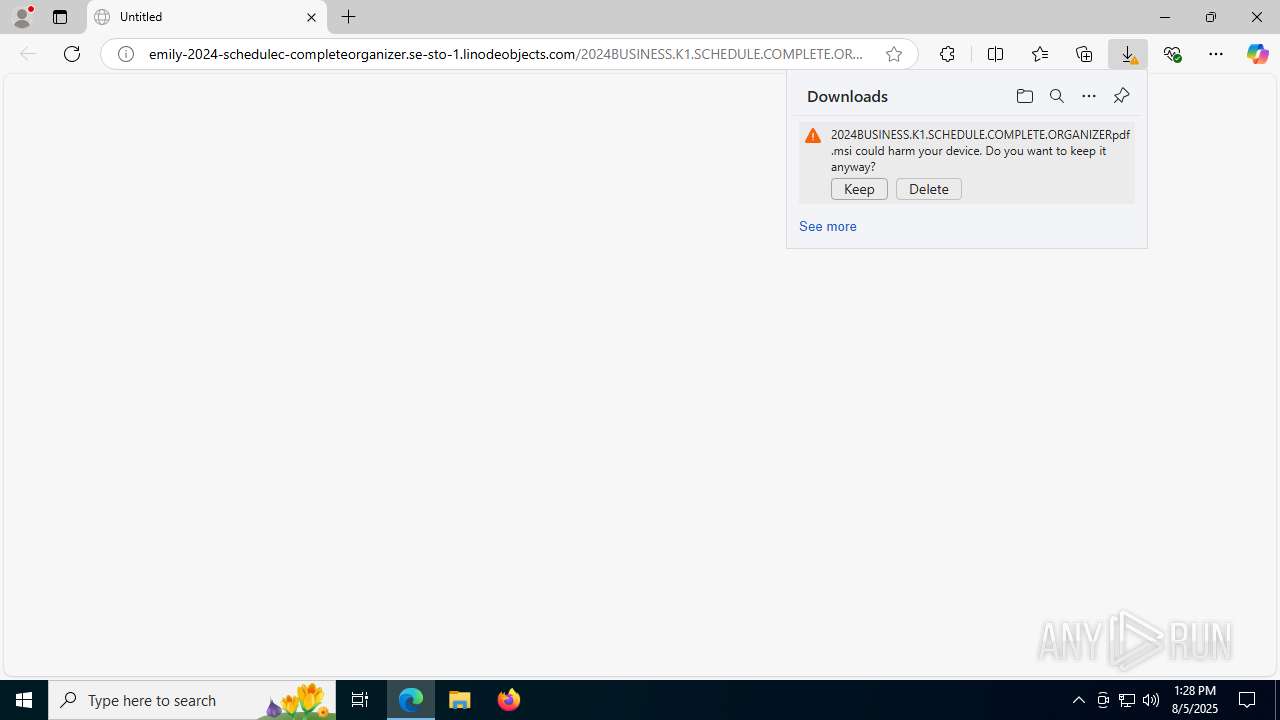
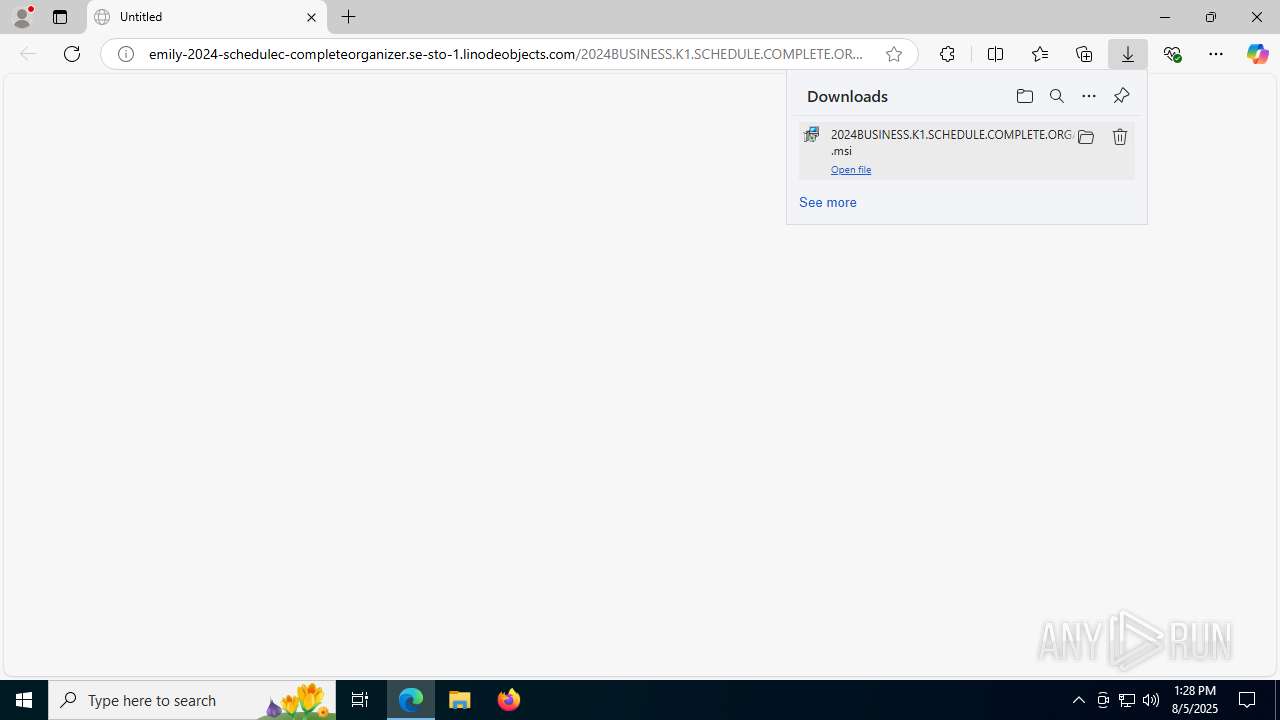
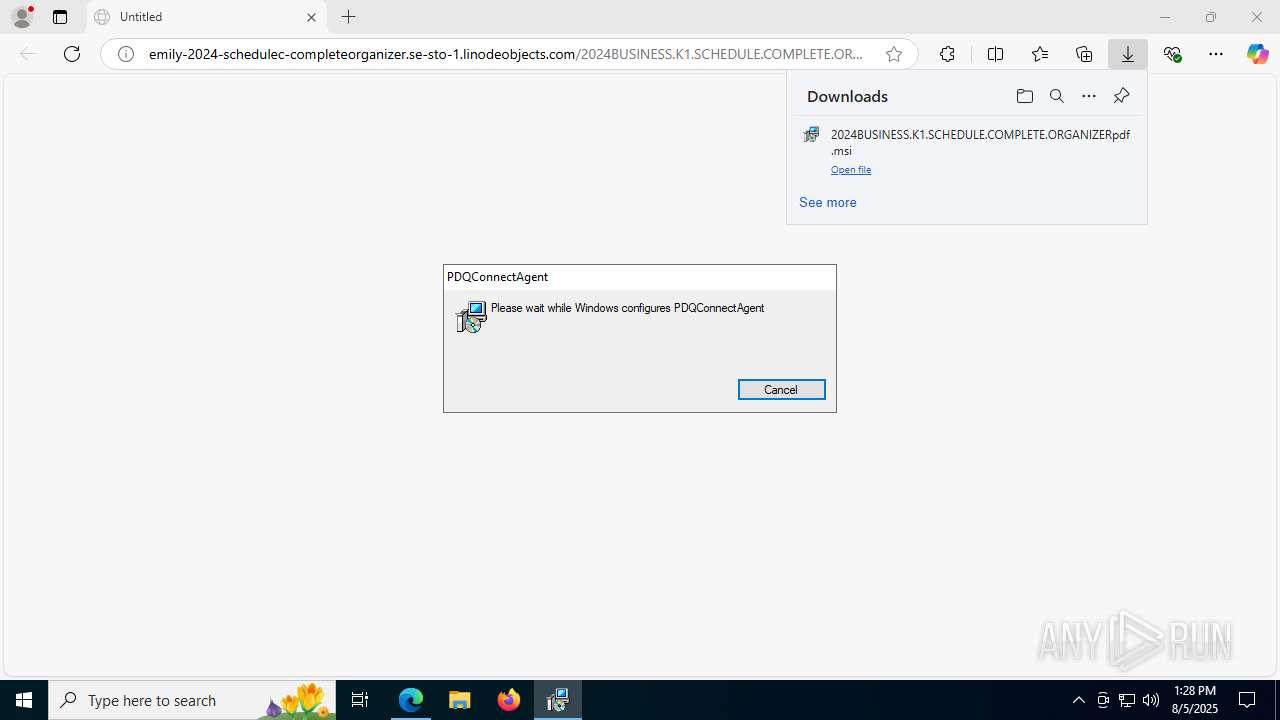
| URL: | emily-2024-schedulec-completeorganizer.se-sto-1.linodeobjects.com/2024BUSINESS.K1.SCHEDULE.COMPLETE.ORGANIZERpdf.msi |
| Full analysis: | https://app.any.run/tasks/184fa3e0-279d-4ad1-a5f0-68a3b866a70a |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2025, 13:28:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 12D7A487EFFAEF9D0C0947416D94A9F3 |
| SHA1: | 7E940A0409E0C24B5D810350A9076B5D04969035 |
| SHA256: | 6726340AB5A0D706EE8C00825F05B40D78BFCE2A9A8FDA9DF9D26E29F467F8BF |
| SSDEEP: | 3:tMJtDfGZJU3LfXhCHlMGGjU8OdZxF3iHWYLn:KGC37C0hO373iLL |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5244)
- powershell.exe (PID: 6508)
- powershell.exe (PID: 7888)
- powershell.exe (PID: 2704)
- powershell.exe (PID: 3392)
- powershell.exe (PID: 440)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6936)
- powershell.exe (PID: 3688)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 6620)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 4576)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 4864)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 3480)
- powershell.exe (PID: 1528)
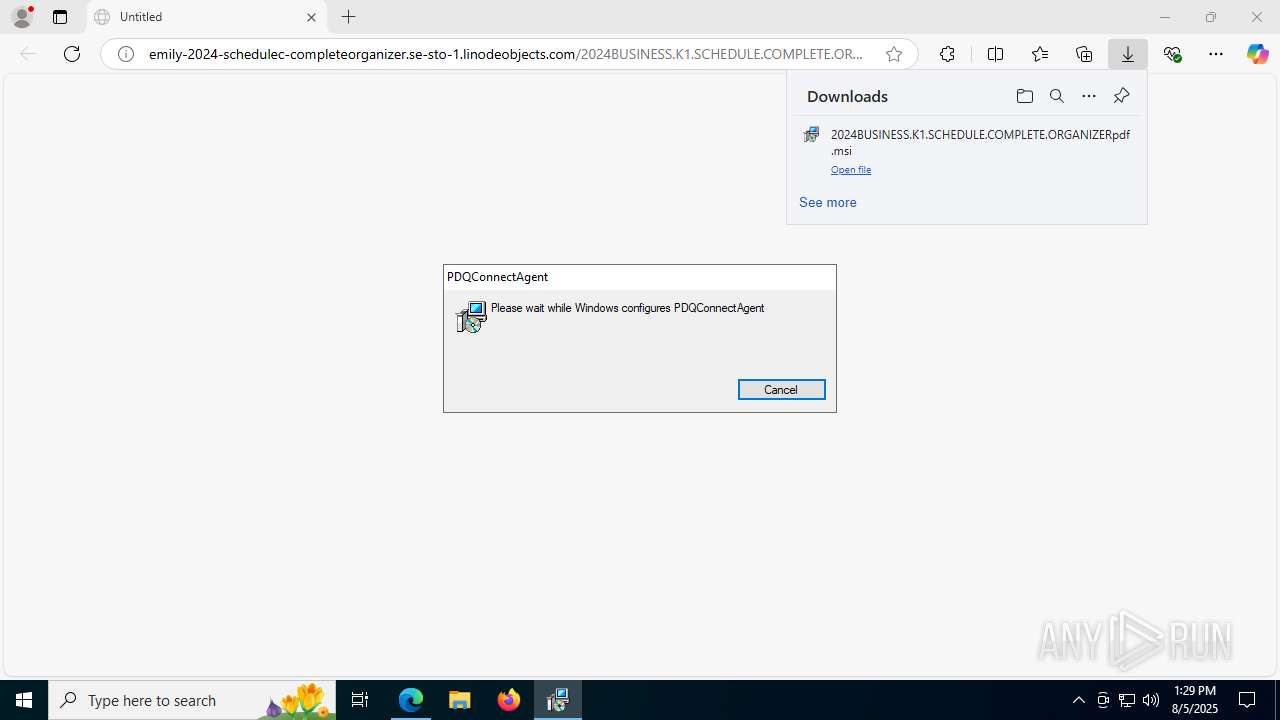
Changes powershell execution policy (Bypass)
- pdq-connect-agent.exe (PID: 7412)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6648)
Application launched itself
- msiexec.exe (PID: 6648)
- powershell.exe (PID: 3480)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 5528)
- msiexec.exe (PID: 1096)
- msiexec.exe (PID: 1524)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 2232)
Executes as Windows Service
- VSSVC.exe (PID: 7544)
- pdq-connect-updater.exe (PID: 7860)
- pdq-connect-agent.exe (PID: 7412)
- WmiApSrv.exe (PID: 6536)
Executable content was dropped or overwritten
- rundll32.exe (PID: 8004)
- rundll32.exe (PID: 7172)
- rundll32.exe (PID: 8056)
- rundll32.exe (PID: 7052)
- rundll32.exe (PID: 4308)
- pdq-connect-agent.exe (PID: 7412)
- rundll32.exe (PID: 1040)
- rundll32.exe (PID: 7556)
- rundll32.exe (PID: 7052)
- rundll32.exe (PID: 6312)
- rundll32.exe (PID: 6620)
- rundll32.exe (PID: 7352)
- rundll32.exe (PID: 5060)
- csc.exe (PID: 1944)
- powershell.exe (PID: 3576)
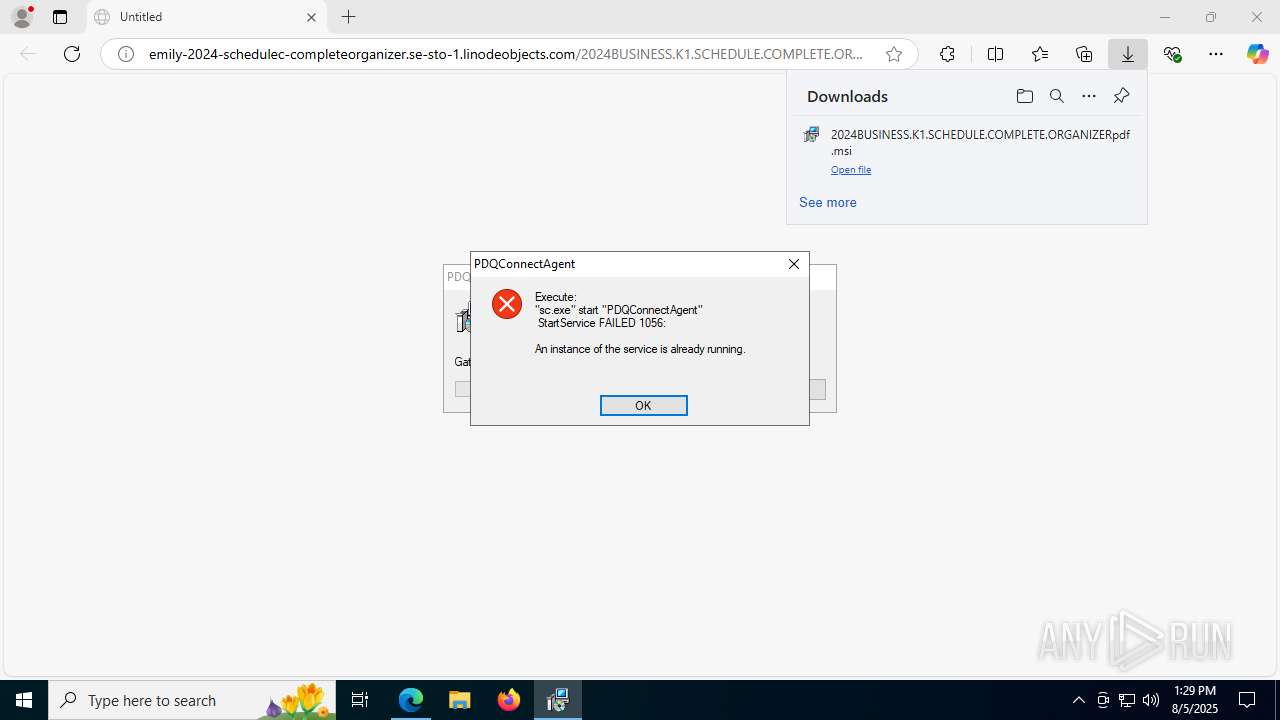
Starts SC.EXE for service management
- rundll32.exe (PID: 7052)
- rundll32.exe (PID: 7352)
Windows service management via SC.EXE
- sc.exe (PID: 2232)
- sc.exe (PID: 7500)
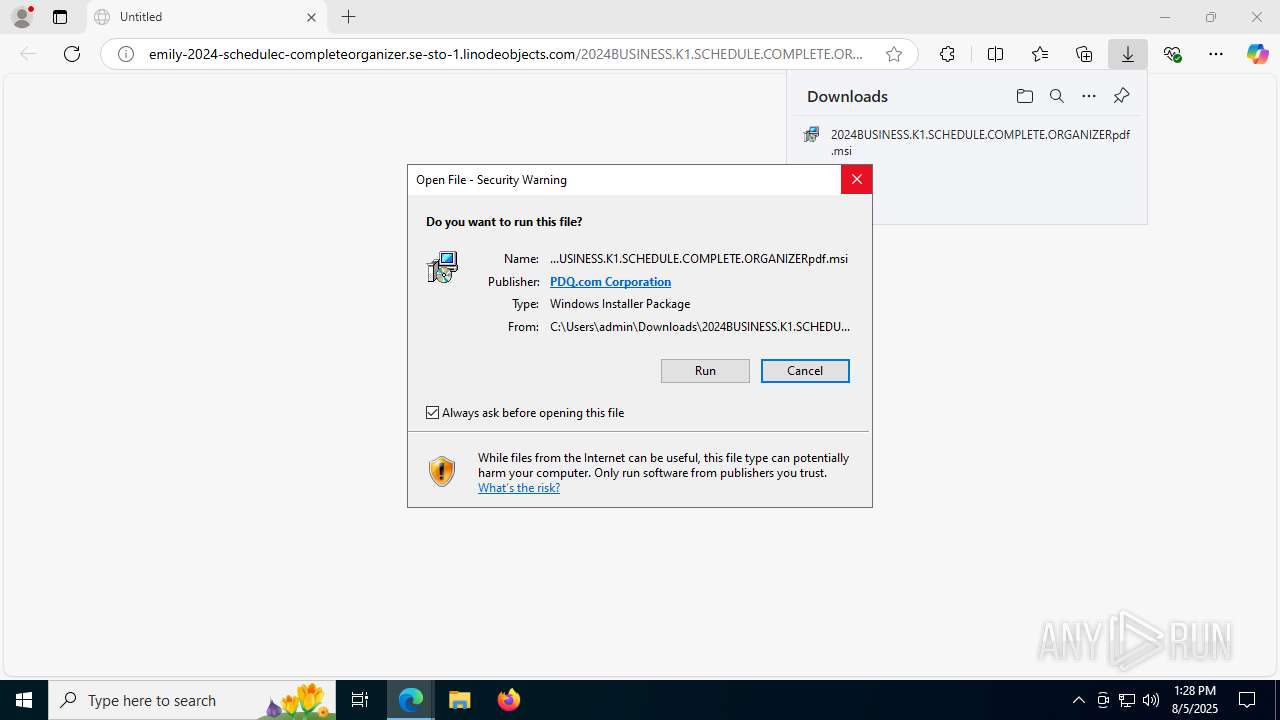
PDQConnect is probably used for system patching and software deployment
- sc.exe (PID: 2232)
- sc.exe (PID: 7500)
The process bypasses the loading of PowerShell profile settings
- pdq-connect-agent.exe (PID: 7412)
- powershell.exe (PID: 3480)
The process hide an interactive prompt from the user
- pdq-connect-agent.exe (PID: 7412)
The process hides Powershell's copyright startup banner
- pdq-connect-agent.exe (PID: 7412)
- powershell.exe (PID: 3480)
Starts POWERSHELL.EXE for commands execution
- pdq-connect-agent.exe (PID: 7412)
- powershell.exe (PID: 3480)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 3576)
CSC.EXE is used to compile C# code
- csc.exe (PID: 1944)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 3576)
The process creates files with name similar to system file names
- powershell.exe (PID: 3576)
Process drops legitimate windows executable
- powershell.exe (PID: 3576)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 4676)
INFO
Application launched itself
- msedge.exe (PID: 32)
Checks supported languages
- identity_helper.exe (PID: 7736)
- msiexec.exe (PID: 6648)
- msiexec.exe (PID: 5528)
- msiexec.exe (PID: 1096)
- msiexec.exe (PID: 1524)
- pdq-connect-updater.exe (PID: 7860)
- pdq-connect-agent.exe (PID: 7412)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 2232)
- csc.exe (PID: 1944)
- cvtres.exe (PID: 7508)
- DismHost.exe (PID: 4676)
Reads the computer name
- identity_helper.exe (PID: 7736)
- msiexec.exe (PID: 6648)
- msiexec.exe (PID: 5528)
- msiexec.exe (PID: 1096)
- pdq-connect-agent.exe (PID: 7412)
- msiexec.exe (PID: 1524)
- pdq-connect-updater.exe (PID: 7860)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 2232)
- DismHost.exe (PID: 4676)
Reads Environment values
- identity_helper.exe (PID: 7736)
- pdq-connect-agent.exe (PID: 7412)
- DismHost.exe (PID: 4676)
Manages system restore points
- SrTasks.exe (PID: 7904)
Reads the software policy settings
- msiexec.exe (PID: 6648)
- msiexec.exe (PID: 1660)
- pdq-connect-agent.exe (PID: 7412)
- pdq-connect-updater.exe (PID: 7860)
- slui.exe (PID: 6228)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1660)
Reads Microsoft Office registry keys
- msedge.exe (PID: 32)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6648)
- csc.exe (PID: 1944)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6648)
Create files in a temporary directory
- rundll32.exe (PID: 8004)
- rundll32.exe (PID: 7172)
- rundll32.exe (PID: 6312)
- rundll32.exe (PID: 7052)
- msiexec.exe (PID: 7680)
The sample compiled with english language support
- msiexec.exe (PID: 6648)
- powershell.exe (PID: 3576)
PDQCONNECT has been detected
- msiexec.exe (PID: 1096)
- rundll32.exe (PID: 7052)
- pdq-connect-agent.exe (PID: 7412)
- msiexec.exe (PID: 2232)
- rundll32.exe (PID: 7352)
Creates files in the program directory
- rundll32.exe (PID: 4308)
- msiexec.exe (PID: 6620)
- pdq-connect-agent.exe (PID: 7412)
Creates a software uninstall entry
- msiexec.exe (PID: 6648)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 8420)
Process checks computer location settings
- pdq-connect-agent.exe (PID: 7412)
Application based on Rust
- pdq-connect-agent.exe (PID: 7412)
- pdq-connect-updater.exe (PID: 7860)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7636)
Reads Windows Product ID
- powershell.exe (PID: 3576)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 8316)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3576)
Checks proxy server information
- slui.exe (PID: 6228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
133
Malicious processes
5
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "emily-2024-schedulec-completeorganizer.se-sto-1.linodeobjects.com/2024BUSINESS.K1.SCHEDULE.COMPLETE.ORGANIZERpdf.msi" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 440 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43c5f208,0x7ffc43c5f214,0x7ffc43c5f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Version 5.1 -s -NoLogo -NoProfile | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | rundll32.exe "C:\WINDOWS\Installer\MSI3E14.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1654375 61 WixSharp!WixSharp.ManagedProjectActions.WixSharp_InitRuntime_Action | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
208 545
Read events
208 112
Write events
391
Delete events
42
Modification events
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC5FF87A349A2F00 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F88793C5-9CCA-4CB9-958C-0FC60A77492A} | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {99CF74CD-2E4E-49DF-9F1D-42CD51CD9E48} | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EB160F7B349A2F00 | |||
| (PID) Process: | (32) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
113
Suspicious files
276
Text files
207
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d107.TMP | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d107.TMP | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d116.TMP | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d107.TMP | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d145.TMP | — | |
MD5:— | SHA256:— | |||
| 32 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
77
DNS requests
70
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:wCIL-pTbL49-MEGRM5cOgQrxpj6oqoAudQuXdy3Zees&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7116 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
32 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
32 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEA5NZ%2FZDFskqO3oXzEaXao8%3D | unknown | — | — | whitelisted |
32 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhtVltVOu8OqBzmsd%2B%2FeFfks3xTQQUvGsiZZ2MaObmHgXx2HIl1LjgSMACEAvcoEuhCK%2FAlHGPdKmo6gs%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6292 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754556116&P2=404&P3=2&P4=WGAw8h3ZLaCQOr5iVH2wZbrLd%2fejxjuhzz81Y4QF6rwKCqE73ekIYo1E0MBwnSAa2zV%2fDZYe6Q5qOAStvbh6BA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2232 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2464 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2464 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2464 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2464 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
2464 | msedge.exe | 172.232.142.106:443 | emily-2024-schedulec-completeorganizer.se-sto-1.linodeobjects.com | Akamai International B.V. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
emily-2024-schedulec-completeorganizer.se-sto-1.linodeobjects.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Bucket Object Storage service (.linodeobjects .com) |
2464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Bucket Object Storage service (.linodeobjects .com) |
2464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Bucket Object Storage service (.linodeobjects .com) |
2464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Bucket Object Storage service (.linodeobjects .com) |
2464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Bucket Object Storage service (.linodeobjects .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
Process | Message |
|---|---|
powershell.exe | PID=3576 TID=7588 Enter DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 Lookup in table by path failed for: DummyPath-2BA51B78-C7F7-4910-B99D-BB7345357CDC - CTransactionalImageTable::LookupImagePath
|
powershell.exe | PID=3576 TID=7588 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 Initialized GlobalConfig - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 DismApi.dll: Parent process command line: "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=3576 TID=7588 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|