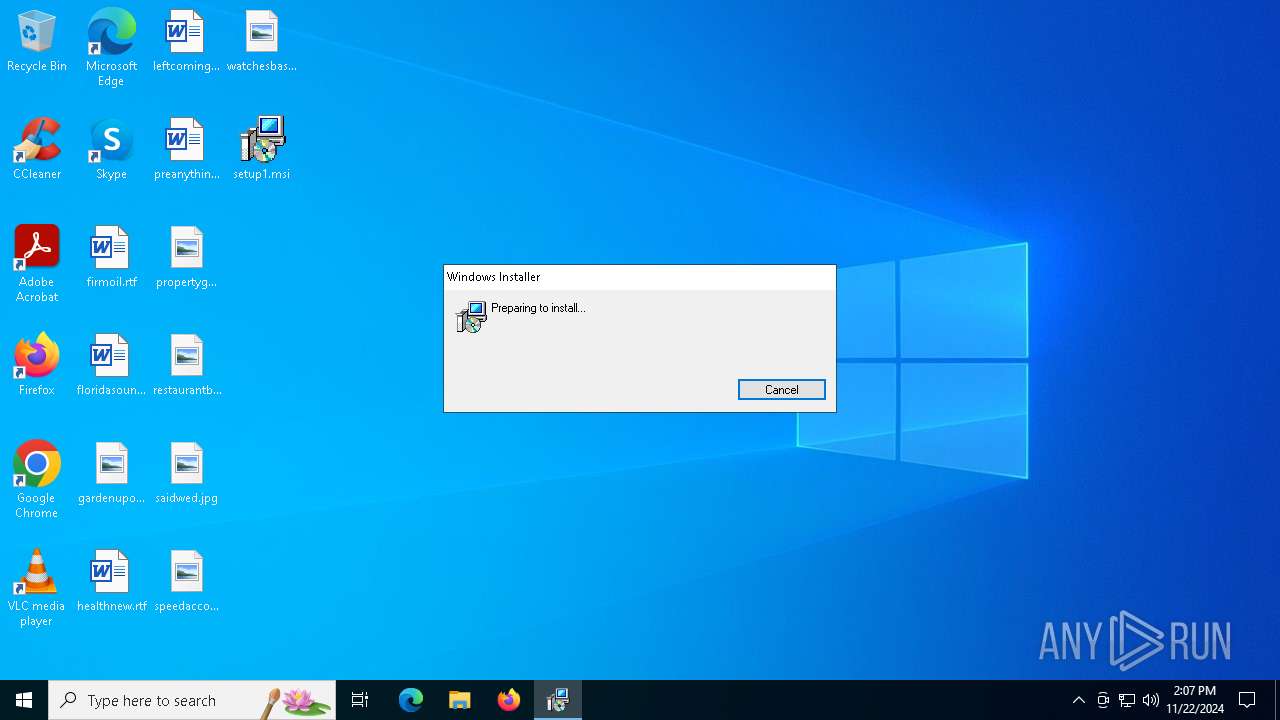
| File name: | setup1.msi |
| Full analysis: | https://app.any.run/tasks/9e9bf520-6148-47bf-a0db-29e1035ba605 |
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2024, 14:06:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: AteraAgent, Author: Atera networks, Keywords: Installer, Comments: This installer database contains the logic and data required to install AteraAgent., Template: Intel;1033, Revision Number: {721AD955-79FD-4019-BBF5-9DCC4C1175BB}, Create Time/Date: Wed Feb 28 10:52:02 2024, Last Saved Time/Date: Wed Feb 28 10:52:02 2024, Number of Pages: 200, Number of Words: 6, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 7F8EF88563FECC928CC24335BBB48AE6 |
| SHA1: | 050FB5D48707F31F48E727DEFFD17F848B71B1FF |
| SHA256: | 671F3E2880A809C70EB4BA951984F9CF4D52306988AB46AF78FCD56879969A97 |
| SSDEEP: | 98304:eIZTffzvns6eLKLdpRwznfsJb+7J7ERXndiWaKzPtSjXmbABY/lT8vjkZBvrePVv:f3XP9No |
MALICIOUS
ATERAAGENT has been detected (YARA)
- msiexec.exe (PID: 5320)
- msiexec.exe (PID: 4264)
Starts NET.EXE for service management
- msiexec.exe (PID: 1796)
- net.exe (PID: 536)
Changes powershell execution policy (Bypass)
- AgentPackageAgentInformation.exe (PID: 4804)
- AgentPackageAgentInformation.exe (PID: 6980)
Bypass execution policy to execute commands
- powershell.exe (PID: 6212)
- powershell.exe (PID: 6232)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 5320)
- msiexec.exe (PID: 4264)
- AteraAgent.exe (PID: 3632)
- AteraAgent.exe (PID: 968)
Executes as Windows Service
- VSSVC.exe (PID: 5208)
- AteraAgent.exe (PID: 3632)
- AteraAgent.exe (PID: 968)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3544)
- rundll32.exe (PID: 5836)
- rundll32.exe (PID: 5592)
- rundll32.exe (PID: 5980)
- AteraAgent.exe (PID: 3632)
- AteraAgent.exe (PID: 968)
ATERAAGENT has been detected
- AteraAgent.exe (PID: 2280)
- AteraAgent.exe (PID: 3632)
- AteraAgent.exe (PID: 968)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 1796)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 3632)
- AteraAgent.exe (PID: 968)
Starts CMD.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 4804)
- AgentPackageAgentInformation.exe (PID: 6980)
The process executes VB scripts
- cmd.exe (PID: 6072)
- cmd.exe (PID: 7088)
Executes application which crashes
- cscript.exe (PID: 5032)
- cscript.exe (PID: 7160)
Starts POWERSHELL.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 4804)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 3052)
- AgentPackageAgentInformation.exe (PID: 6980)
The process executes Powershell scripts
- cmd.exe (PID: 6504)
- cmd.exe (PID: 3052)
INFO
Creates files or folders in the user directory
- msiexec.exe (PID: 5320)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5320)
Reads the software policy settings
- msiexec.exe (PID: 5320)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4264)
Manages system restore points
- SrTasks.exe (PID: 3540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | AteraAgent |
| Author: | Atera networks |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install AteraAgent. |
| Template: | Intel;1033 |
| RevisionNumber: | {721AD955-79FD-4019-BBF5-9DCC4C1175BB} |
| CreateDate: | 2024:02:28 10:52:02 |
| ModifyDate: | 2024:02:28 10:52:02 |
| Pages: | 200 |
| Words: | 6 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
186
Monitored processes
57
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 536 | "NET" STOP AteraAgent | C:\Windows\SysWOW64\net.exe | — | msiexec.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 748 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\AgentPackageMonitoring.exe" af80a0a8-1add-4357-8773-de4462ef2597 "fd0d6cd5-4648-406d-a63e-ef9d91d3dfbf" agent-api.atera.com/Production 443 or8ixLi90Mf "syncprofile" 001Q300000NOSXQIA5 | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\AgentPackageMonitoring.exe | — | AteraAgent.exe |
User: SYSTEM Integrity Level: SYSTEM Description: AgentPackageMonitoring Exit code: 0 Version: 37.8.0.0 | ||||
| 900 | C:\WINDOWS\system32\WerFault.exe -u -p 5032 -s 1764 | C:\Windows\System32\WerFault.exe | — | cscript.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 968 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe" | C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe | services.exe | |
User: SYSTEM Company: ATERA Networks Ltd. Integrity Level: SYSTEM Description: AteraAgent Version: 1.8.7.2 | ||||
| 1796 | C:\Windows\syswow64\MsiExec.exe -Embedding 393D6A9AF16BE4AE5A2D5F2A2A11AEAD E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | ||||
| 2144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AgentPackageAgentInformation.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2280 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe" /i /IntegratorLogin="lucasrp112@gmail.com" /CompanyId="1" /IntegratorLoginUI="" /CompanyIdUI="" /FolderId="" /AccountId="001Q300000NOSXQIA5" /AgentId="af80a0a8-1add-4357-8773-de4462ef2597" | C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe | msiexec.exe | |
User: admin Company: ATERA Networks Ltd. Integrity Level: MEDIUM Description: AteraAgent Exit code: 0 Version: 1.8.7.2 | ||||
| 2600 | C:\Windows\syswow64\MsiExec.exe -Embedding 2DDDA715B3E80573A48CA5C9108C4CE3 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | ||||
| 2996 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageSTRemote\AgentPackageSTRemote.exe" af80a0a8-1add-4357-8773-de4462ef2597 "397e0d69-642d-4d76-a626-f16c0894d996" agent-api.atera.com/Production 443 or8ixLi90Mf "install eyJSbW1Db2RlIjoiaFpDREZQaEs3NW1KIn0=" 001Q300000NOSXQIA5 | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageSTRemote\AgentPackageSTRemote.exe | — | AteraAgent.exe |
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageSTRemote Version: 23.4.0.0 | ||||
| 3052 | "cmd.exe" /c powershell.exe -File "C:\Program Files\Microsoft Office\Office16\vNextDiag.ps1" | C:\Windows\System32\cmd.exe | — | AgentPackageAgentInformation.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
Total events
8 641
Read events
8 487
Write events
145
Delete events
9
Modification events
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000007677C1D0E73CDB01A8100000680E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000038DCC3D0E73CDB01A8100000680E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000003E0E3BD1E73CDB01A8100000680E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000003E0E3BD1E73CDB01A8100000680E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000004AD93FD1E73CDB01A8100000680E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000848F44D1E73CDB01A8100000680E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000DEEEC2D1E73CDB01A8100000680E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4264) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C753C5D1E73CDB01A810000060120000E803000001000000000000000000000055078EC21B86614B9A985B345899C54E00000000000000000000000000000000 | |||
| (PID) Process: | (5208) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000002739D1D1E73CDB0158140000580F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
65
Suspicious files
49
Text files
38
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4264 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_DEB07B5578A606ED6489DDA2E357A944 | der | |
MD5:4223B22A7E4BE6712287C44BD1D05031 | SHA256:453A5A7DEB719B735941357560B3A78C33AE23B90B4C8BEB7E9104B5856841D5 | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:3971829FEC73B212BDCDCB6DD89AEDB7 | SHA256:6C7F5198F334DBB46CCAB08A2E85AA73E4E4609F898A612271A56D8AC40FD48E | |||
| 3544 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICF59.tmp-\CustomAction.config | xml | |
MD5:BC17E956CDE8DD5425F2B2A68ED919F8 | SHA256:E4FF538599C2D8E898D7F90CCF74081192D5AFA8040E6B6C180F3AA0F46AD2C5 | |||
| 4264 | msiexec.exe | C:\Windows\Installer\MSICF59.tmp | executable | |
MD5:88D29734F37BDCFFD202EAFCDD082F9D | SHA256:87C97269E2B68898BE87B884CD6A21880E6F15336B1194713E12A2DB45F1DCCF | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:FB7D985BE173E4BBB25C78D9CC4535E2 | SHA256:E9D8F66896D2A23FF7E8AFB7D2DB5F1A77CBF7DE7432B64E94E65EFA197DEA12 | |||
| 4264 | msiexec.exe | C:\Windows\Installer\13cba0.msi | executable | |
MD5:7F8EF88563FECC928CC24335BBB48AE6 | SHA256:671F3E2880A809C70EB4BA951984F9CF4D52306988AB46AF78FCD56879969A97 | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:FAEF9FD1B29A876565815D741358ED1A | SHA256:AFA189C73AD5A3456A8F9C75AC8703BD8591DAF3D5249D363BDDA13152DE8D13 | |||
| 4264 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{c28e0755-861b-4b61-9a98-5b345899c54e}_OnDiskSnapshotProp | binary | |
MD5:0917C6D205589D596A004147EBFC5089 | SHA256:2AE98EE149D64F3A74F5F8E0EF3507B5EBBA6B07814AC3636E60D575989FEF83 | |||
| 3544 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICF59.tmp-\AlphaControlAgentInstallation.dll | executable | |
MD5:AA1B9C5C685173FAD2DABEBEB3171F01 | SHA256:E44A6582CD3F84F4255D3C230E0A2C284E0CFFA0CA5E62E4D749E089555494C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
50
DNS requests
25
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4536 | svchost.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5320 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5320 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
1804 | RUXIMICS.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5320 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAooSZl45YmN9AojjrilUug%3D | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1804 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1804 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.43:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5320 | msiexec.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1804 | RUXIMICS.exe | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4536 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
agent-api.atera.com |
| whitelisted |
ps.pndsn.com |
| unknown |
ps.atera.com |
| whitelisted |
my.splashtop.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Splashtop Domain in DNS Lookup (splashtop .com) |
— | — | Misc activity | ET INFO Splashtop Domain (splashtop .com) in TLS SNI |
— | — | Misc activity | ET INFO Splashtop Domain in DNS Lookup (splashtop .com) |
— | — | Misc activity | ET INFO Splashtop Domain (splashtop .com) in TLS SNI |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
19 ETPRO signatures available at the full report