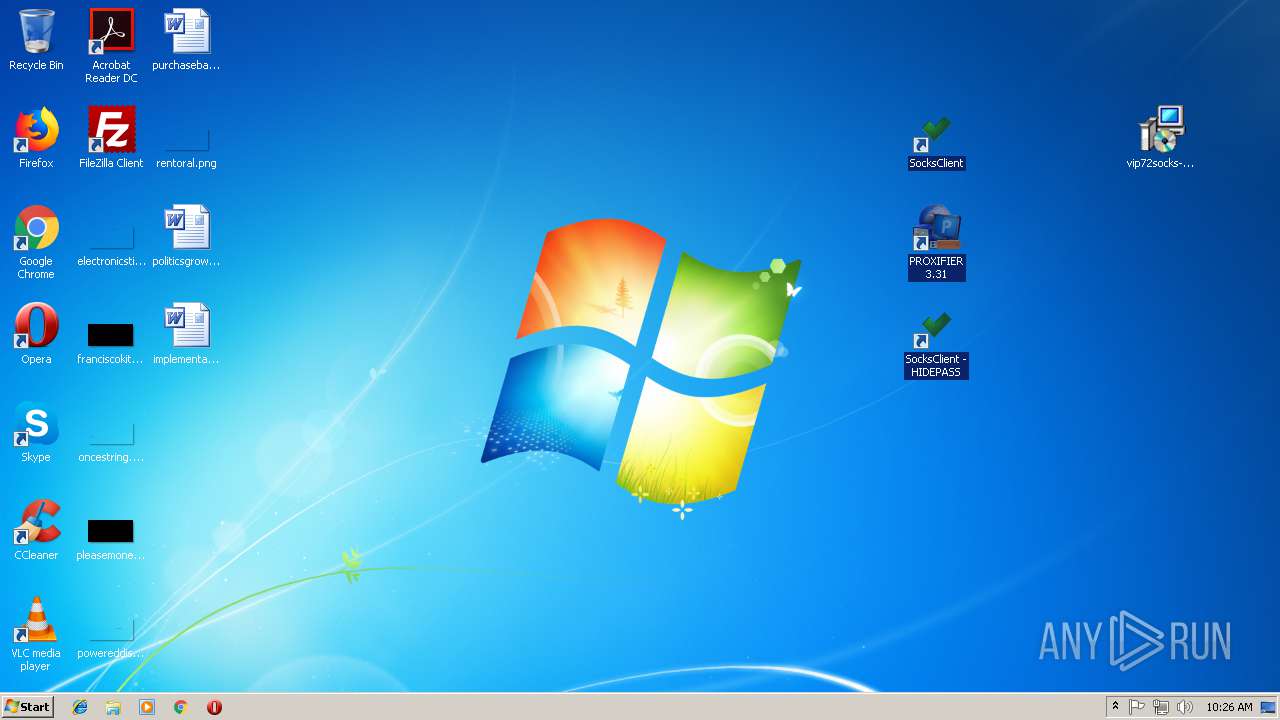
| File name: | vip72socks-installer.rar |
| Full analysis: | https://app.any.run/tasks/77e6d004-dbc8-4275-8f63-6db12bd0340d |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2018, 10:25:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
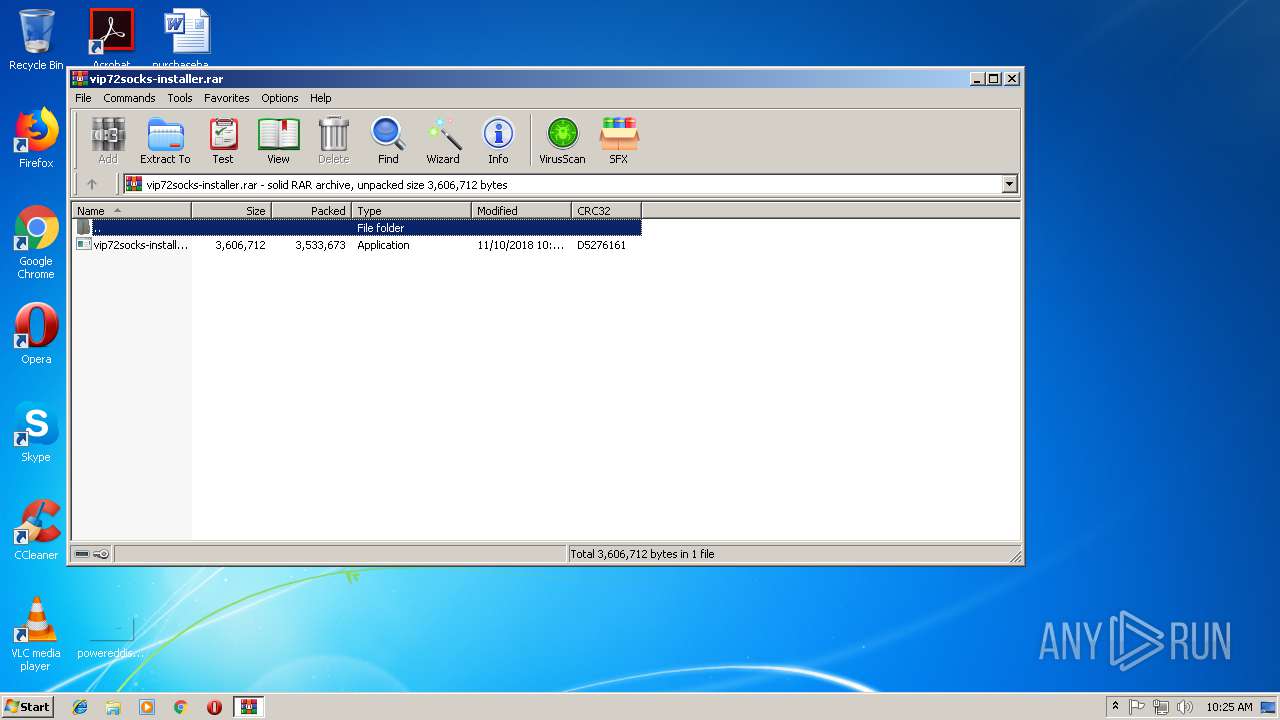
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | EAEAD9BFE529ECBF96FCC83902C64DE4 |
| SHA1: | BC9ECBF1B70226DE337BE3C193C3145885A1417D |
| SHA256: | 670D476B64C7A88A25D78B6CCCD48F76A1E843F5350261B0A93986B13083DDB5 |
| SSDEEP: | 98304:FyWJwc3nXvARhKZeb1z1tiFIf8B+OyKLQFEj:FLYRhKENHiGUw9kQFEj |
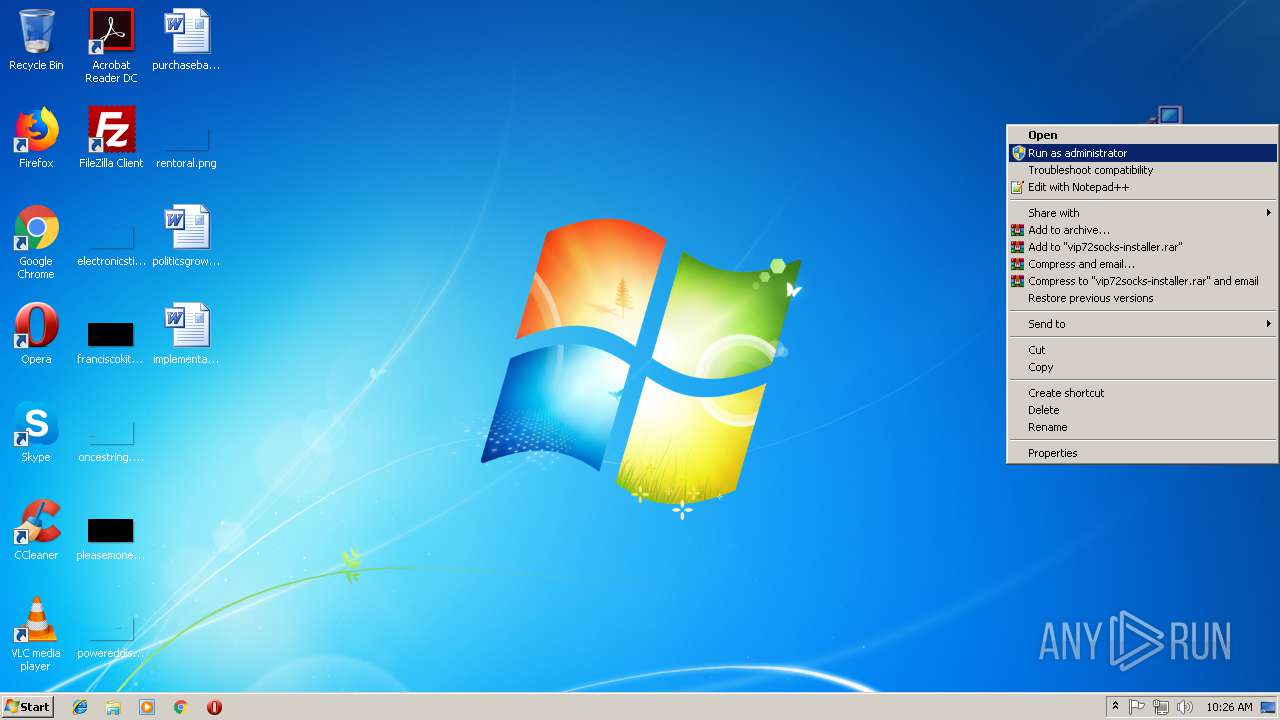
MALICIOUS
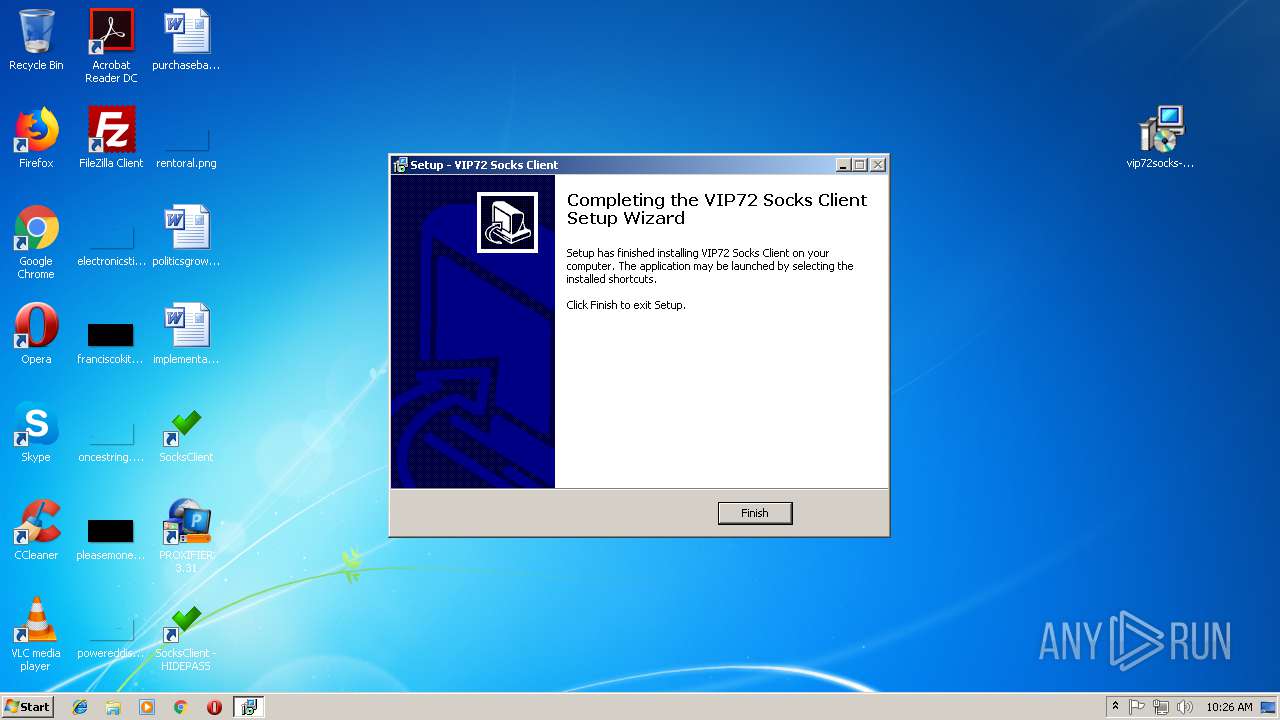
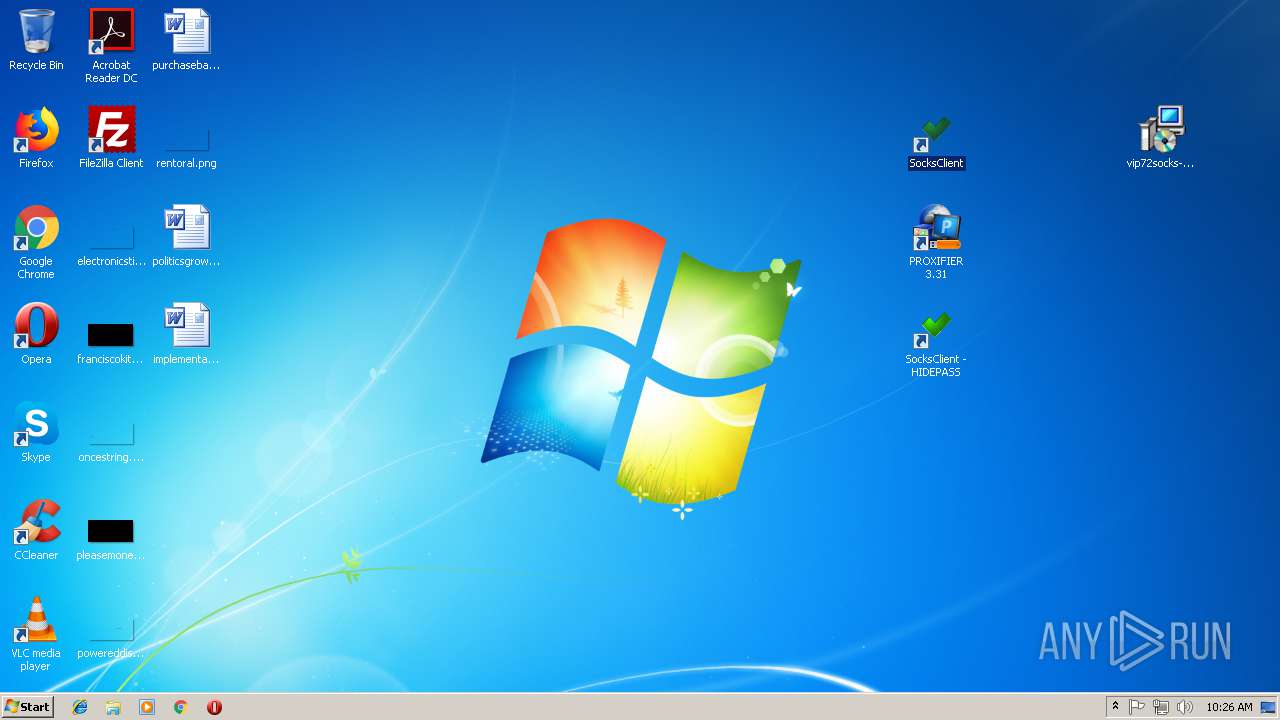
Application was dropped or rewritten from another process
- vip72socks-installer.exe (PID: 648)
- vip72socks.exe (PID: 2816)
SUSPICIOUS
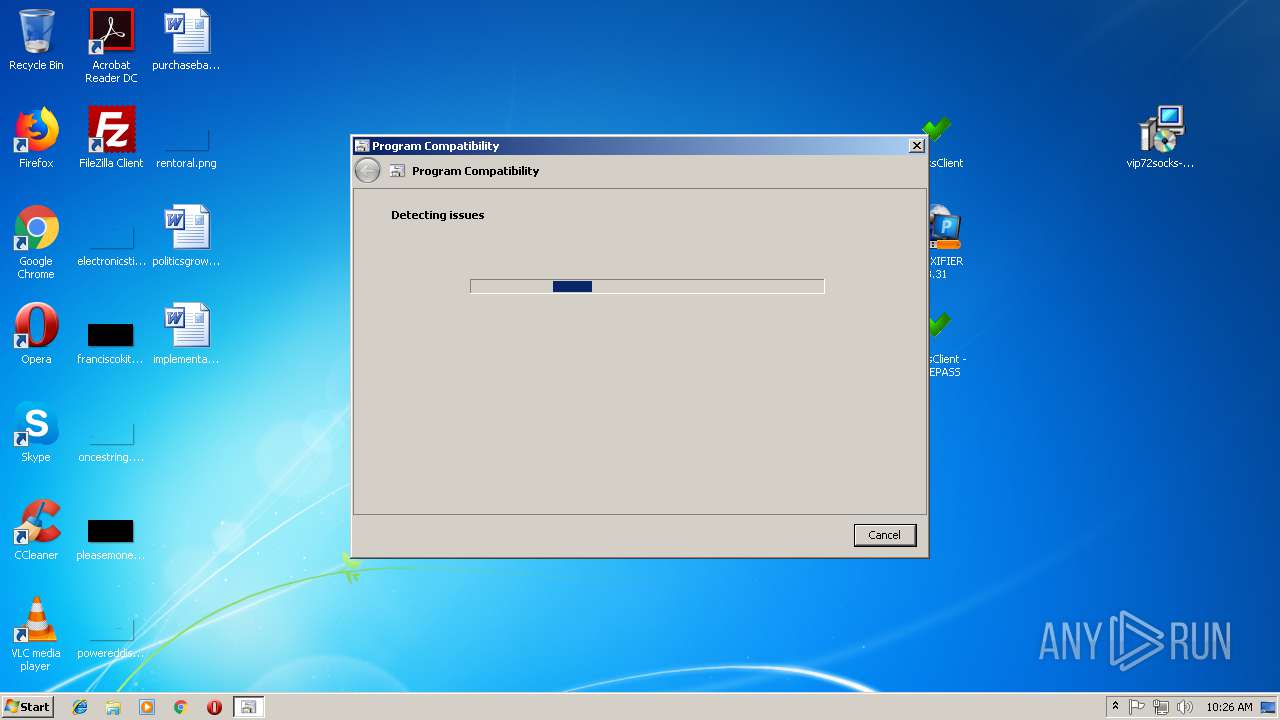
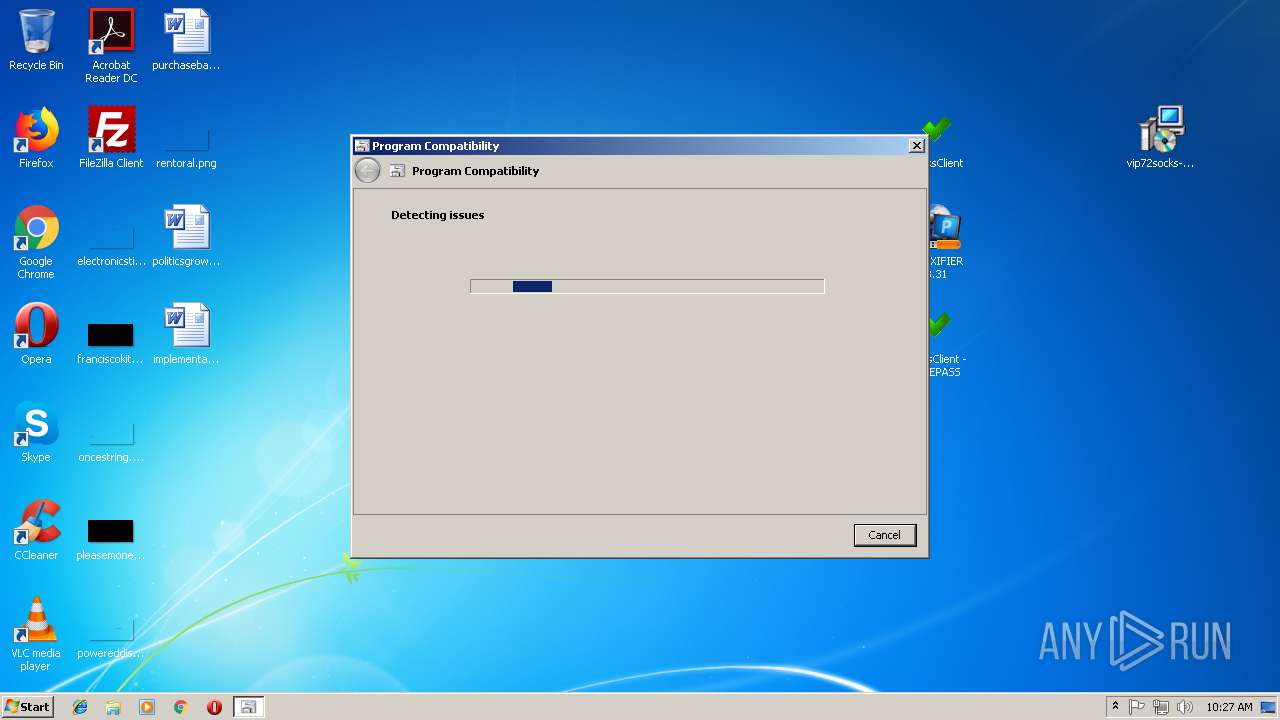
Executable content was dropped or overwritten
- vip72socks-installer.exe (PID: 648)
- msdt.exe (PID: 736)
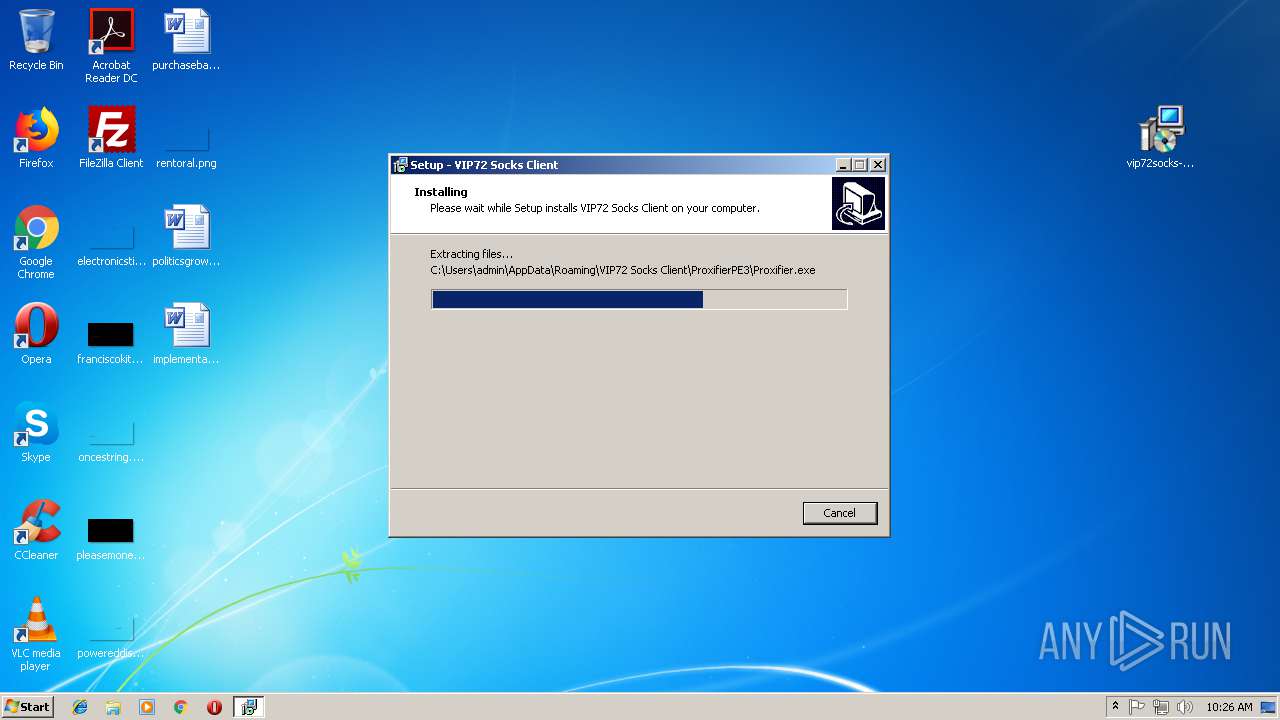
- vip72socks-installer.tmp (PID: 2436)
- csc.exe (PID: 2140)
- msdt.exe (PID: 1684)
Reads the Windows organization settings
- vip72socks-installer.tmp (PID: 2436)
Reads Windows owner or organization settings
- vip72socks-installer.tmp (PID: 2436)
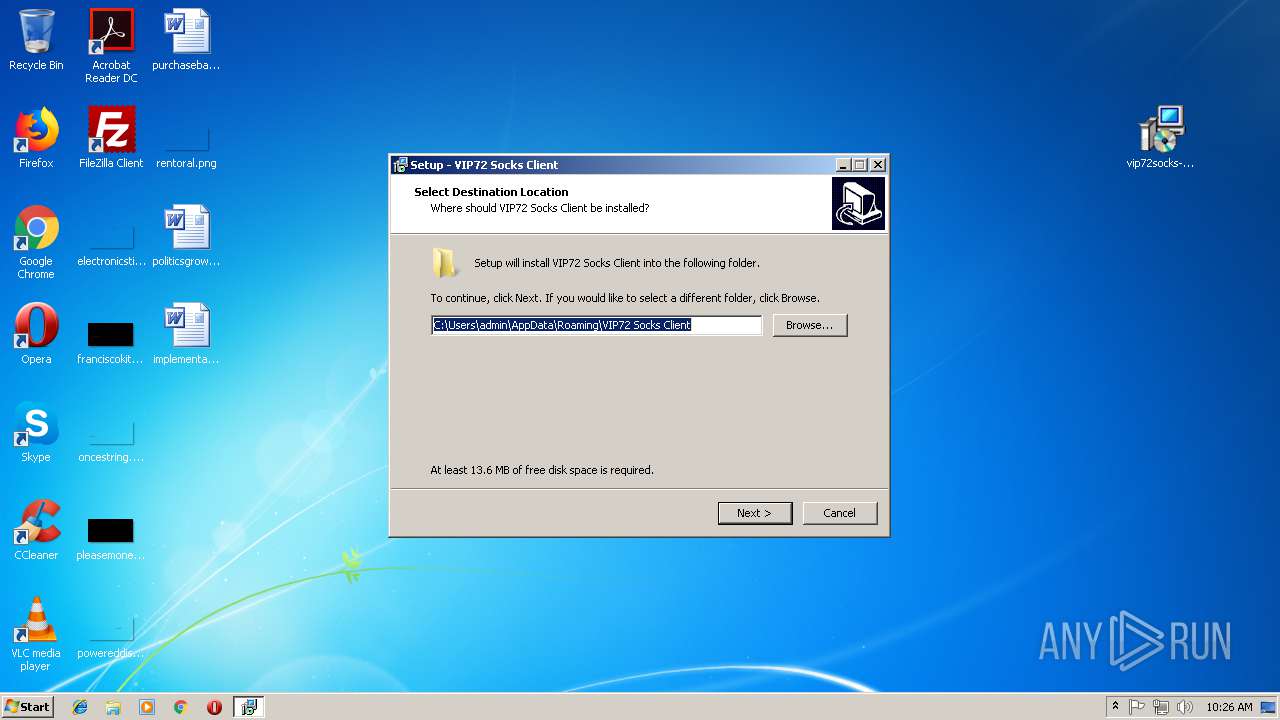
Creates files in the user directory
- vip72socks-installer.tmp (PID: 2436)
- vip72socks.exe (PID: 2816)
INFO
Application was dropped or rewritten from another process
- vip72socks-installer.tmp (PID: 2436)
Creates files in the program directory
- vip72socks-installer.tmp (PID: 2436)
Creates a software uninstall entry
- vip72socks-installer.tmp (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
58
Monitored processes
18
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7508.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7507.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
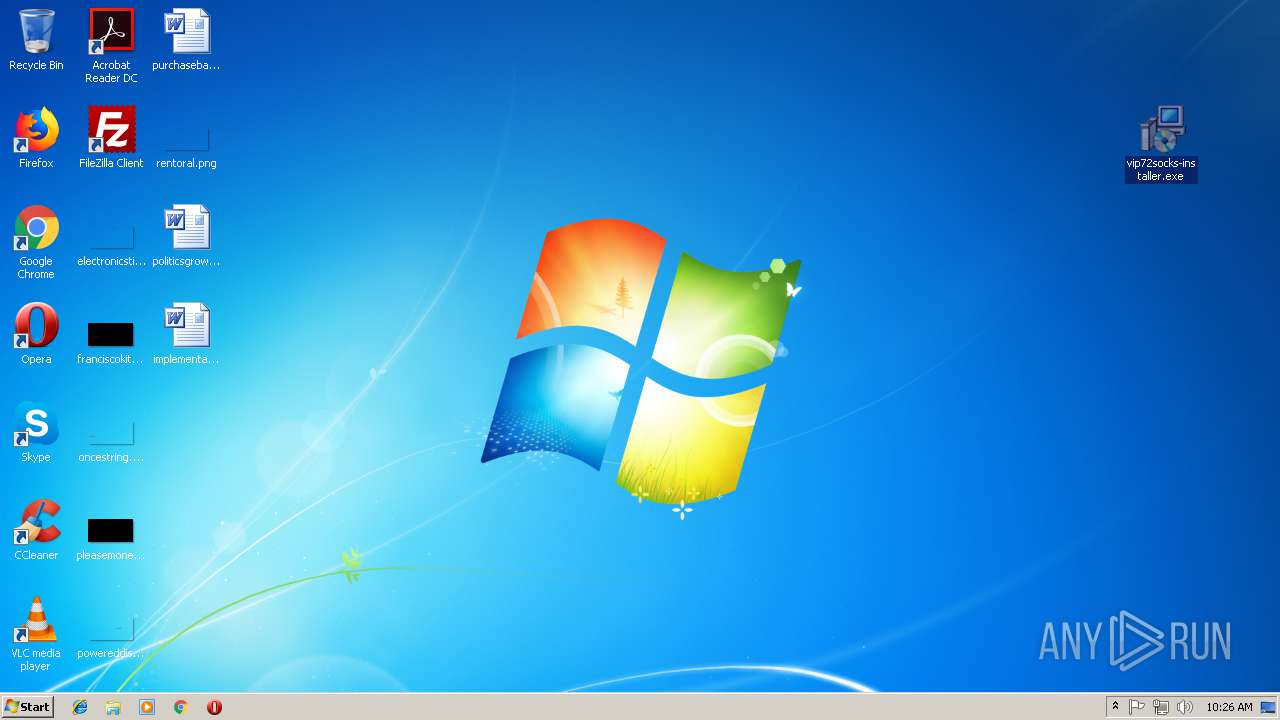
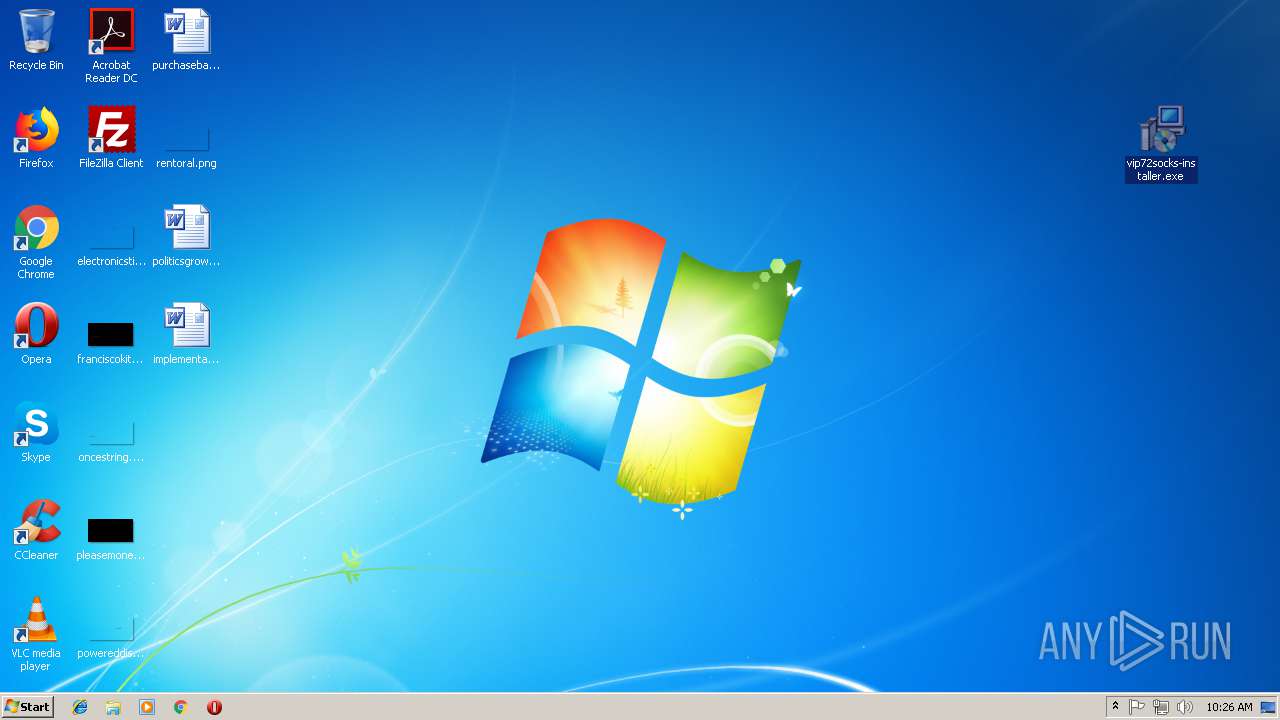
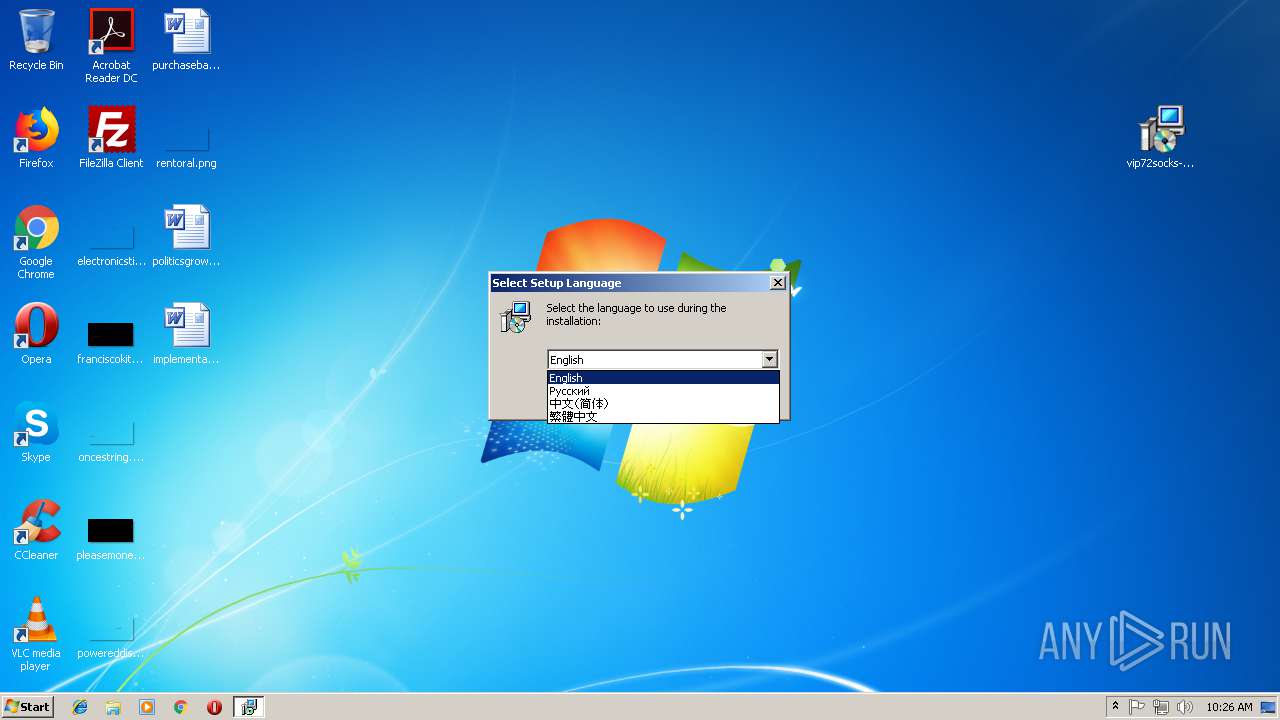
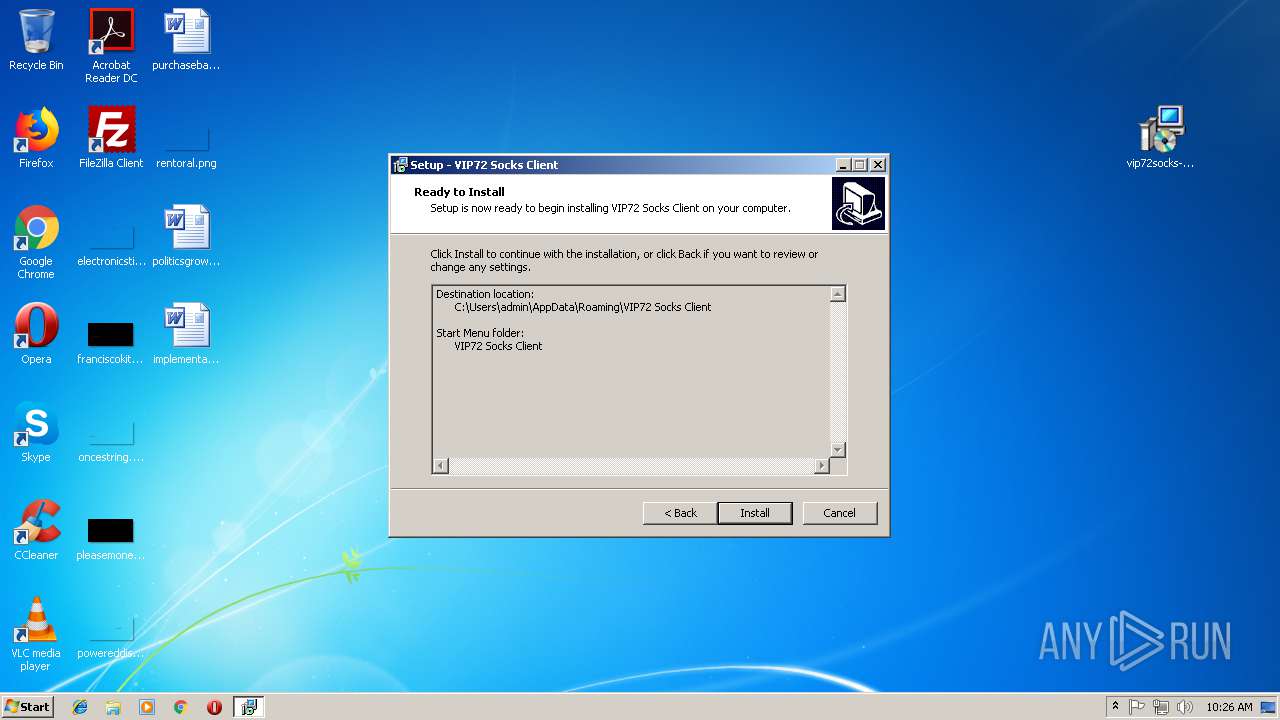
| 648 | "C:\Users\admin\Desktop\vip72socks-installer.exe" | C:\Users\admin\Desktop\vip72socks-installer.exe | explorer.exe | ||||||||||||
User: admin Company: VIP Technologies Integrity Level: HIGH Description: VIP72 Socks Client Setup Exit code: 0 Version: 1.8.3.5.1 Modules
| |||||||||||||||
| 736 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCW6E8F.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\AppData\Roaming\VIP72 Socks Client\vip72socks.exe" | C:\Windows\system32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\smmc1dr6.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
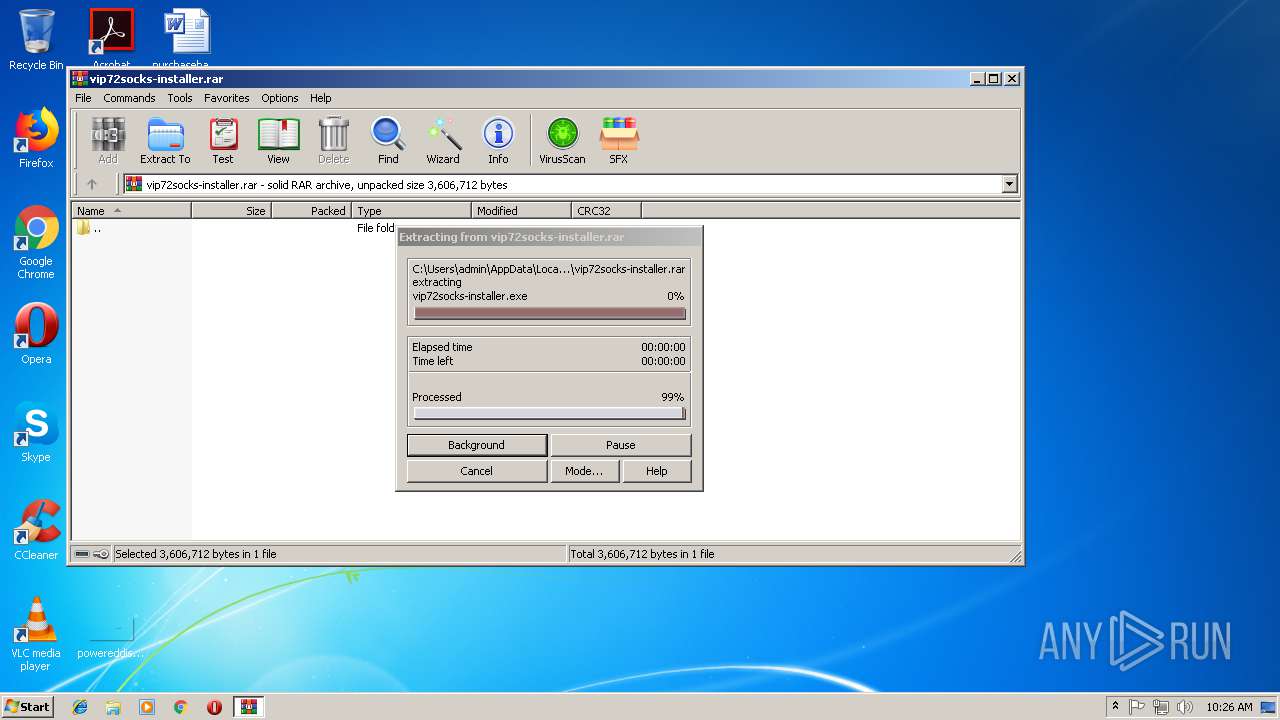
| 1488 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\vip72socks-installer.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1684 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\lfd6i-od.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1684 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCWF023.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\up-t3ztq.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
959
Read events
879
Write events
74
Delete events
6
Modification events
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vip72socks-installer.rar | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
18
Suspicious files
8
Text files
45
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1488.6414\vip72socks-installer.exe | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-L1DL1.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-R088Q.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-0MPIV.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-C4L9V.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-T81I9.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-LCF63.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-PMCSF.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\is-A69CI.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | vip72socks-installer.tmp | C:\Users\admin\AppData\Roaming\VIP72 Socks Client\howto\is-FL7U8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|